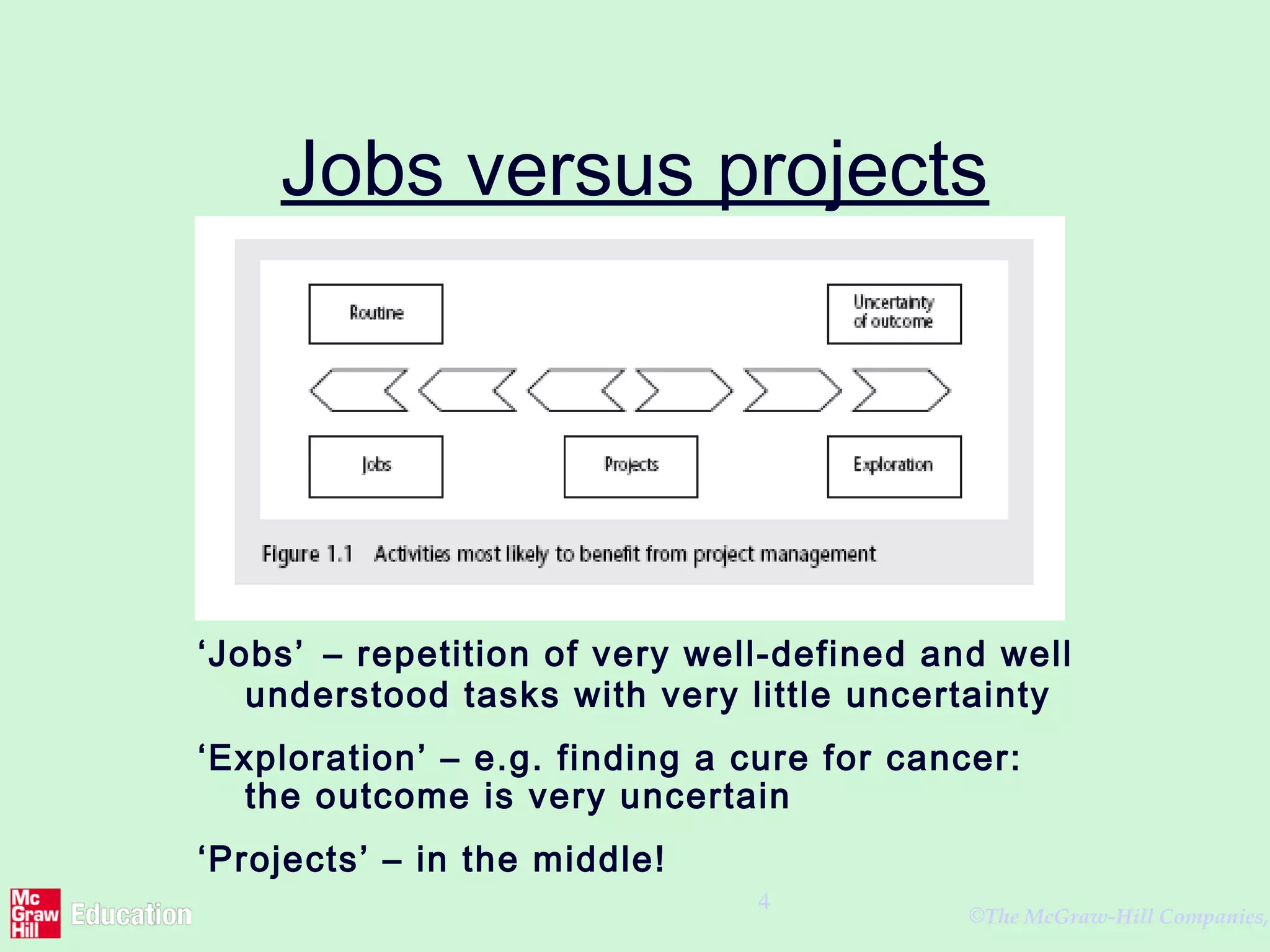
