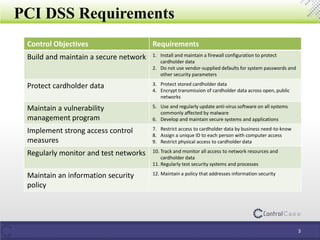
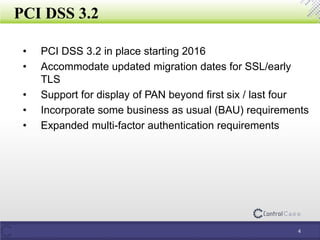
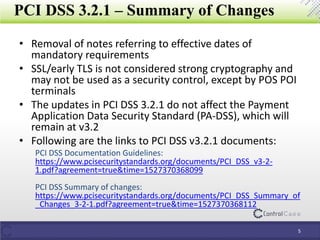
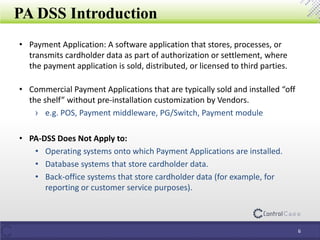
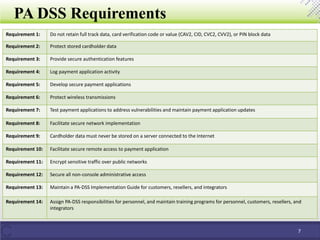
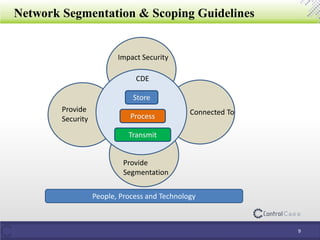
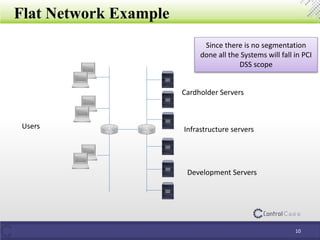
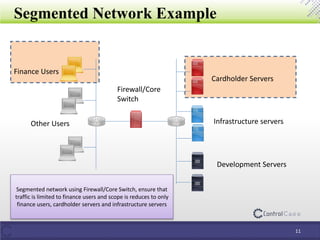
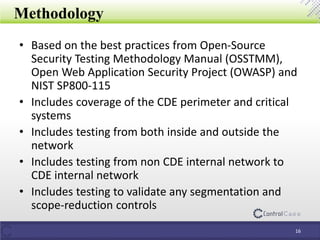
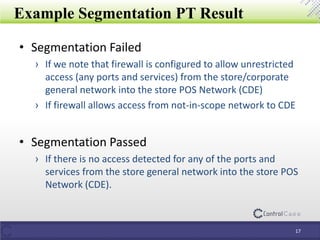
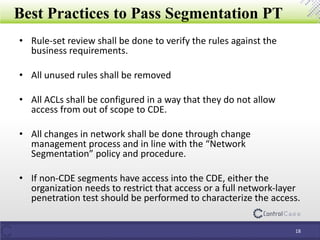
The document details the Payment Card Industry Data Security Standard (PCI DSS) and Payment Application Data Security Standard (PA DSS), outlining guidelines for securely processing and protecting cardholder data. It provides requirements for network security, vulnerability management, access control, and data protection, as well as changes in versions 3.2 and 3.2.1 of PCI DSS. Additionally, it emphasizes the importance of network segmentation, penetration testing, and data discovery for maintaining compliance and reducing risks of data breaches.