This document contains notes and examples related to reviewing concepts involving quadratics and radical operations:
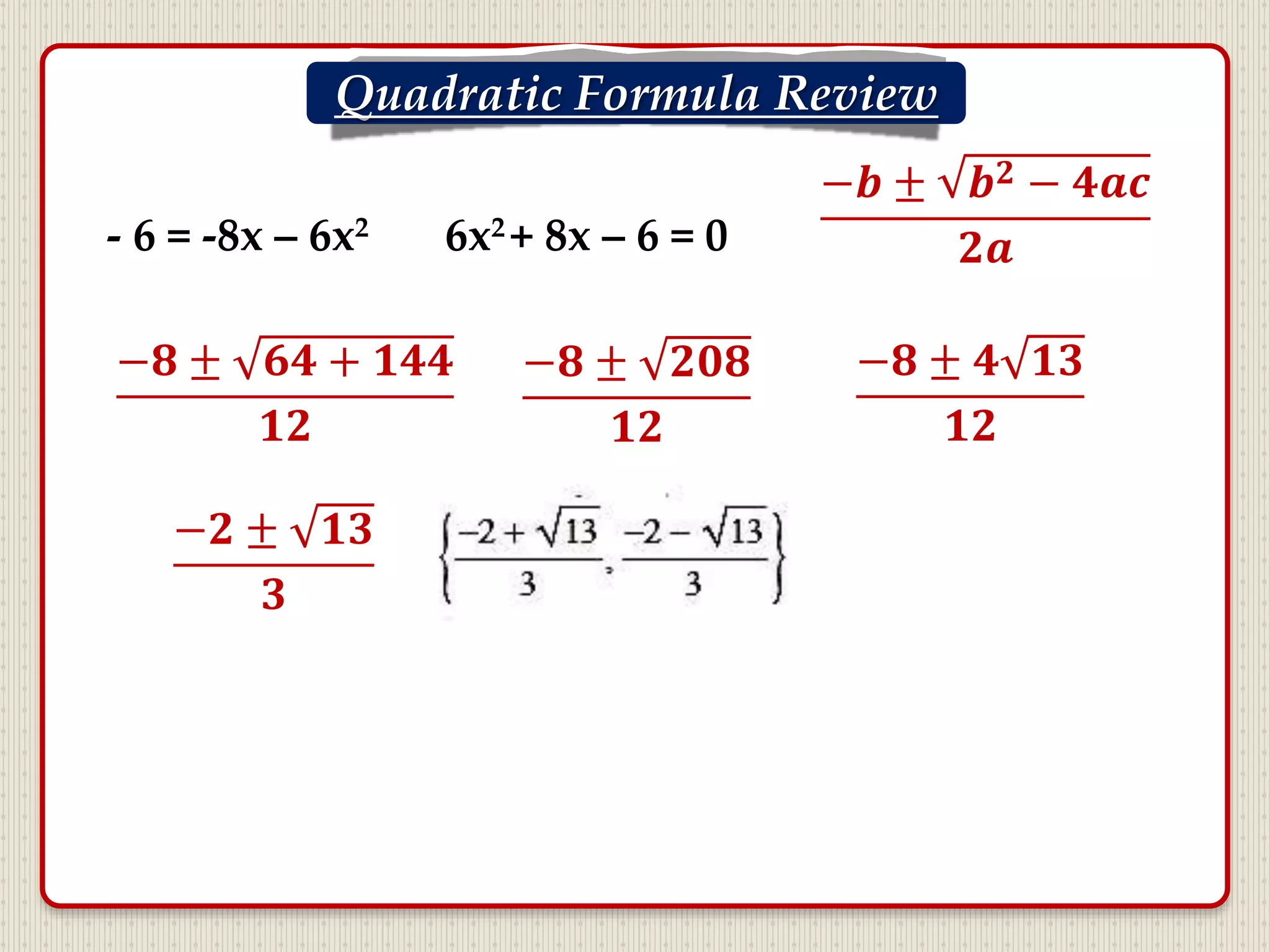
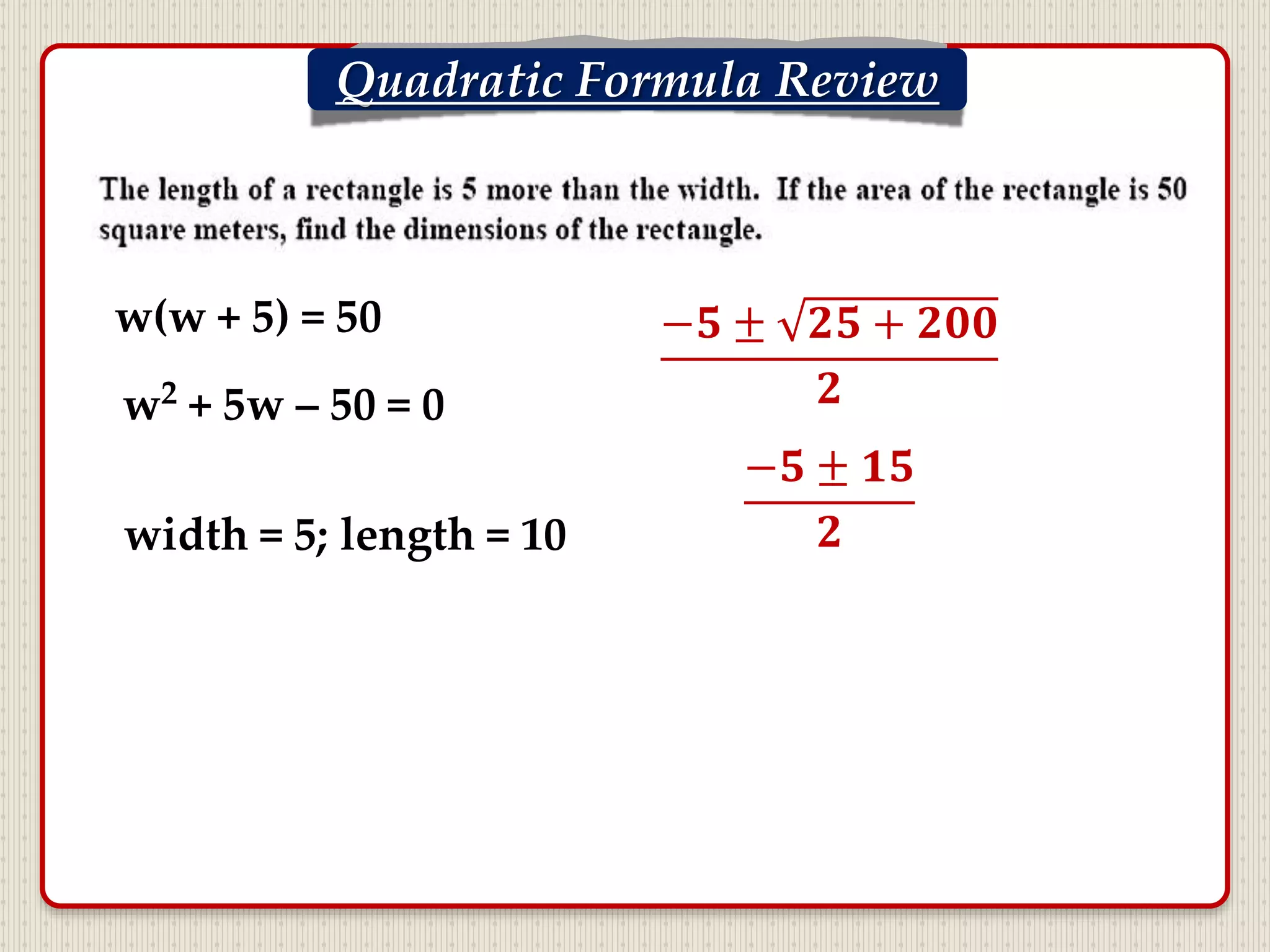
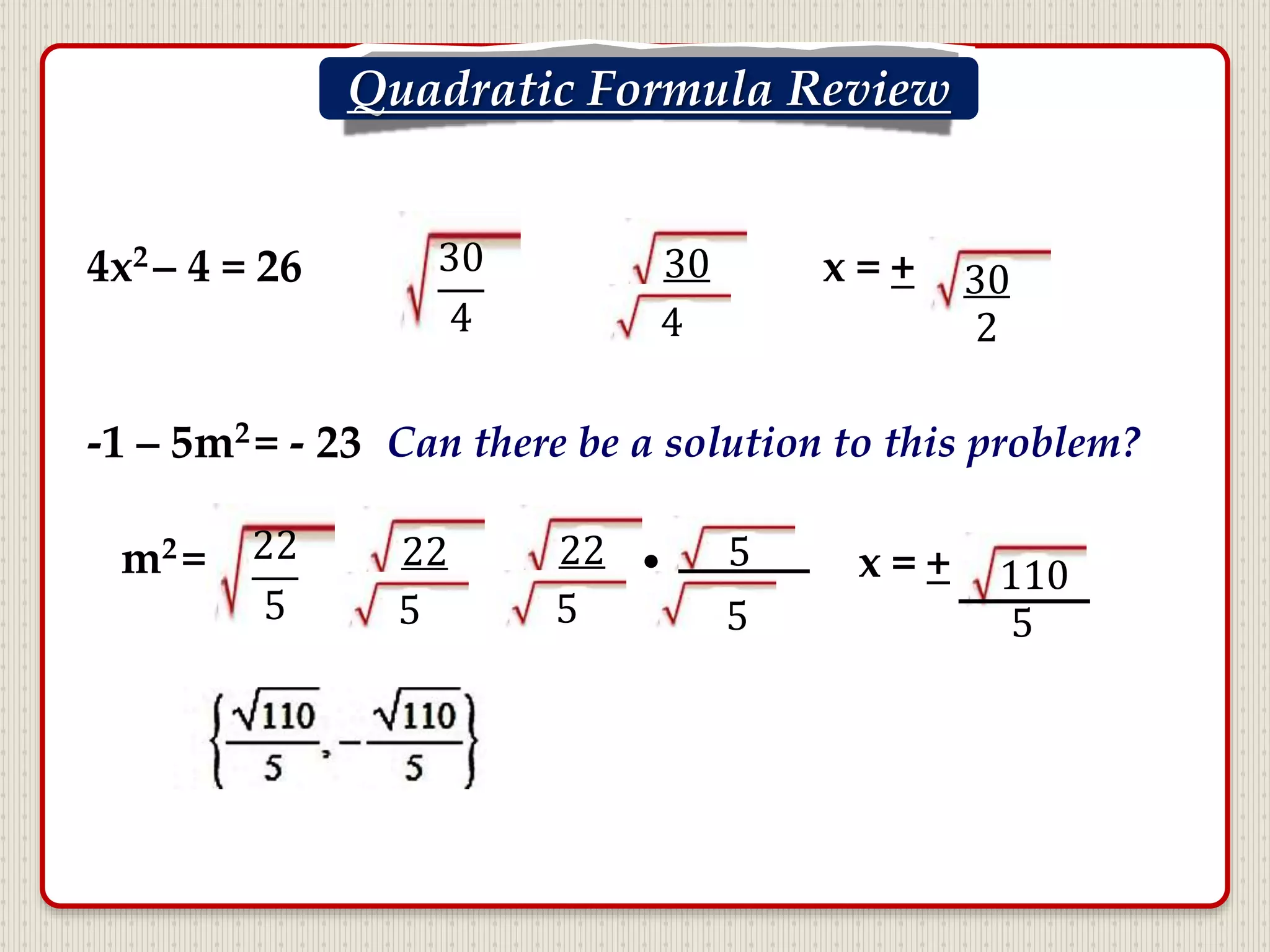
- There is a review scheduled for the quadratic formula tomorrow and examples are provided of using the formula to solve quadratic equations.
