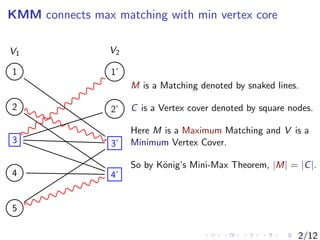
The document presents a study on combinatorial matrix theory, focusing on the connection between maximum matching and minimum vertex covers through the Kőnig-Menger-Maxwell theorem. It introduces a formal language for min-max reasoning and demonstrates the equivalence of fundamental theorems in graph theory, including Menger's theorem, Hall's theorem, and Dilworth's theorem. The authors also discuss potential future work, including the relationship between KMM and Pigeonhole Principle, and the ability of their formalism to prove complex matrix identities.



![LA with ΣB
1 -Induction
LA (i.e., LA with ΣB
0 -Induction), proves all the ring properties of
matrices (eg.,(AB)C = A(BC)), and LA over Z translates into
TC0
-Frege ([Cook-Soltys’04]).
Bounded Matrix Quantifiers: We let
(∃A ≤ n)α stands for (∃A)[|A| ≤ n ∧ α], and
(∀A ≤ n)α stands for (∀A)[|A| ≤ n → α].
LA with ΣB
1 -Induction correspond to polytime reasoning and proves
standard properties of the determinant, and translate into extended
Frege.
4/12](https://image.slidesharecdn.com/lics2013presentation-130701080217-phpapp01/85/Feasible-Combinatorial-Matrix-Theory-LICS2013-presentation-6-320.jpg)

![LA with ΣB
1 -Ind. proves KMM
Diagonal Property
∗
∗
0
...
00
0
0 . . .1
Either Aii = 1 or (∀j ≥ i)[Aij = 0 ∧ Aji = 0].
Claim Given any matrix A, ∃LA proves that there exist permutation
matrices P, Q such that PAQ has the diagonal property.
6/12](https://image.slidesharecdn.com/lics2013presentation-130701080217-phpapp01/85/Feasible-Combinatorial-Matrix-Theory-LICS2013-presentation-8-320.jpg)







![Dilworth’s Decomposition Theorem - Example
{}
{1} {2} {3}
{1, 2} {1, 3} {2, 3}
{1, 2, 3}
Let P = (⊂, 2X
), i.e., all subsets of
X with |X| = n with set inclusion,
x < y ⇐⇒ x ⊂ y.
(A) Suppose that the largest
chain in P has size . Then P can
be partitioned into antichains.
We have 4-antichains [{}] ,
[{1}, {2}, {3}] , [{1, 2}, {1, 3}, {2, 3}] ,
and [{1, 2, 3}] .
(B) Suppose that the largest
antichain in P has size .
Then P can be partitioned into
disjoint chains. We have
[{} ⊂ {1} ⊂ {1, 2} ⊂ {1, 2, 3}] ,
[{2} ⊂ {2, 3}] , and [{3} ⊂ {1, 3}].
10/12](https://image.slidesharecdn.com/lics2013presentation-130701080217-phpapp01/85/Feasible-Combinatorial-Matrix-Theory-LICS2013-presentation-16-320.jpg)

![Future Work
Can LA-Theory prove KMM?
What is the relationship between KMM and PHP?
(Eg. LA ∪ PHP KMM?)
Can LA ∪ KMM prove Hard Matrix Identities?
We would like to know whether LA ∪ KMM can prove hard
matrix identities, such as AB = I → BA = I. Of course, we
already know from [TZ11] that (non-uniform) NC2
-Frege is
sufficient to prove AB = I → BA = I, and from [Sol06] we
know that ∃LA can prove them also.
What about ∞-KMM?
12/12](https://image.slidesharecdn.com/lics2013presentation-130701080217-phpapp01/85/Feasible-Combinatorial-Matrix-Theory-LICS2013-presentation-18-320.jpg)