Embed presentation
Downloaded 52 times

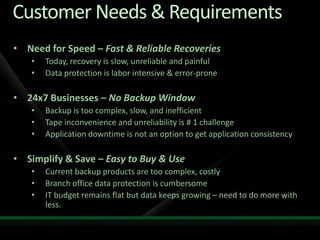
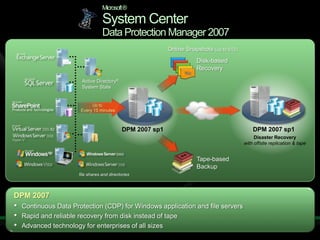

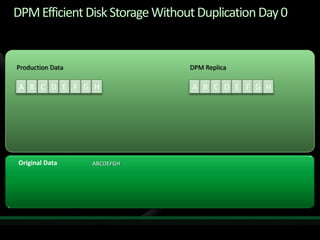
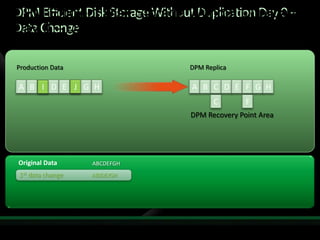
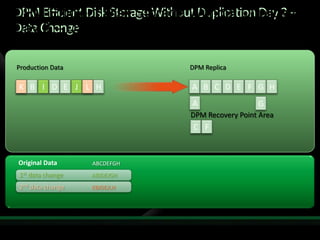
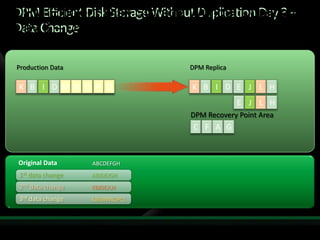
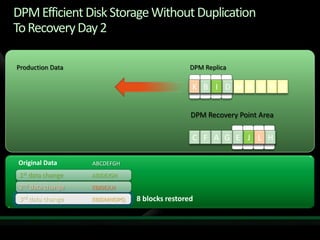
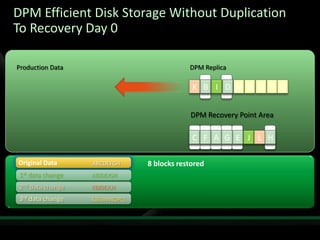

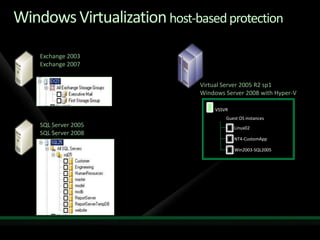
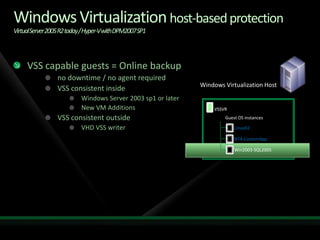
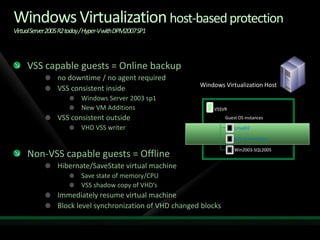
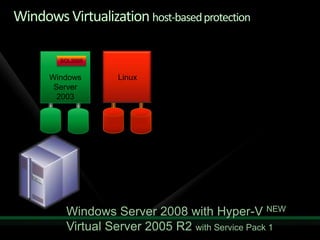
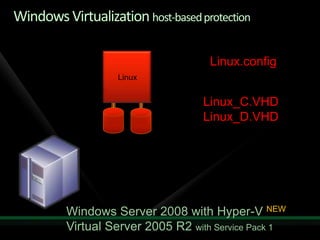
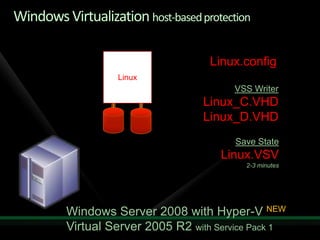
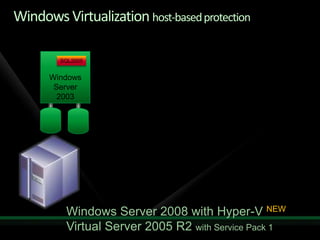
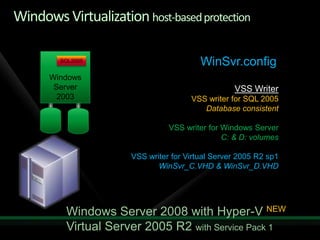
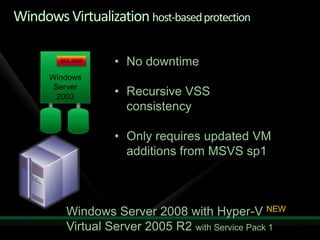
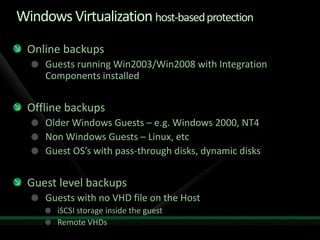

