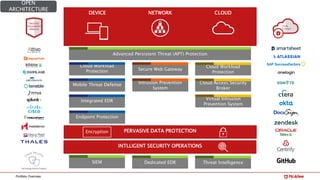
McAfee is a leading cybersecurity company specializing in device-to-cloud security with over 30 years of experience and numerous patents. Its portfolio includes advanced threat protection solutions, cloud workload protection, and integrated security services aimed at enhancing cybersecurity operations. The document outlines various products and strategies for defending against cyber threats in open architectures and multi-cloud environments.