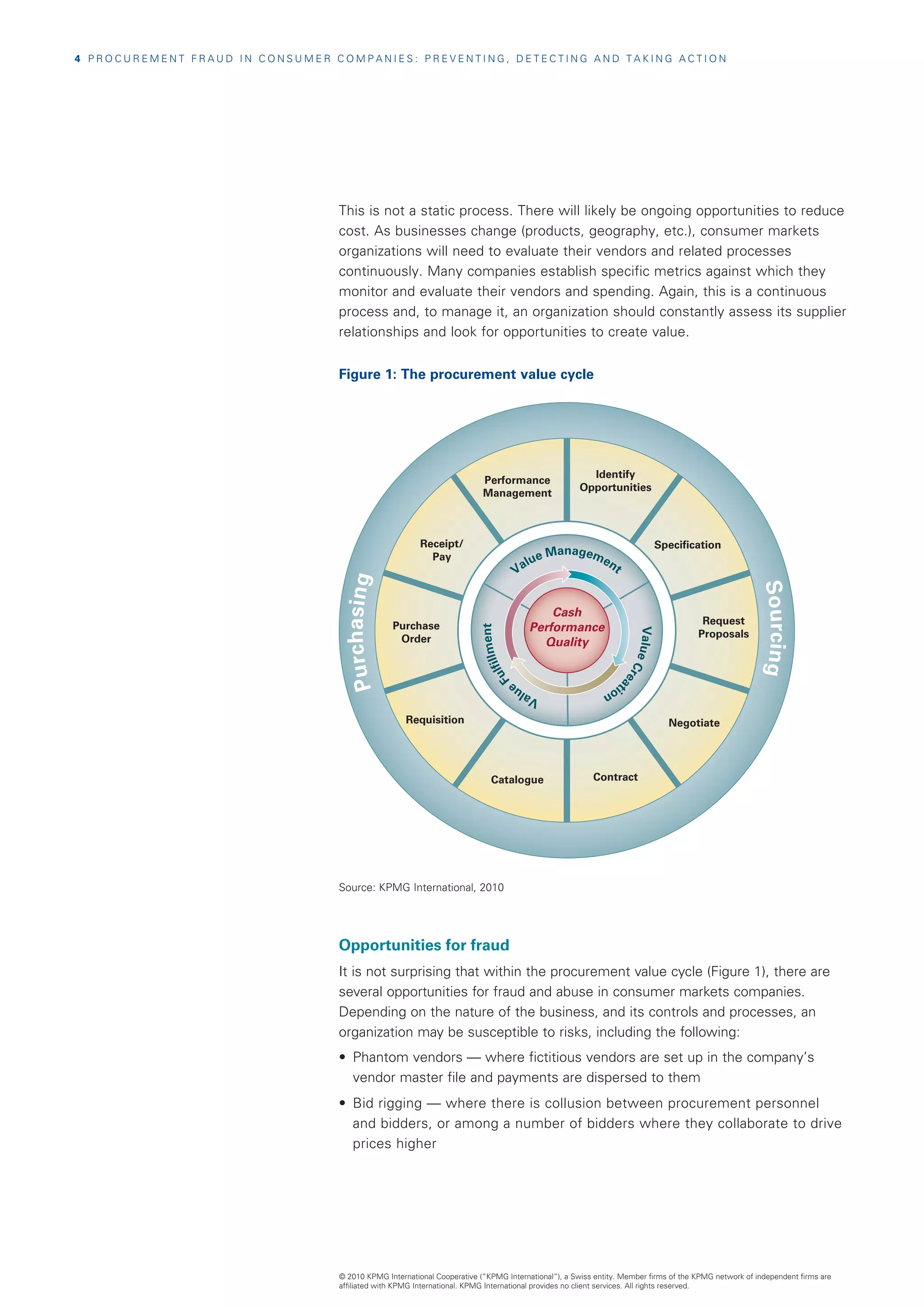
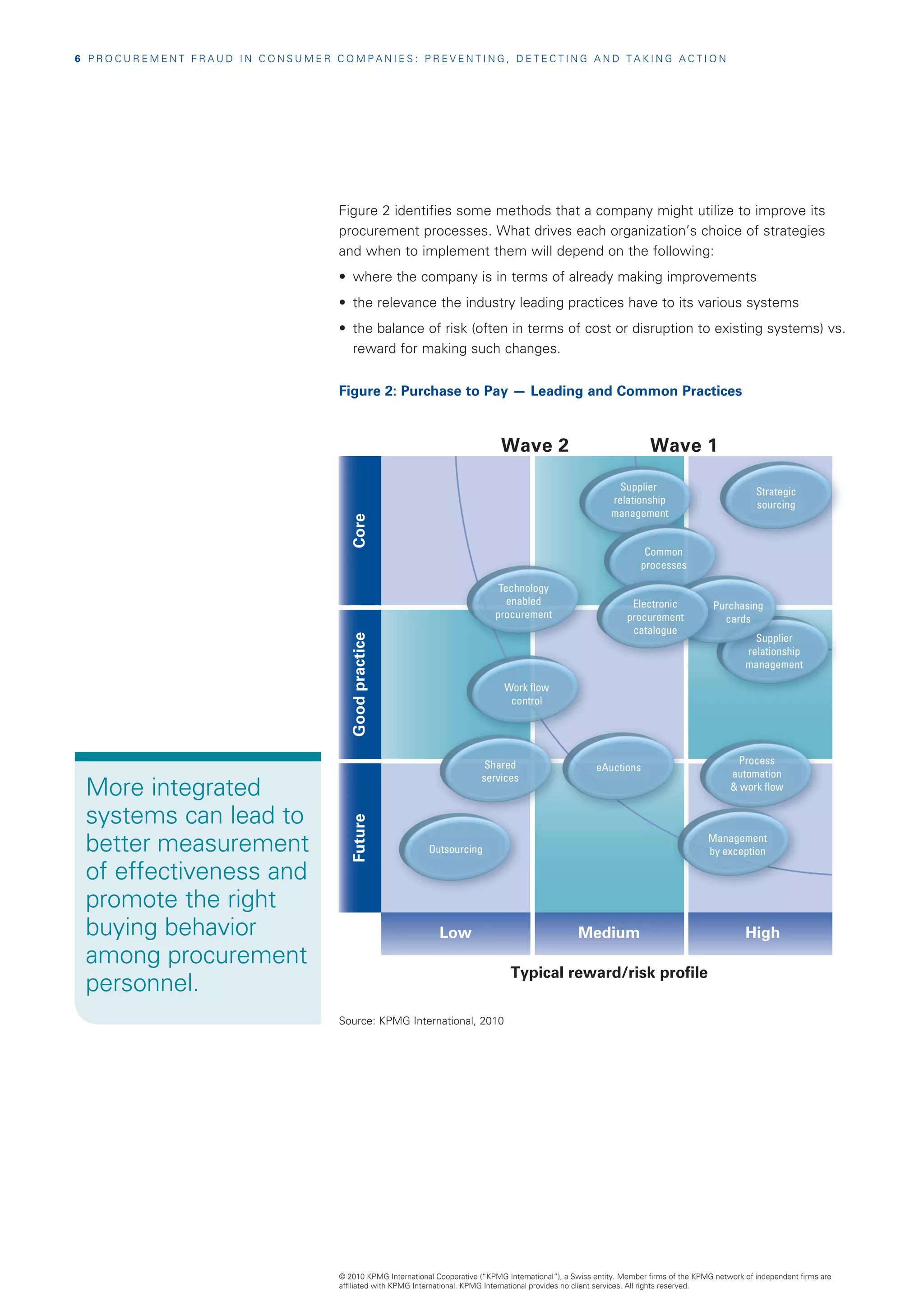
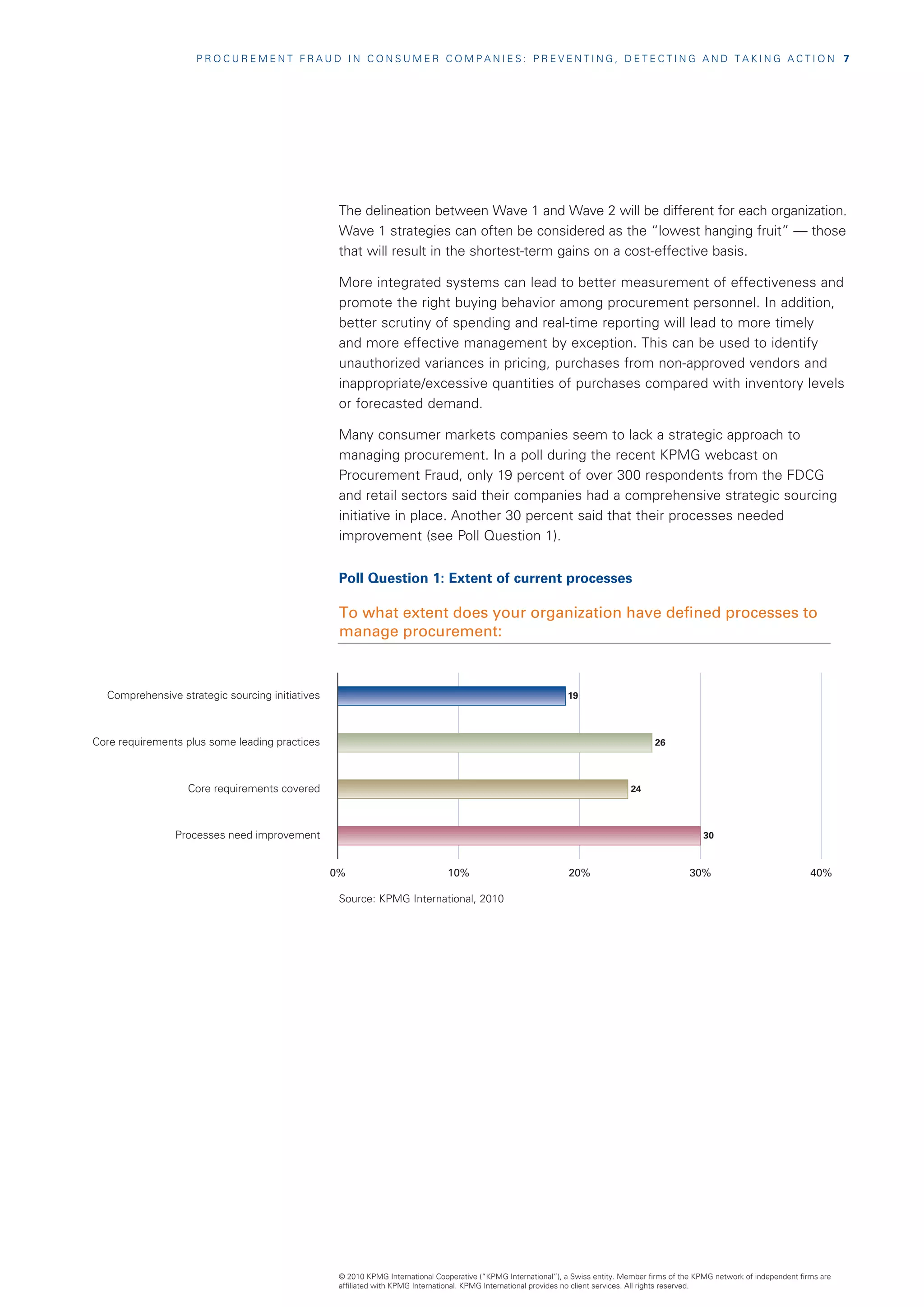