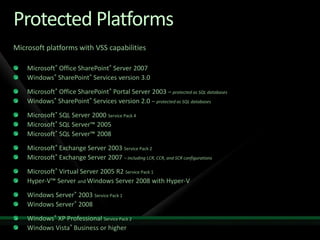

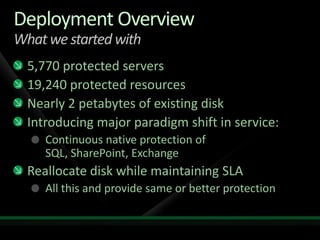
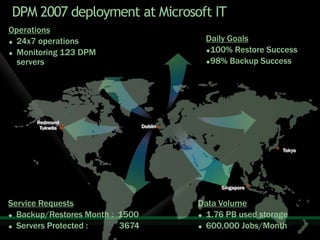
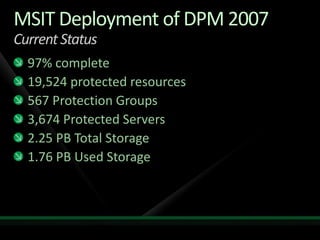
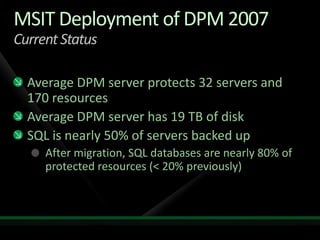
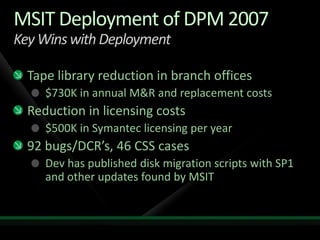
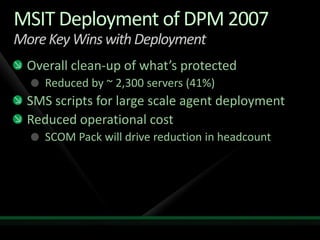



