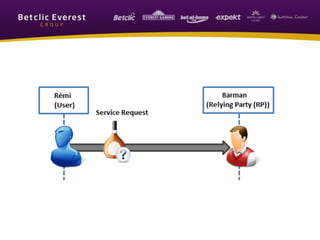
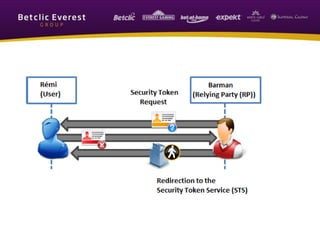
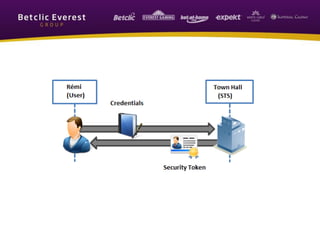
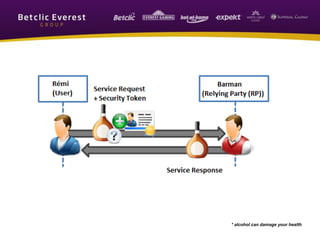
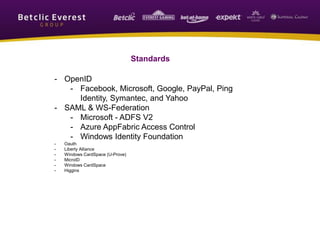
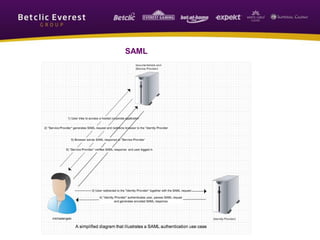
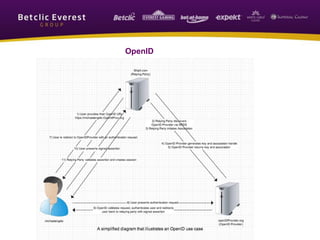
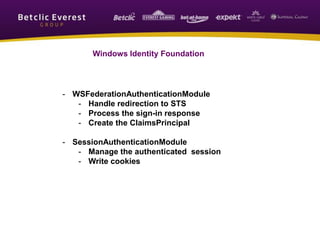
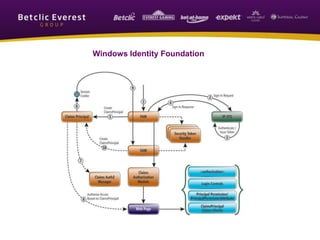
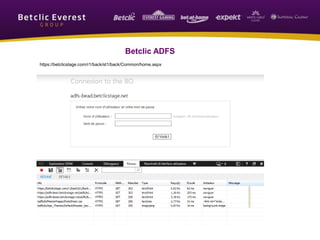
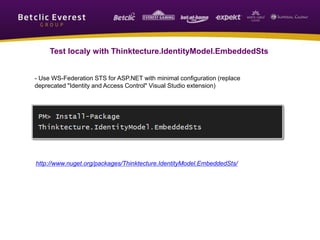
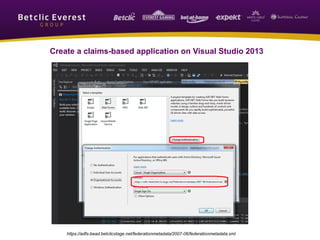
The document explains Single Sign-On (SSO), which allows users to log in once and access multiple systems, reducing password fatigue and IT support costs. It mentions key concepts such as security tokens, identity providers, and the significance of standards like OpenID and SAML. Additionally, it highlights the Betclic Everest Group's commitment to secure online gaming and responsible practices across various international brands.