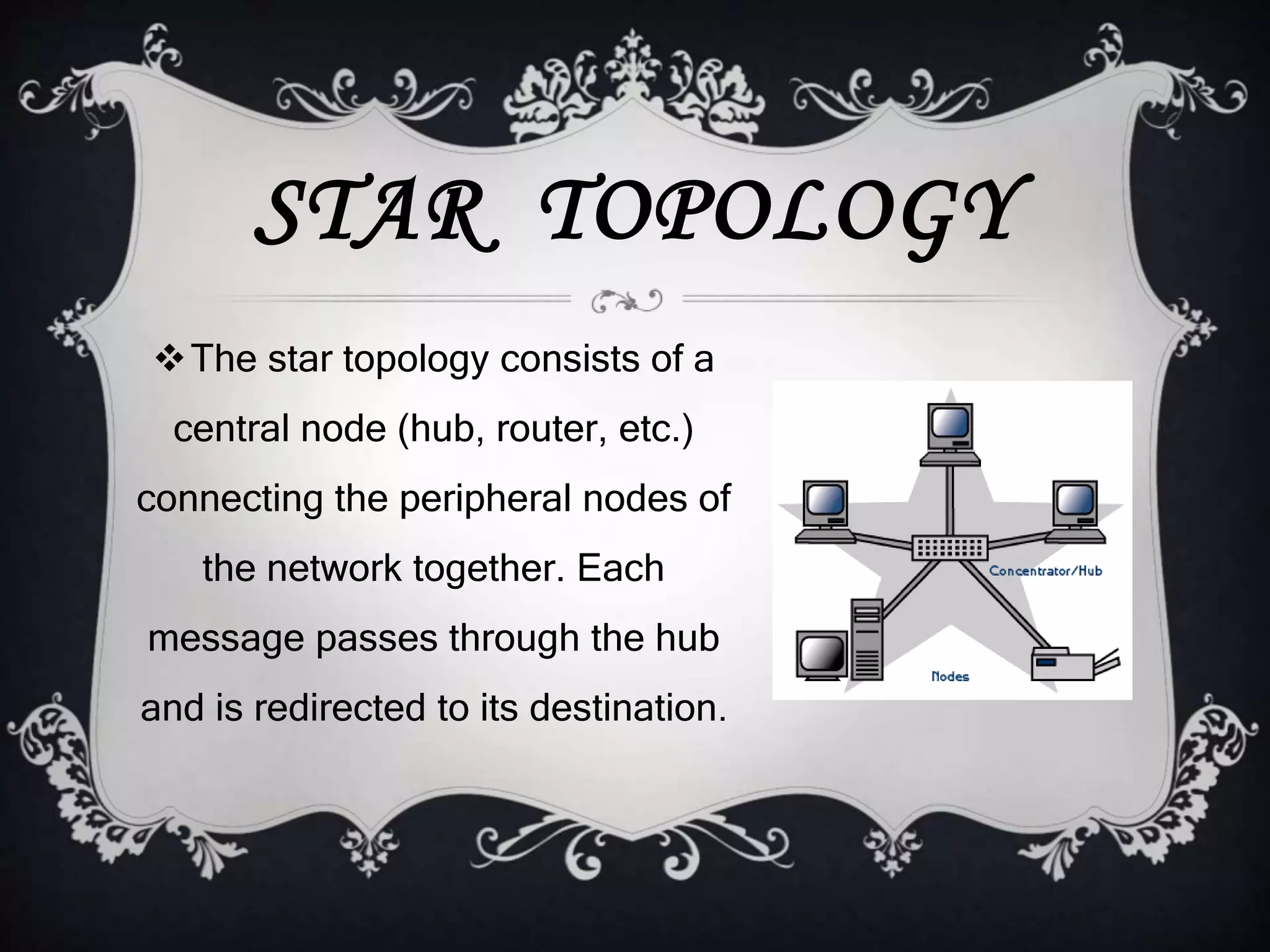
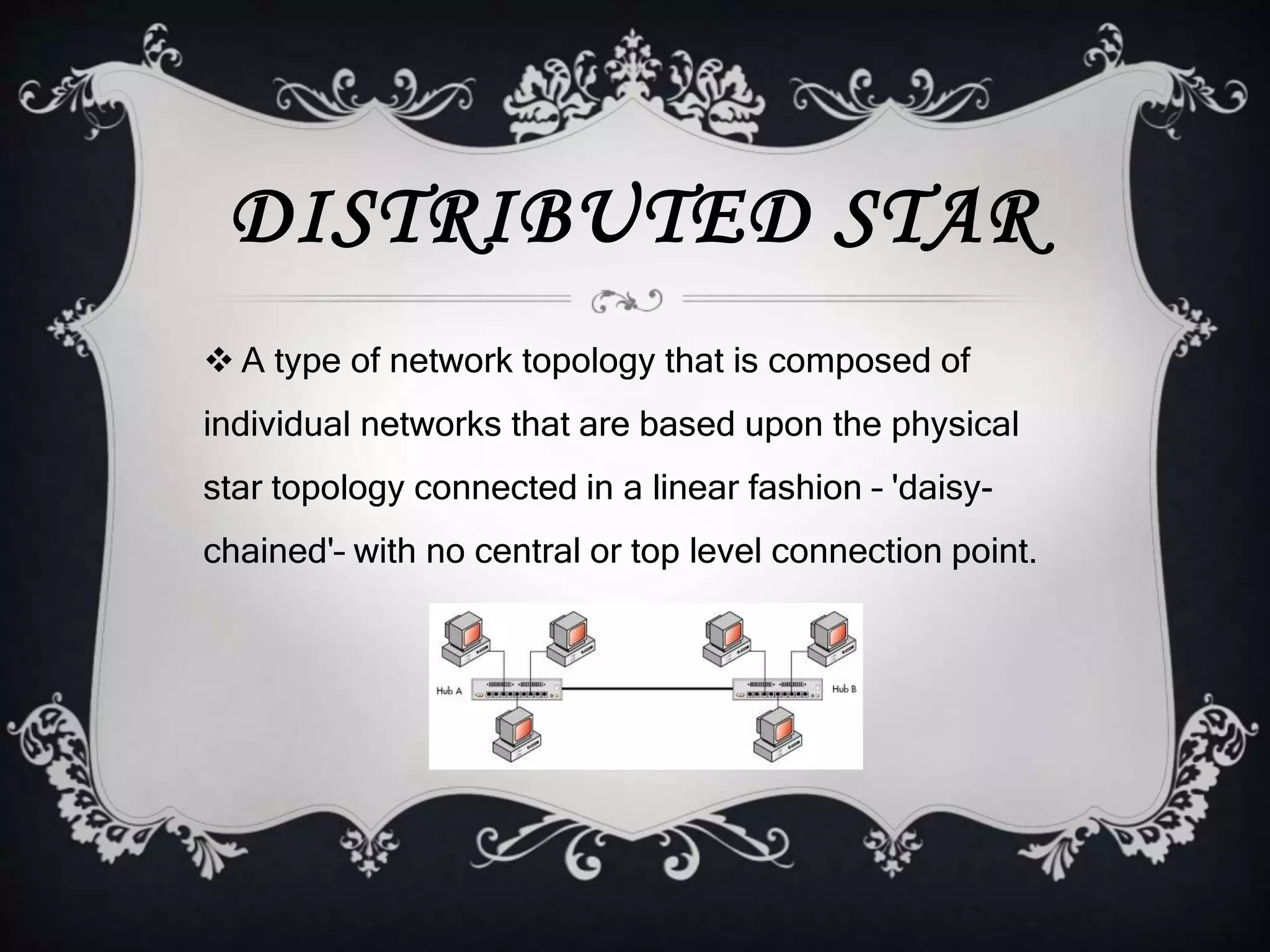
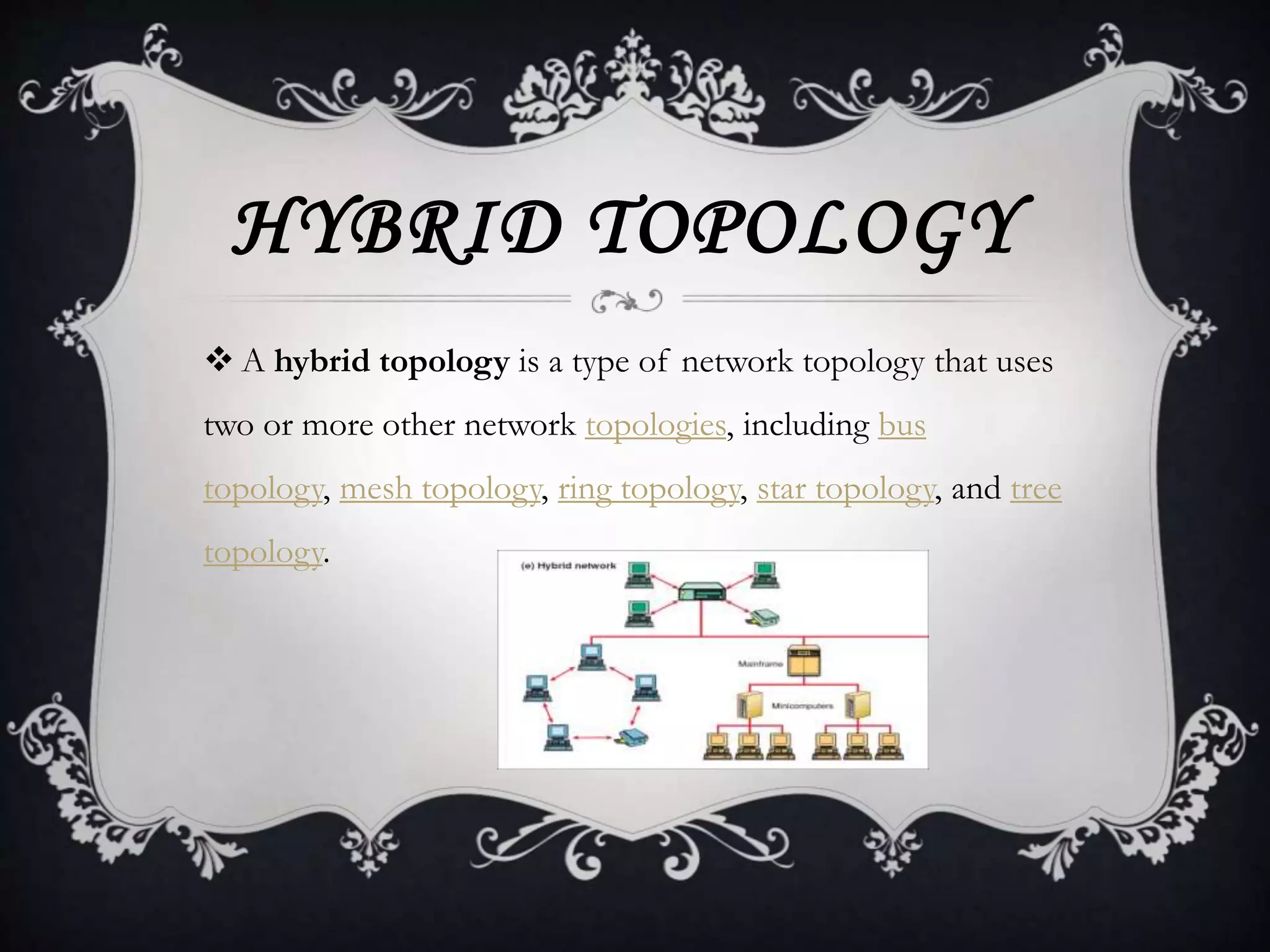
The document describes various network topologies. It discusses physical and logical topologies. Common topologies described include star, mesh, bus, ring, tree, and hybrid topologies. For each topology, it provides details on the structure and provides advantages and disadvantages. It also discusses extended star, distributed star, full mesh, partial mesh, linear bus, distributed bus, dual ring, point to point, and point to multipoint variations of the topologies.