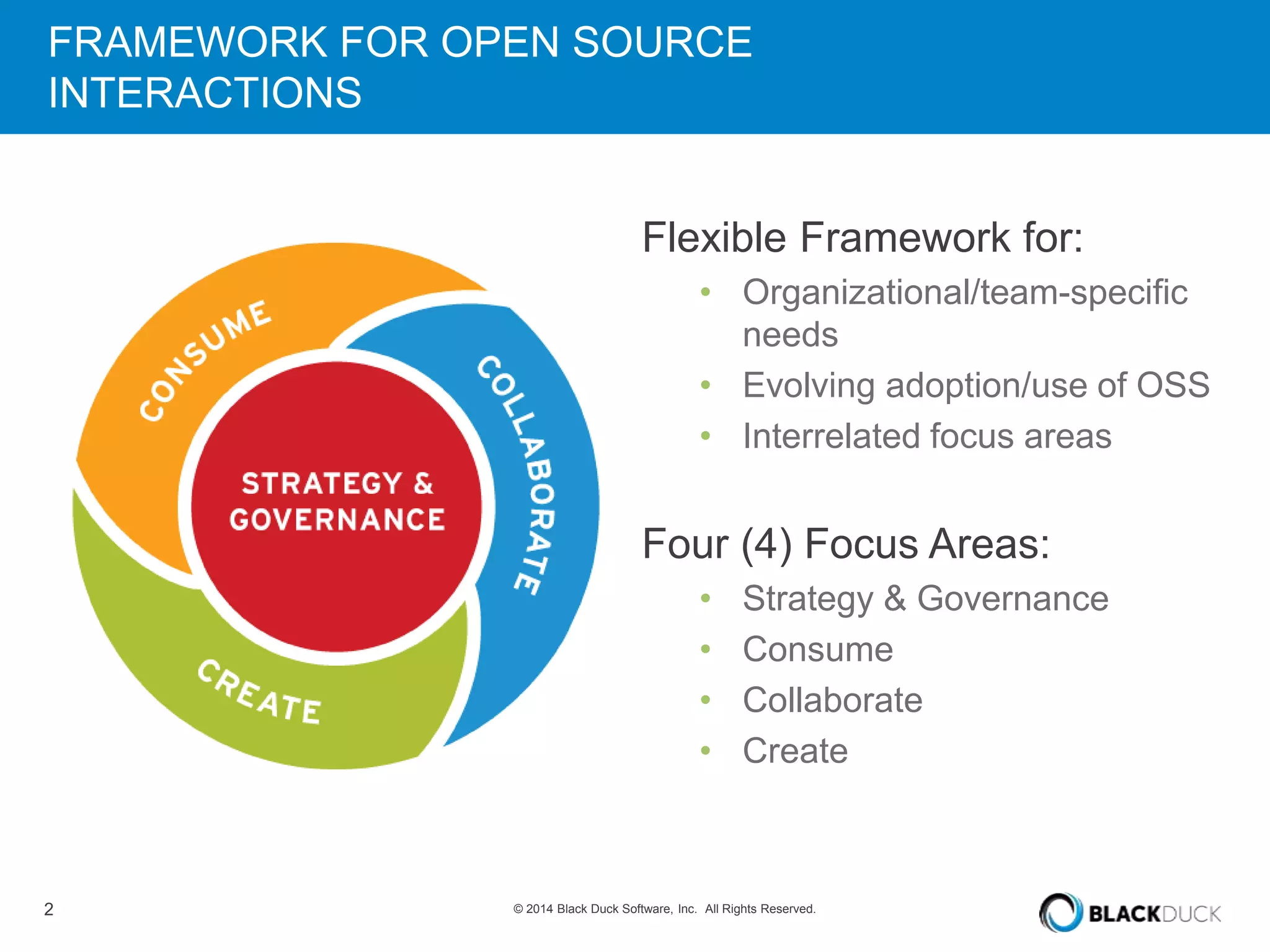
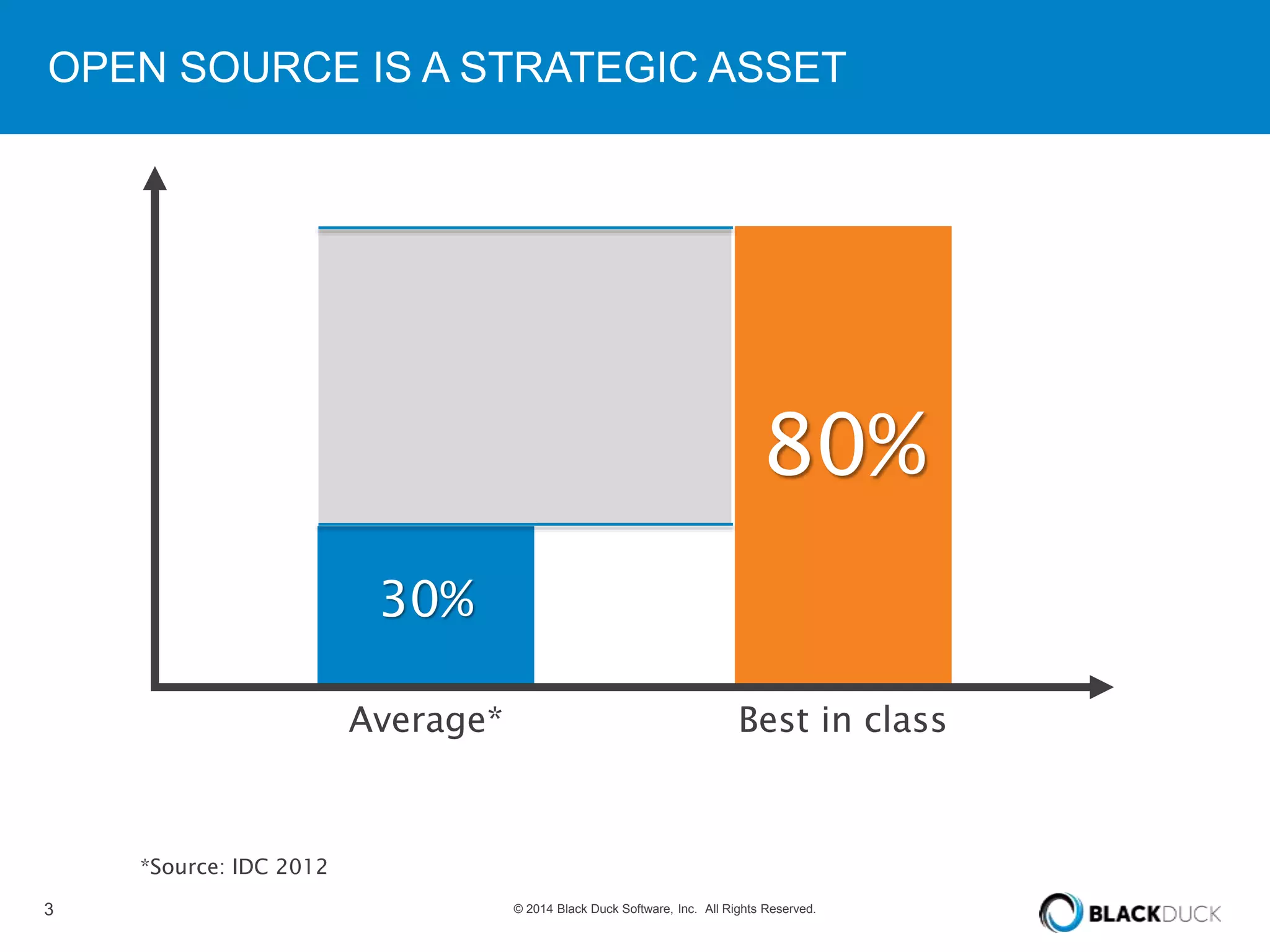
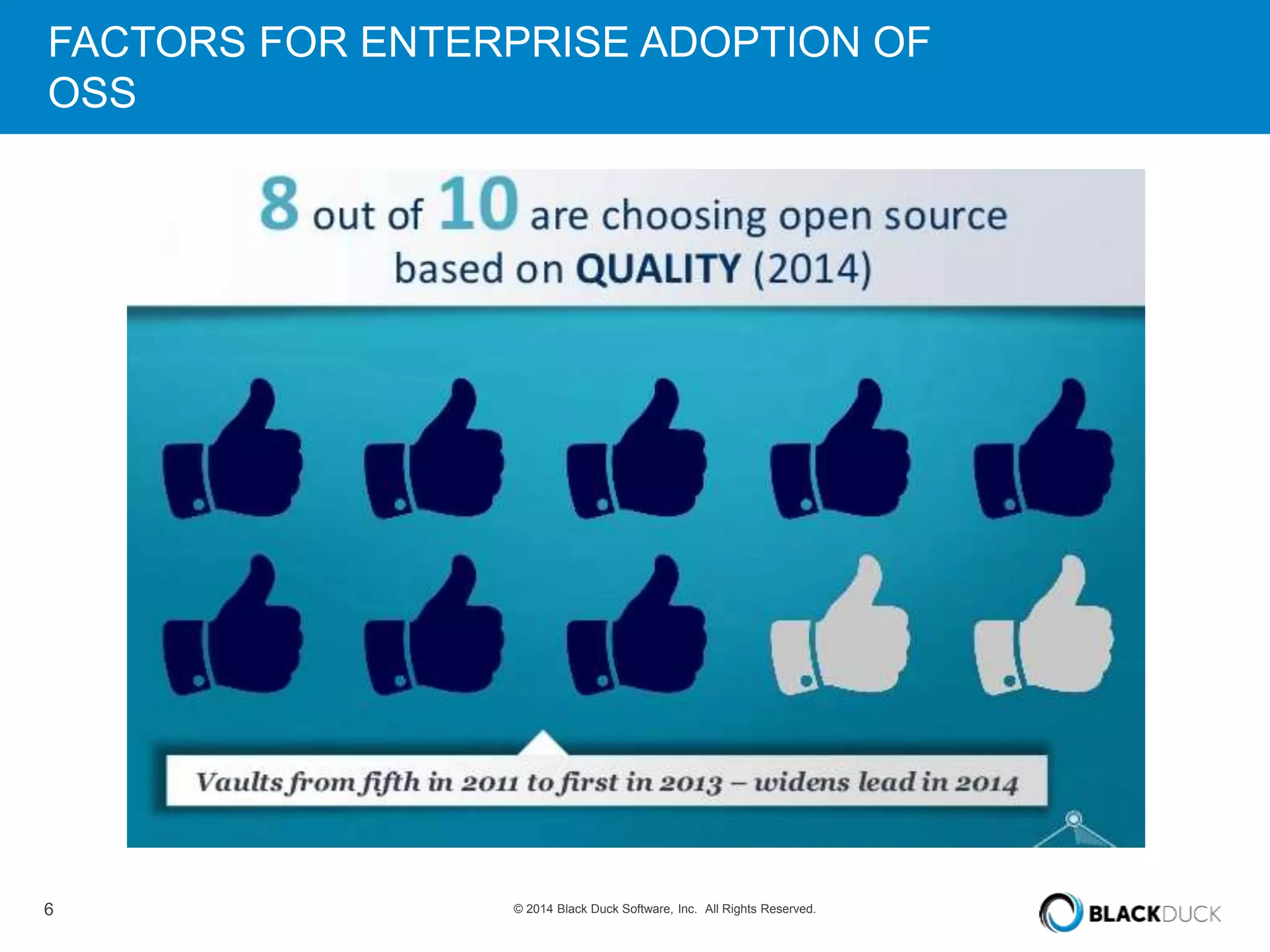