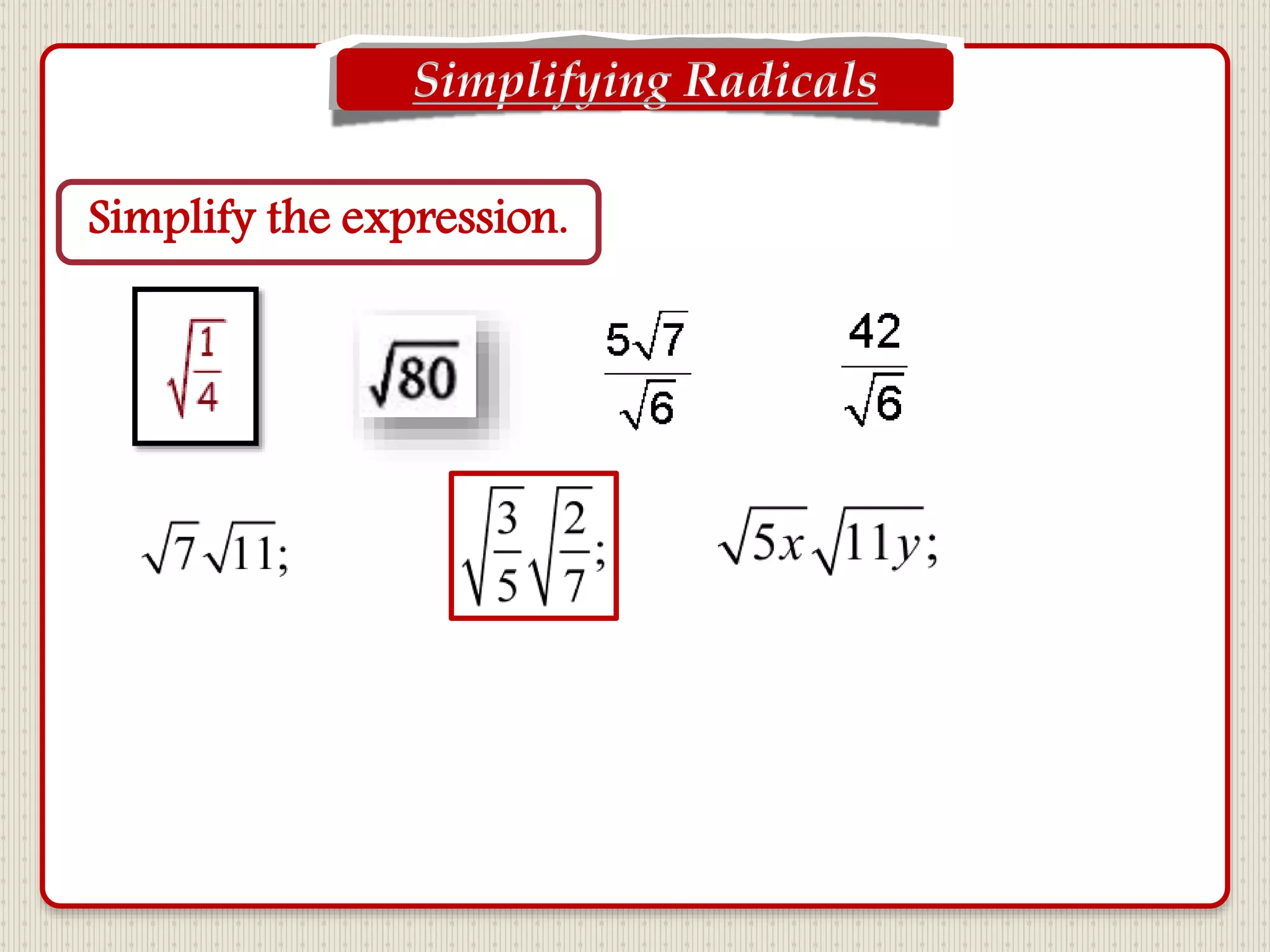
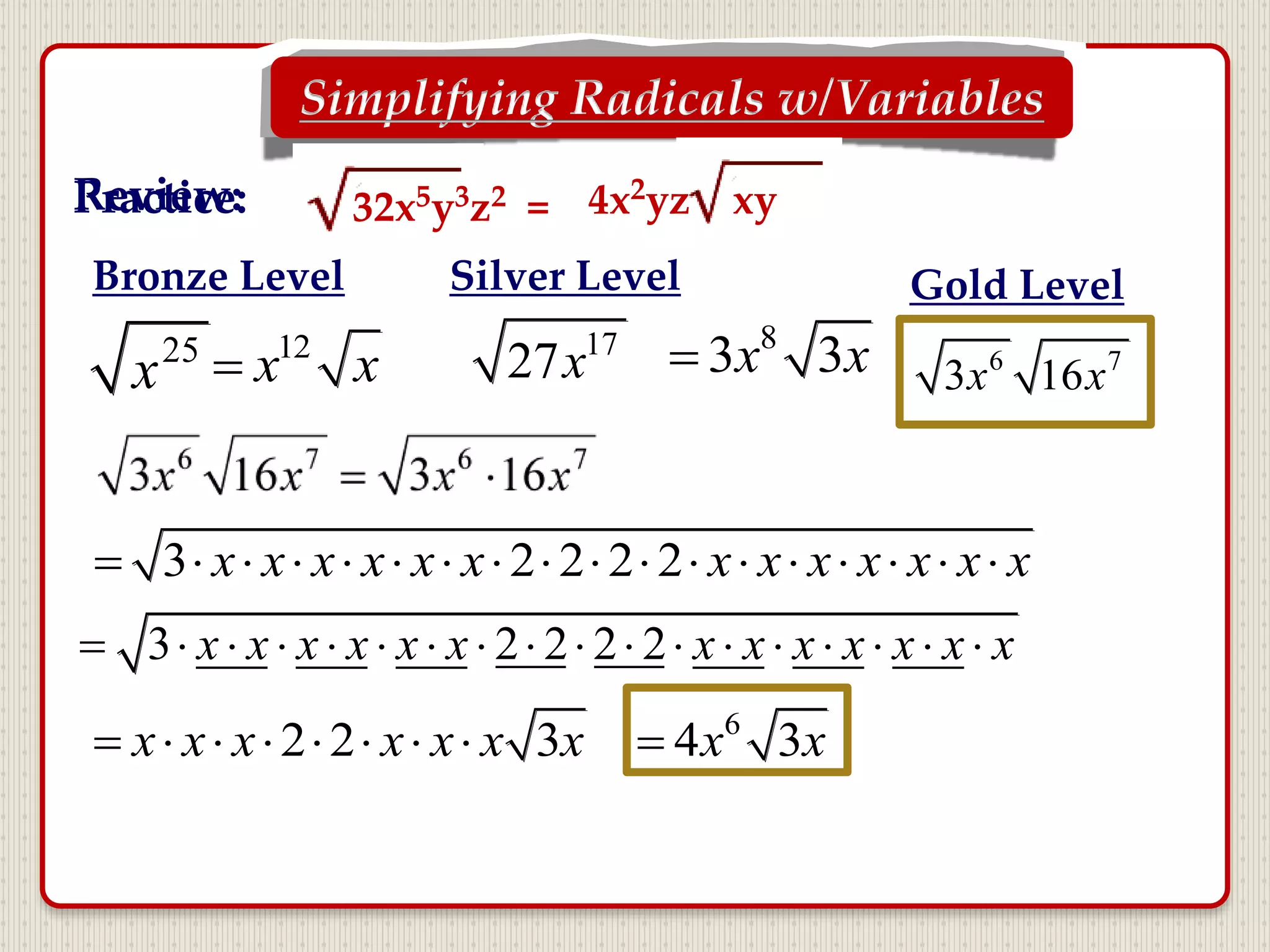
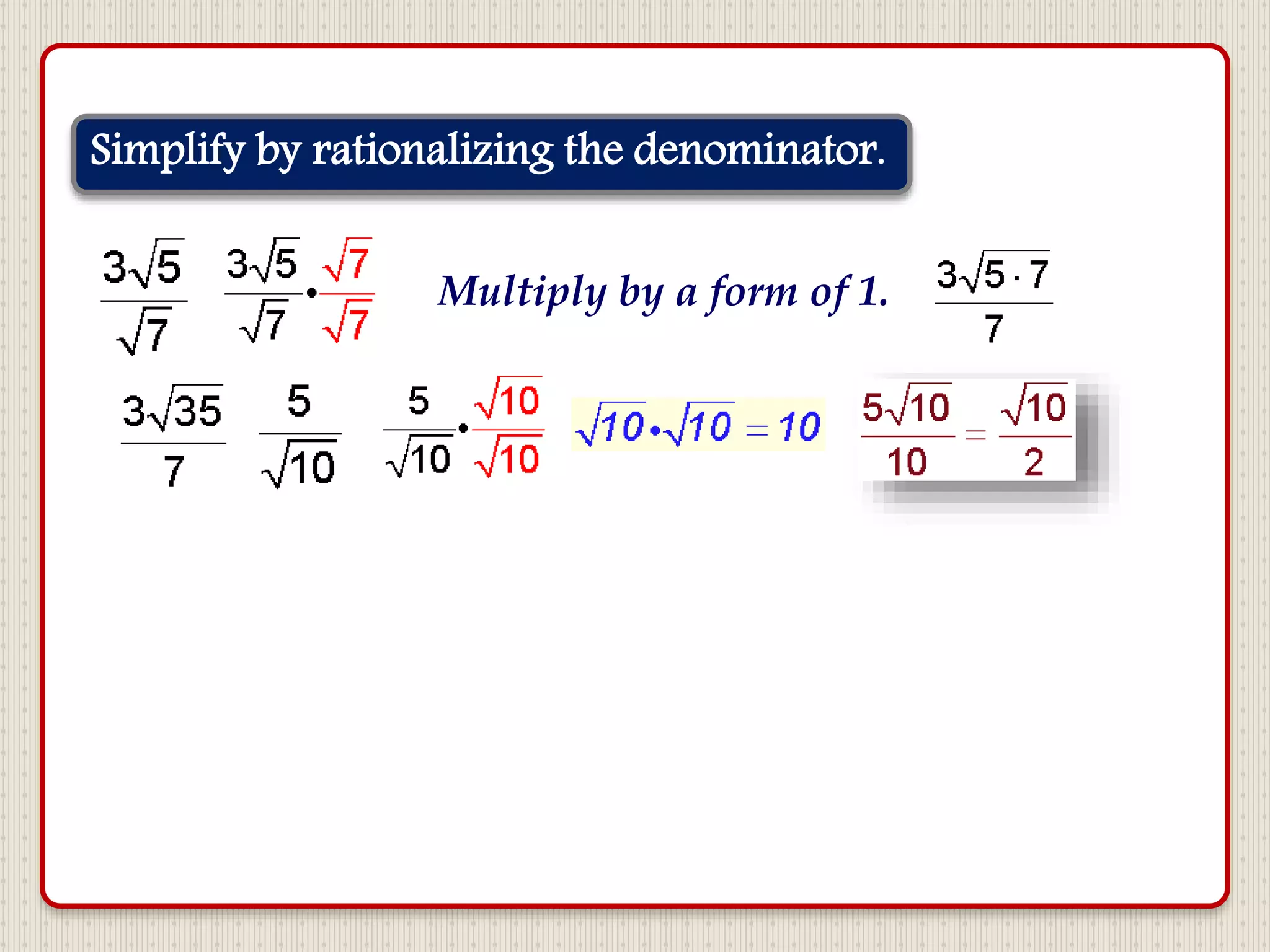
