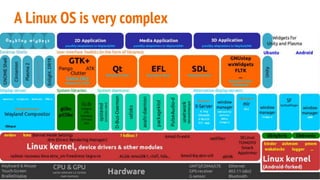
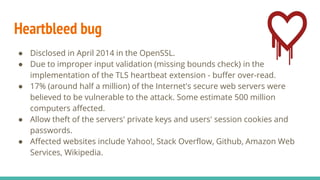
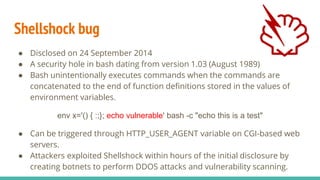
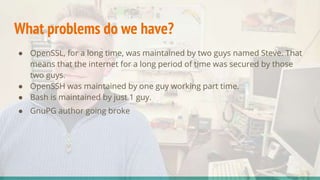
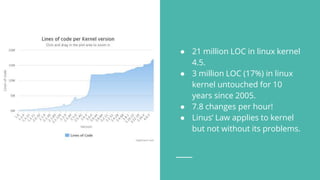
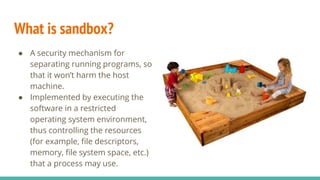
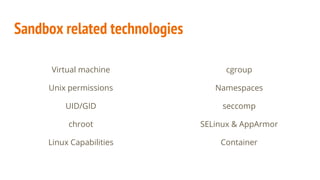
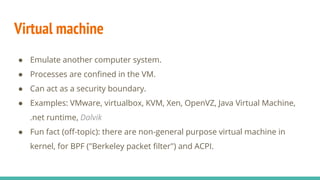
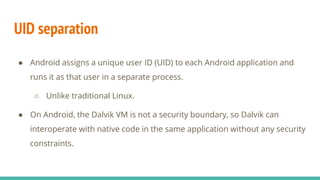
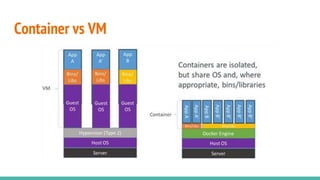
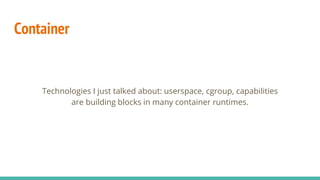
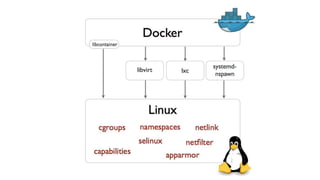
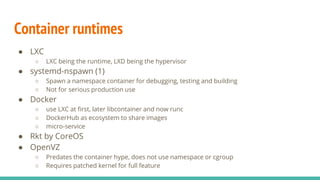
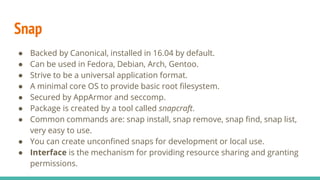
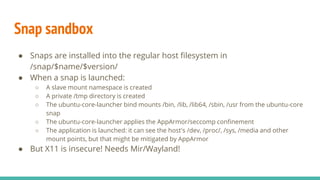
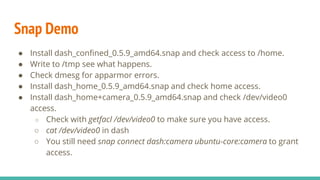
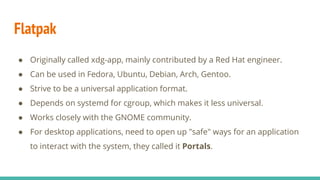
The document discusses the evolution and security of the Linux operating system, emphasizing its complexity and wide usage across various platforms, including containers. It highlights significant security vulnerabilities like Heartbleed and Shellshock, as well as the development challenges in maintaining open-source projects. Additionally, it covers security mechanisms such as sandboxes, namespaces, seccomp, and various container technologies, alongside emerging packaging formats like Snap.













