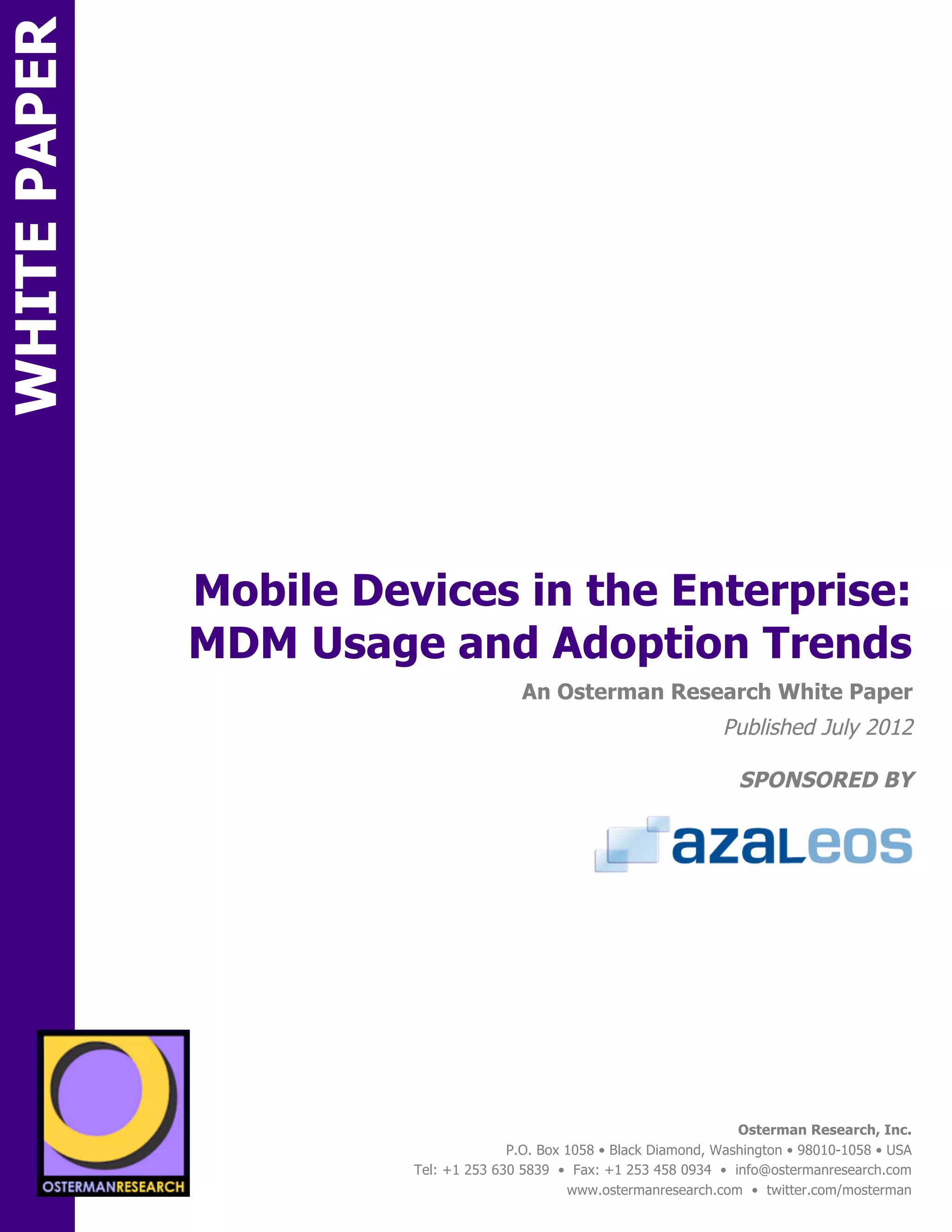
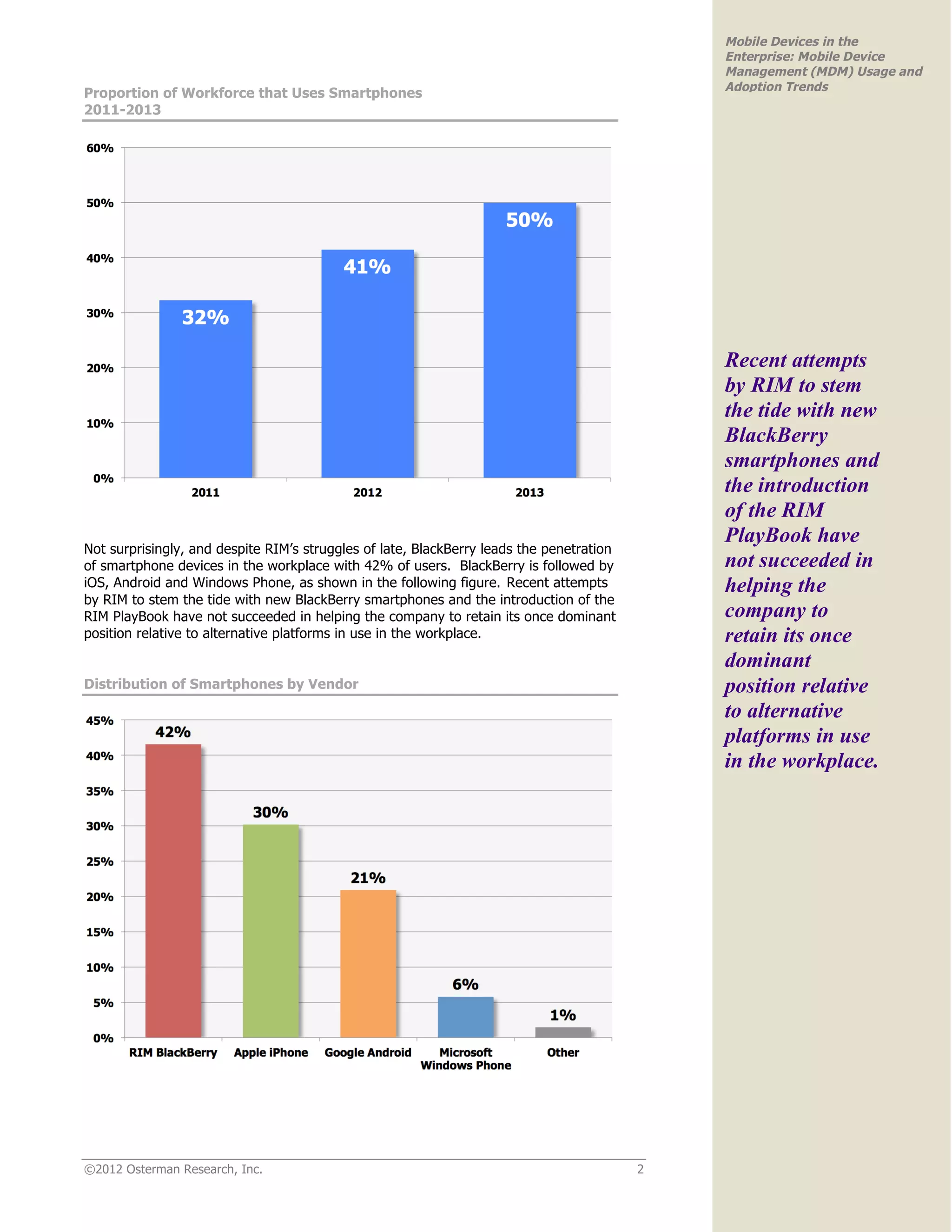
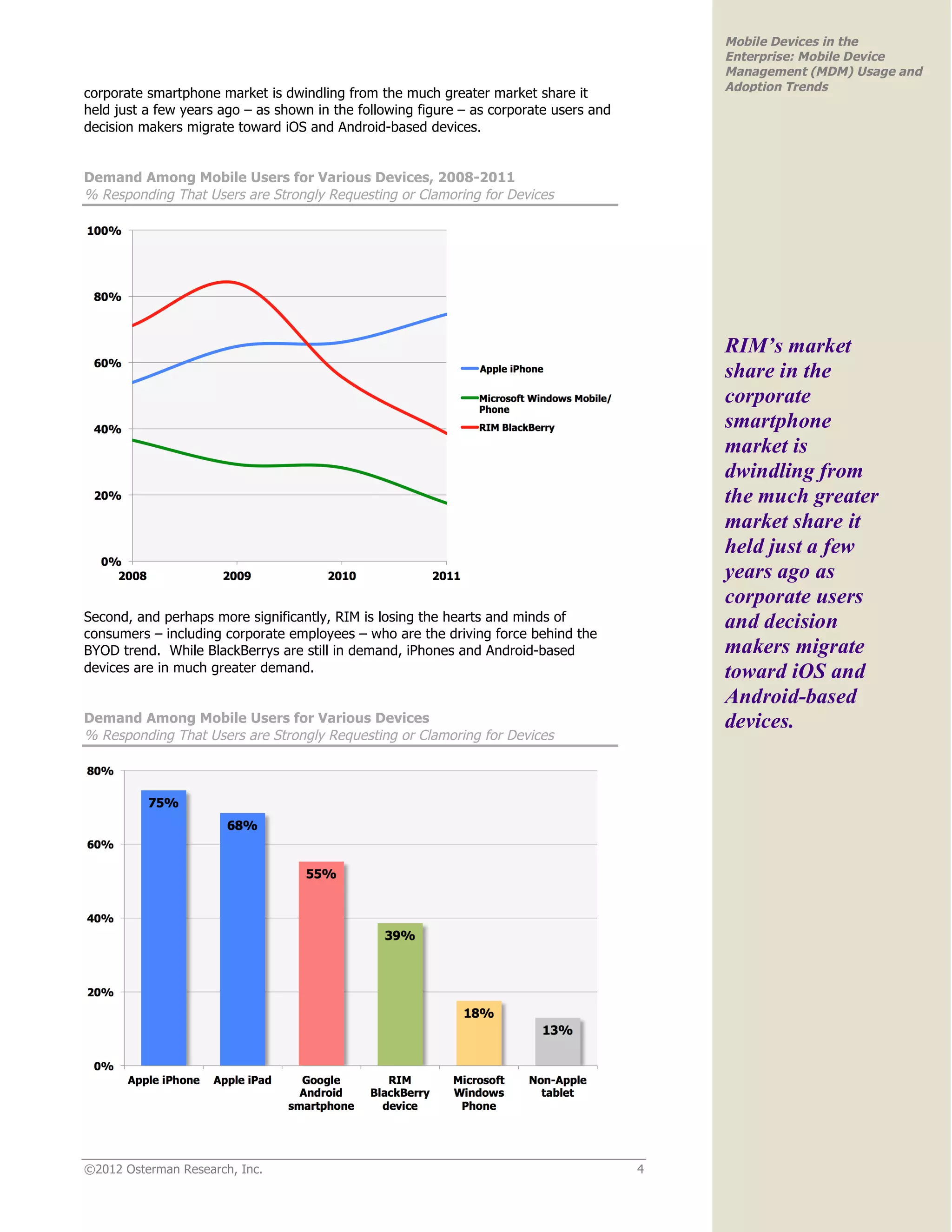
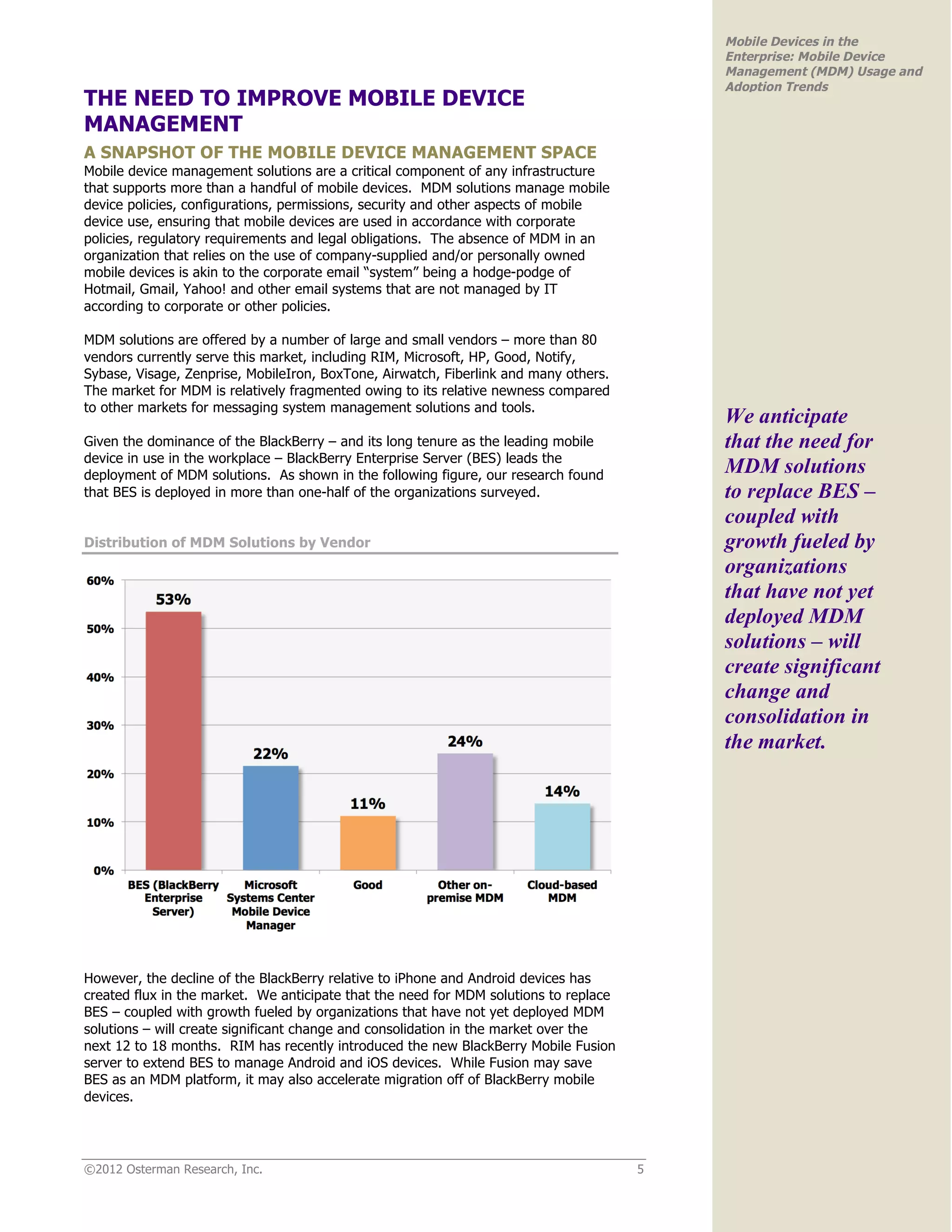
