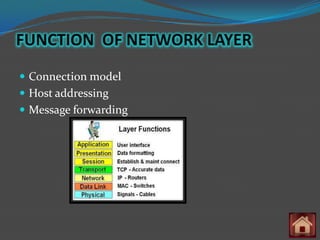
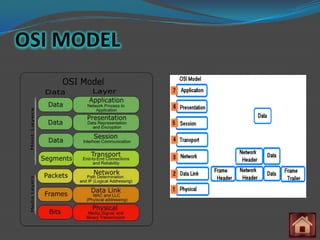
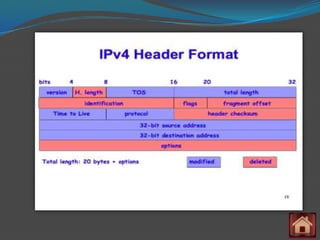
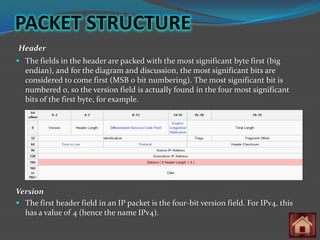
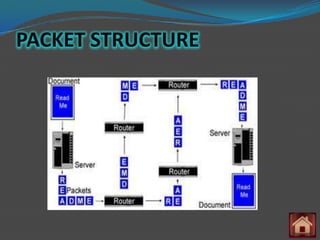
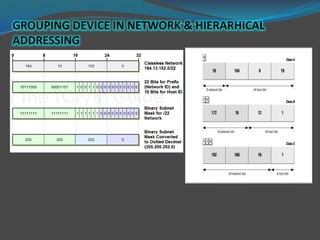
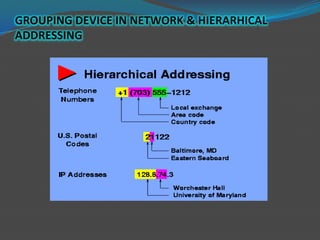
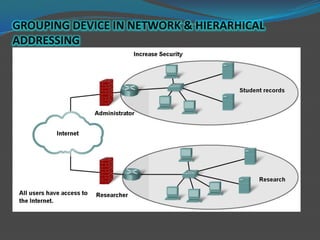
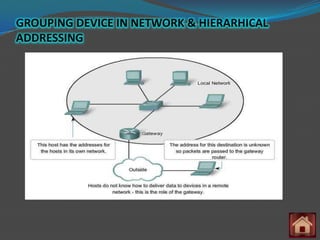
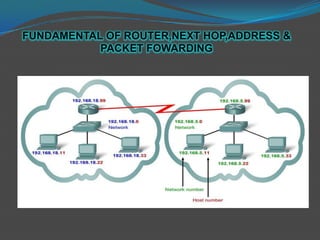
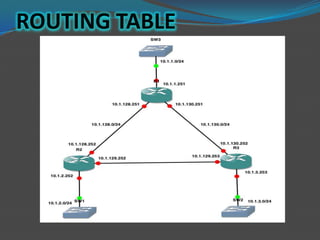
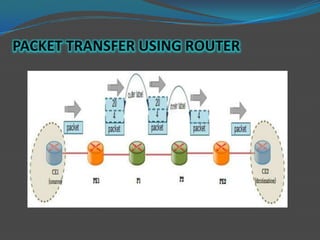
The document discusses the network layer of the OSI model. It describes the network layer's role in dividing networks into groups, facilitating communication between networks via routing. Key aspects covered include network layer protocols like IP, addressing, packet structure, grouping devices into networks via hierarchical addressing, and the fundamentals of routing tables, next hop addresses, and packet forwarding.