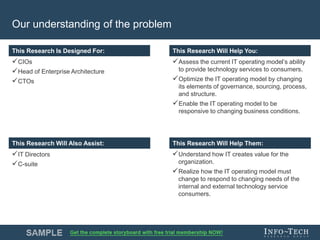
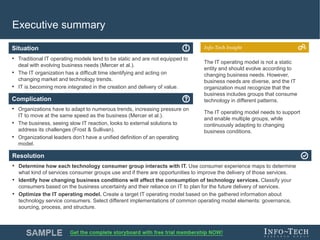
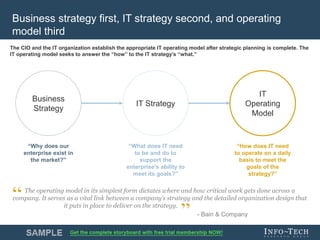
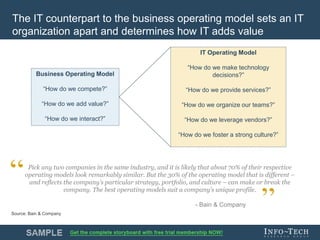
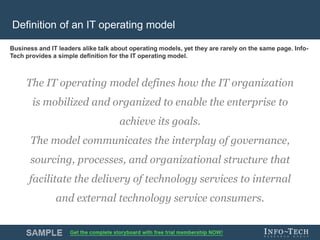
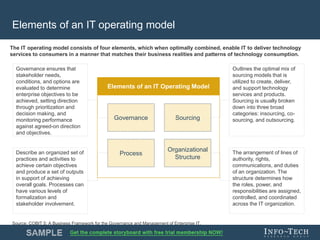
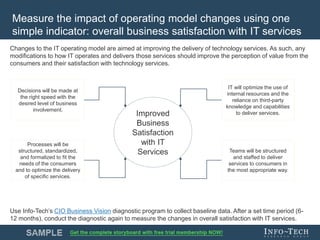
Info-Tech Research Group is a leading provider of IT research and advisory services, offering insights and tools to optimize IT operating models for diverse technology service consumers. The organization emphasizes the need for IT operating models to evolve with changing business conditions, advocating for a dynamic approach rather than static structures. Additionally, it outlines key elements such as governance, sourcing, processes, and organizational structure that support effective technology service delivery.