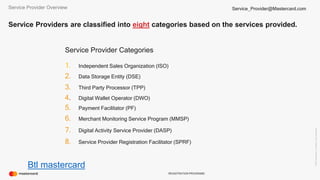
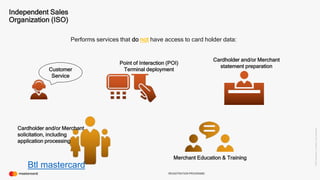
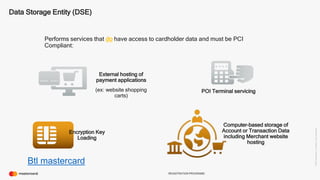
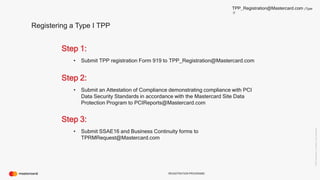
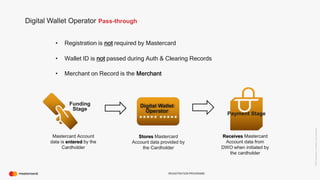
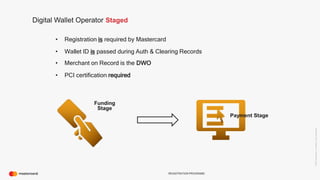
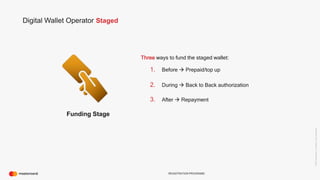
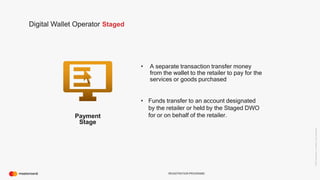
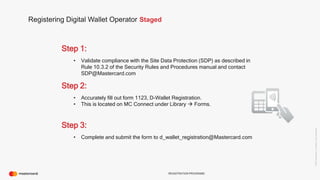
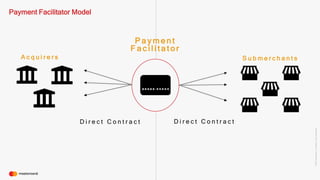
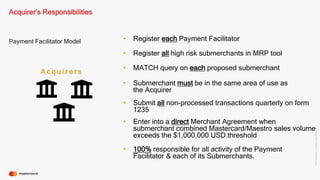
The document provides an overview of MasterCard's registration programs for service providers involved in payment processing, detailing the types and requirements for service providers such as Independent Sales Organizations, Third Party Processors, and Digital Wallet Operators. It outlines the registration process and compliance obligations for each category, including PCI compliance and due diligence for payment facilitators. The document also discusses the responsibilities of acquirers and the impact on cardholder experiences in various marketplace scenarios.