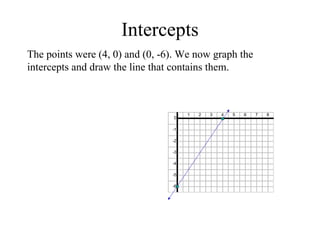
The document discusses intercepts in linear equations. It defines an x-intercept as the x-coordinate where the graph of the linear equation crosses the x-axis. The y-intercept is defined as the y-coordinate where the graph crosses the y-axis. To find the intercepts of a linear equation, set y=0 and solve for x to find the x-intercept, or set x=0 and solve for y to find the y-intercept. An example finds the intercepts of y=3/2x - 6 by setting each variable equal to 0 and solving, finding the x-intercept to be 4 and the y-intercept to be -6.