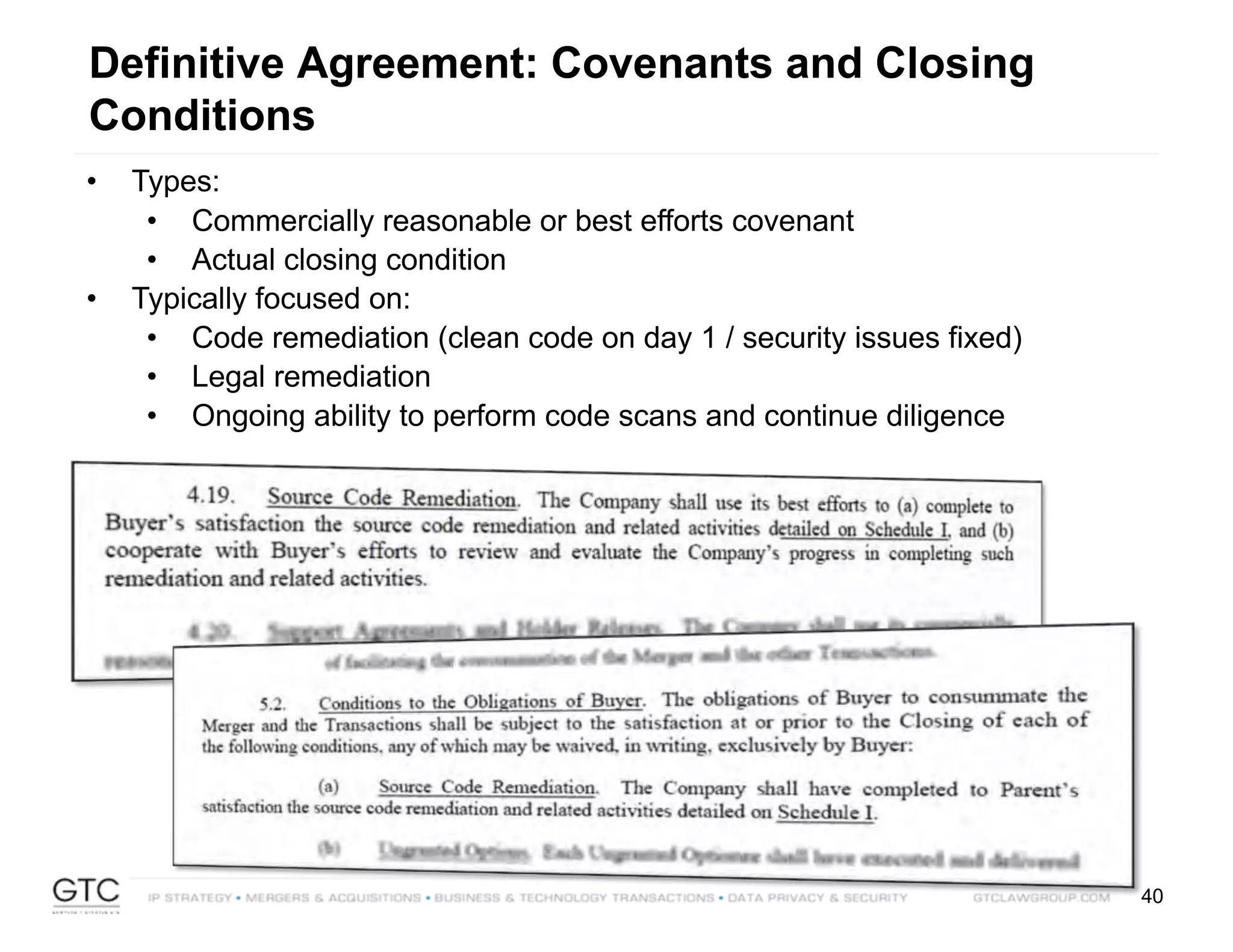
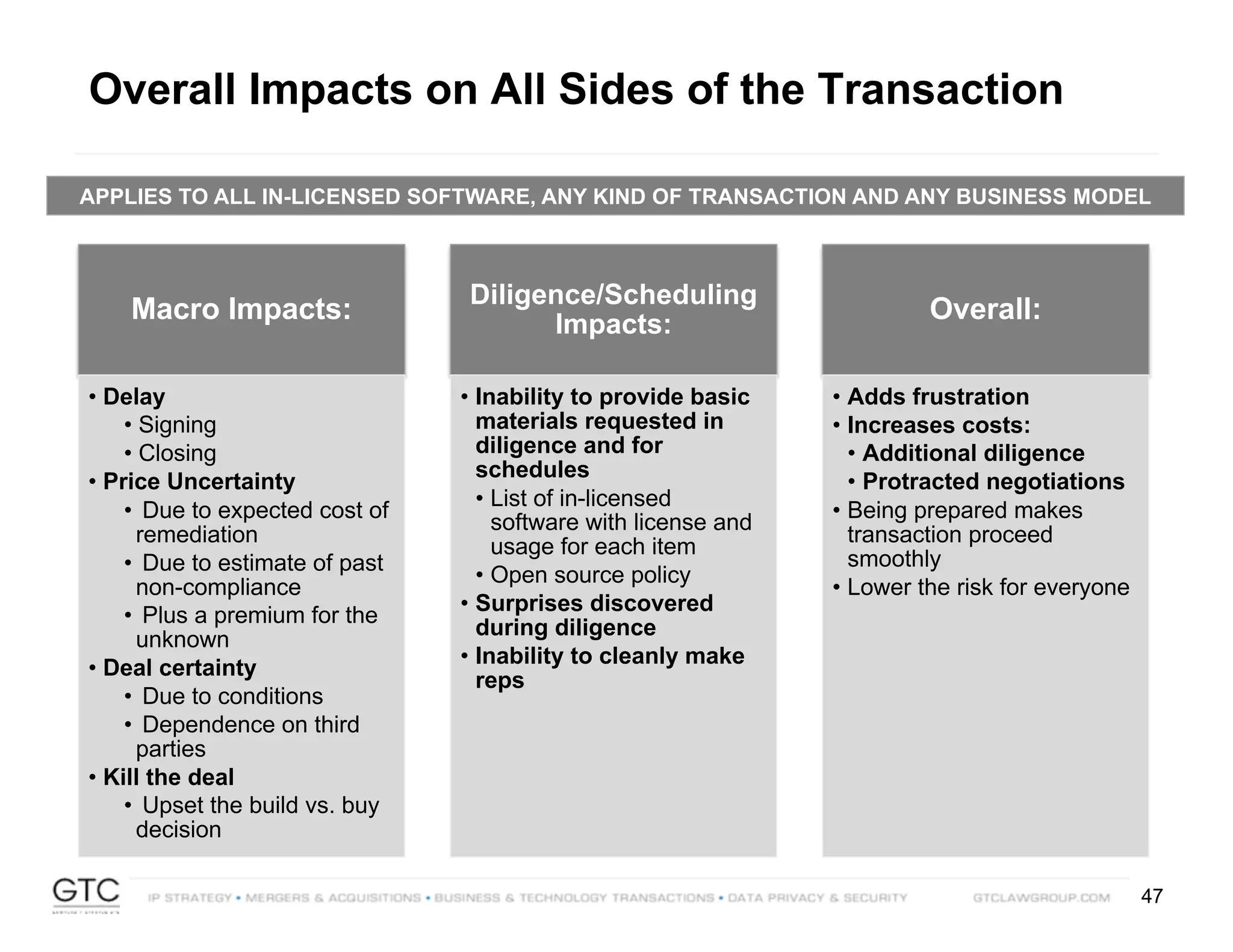
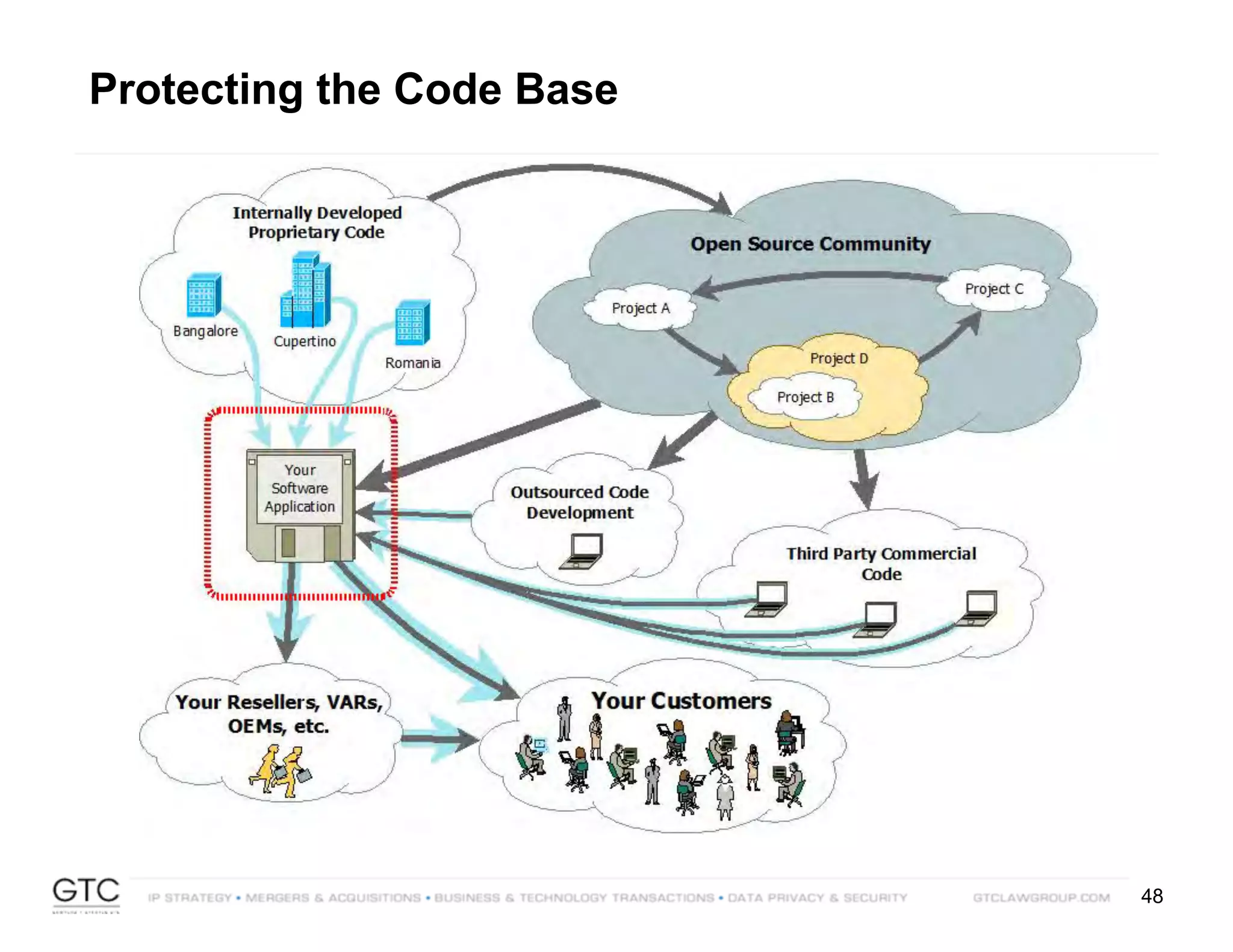
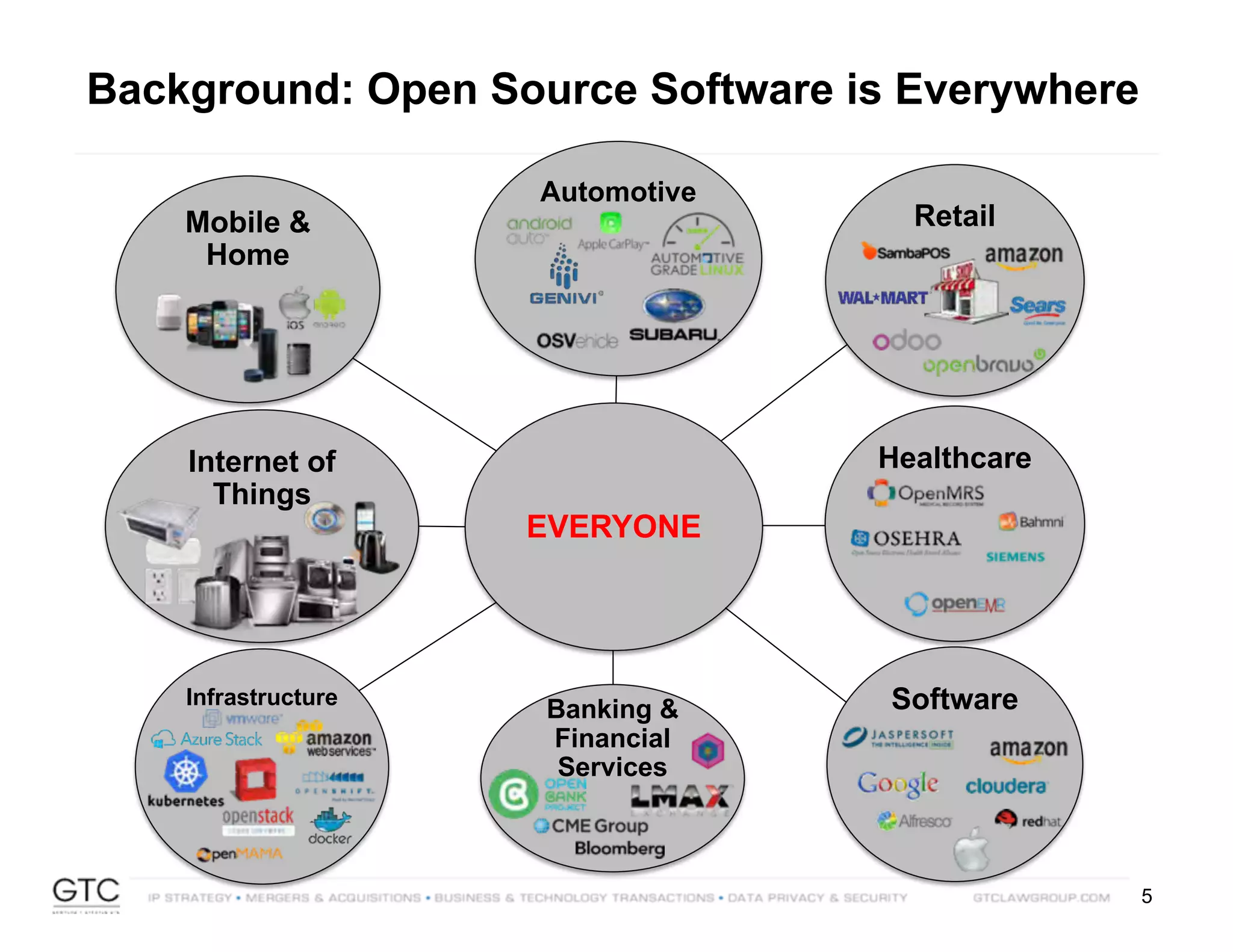
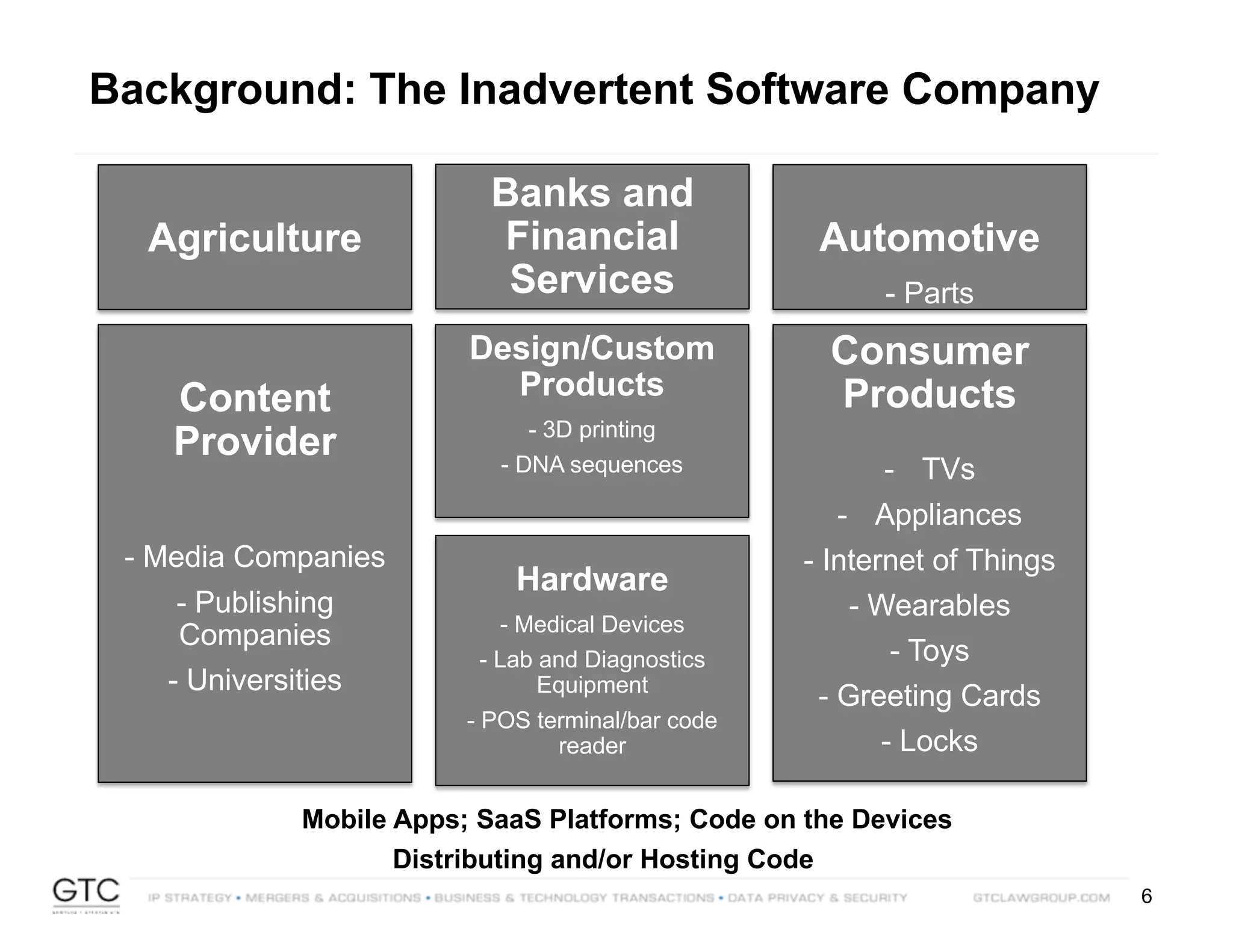
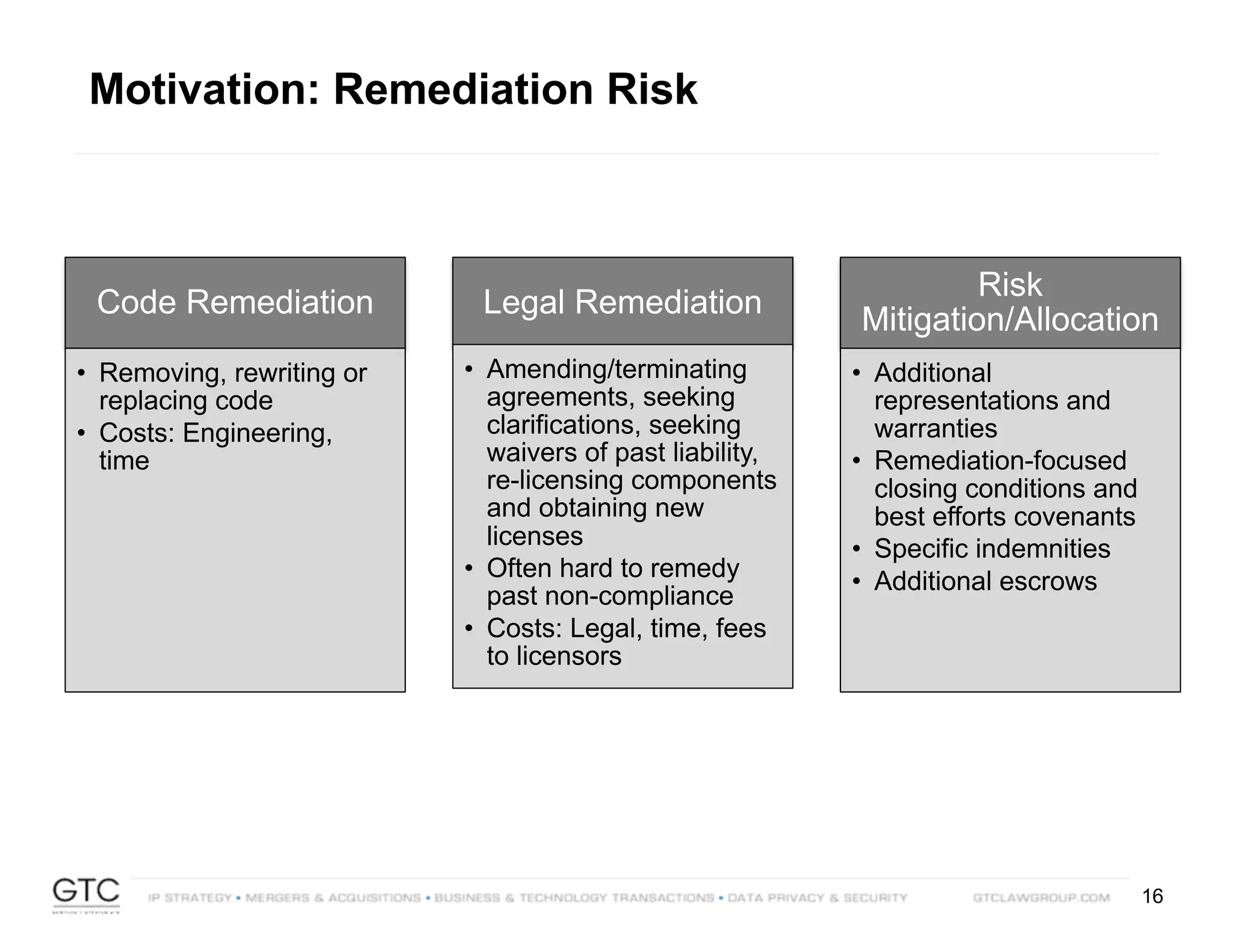
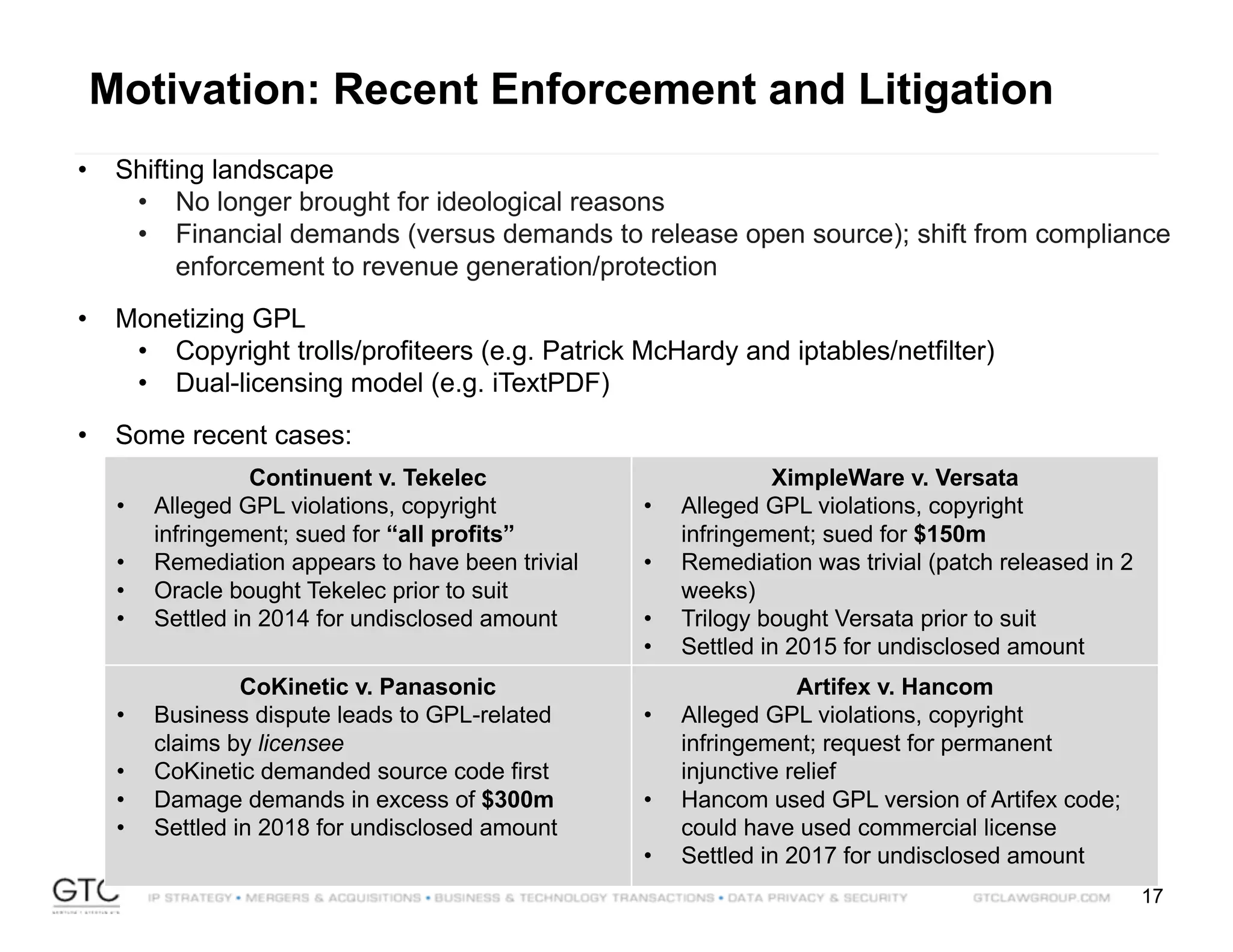
