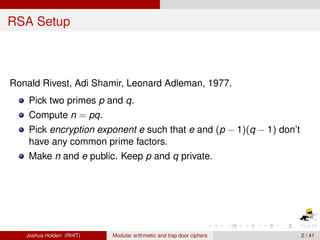
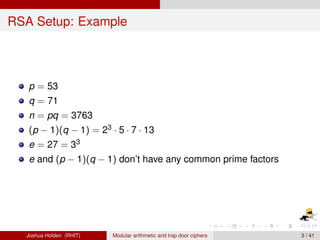
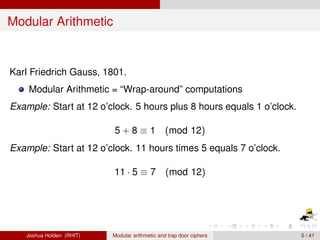
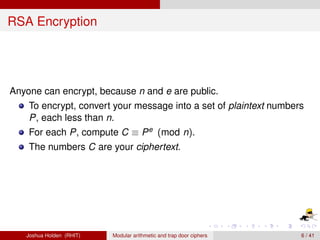
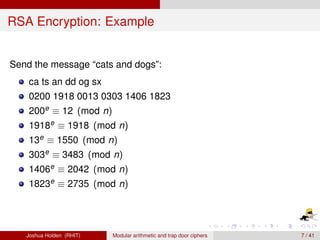
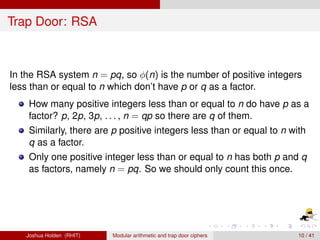
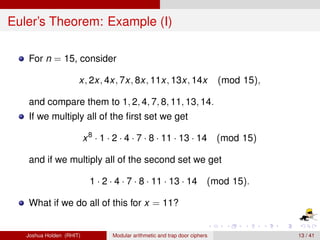
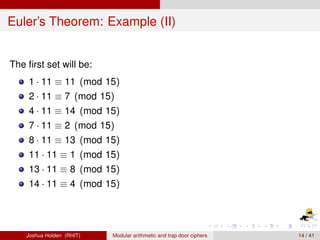
The document discusses the RSA encryption algorithm which is based on modular arithmetic and uses a "trap door" property related to prime factorization. It describes how RSA works including: generating public and private keys from two primes, encrypting messages using modular exponentiation, and decrypting ciphertext using the private key and Euler's theorem. The security of RSA relies on the fact that factoring large numbers is computationally infeasible, while setting up the system is relatively fast.