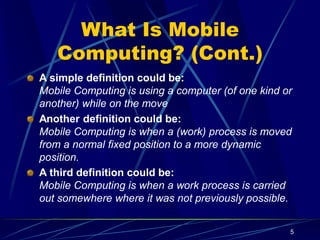
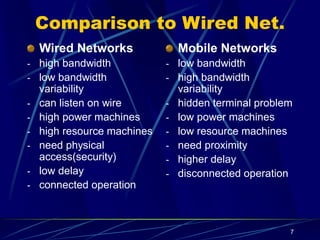
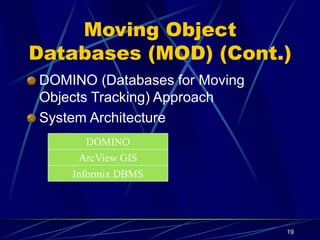
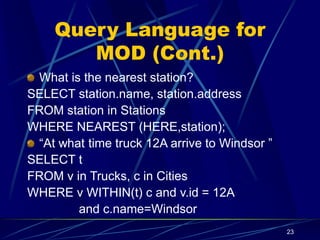
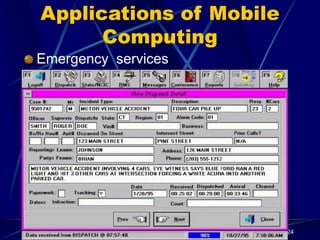
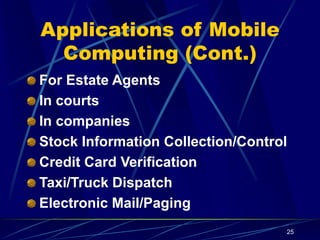
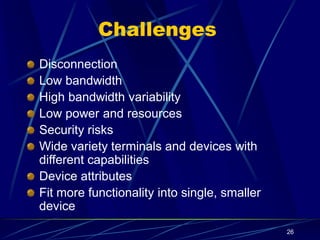
The document discusses mobile computing, which allows users with portable devices to access network services anytime and anywhere. It compares mobile networks to wired networks, highlighting the advantages of mobility, numerous wireless devices, and the concept of mobile objects that change state and location. The presentation also addresses challenges in mobile computing, future developments, and applications in various fields such as emergency services and transportation.