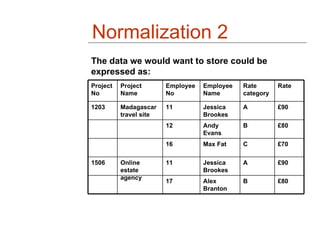
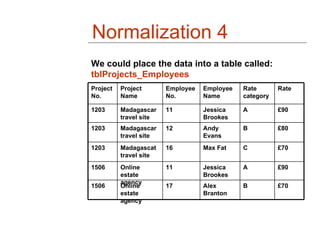
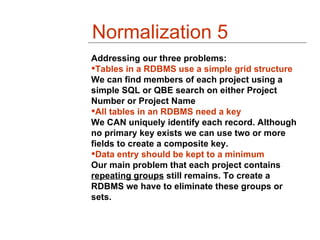
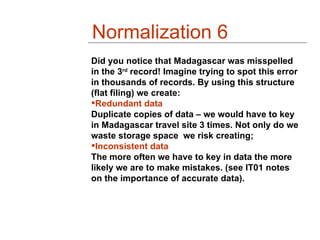
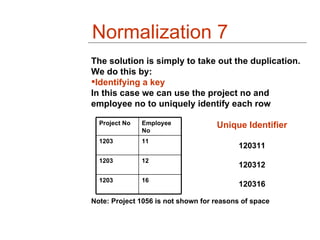
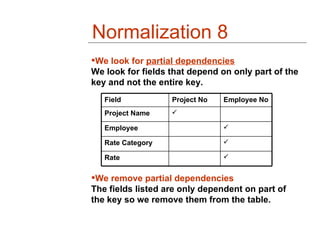
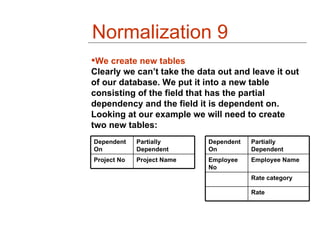
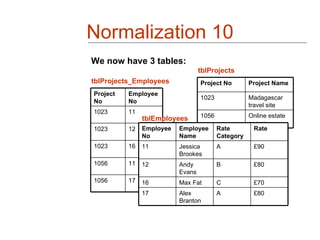
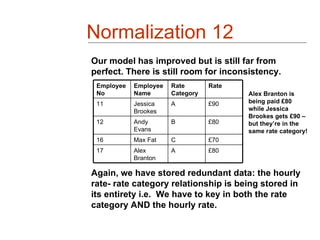
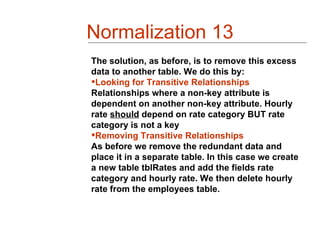
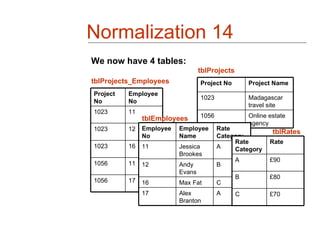
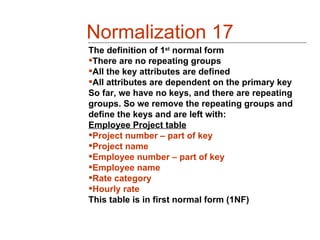
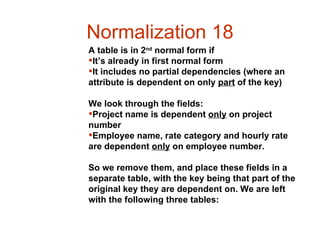
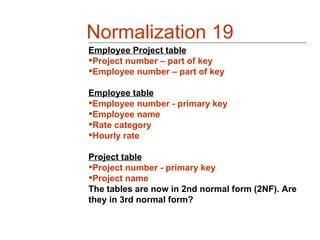
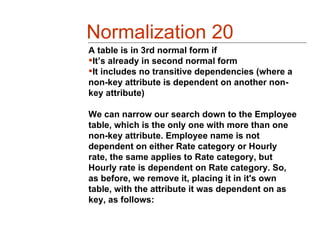
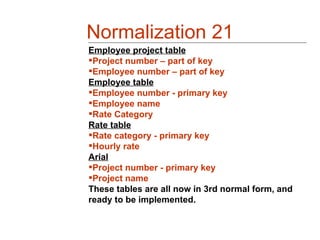
The document describes the process of normalizing a database about projects and employees. It starts with a single table that has repeating groups and other issues. Through removing redundant data and splitting into multiple tables based on dependencies, it normalizes the data into third normal form with three tables: a projects table, employees table, and rates table. This reduces data redundancy and inconsistency while making the database structure more efficient and queries easier.