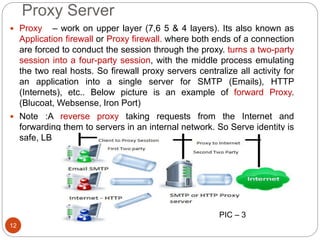
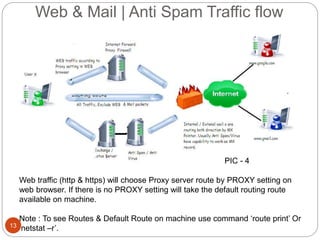
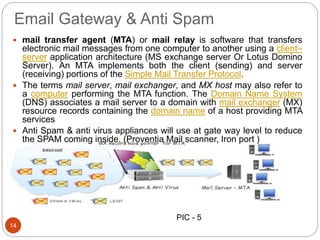
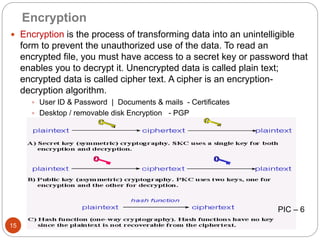
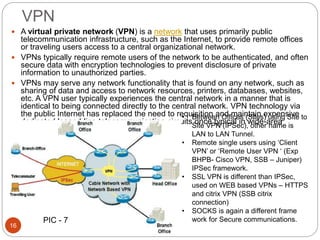
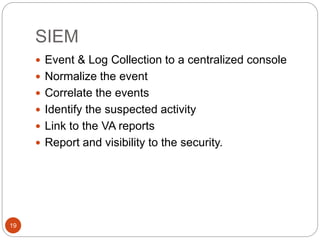
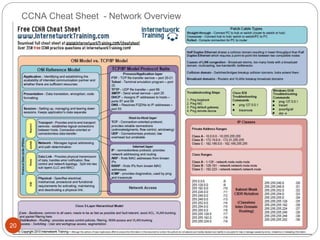
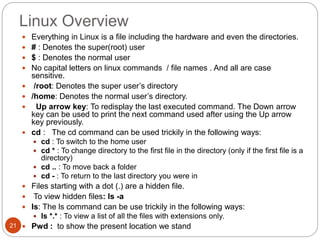
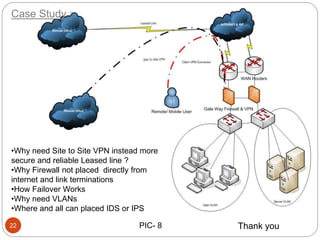
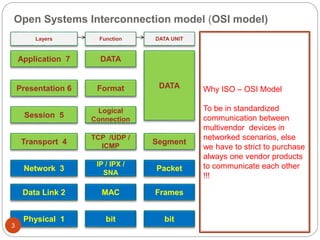
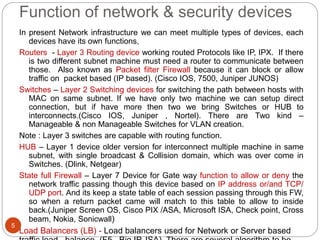
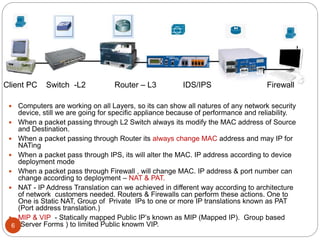
This document provides an overview of networking and security concepts including the OSI model, functions of common network devices like routers, switches, firewalls and IDS/IPS systems. It describes technologies like NAT, VPNs, encryption, file integrity monitoring and SIEM. It also includes brief introductions to Linux, the CCNA and a case study on site-to-site VPN deployment considerations.

![File Integrity Manager - FIM
11
File integrity monitoring (FIM) is an internal control or
process that performs the act of validating the integrity of
operating system and application software files using a
verification method between the current file state and the
known, good baseline. This comparison method often
involves calculating a known cryptographic checksum of the
file's original baseline and comparing with the calculated
checksum of the current state of the file.[1] Other file
attributes can also be used to monitor integrity.[2]
Generally, the act of performing file integrity monitoring is
automated using internal controls such as an application or
process. Such monitoring can be performed randomly, at a
defined polling interval, or in real-time.
Regulatory requirement](https://image.slidesharecdn.com/networksecuritystartup-190205091922/85/Network-amp-security-startup-11-320.jpg)