![{
"defaultAction": "SCMP_ACT_ERRNO",
"syscalls": [
{
"name": "accept",
"action": "SCMP_ACT_ALLOW",
"args": []
},
{
"name": "accept4",
"action": "SCMP_ACT_ALLOW",
"args": []
...
seccomp in Docker Example
● Pass a docker profile (in JSON
format) when running your
container.
● Docker's default seccomp
profile is a whitelist.
● Syscalls such as clone, ptrace,
reboot, umount are not in
whitelist.](https://image.slidesharecdn.com/linux1-171119123607/85/Linux-56-320.jpg)
![AppArmor profile /etc/apparmor.d/sbin.dhclient
#include <tunables/global>
/sbin/dhclient flags=(attach_disconnected) {
#include <abstractions/base>
#include <abstractions/nameservice>
#include <abstractions/openssl>
capability net_bind_service,
capability net_raw,
capability sys_module,
capability dac_override,
capability net_admin,
network packet,
network raw,
@{PROC}/[0-9]*/net/ r,
@{PROC}/[0-9]*/net/** r,
/sbin/dhclient mr,
/bin/bash mr,
/etc/dhclient.conf r,
/etc/dhcp/ r,
/etc/dhcp/** r,
/var/lib/dhcp{,3}/dhclient* lrw,
/{,var/}run/dhclient*.pid lrw,
/{,var/}run/dhclient*.lease* lrw,](https://image.slidesharecdn.com/linux1-171119123607/85/Linux-60-320.jpg)




![Snapcraft example
name: dash
version: "0.5.9"
summary: dash shell
description: |
The Debian Almquist Shell (dash) is a POSIX-compliant shell derived
from ash.
Since it executes scripts faster than bash, and has fewer library
dependencies (making it more robust against software or hardware
failures), it is used as the default system shell on Debian systems.
apps:
dash:
command: dash
plugs: [home, camera]](https://image.slidesharecdn.com/linux1-171119123607/85/Linux-75-320.jpg)
![Snap interface
# Description: Can access non-hidden files in user's $HOME. This is restricted
# because it gives file access to all of the user's $HOME.
# Usage: reserved
# Note, @{HOME} is the user's $HOME, not the snap's $HOME
# Allow read access to toplevel $HOME for the user
owner @{HOME}/ r,
# Allow read/write access to all non-hidden files that aren't in ~/snap/
# allow creating a few files not caught above
owner @{HOME}/{s,sn,sna}{,/} rwk,
# allow access to gvfs mounts (only allow writes to files, not mount point)
owner /run/user/[0-9]*/gvfs/** r,
owner /run/user/[0-9]*/gvfs/*/** w,](https://image.slidesharecdn.com/linux1-171119123607/85/Linux-76-320.jpg)


![Controversy
https://lkml.org/lkml/2014/4/2/420
On Wed, Apr 2, 2014 at 11:42 AM, Steven Rostedt <rostedt@goodmis.org> wrote:
>
> The response is:
>
> "Generic terms are generic, not the first user owns them."
And by "their" you mean Kay Sievers.
Key, I'm f*cking tired of the fact that you don't fix problems in the
code *you* write, so that the kernel then has to work around the
problems you cause.
Greg - just for your information, I will *not* be merging any code
from Kay into the kernel until this constant pattern is fixed.
[show linus’s middle finger photo]](https://image.slidesharecdn.com/linux1-171119123607/85/Linux-85-320.jpg)
![systemd 101
● Important directories:
○ /etc/systemd/system
○ /lib/systemd/system
● systemctl list-units [--type service|target|...] [--all]
● systemctl [start|stop|restart|enable|disable] <service>
● systemctl get-default
● systemctl set-default <target>](https://image.slidesharecdn.com/linux1-171119123607/85/Linux-86-320.jpg)
![Service unit configuration
PrivateNetwork=yes|no
● ‘no’ means loopback and no access to network interfaces
● fwupd.service:
[Service]
Type=dbus
BusName=org.freedesktop.fwupd
ExecStart=/usr/lib/x86_64-linux-gnu/fwupd/fwupd
PrivateNetwork=yes
PrivateTmp=yes
RestrictAddressFamilies=AF_UNIX|AF_INET|AF_INET6](https://image.slidesharecdn.com/linux1-171119123607/85/Linux-94-320.jpg)


![Service unit configuration
User=
Group=
● Example:
saned@.service:
[Service]
ExecStart=/usr/sbin/saned
User=saned
Group=saned](https://image.slidesharecdn.com/linux1-171119123607/85/Linux-98-320.jpg)