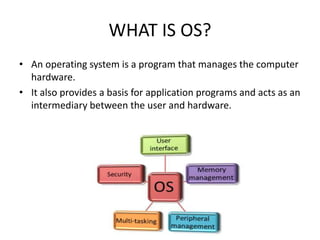
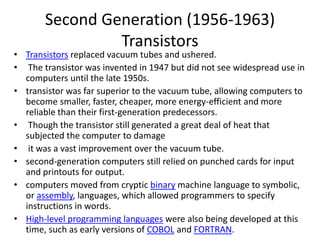
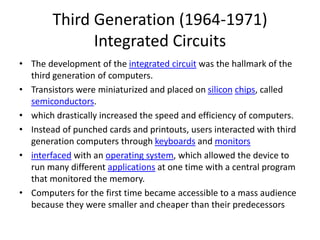
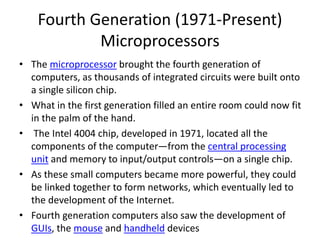
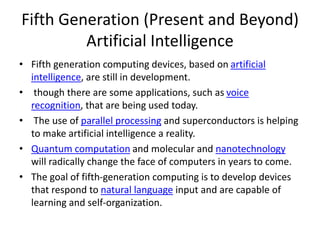
An operating system manages computer hardware and acts as an intermediary between the user and hardware. Operating systems have evolved through five generations from vacuum tubes to integrated circuits and now artificial intelligence. The first generation used vacuum tubes and magnetic drums, were room-sized, and could only solve one problem at a time. Later generations introduced transistors, integrated circuits, and microprocessors, making computers smaller, faster, and more powerful. Operating systems also evolved from batch processing to multiprogramming, multitasking, time-sharing, and real-time systems to better utilize resources and improve user interaction and response times.