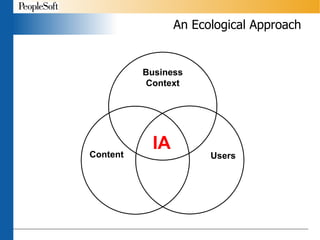
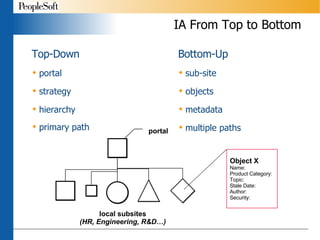
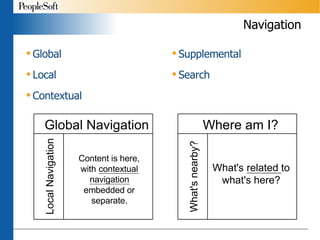
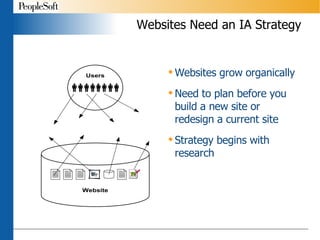
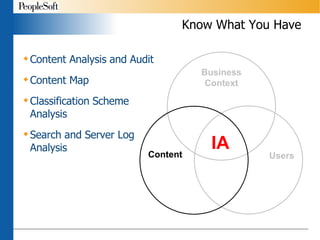
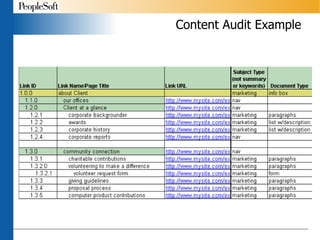
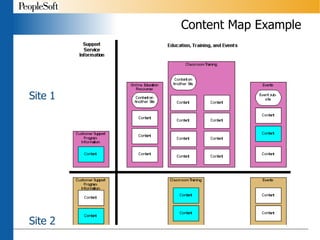
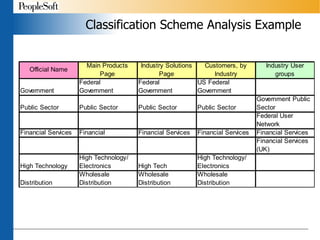
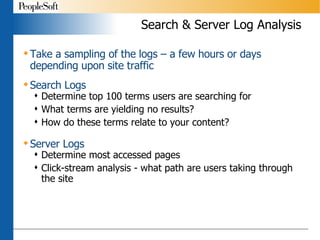
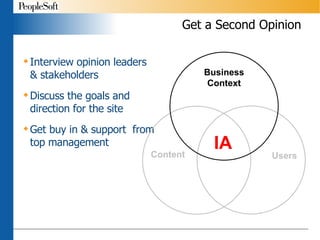
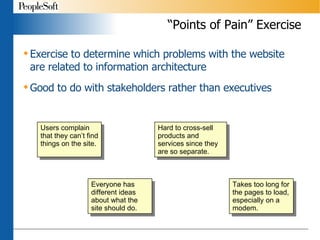
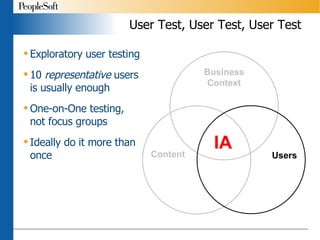
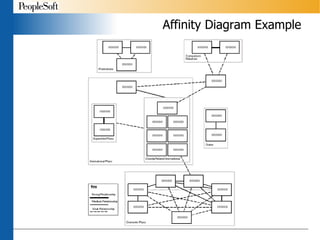
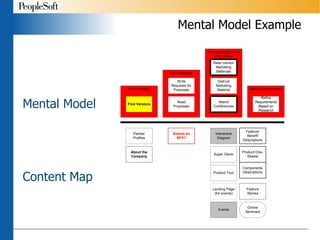
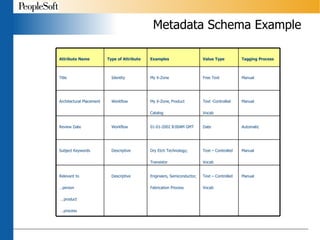
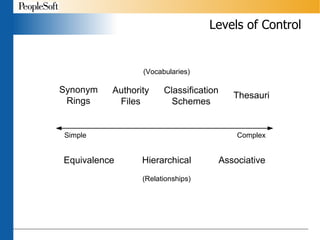
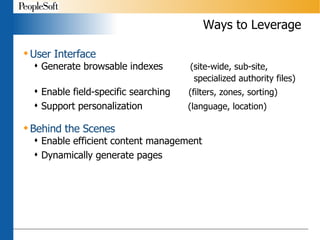
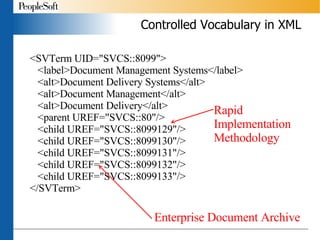
The document outlines the principles and strategies of information architecture (IA), emphasizing the importance of structuring and organizing information systems to meet user needs. Key components include content analysis, user testing, and collaborative planning to enhance navigational systems and improve user experience. It also discusses the use of metadata and effective labeling to facilitate information retrieval and site organization.
![Thank You Chiara Fox Information Architect [email_address] Presentation available at http://www.geocities.com/chiarafox PeopleSoft http://www.peoplesoft.com](https://image.slidesharecdn.com/makingiareal-1222850065802253-8/85/Making-IA-Real-Planning-an-Information-Architecture-Strategy-35-320.jpg)