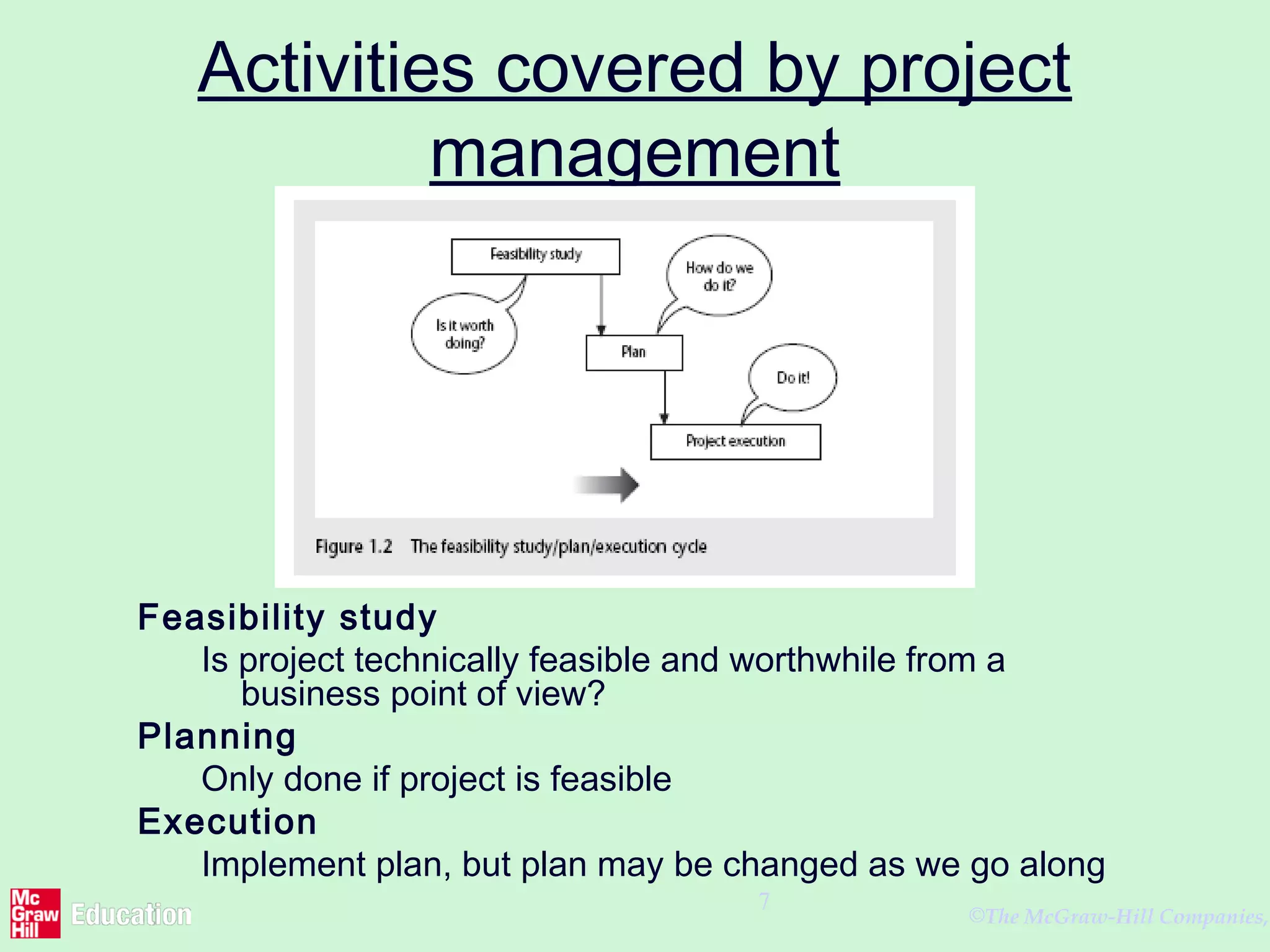
