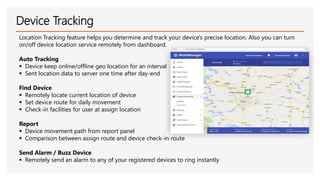
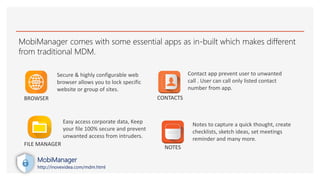
Mobimanager is a mobile device management solution designed to secure and manage company-owned Android devices, ensuring productivity and data protection. It offers features like application management, device tracking, security policies, and content management to safeguard sensitive business information. The platform provides a user-friendly interface with customizable options for policy enforcement and remote management capabilities.