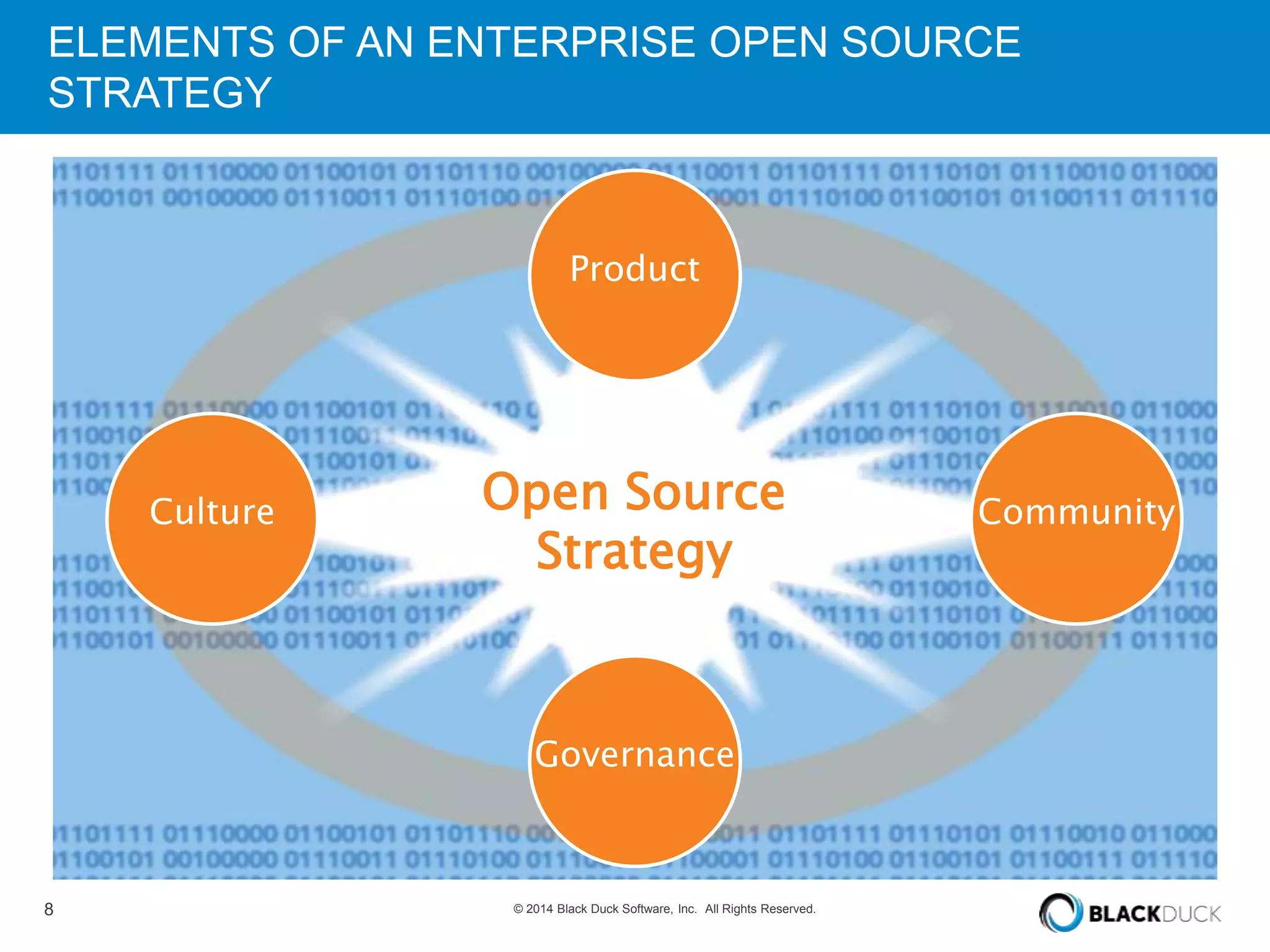
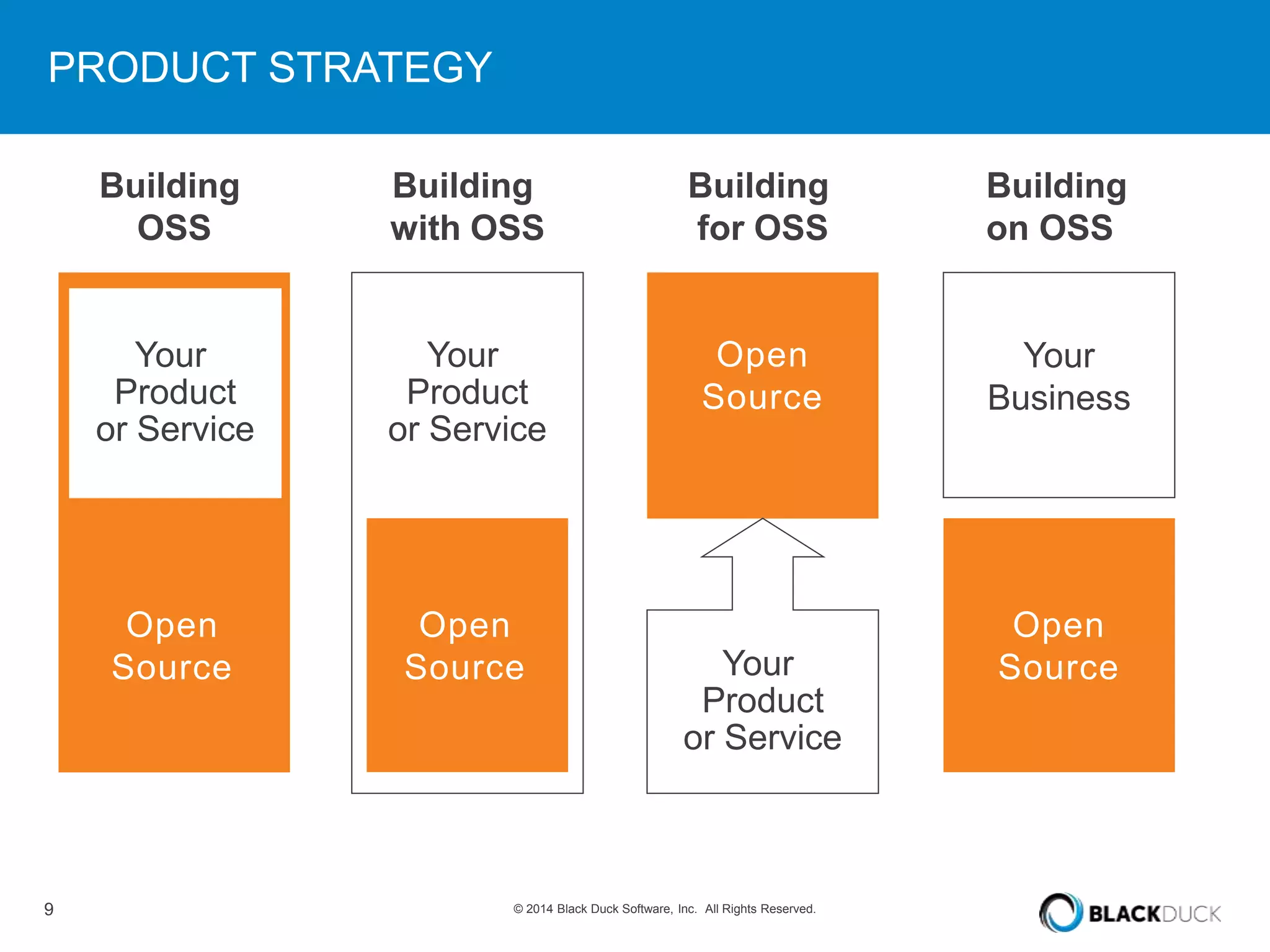
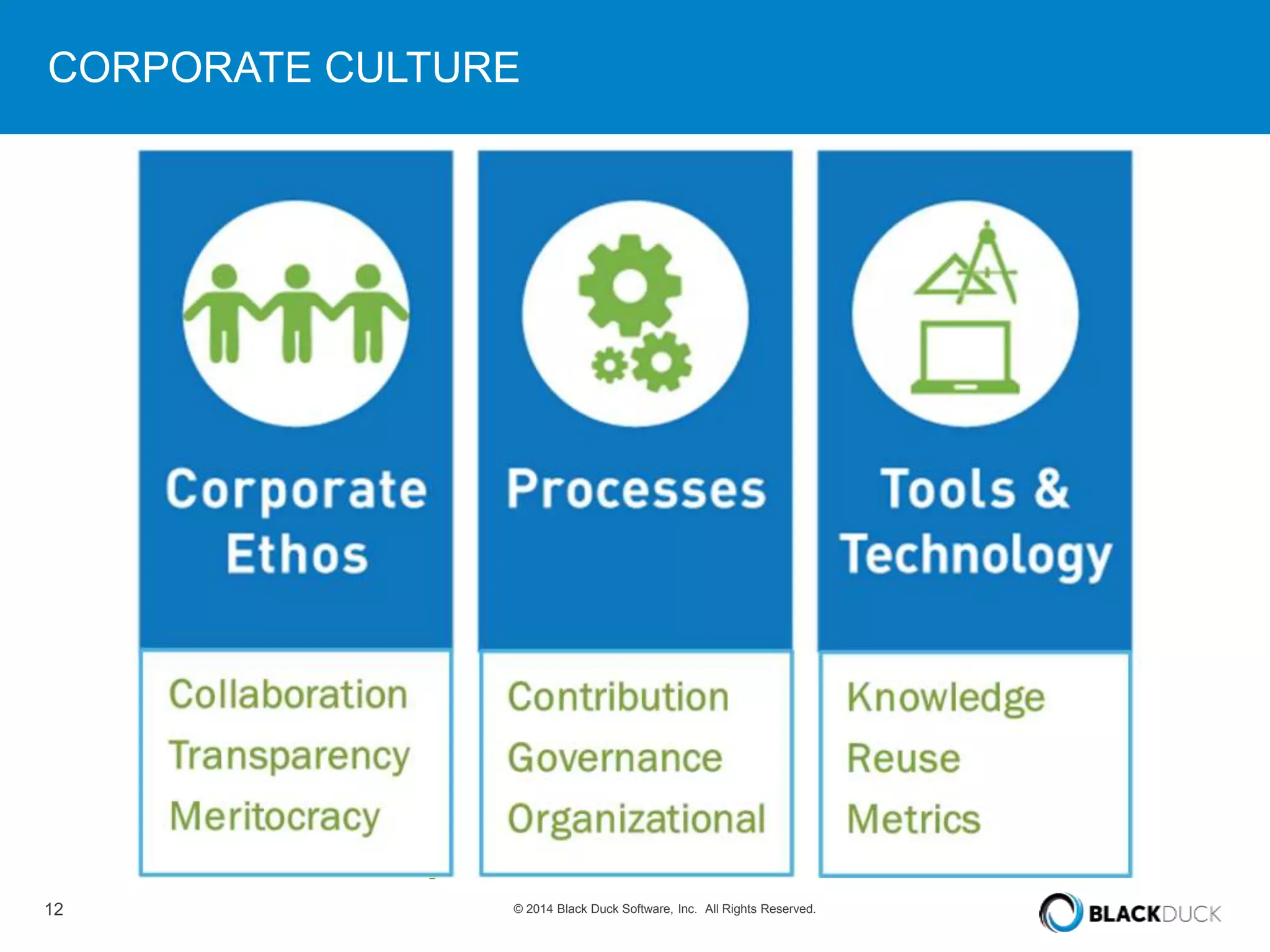