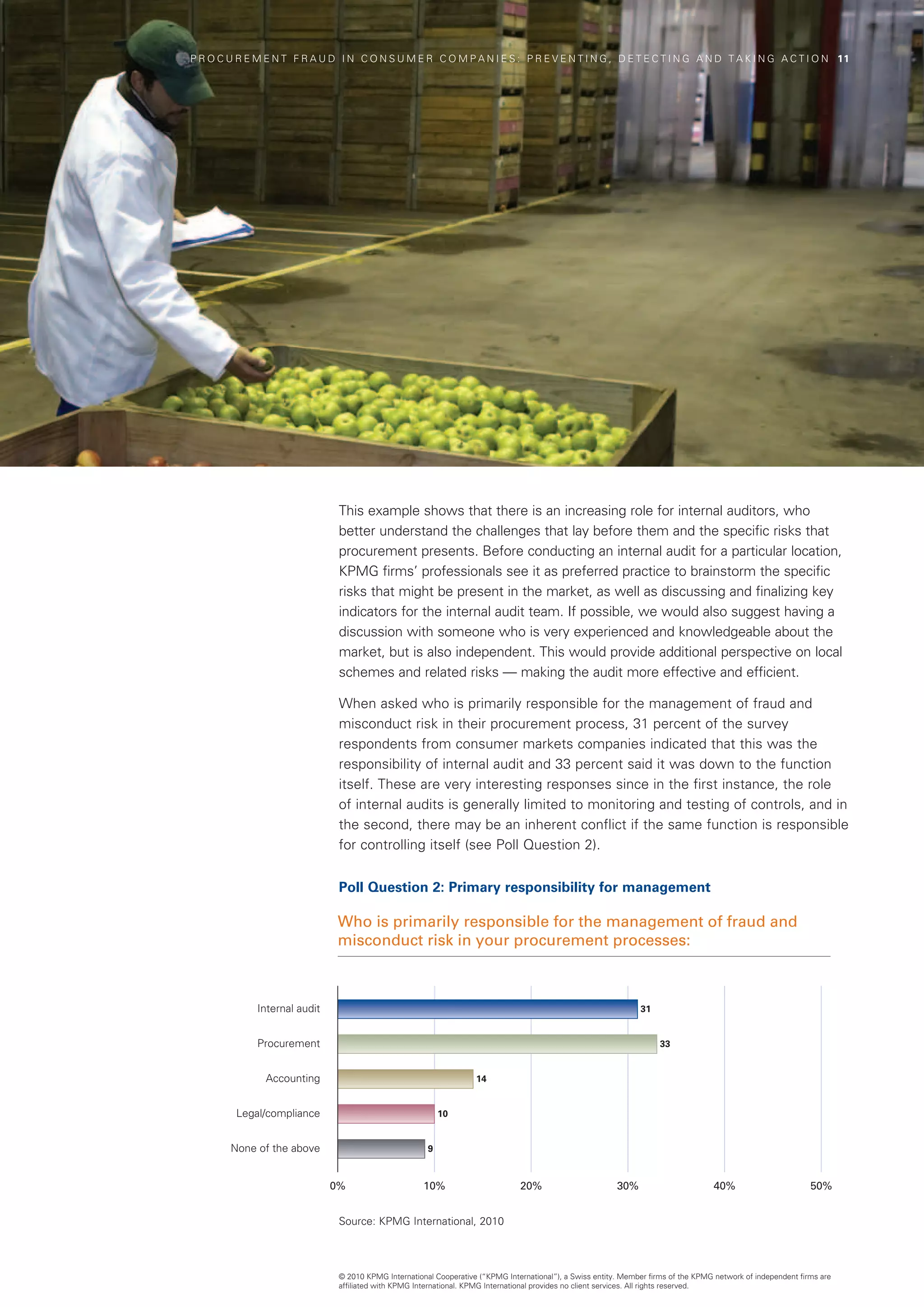
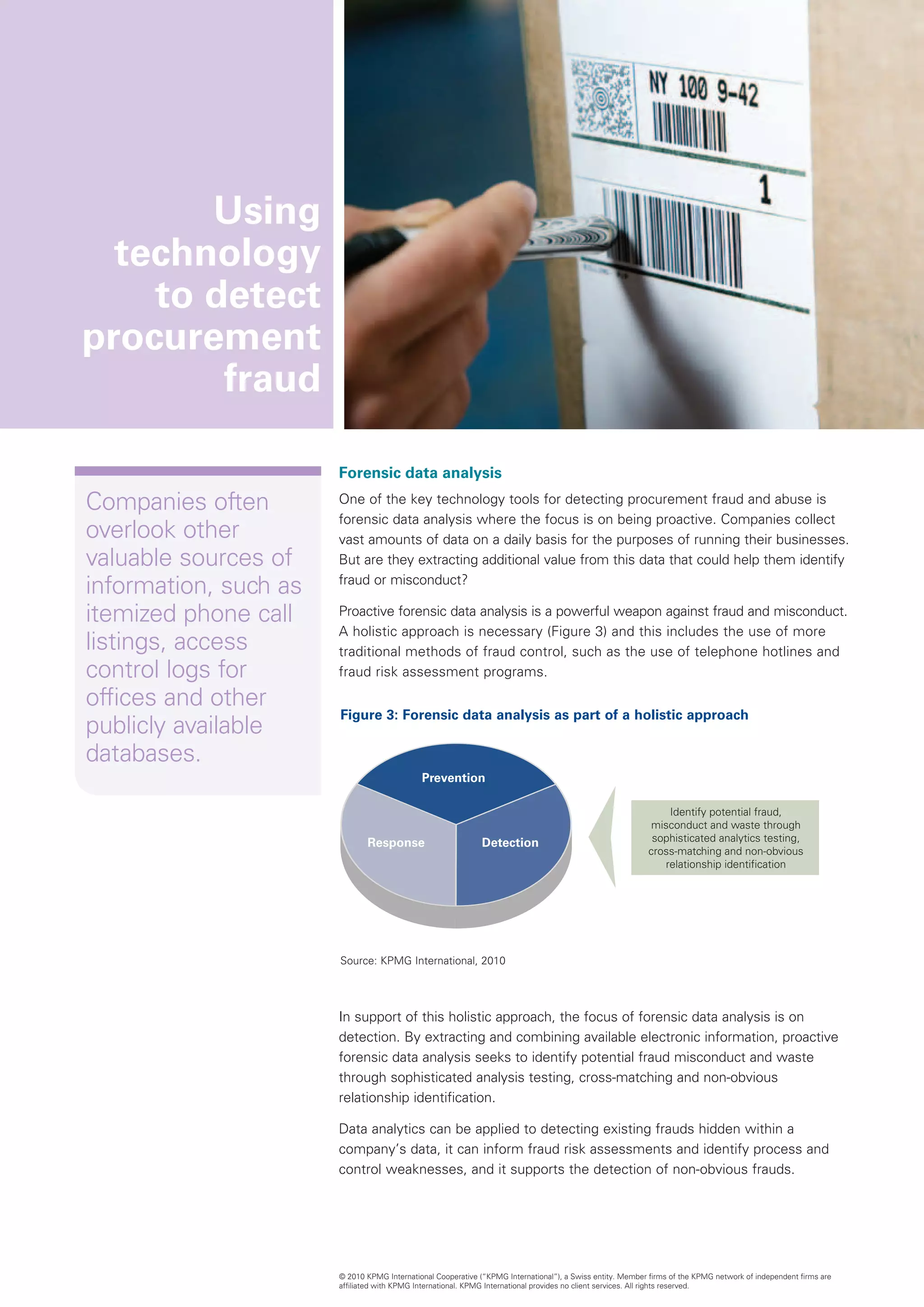
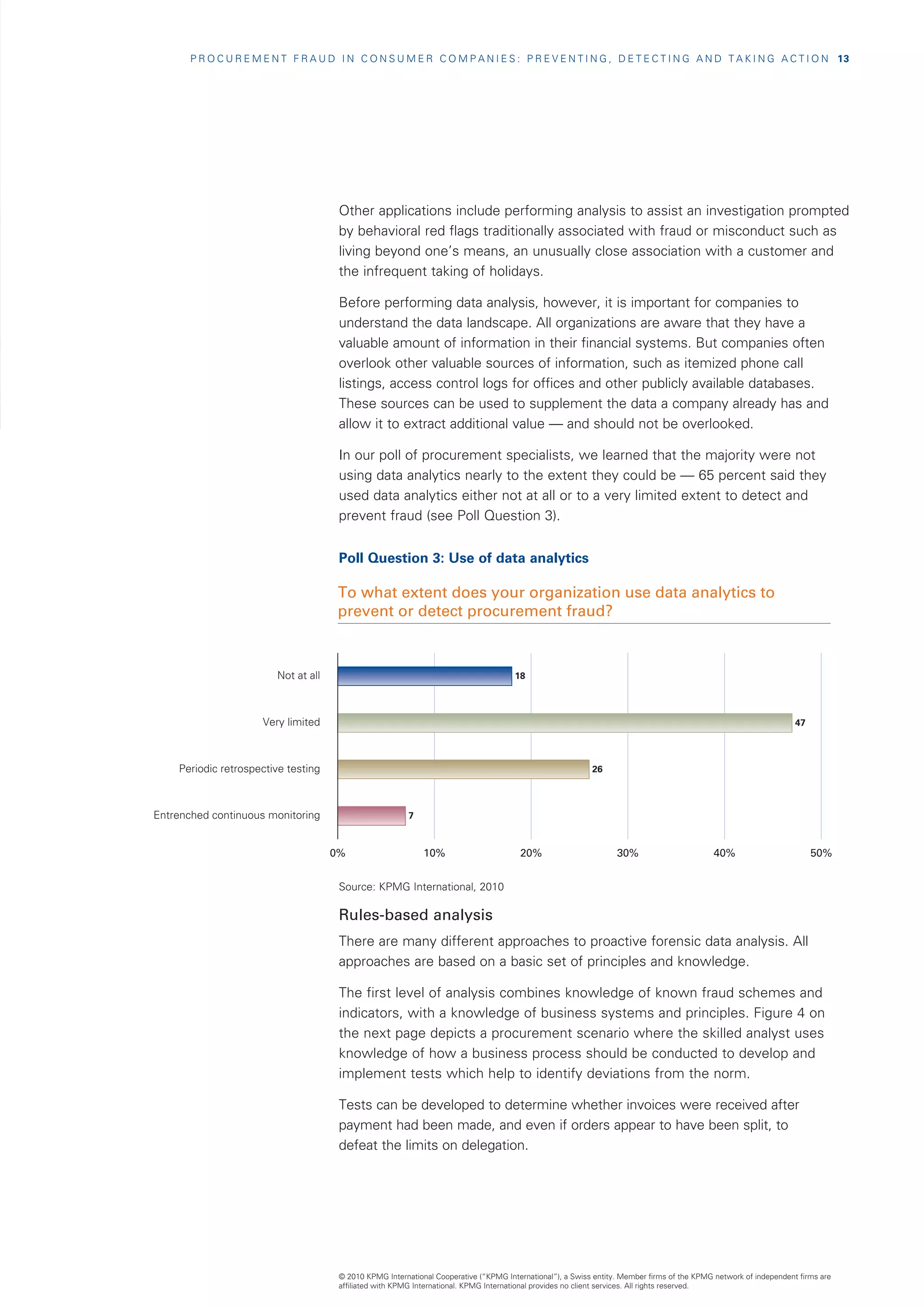