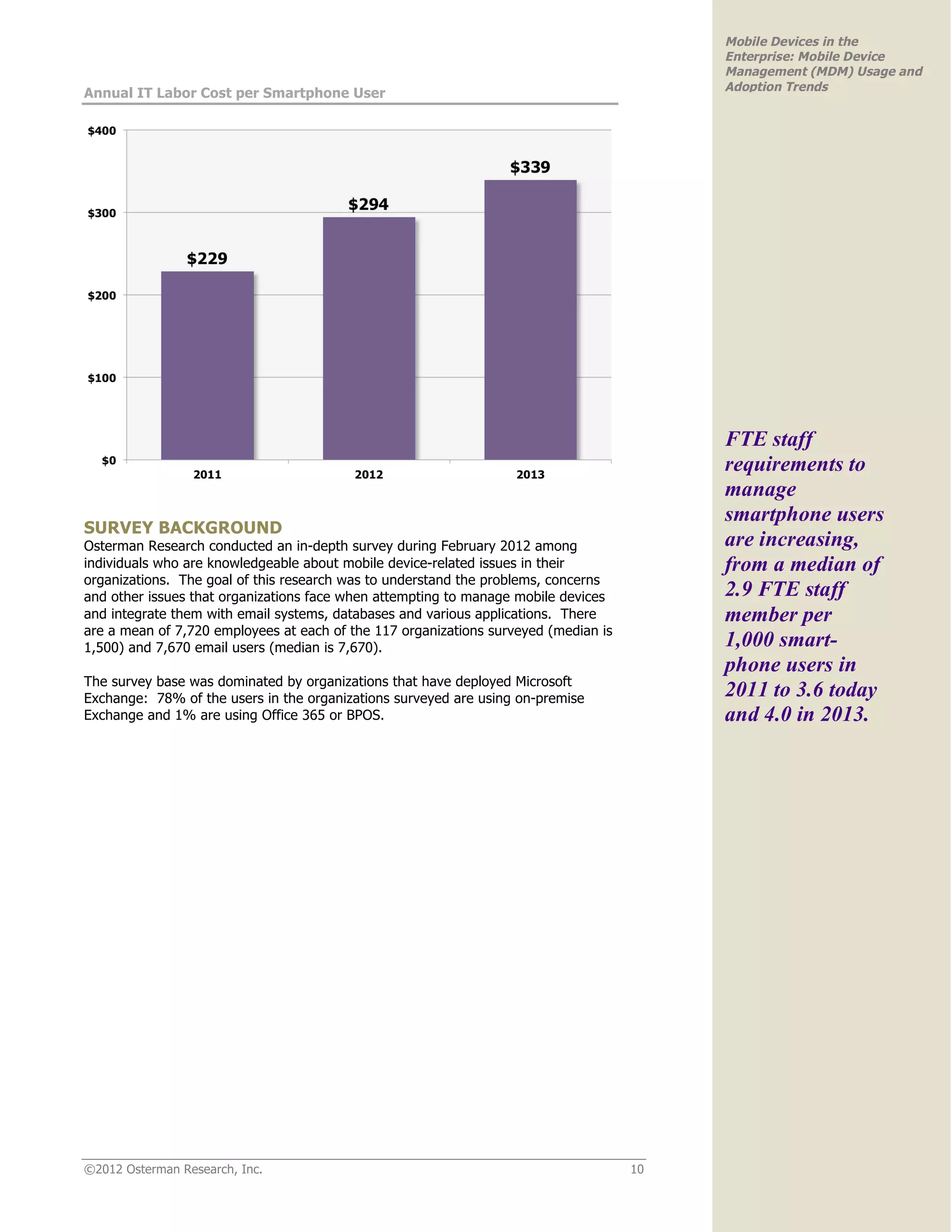
The white paper discusses the growing importance of mobile devices and the necessity of Mobile Device Management (MDM) in enterprises, highlighting a rapid increase in smartphone usage and the BYOD trend. Organizations face risks from unaddressed MDM, leading to potential data breaches, increased IT costs, and lost productivity. The study predicts significant growth in MDM adoption driven by the need for enhanced security, scalability, and control over diverse mobile devices.