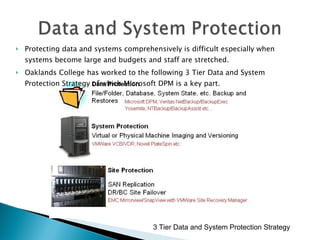
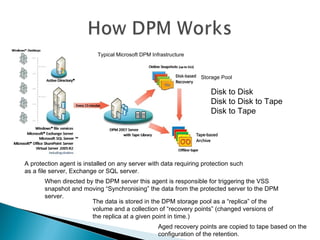
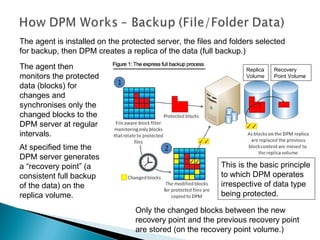
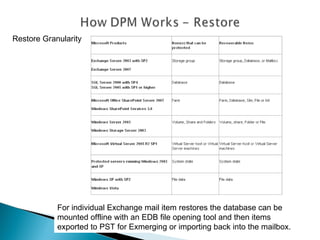
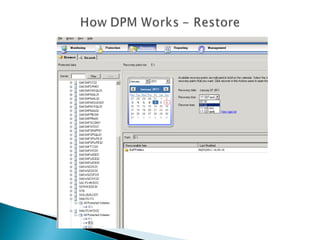
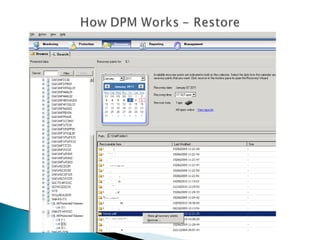
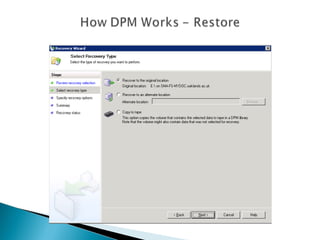
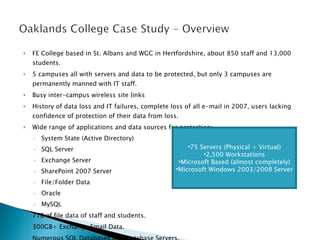
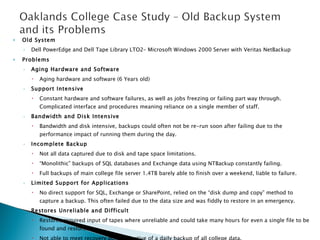
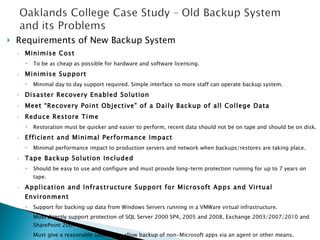
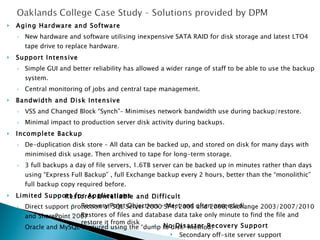
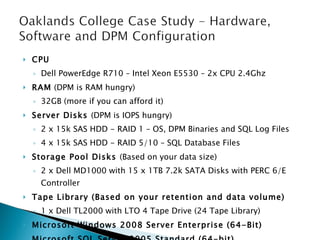
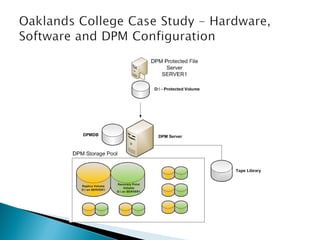
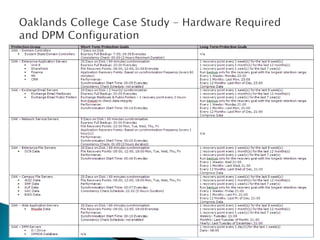
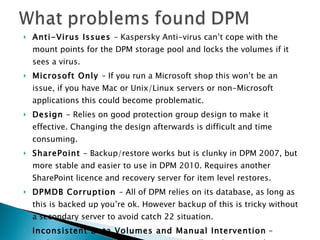
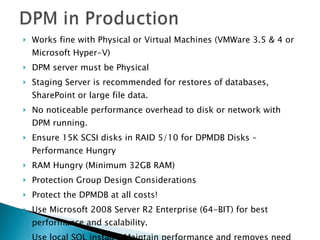
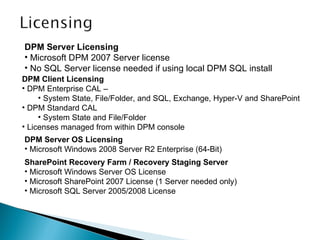
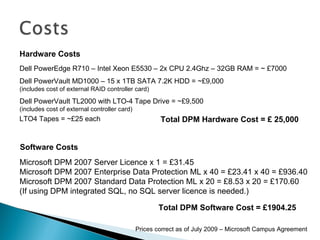
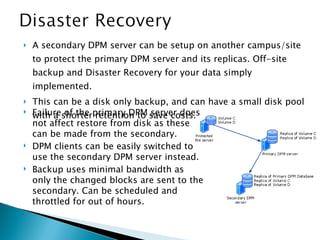
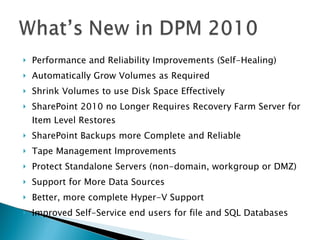
The presentation discusses the implementation of Microsoft Data Protection Manager (DPM) 2007 at Oaklands College to overcome issues with their old backup system. It highlights the college's data protection strategy, integration of DPM with various Microsoft products, and addresses challenges faced, including hardware limitations and assurance of data recovery. Furthermore, it outlines the benefits of DPM, such as efficient backups, disaster recovery support, and performance improvements, while also discussing licensing and hardware costs involved.