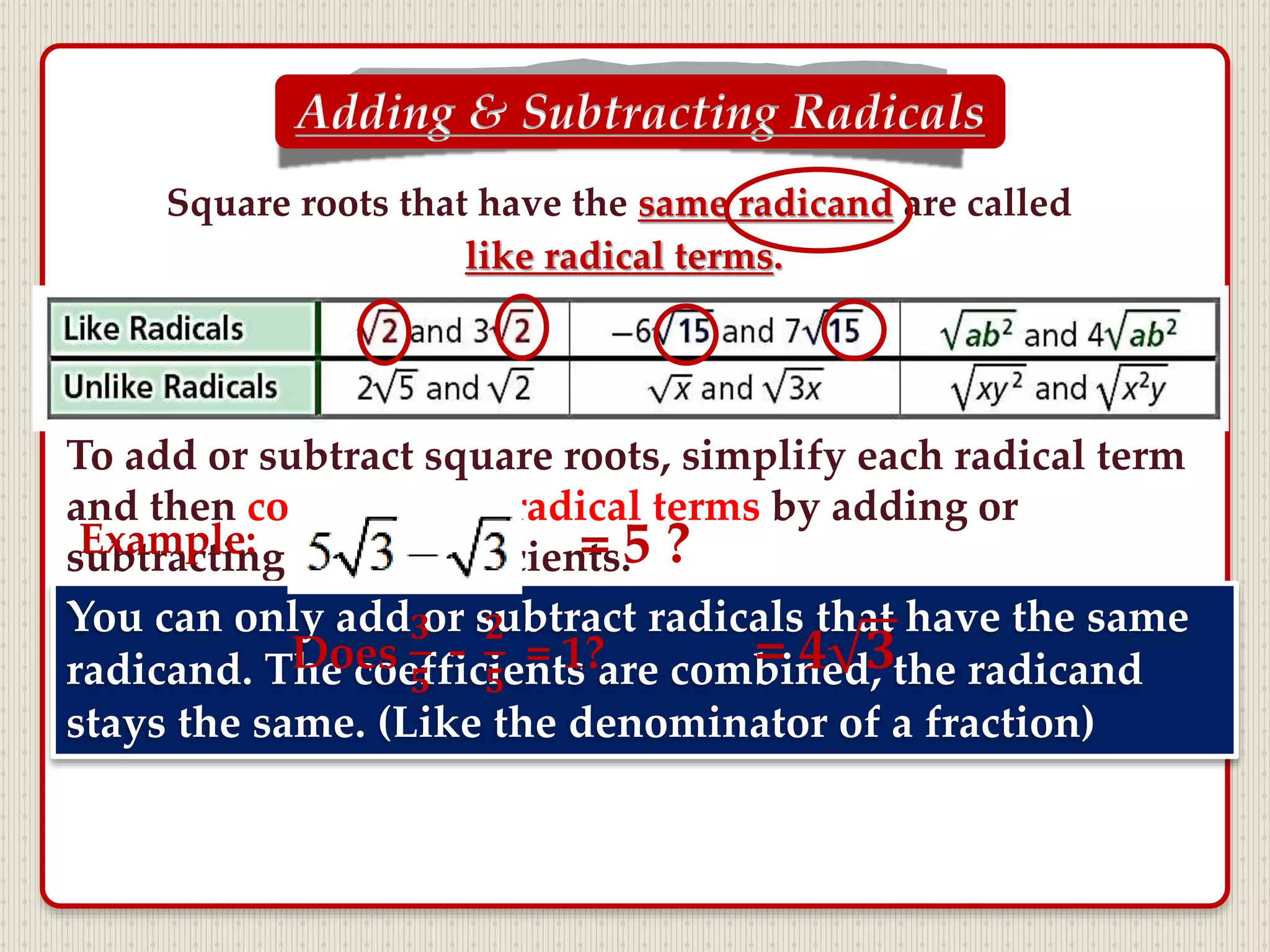
- Examples are also given of simplifying radical expressions through combining like terms, rationalizing denominators containing radicals, and adding/subtracting radical expressions.
- Notes cover properties of square roots, simplifying radicals with variables, rationalizing binomial denominators, and solving word problems involving areas of squares using radicals.