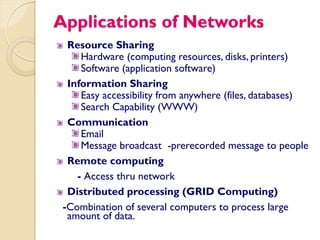
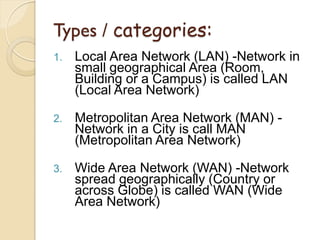
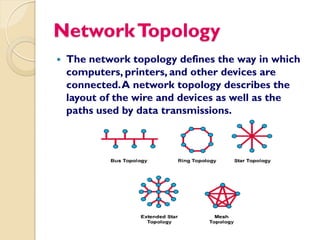
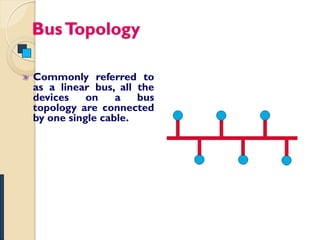
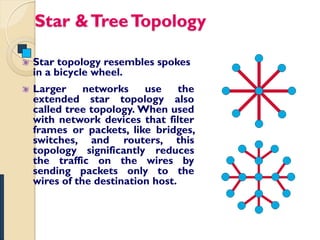
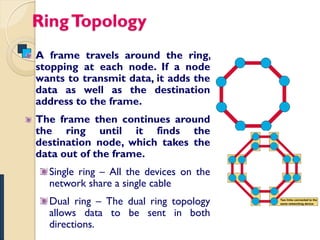
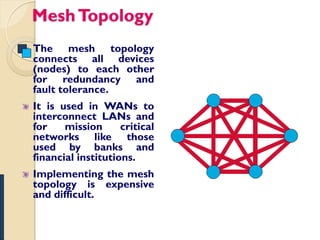
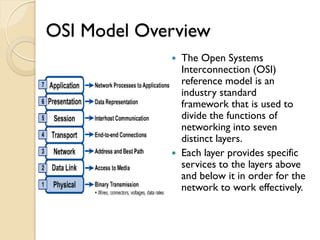
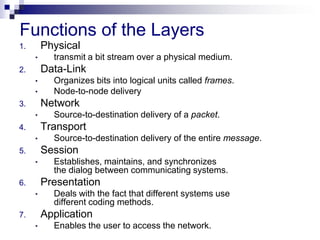
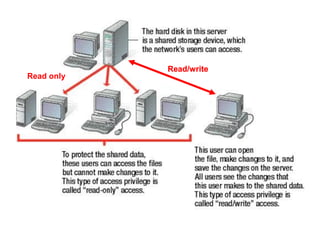
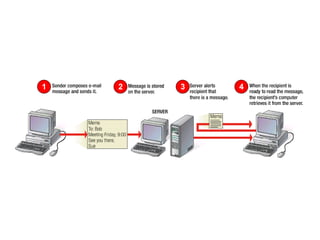
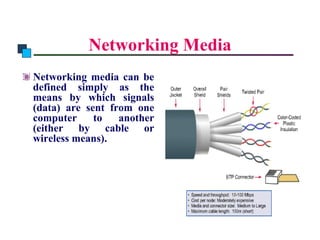
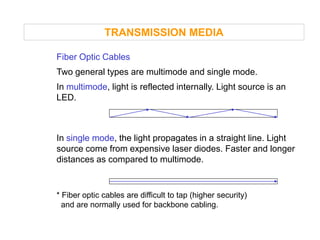
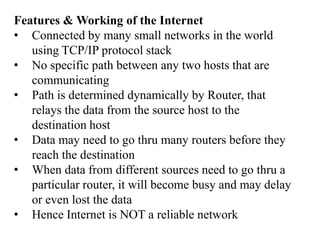
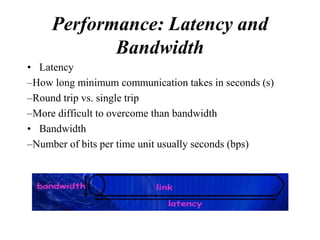
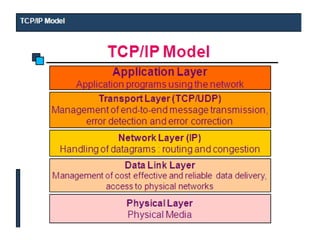
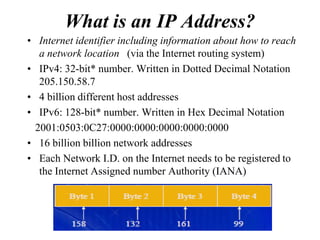
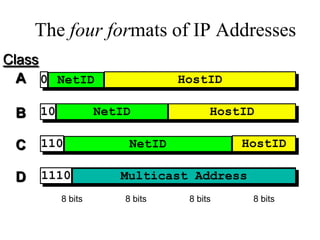
This document provides an overview of computer networks. It defines what a computer network is and discusses how computers connect and share resources over a network. It also covers different types of networks like LAN, MAN, and WAN. Additionally, it describes common network devices like hubs, switches, routers, and gateways. The document also discusses network topologies, transmission media, and addressing in TCP/IP networks. In summary, it serves as a comprehensive introduction to fundamental computer networking concepts.