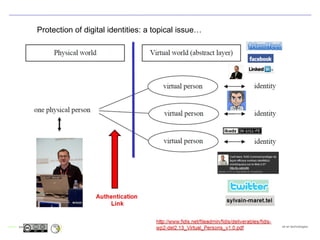
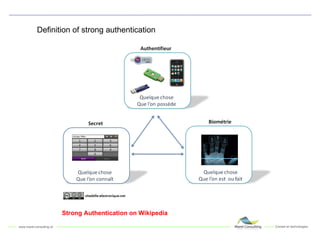
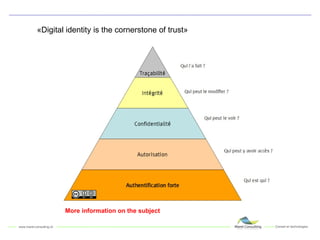
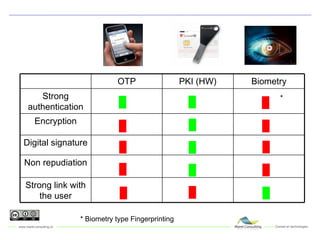
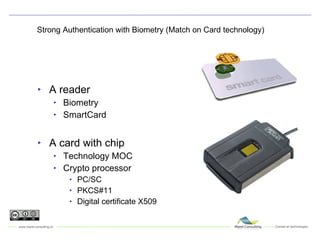
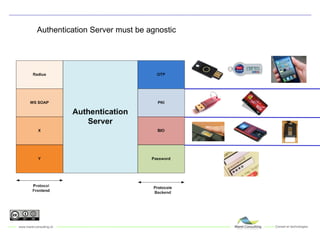
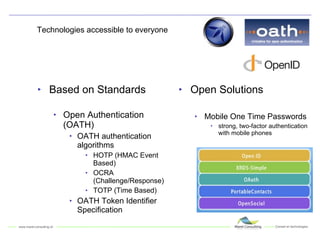
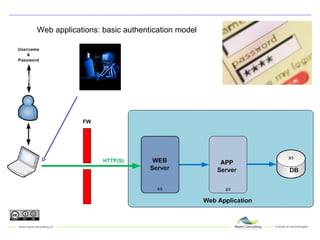
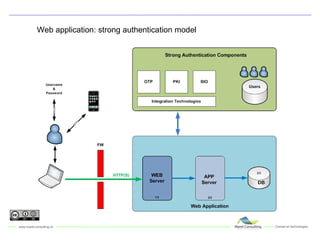
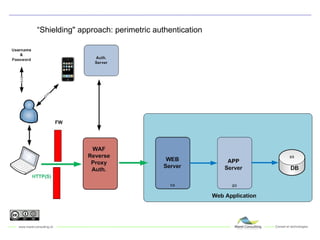
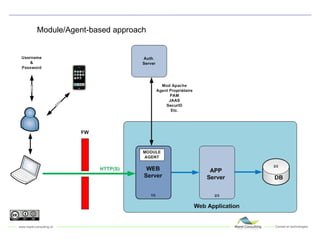
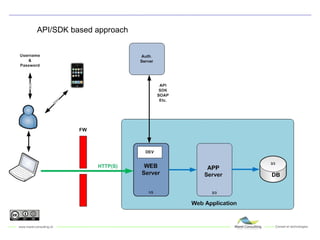
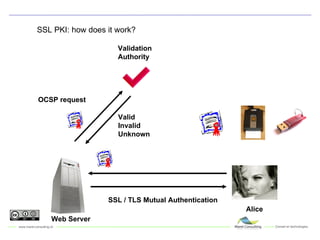
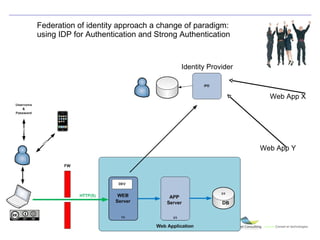
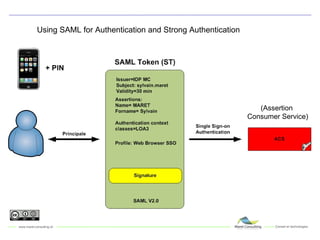
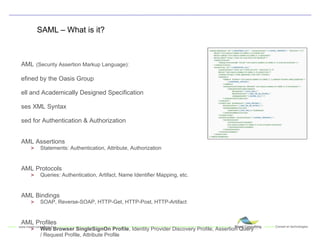
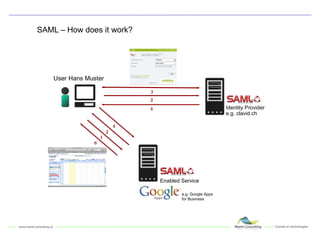
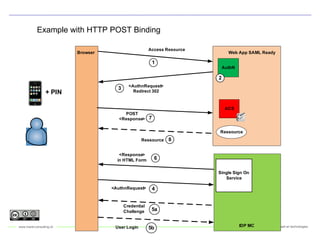
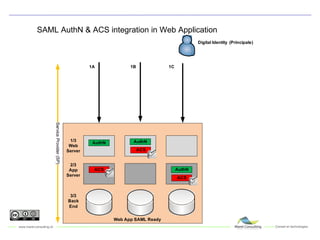
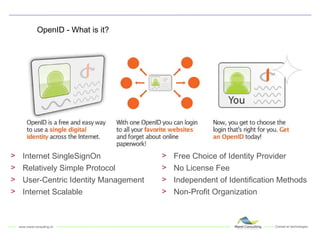
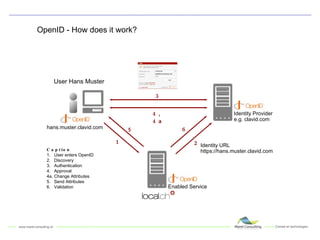
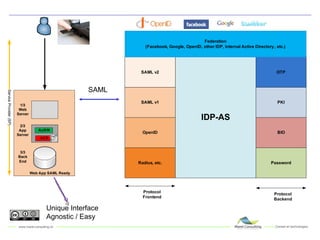
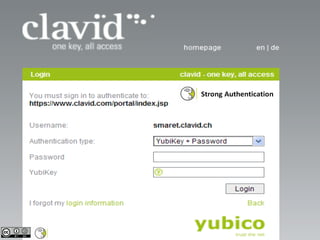
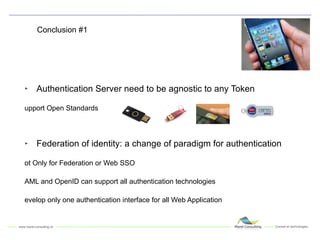
Sylvain Maret is a digital security expert who gave a presentation on strong authentication in web applications. He discussed threats to authentication like keyloggers and social engineering. New standards like FFIEC and PCI DSS require strong authentication for financial applications and remote access. Strong authentication can use biometrics or one-time passwords. Standards like SAML and OpenID allow for identity federation where users can authenticate with an identity provider and access multiple applications.