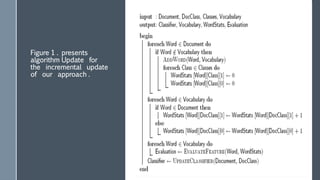
This document discusses machine learning and its applications to email. It begins with definitions of machine learning and its goal of allowing computers to learn from data without being explicitly programmed. The document then discusses the history of machine learning, including early enthusiasm, dark ages, renaissance, and current maturity. It describes three main types of machine learning: supervised, semi-supervised, and unsupervised learning. The document focuses on applications of machine learning to email, including automatic answering, automatic organization into folders, email summarization, spam filtering, and dynamic feature selection for classification. It concludes by noting other potential applications like medical imaging and robotics.