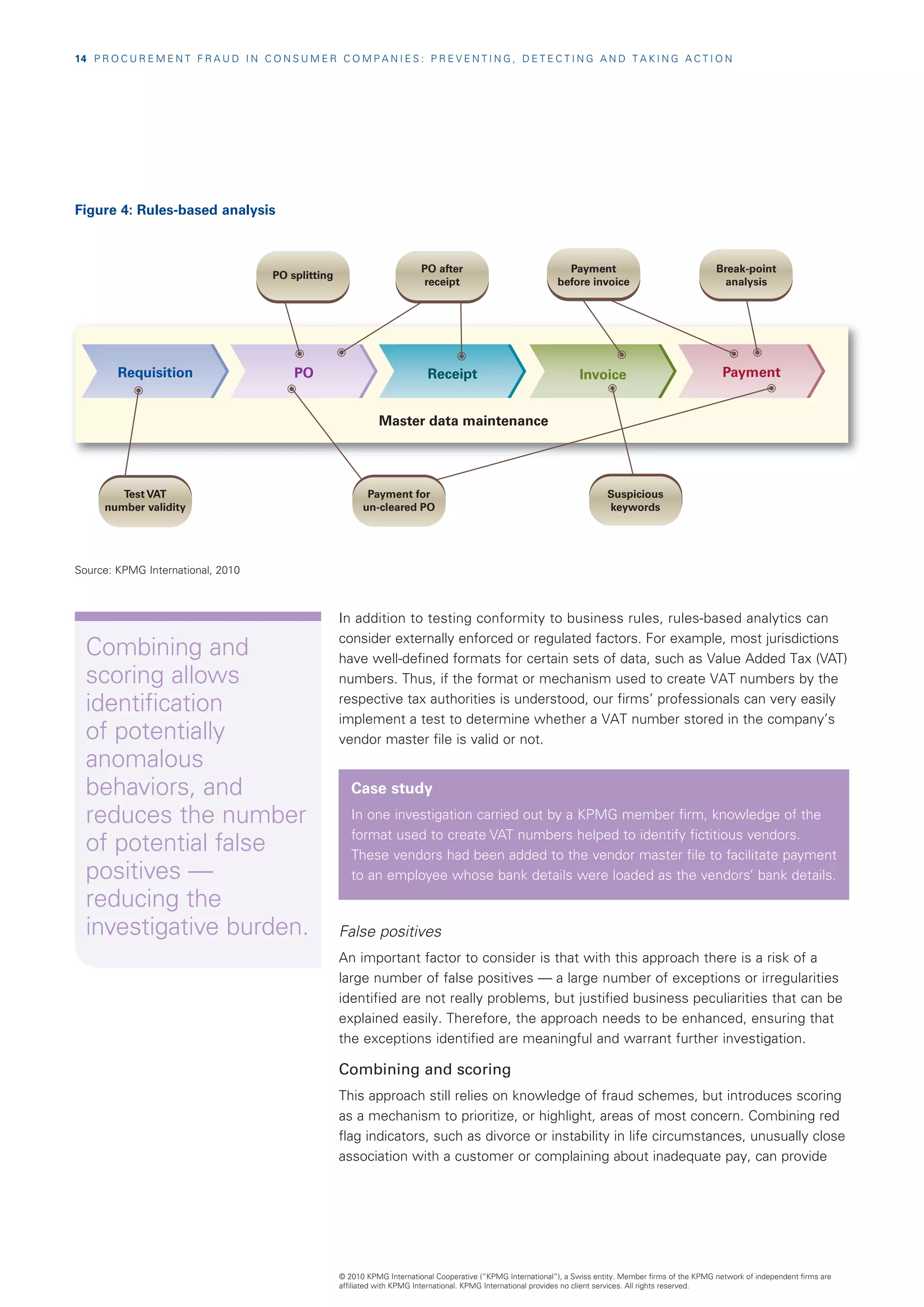
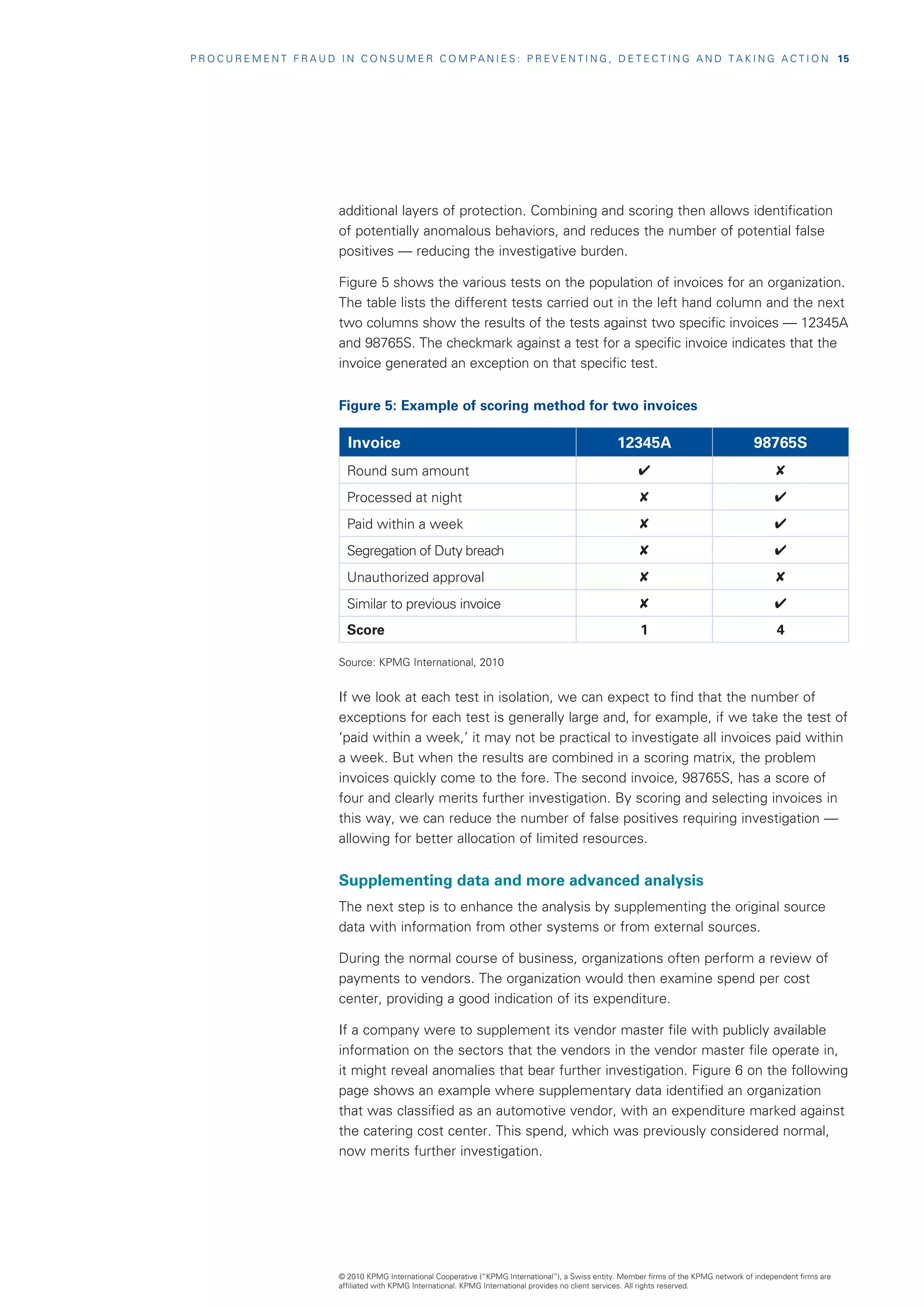
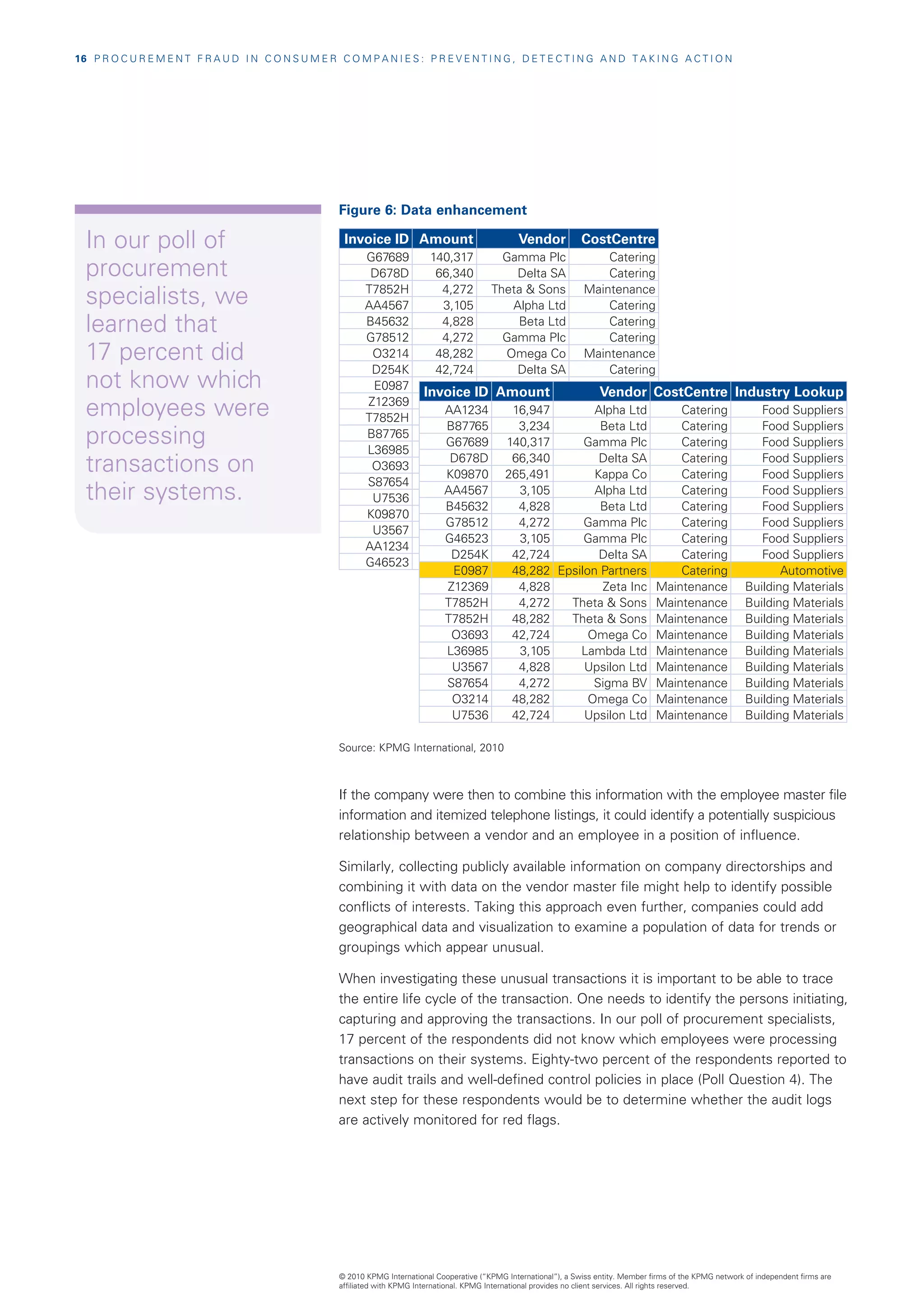