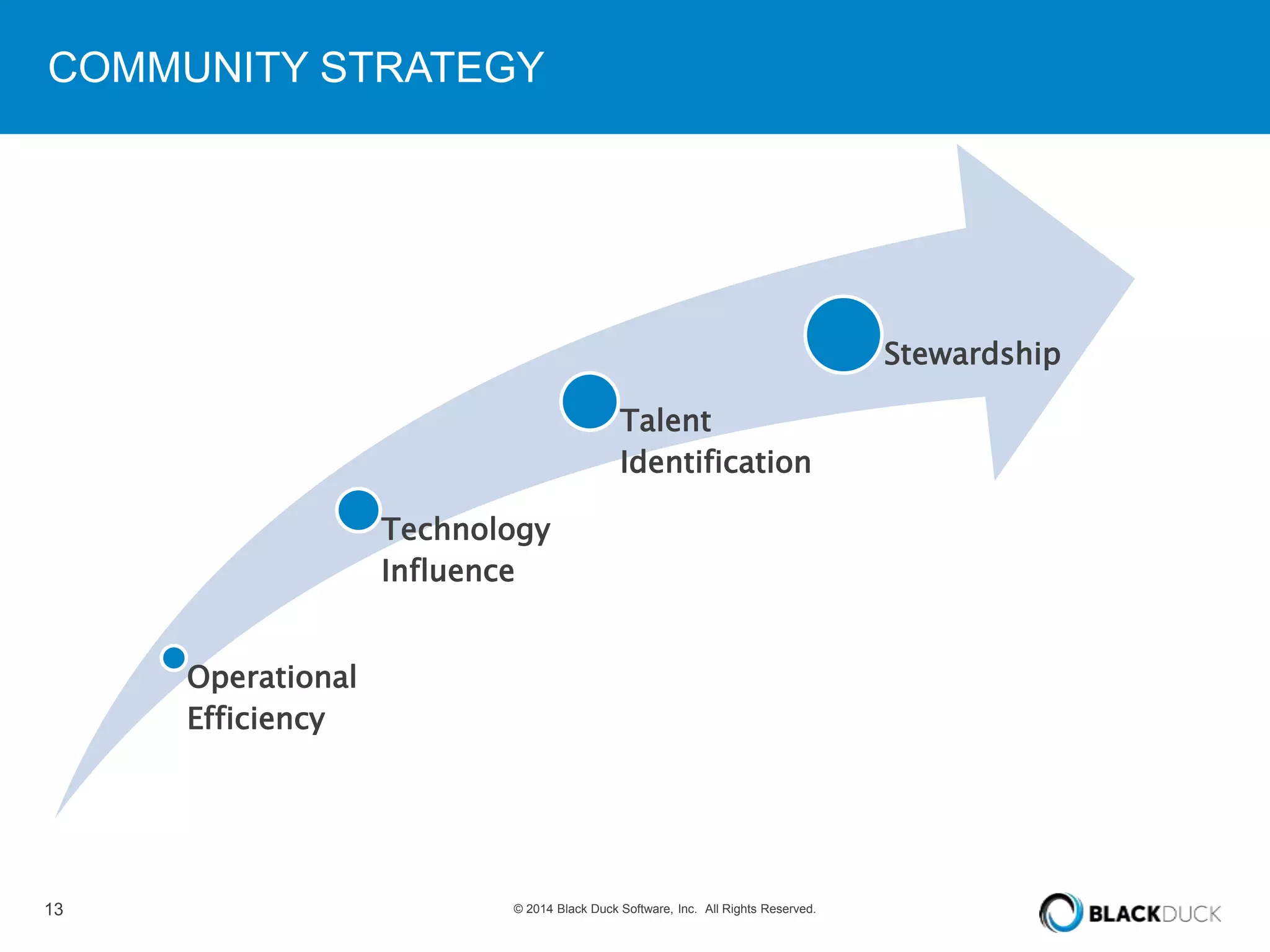
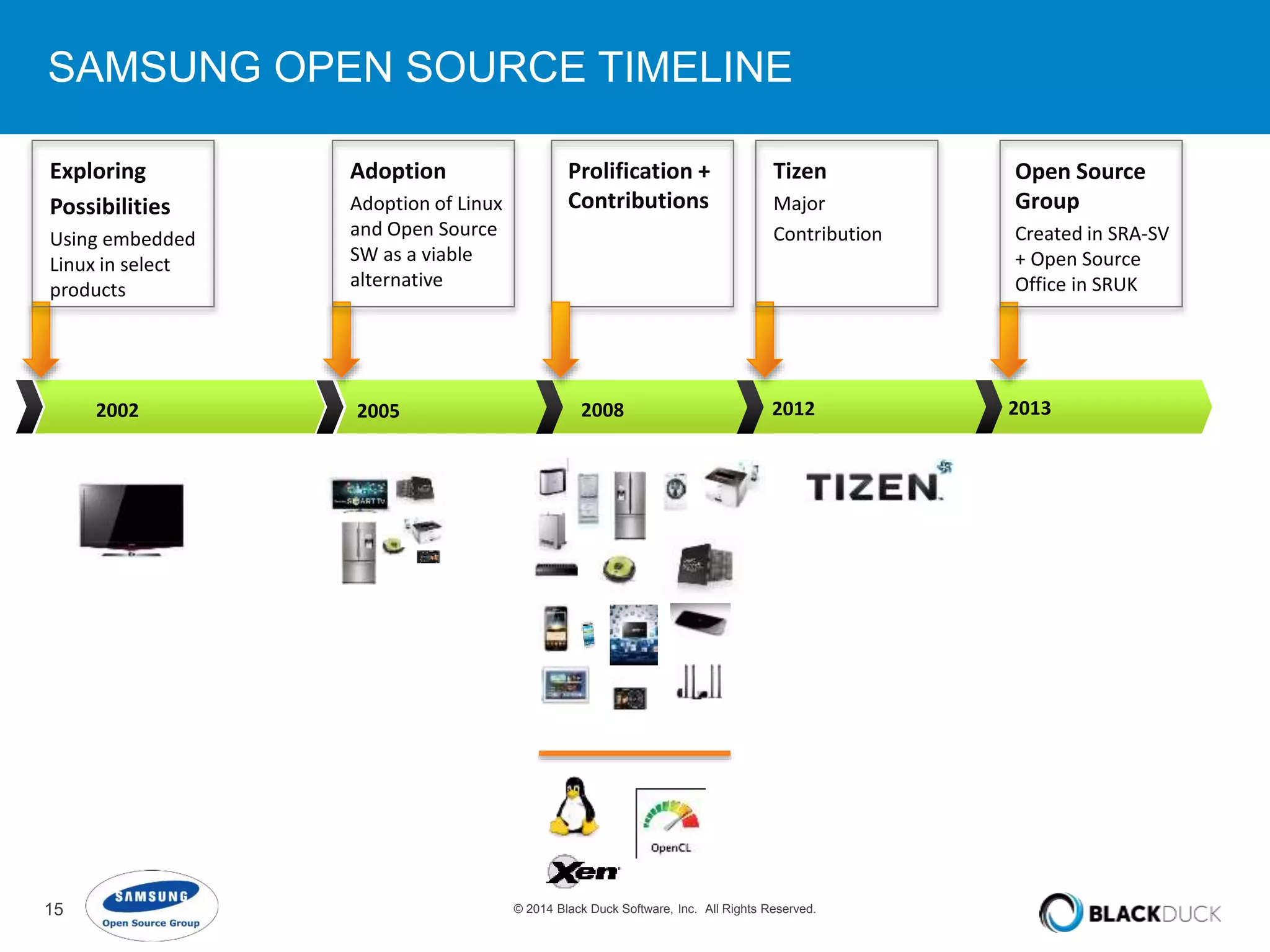
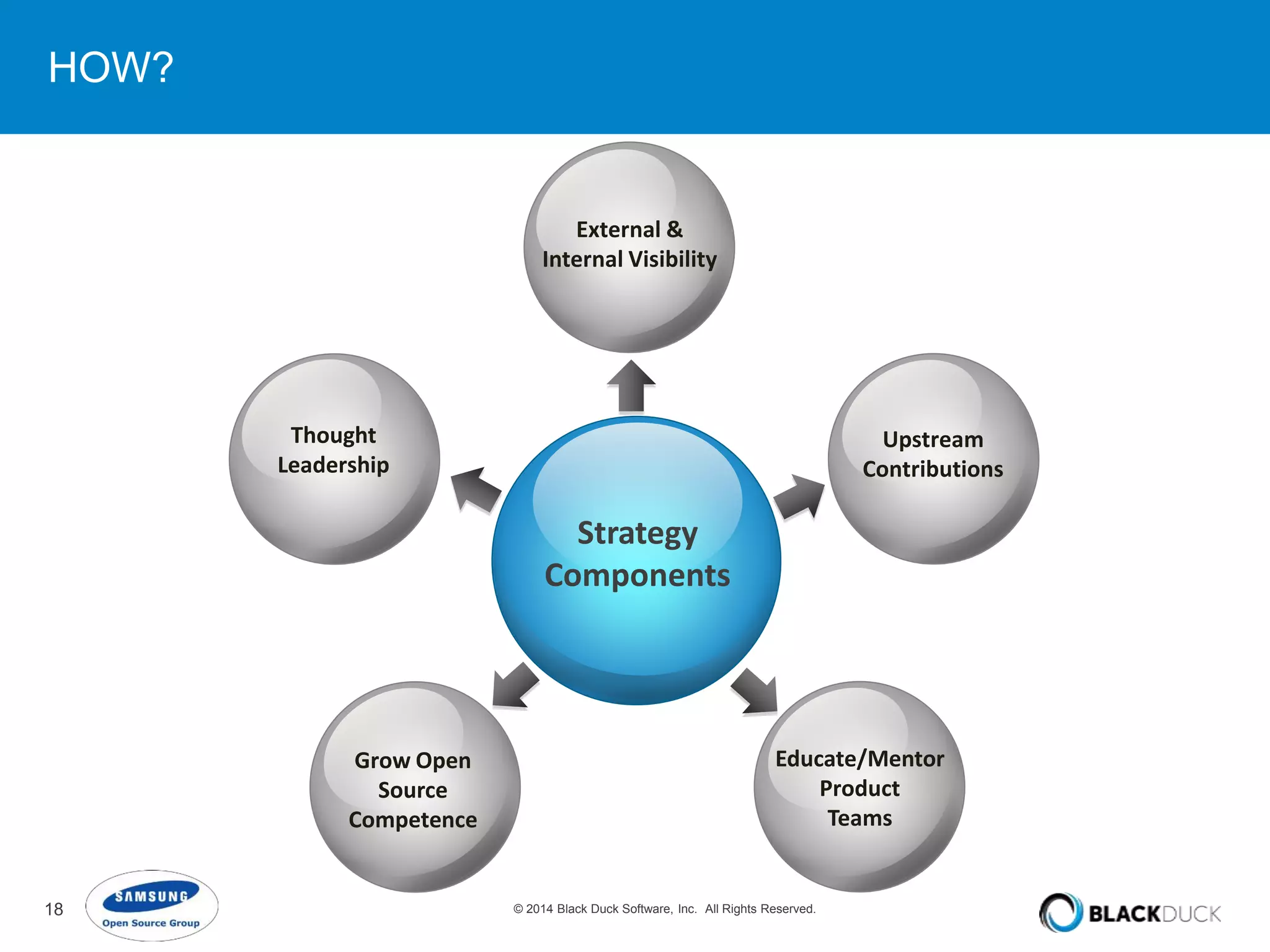
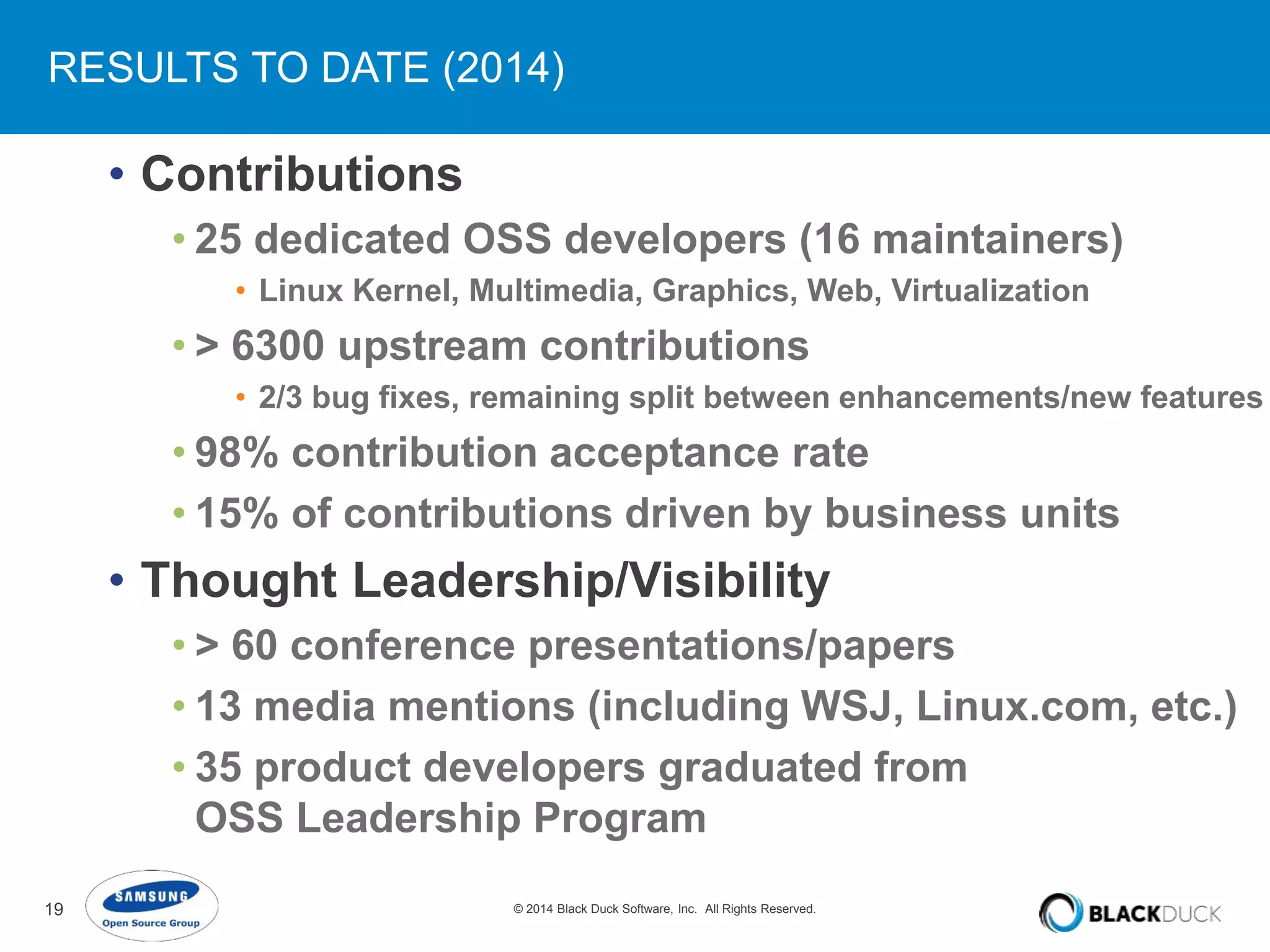
