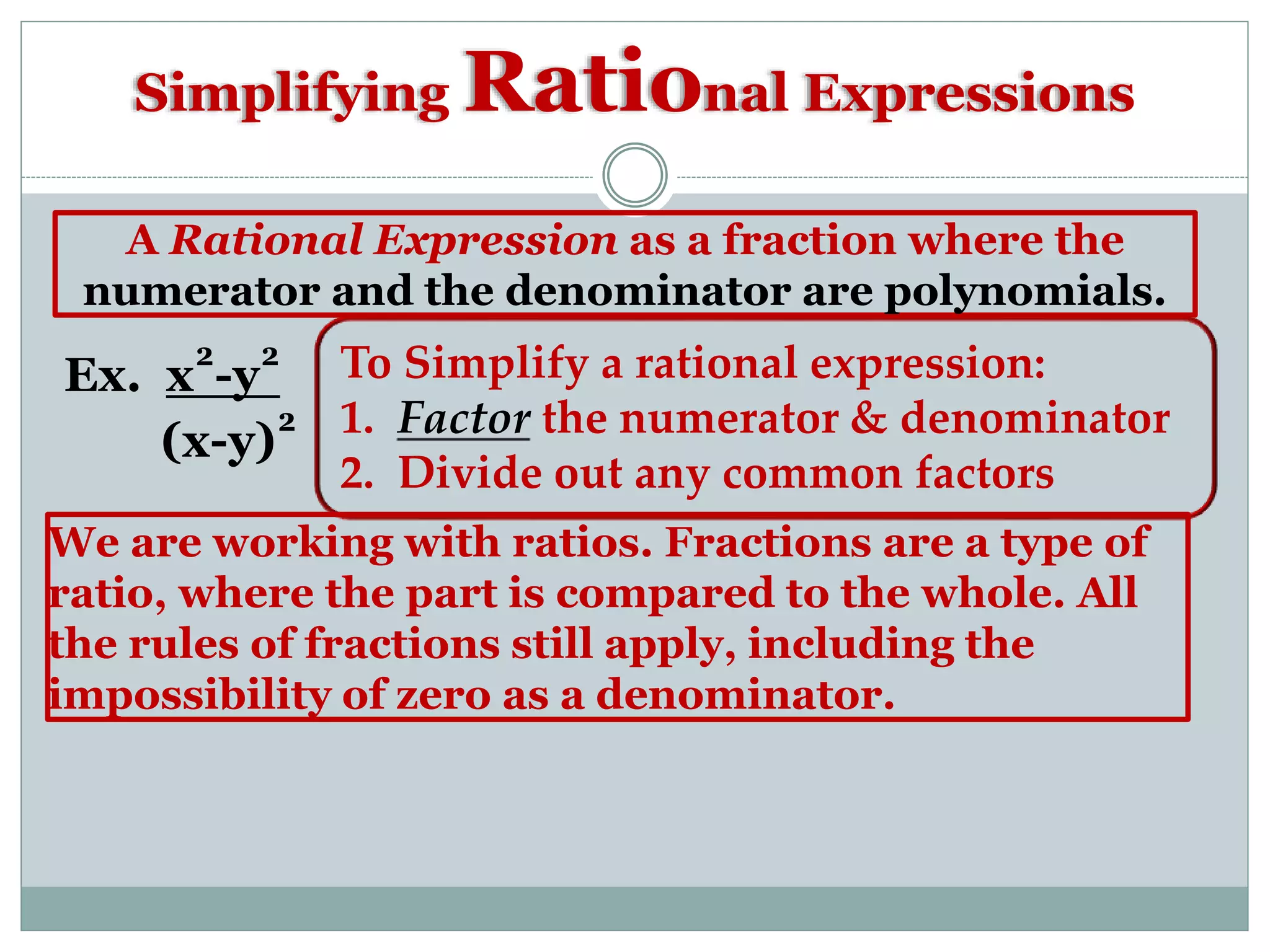
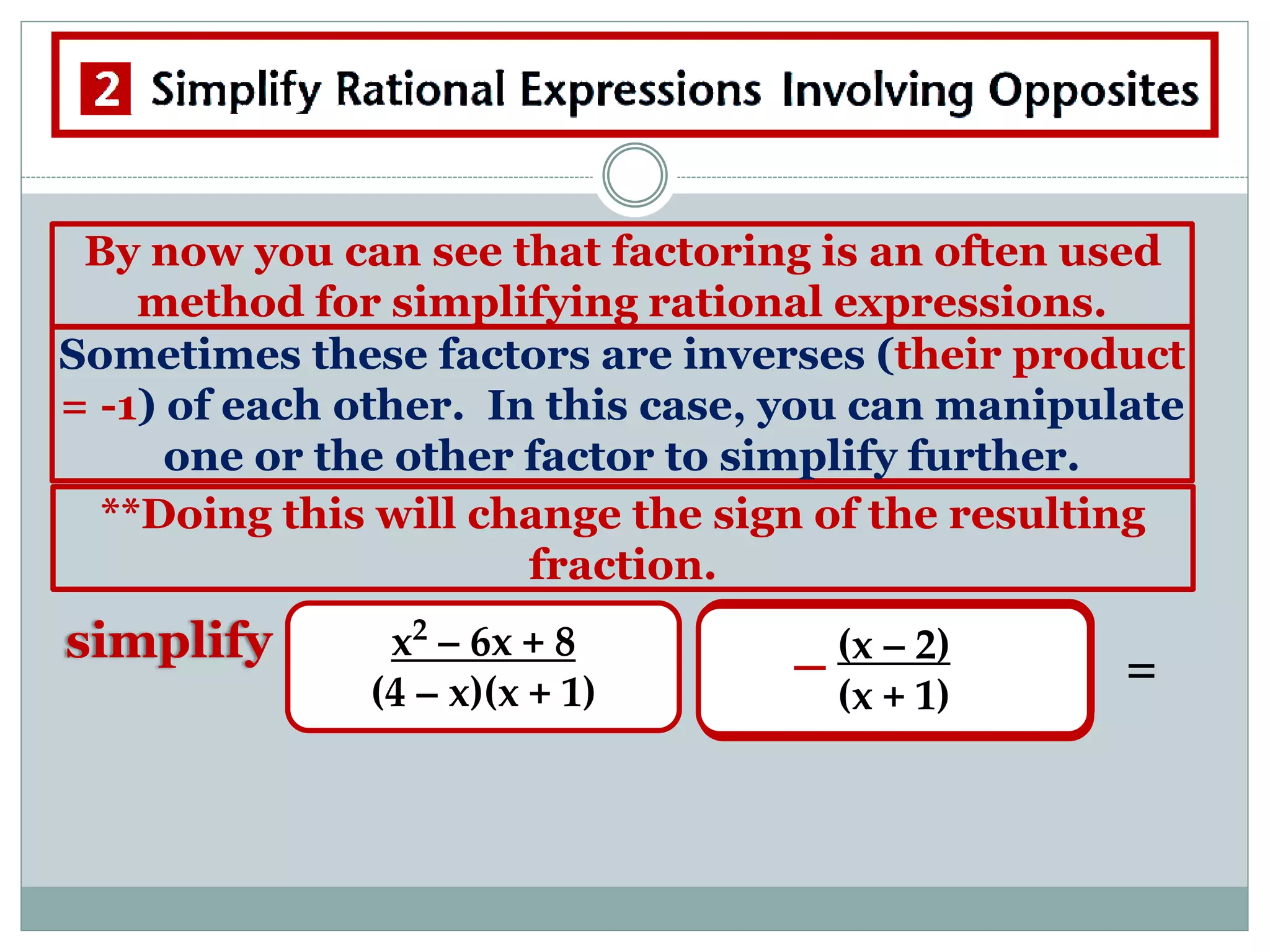
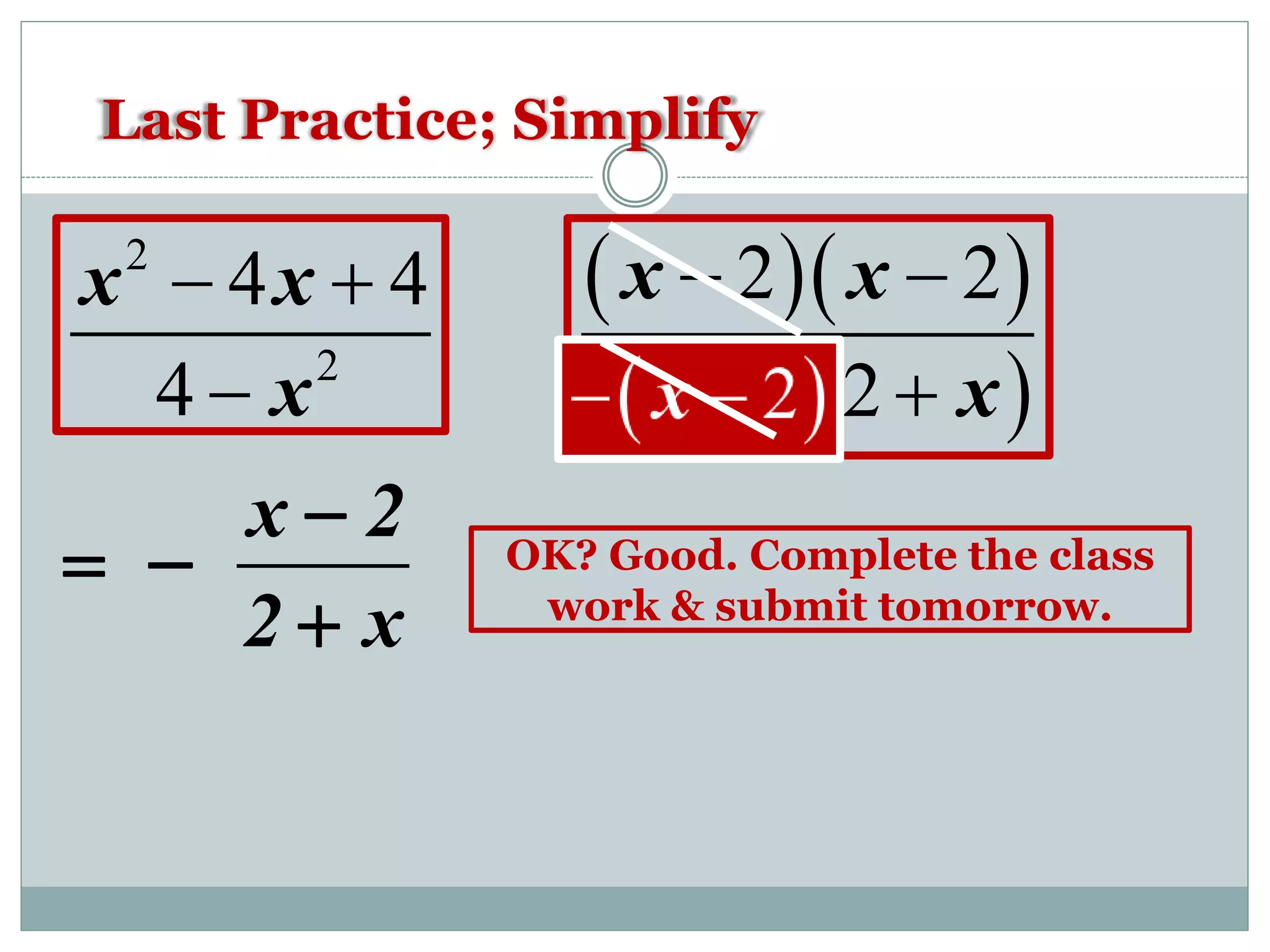
This document provides a review for a final exam on simplifying rational expressions. It includes examples of simplifying rational expressions by factoring the numerator and denominator and canceling common factors. It also discusses excluded values where the denominator cannot equal zero. Practice problems are provided to simplify rational expressions and identify excluded values. The document emphasizes the importance of factoring, canceling common factors, and paying attention to excluded values when simplifying rational expressions.