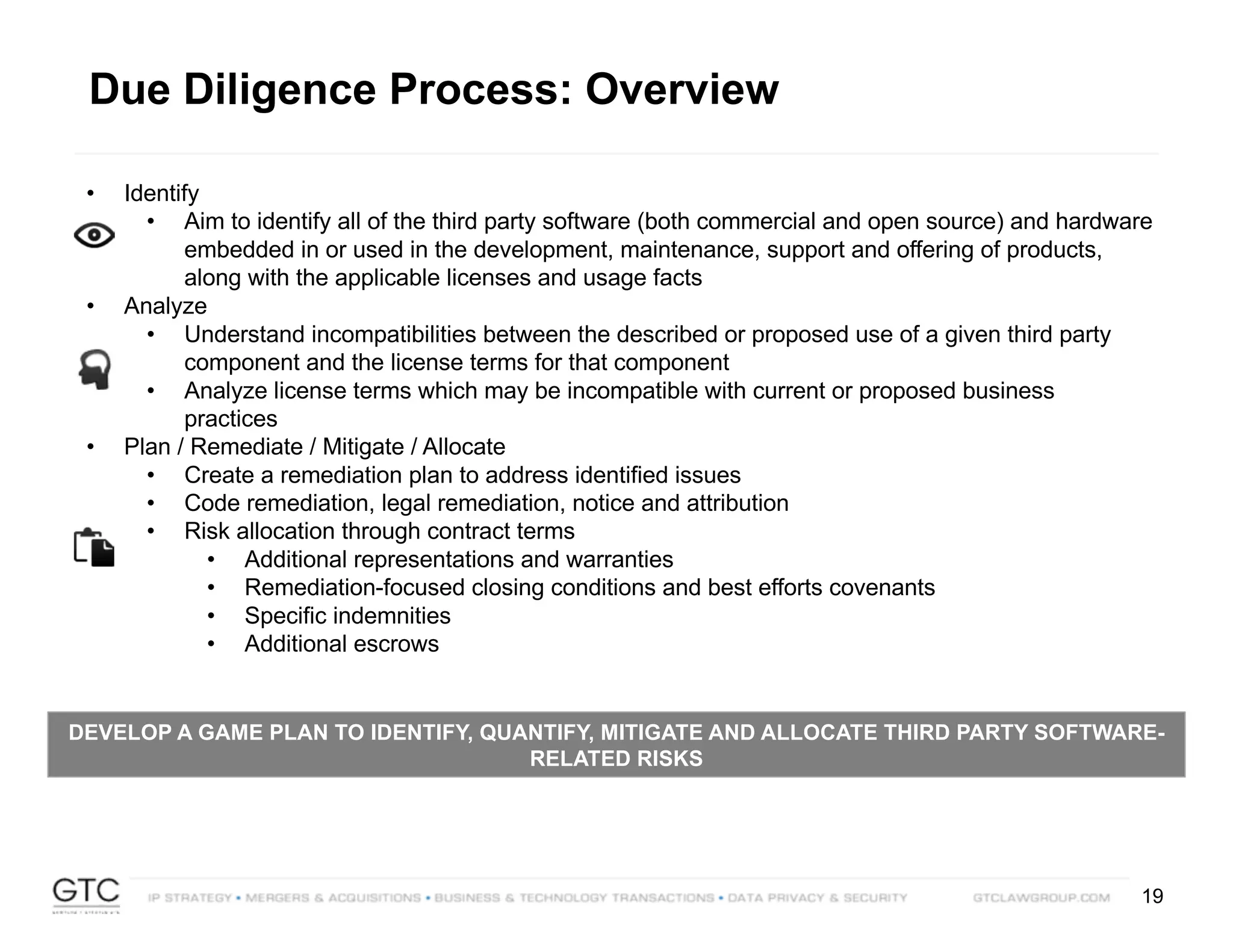
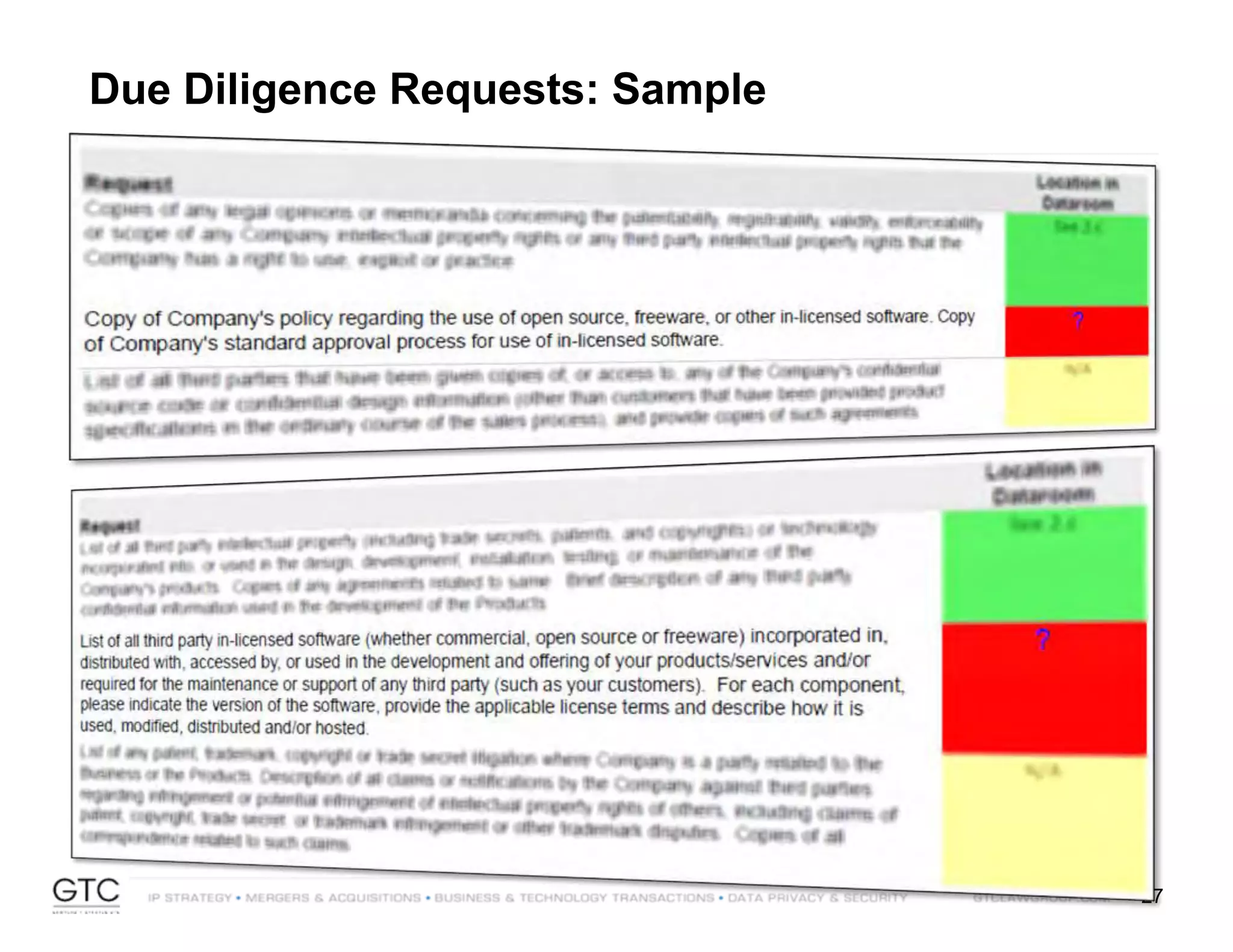
The document discusses the impact of open source software on mergers and acquisitions (M&A), highlighting the associated risks such as licensing, compliance, security, and remediation. It outlines the importance of conducting thorough due diligence