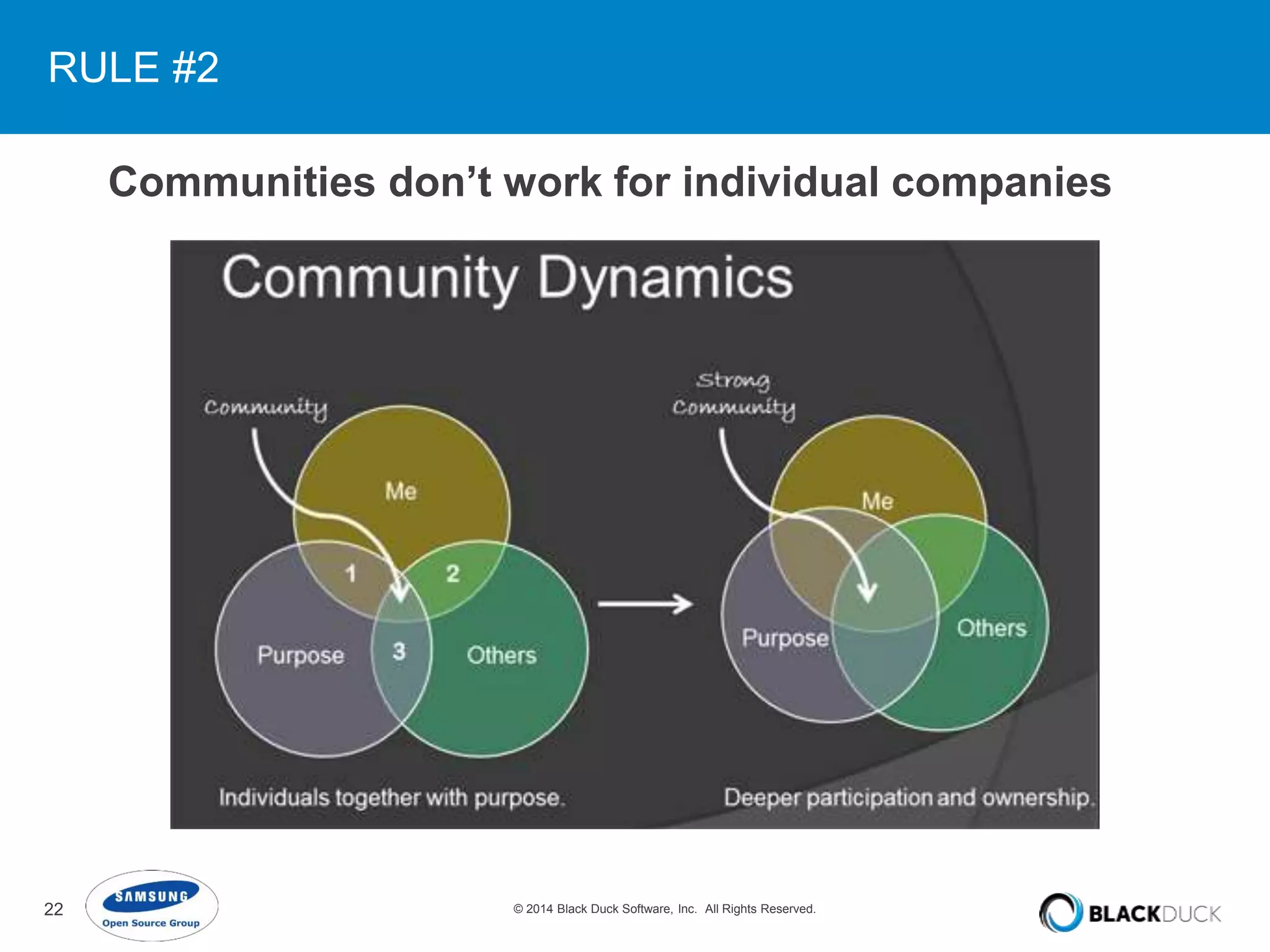
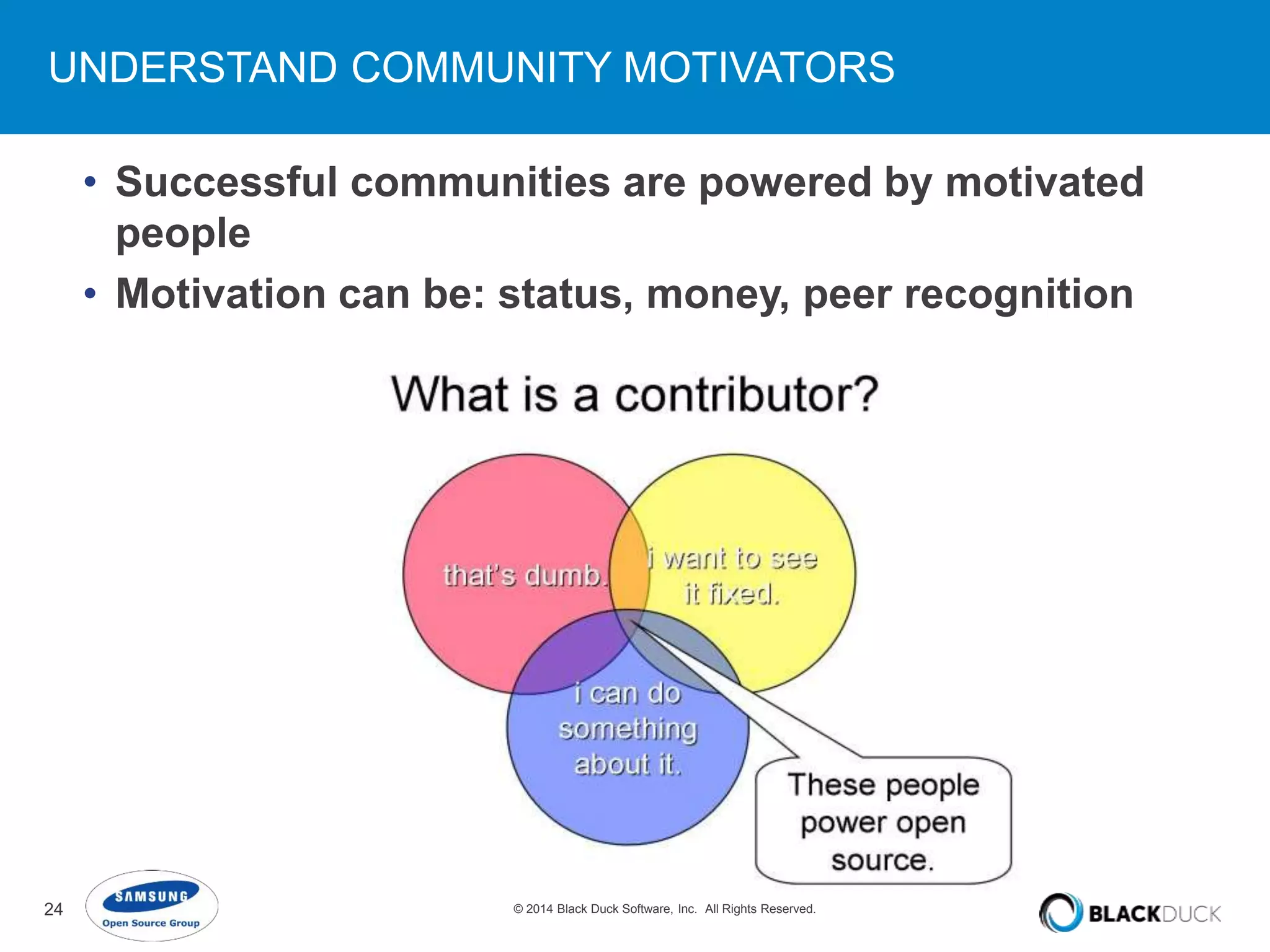
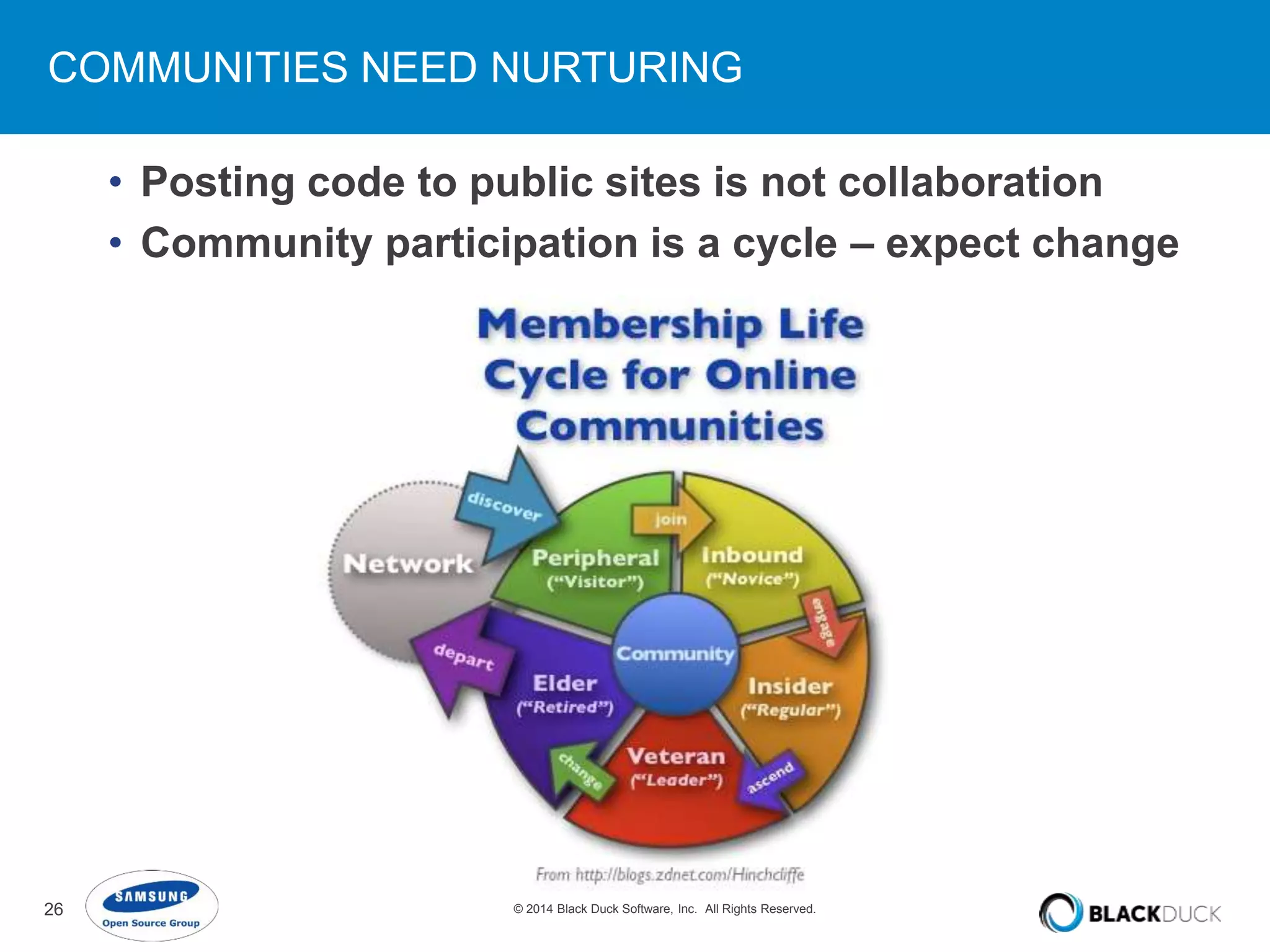
The document discusses the integration of open source into corporate strategy, outlining a flexible framework that includes focus areas such as governance, collaboration, and product strategy. It emphasizes the importance of an open source culture and community engagement for successful adoption and participation in open source projects. Key insights include the need for nurturing communities and understanding community governance and motivators to effectively leverage open source as a strategic business asset.