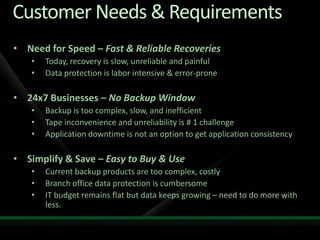
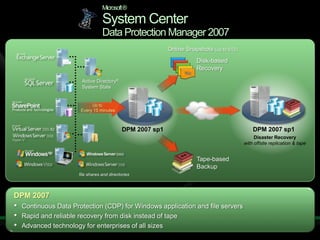
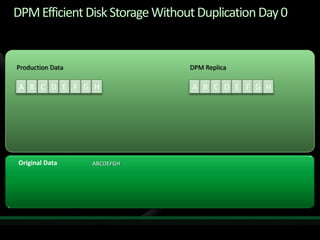
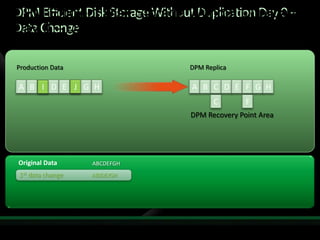
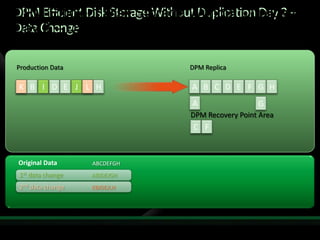
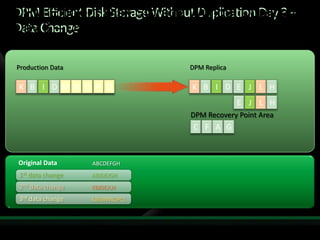
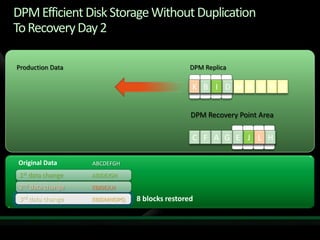
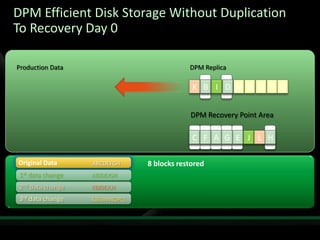
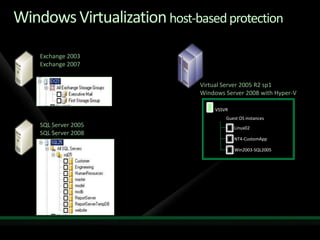
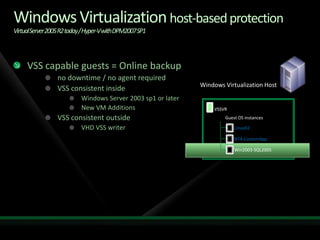
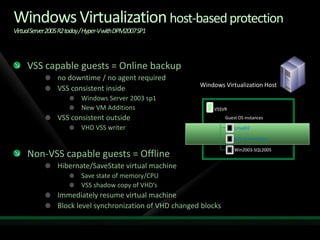
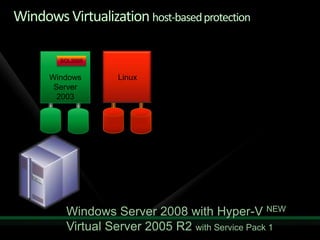
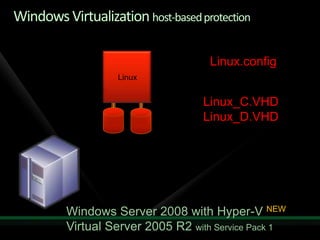
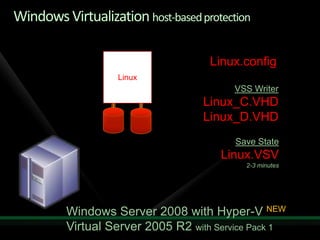
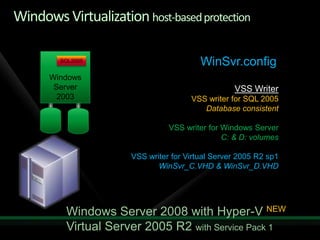
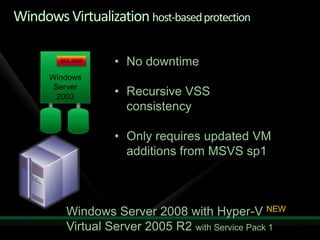
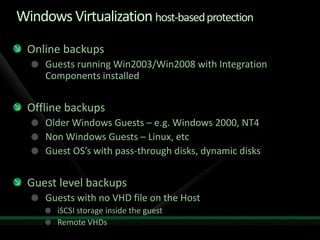
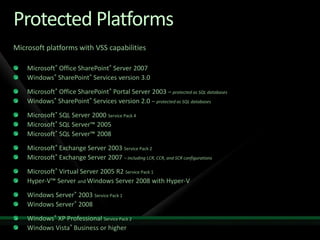
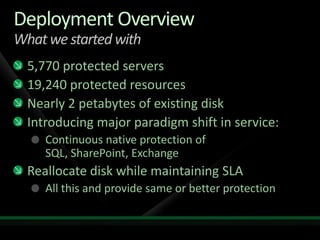
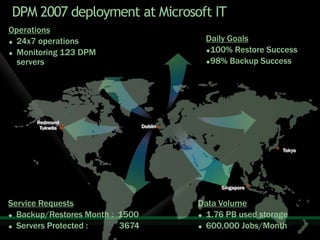
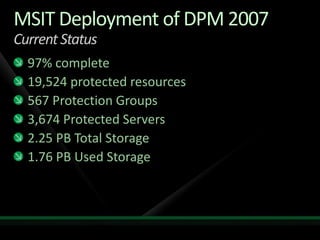
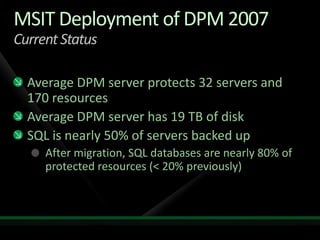
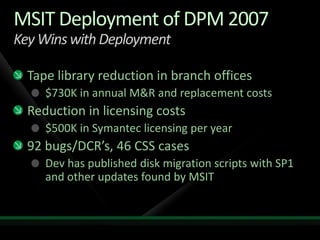
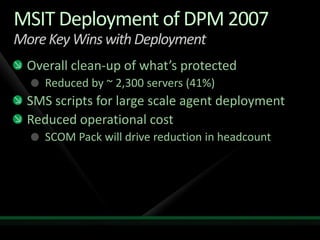
This document provides an overview of Microsoft's System Center Data Protection Manager (DPM) 2007. It discusses customer needs for fast and reliable data recovery, 24/7 backup capabilities without downtime, and an easy to use and cost effective solution. It then summarizes DPM's continuous data protection features, efficient disk-based storage that avoids data duplication, support for virtual and application-level backups, and Microsoft IT's deployment of DPM across its infrastructure.