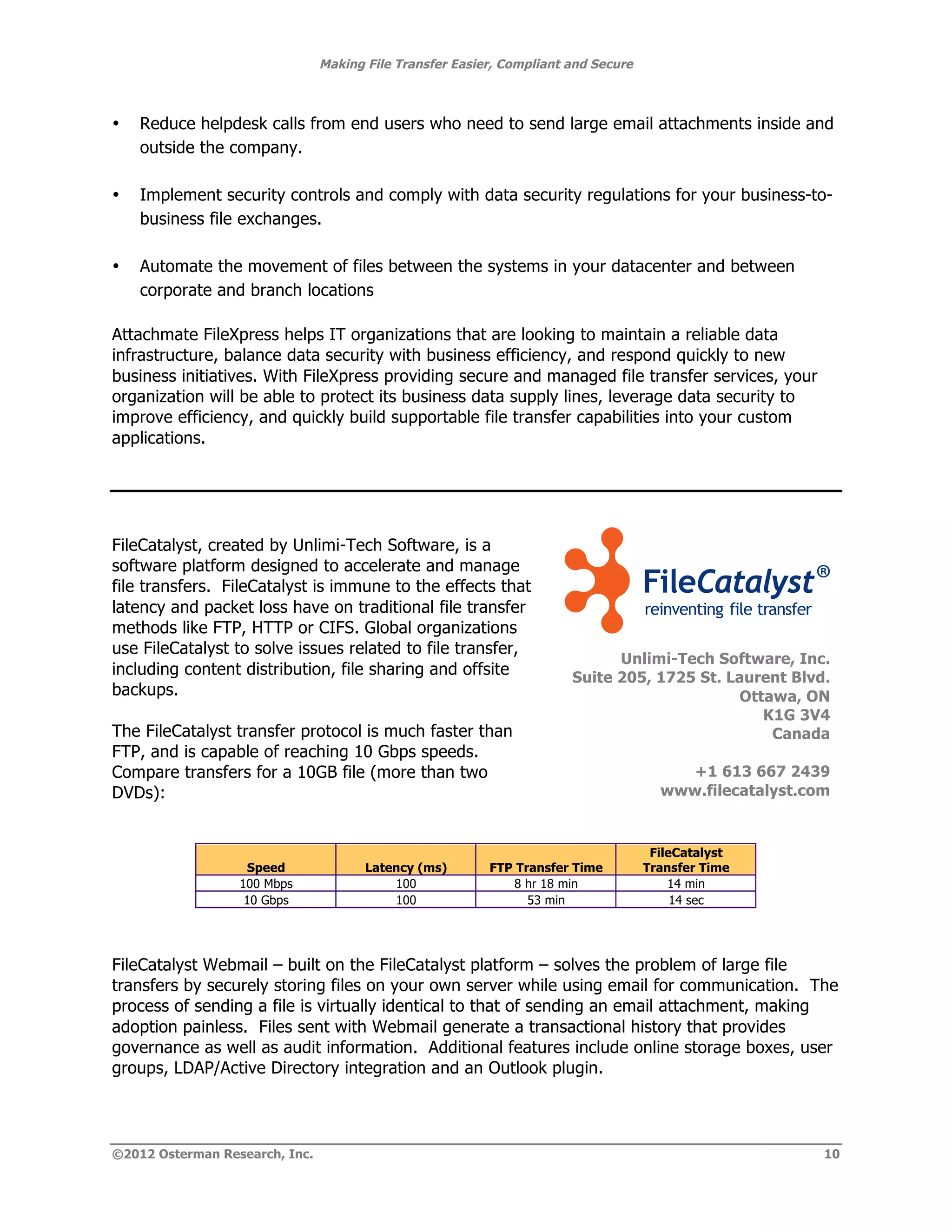
This white paper discusses the need for a dedicated, secure file transfer solution to address the inefficiencies and risks associated with using email as a primary file transfer mechanism in organizations. It highlights the challenges of existing systems, including lack of governance, increased risk of data breaches, and escalating management costs, while advocating for better alternatives that integrate easily into workflows and comply with regulatory requirements. The document also emphasizes the importance of solutions that manage content throughout its lifecycle and improve corporate governance.