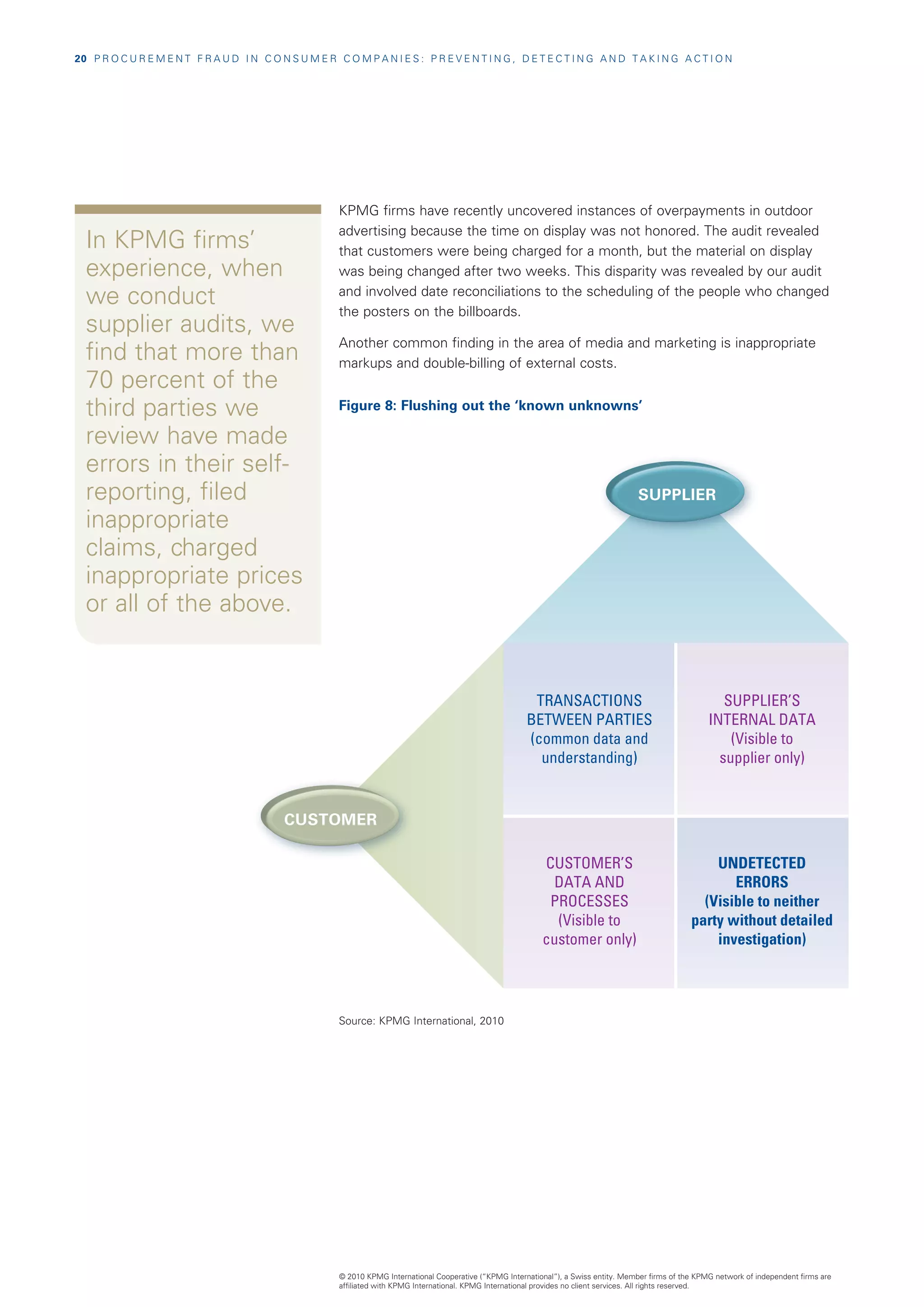
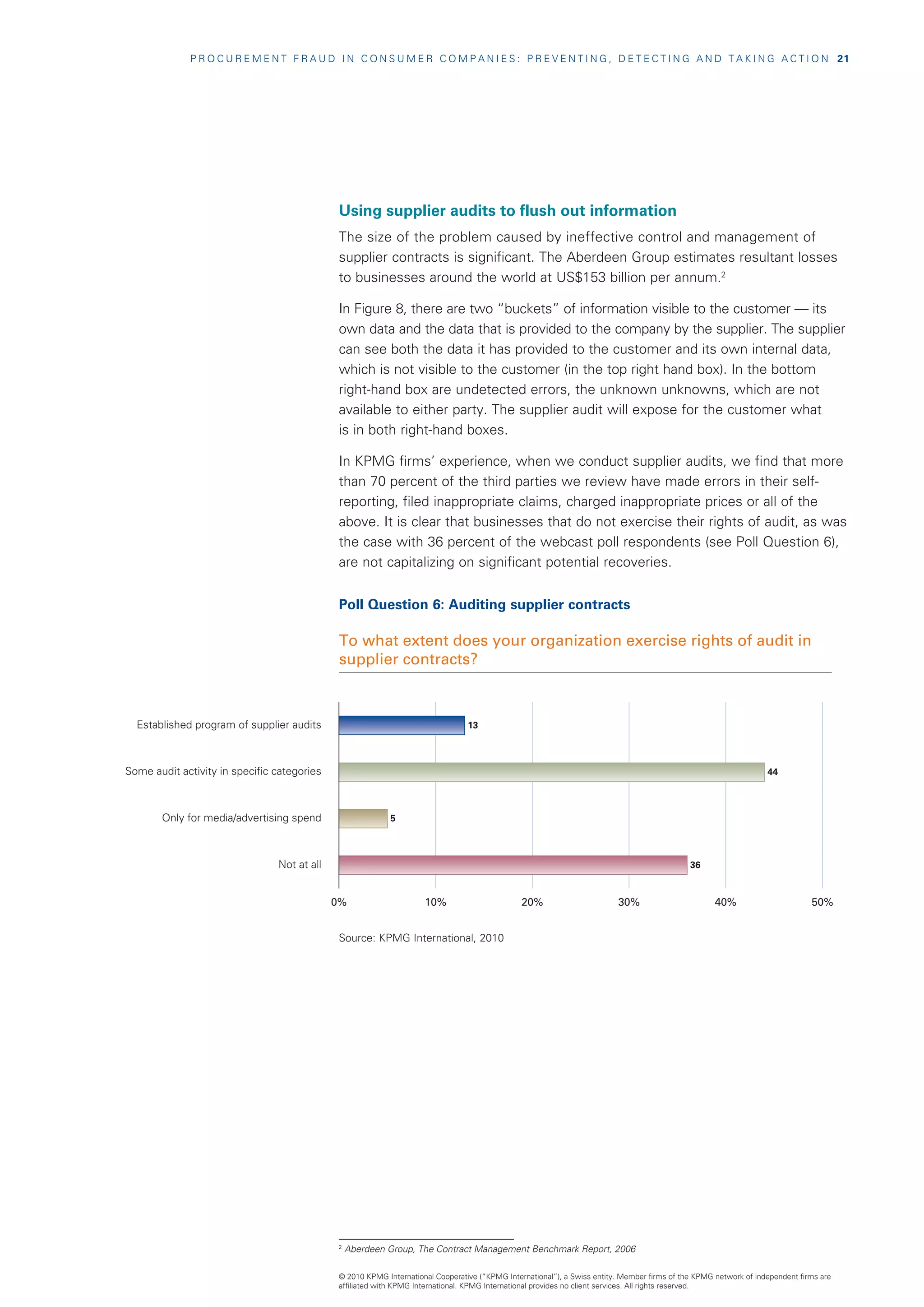
The document discusses procurement fraud in consumer markets, emphasizing its prevalence and the financial impact on companies. It explores the risks, opportunities for fraud, and proposes measures to prevent and detect such misconduct, including improved internal controls and the use of technology. Insights from a KPMG poll highlight the current state of procurement practices among industry professionals, indicating a need for more comprehensive strategies to address fraud.