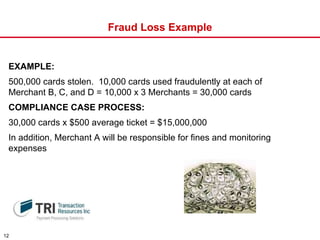
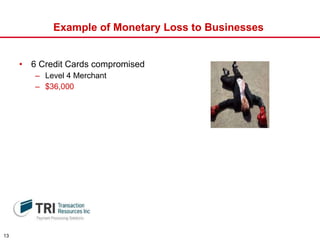
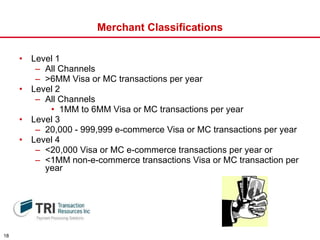
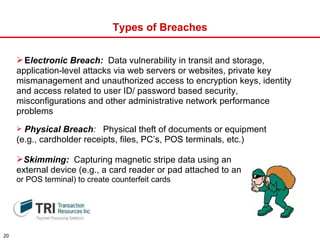
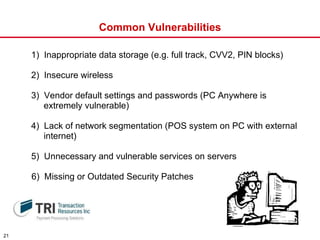
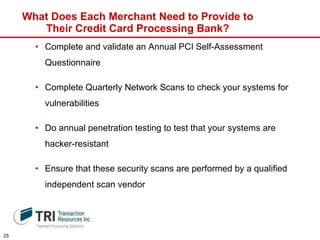
The document discusses PCI DSS compliance requirements for businesses that accept credit cards. It covers what PCI DSS is, who it applies to, how compliance is achieved, why the standards were established, impacts of non-compliance such as fraud and fines, and steps businesses need to take to protect customer payment data and stay compliant.