to identify third-party software and mitigate risks throughout the transaction process. Key recommendations include establishing an open source policy, conducting code scans, and preparing documentation to ensure smooth transactions and avoid potential legal issues.
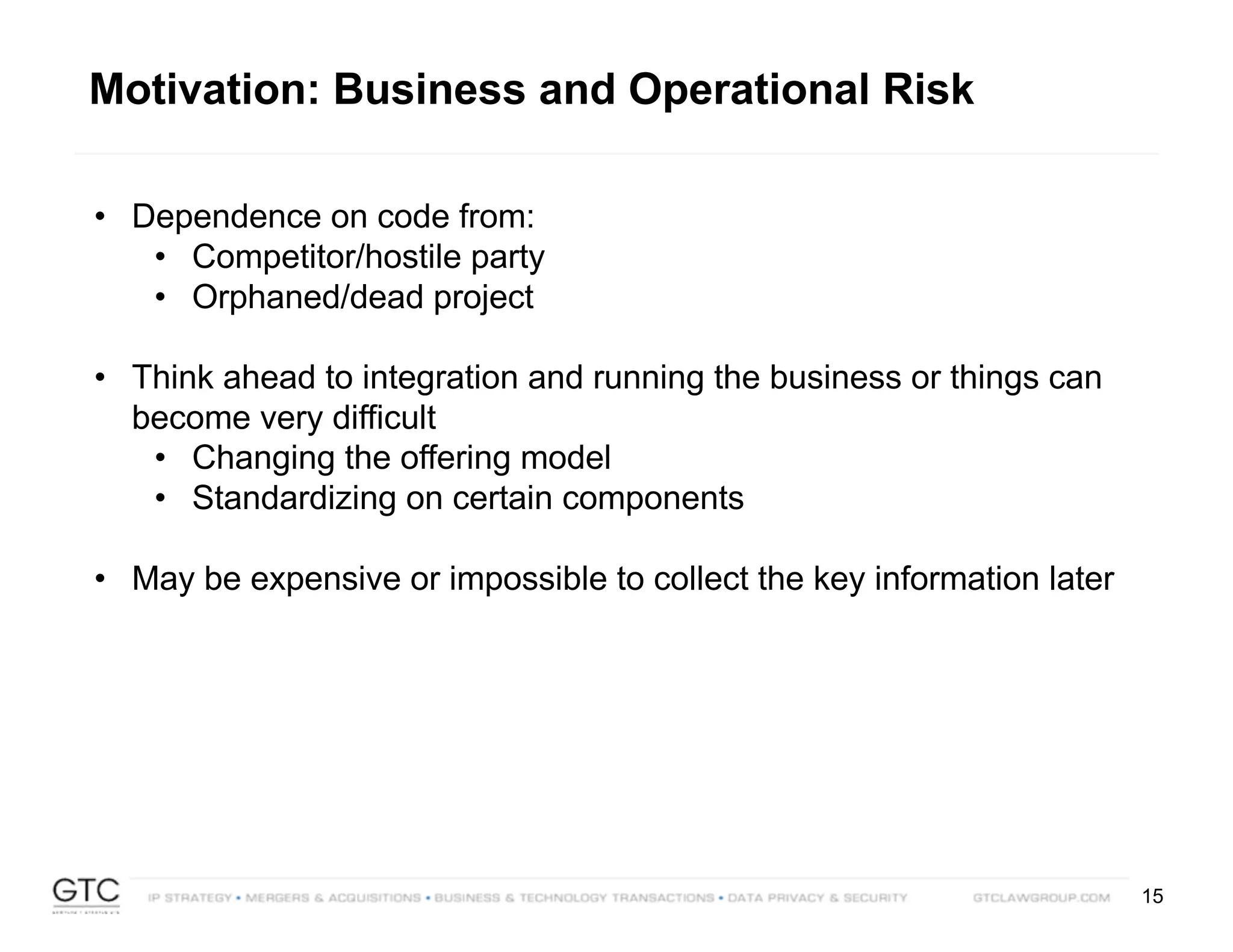
