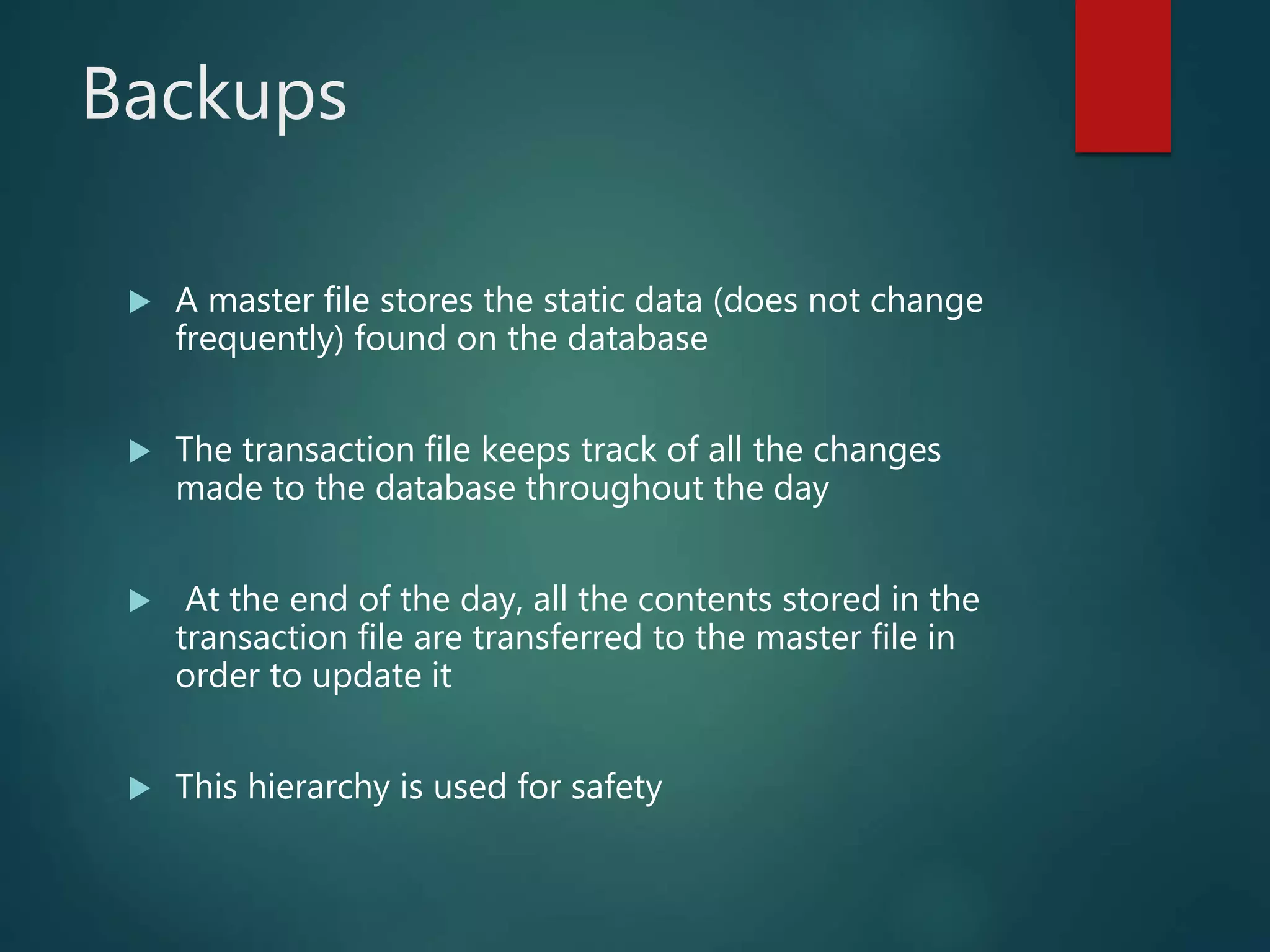
Data security involves keeping information private by using methods to ensure confidentiality, integrity, and availability of data. It is important for businesses that hold confidential information. Data is backed up and stored hierarchically for safety. Software uses measures like intrusion detection systems, user IDs, passwords, biometrics, encryption, and digital signatures and certificates to protect data. Downloading pirated software poses legal and ethical issues and risks to users. Developers employ serial numbers, activation keys, copy protection, and hardware keys to protect their software and encourage users to register for updates and support.