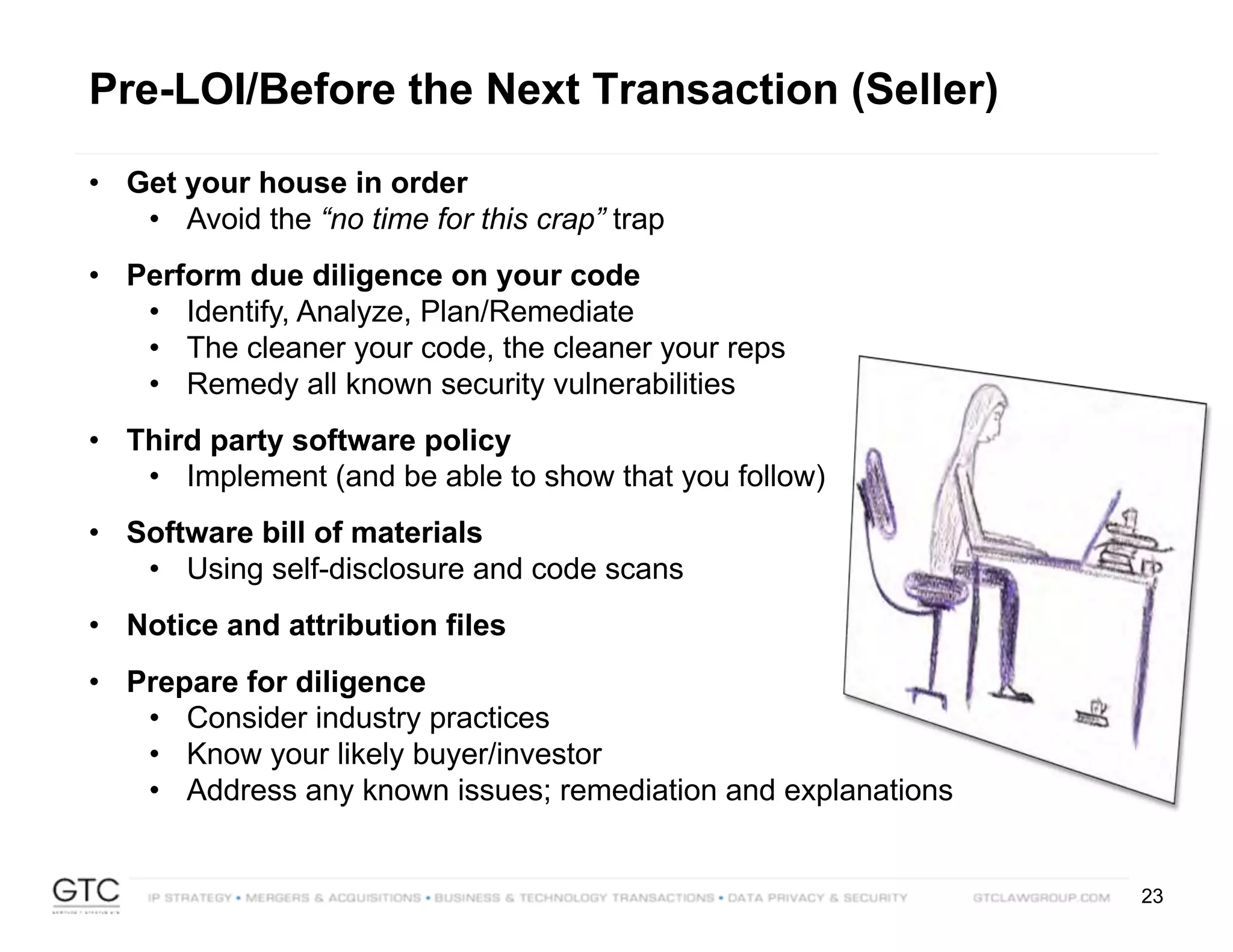
![37
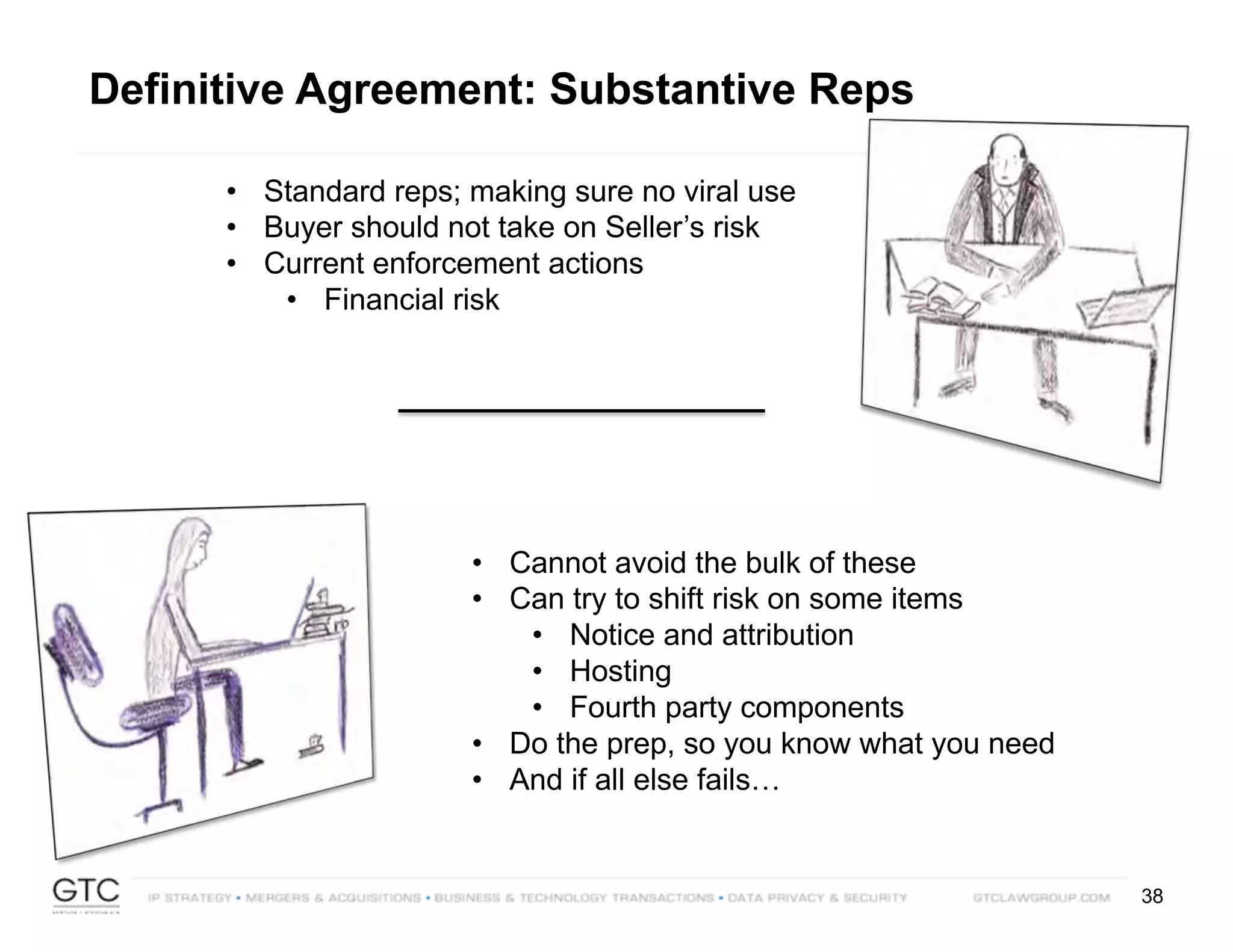
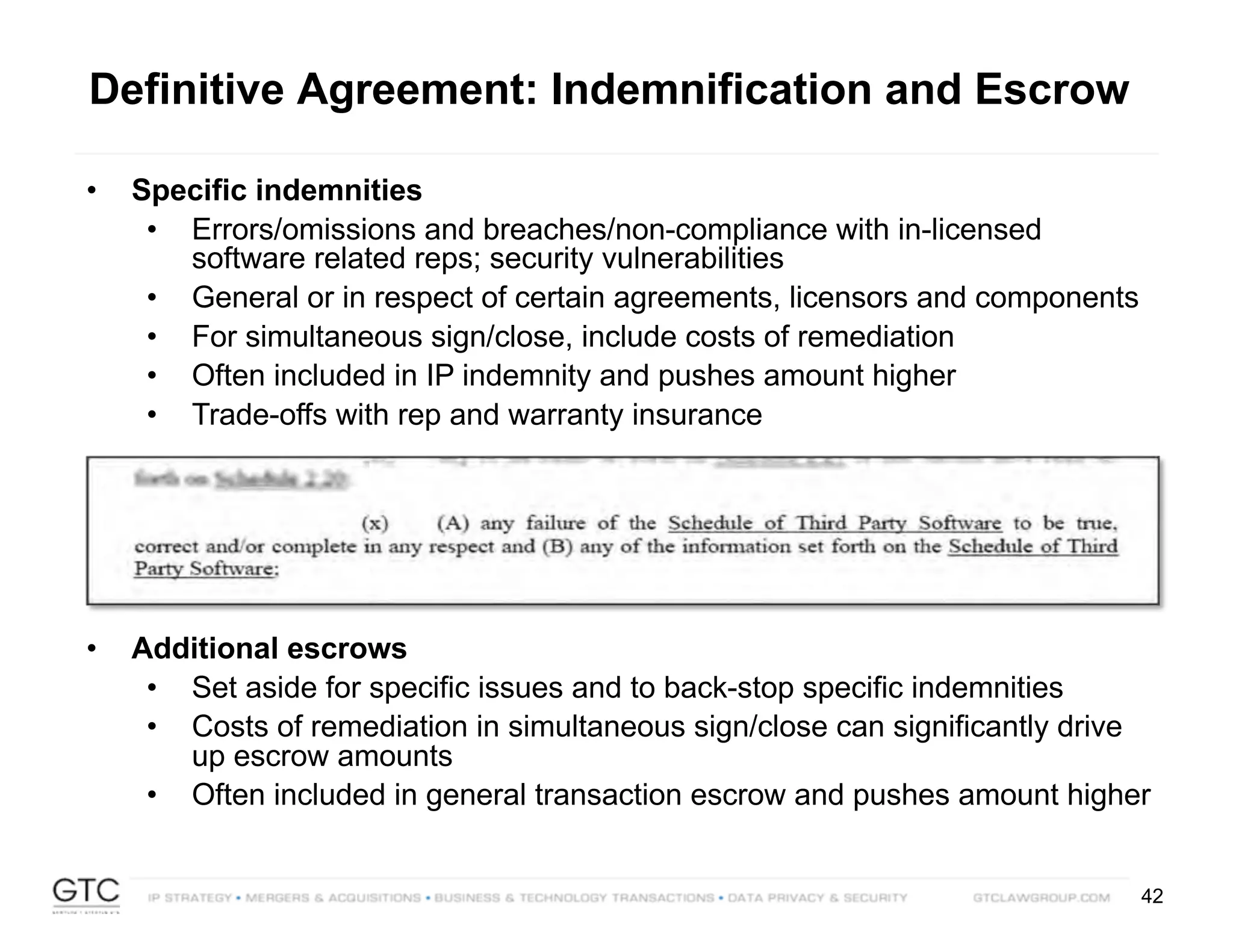
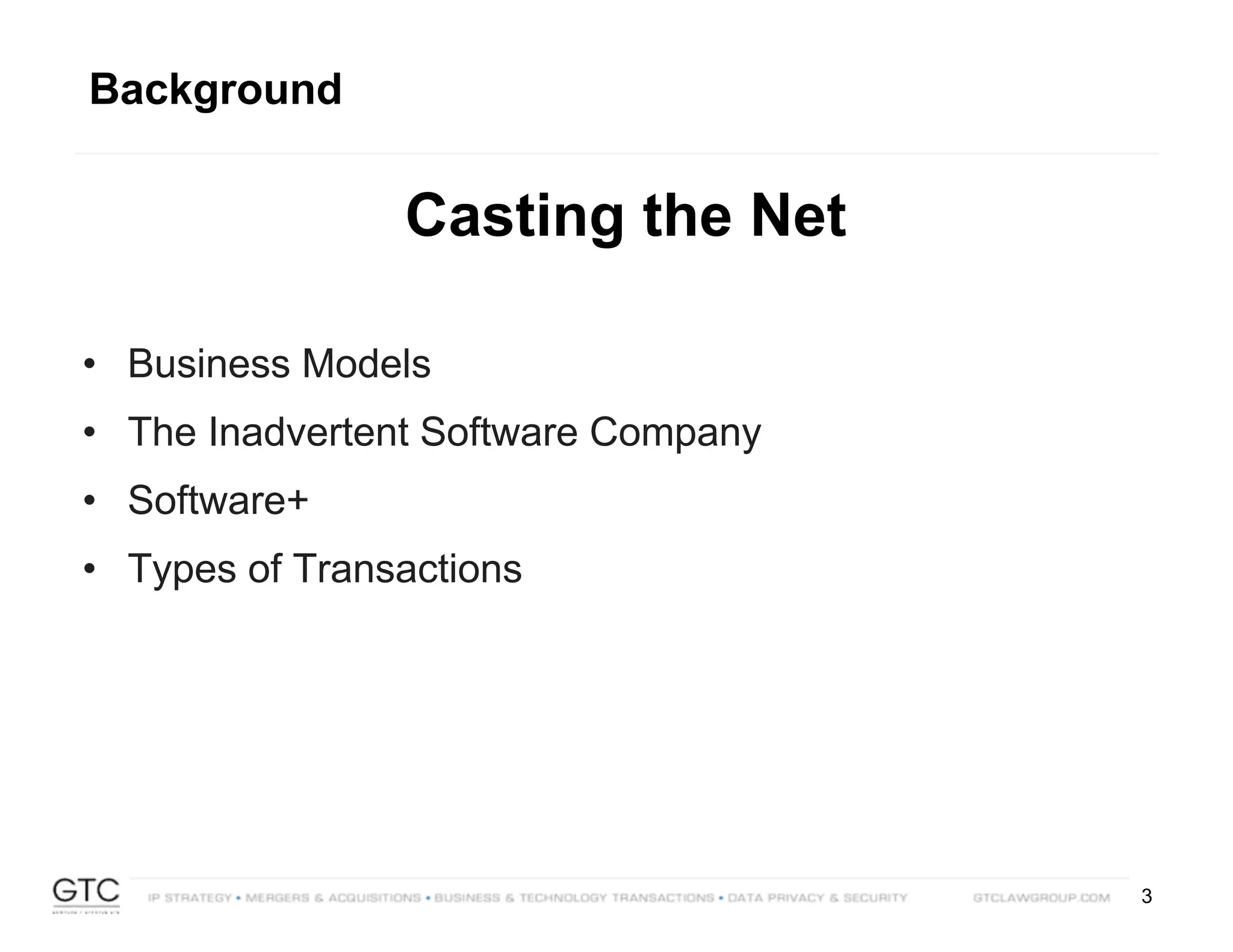
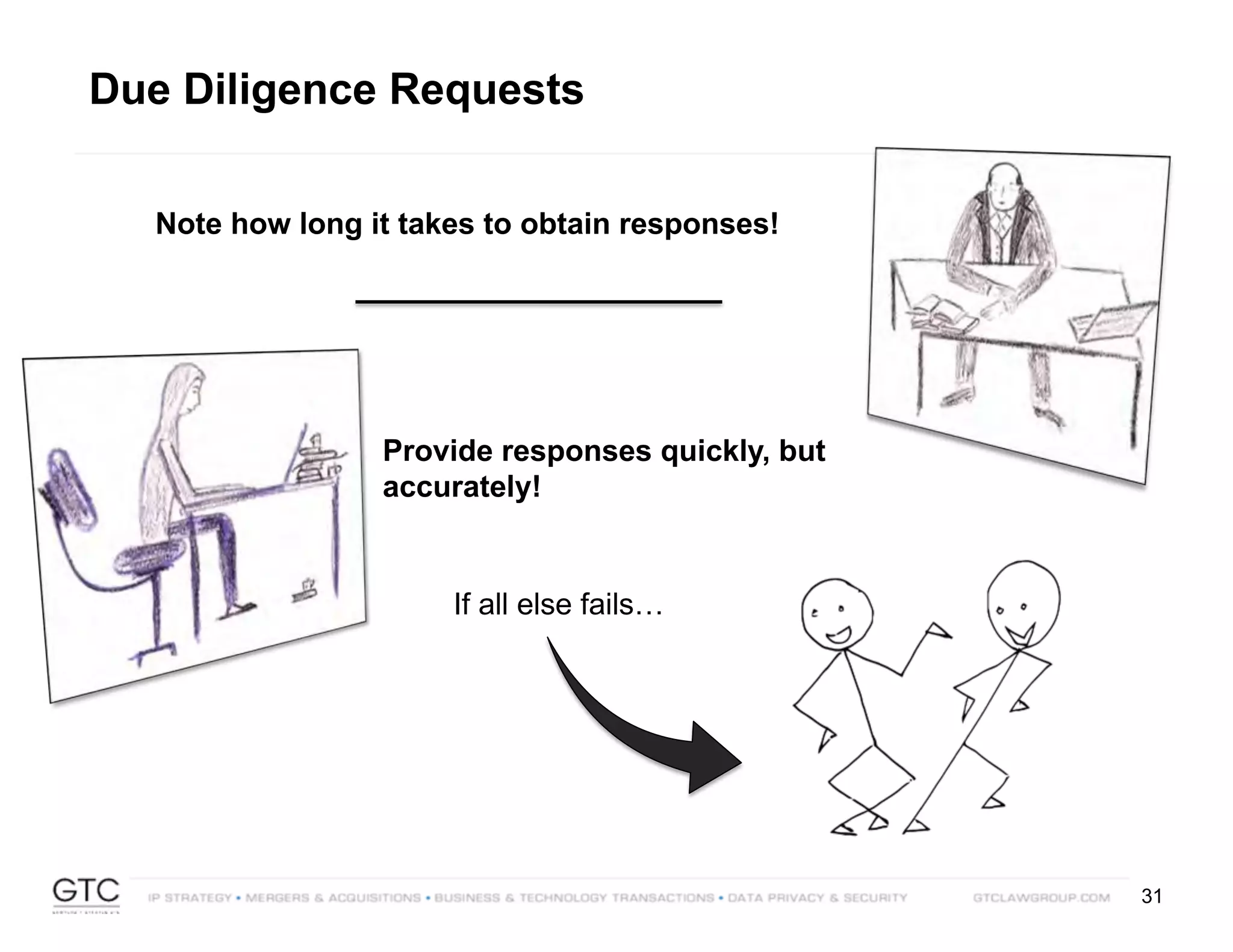
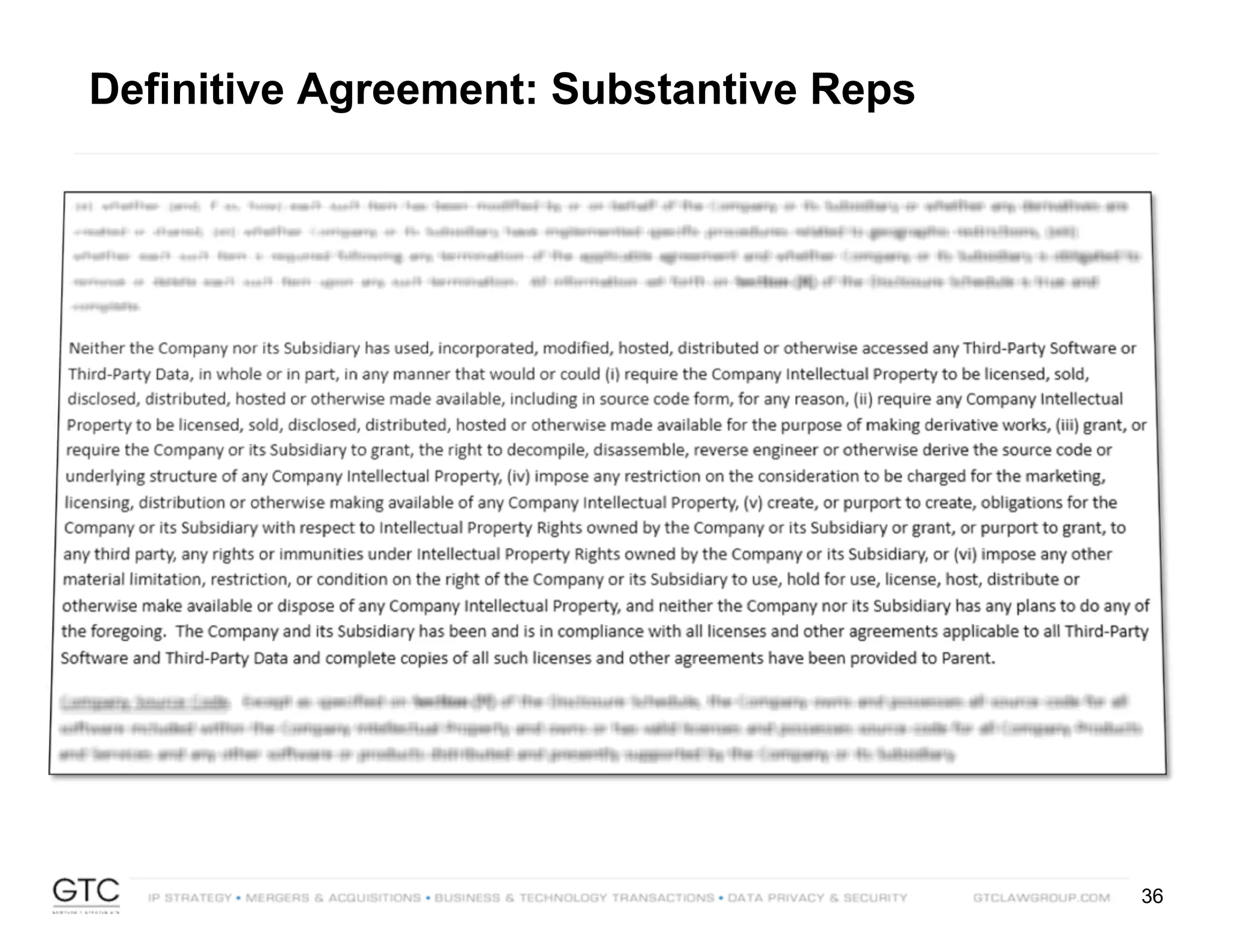
Company has not accessed,
used, distributed, hosted or
modified any third party software
in such a manner as to:
• Require disclosure or distribution of any
Company product/technology in source code
form
• Require the licensing of any Company
product/technology for the purpose of making
derivative works/modifications
• Grant the right to decompile, reverse engineer or
otherwise derive the source of any Company
product/technology
• Require distribution of any Company
product/technology at no charge or with limited
usage restrictions
• Limit in any manner the ability to charge fees or
seek compensation in respect of any Company
product/technology
• Place any limitation on the right of the Company
to use, host or distribute any Company
product/technology
Company:
• Has no plans to do any of the
foregoing
• Is in compliance [in all material
respects] with the licenses
• Has not been subjected to an
audit, nor received any notice of
intent to conduct any such audit
• Has no payment obligations,
except as scheduled
• Company has remedied all
security vulnerabilities
Definitive Agreement: Substantive Reps](https://image.slidesharecdn.com/gtc-flightamsterdam2018may15v-180621175609/75/FLIGHT-Amsterdam-Presentation-Don-t-Let-Open-Source-Software-Kill-Your-Deal-37-2048.jpg)