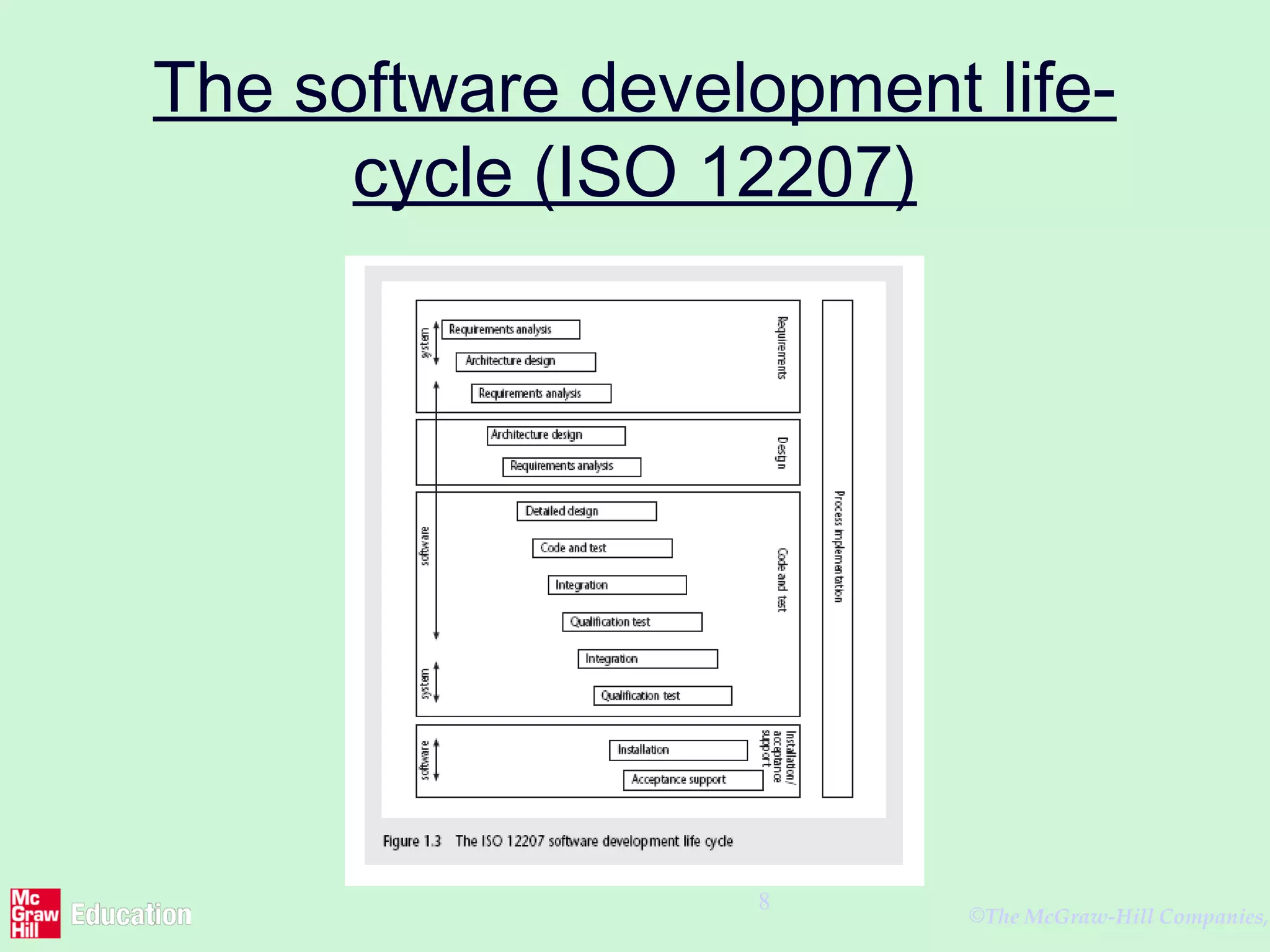
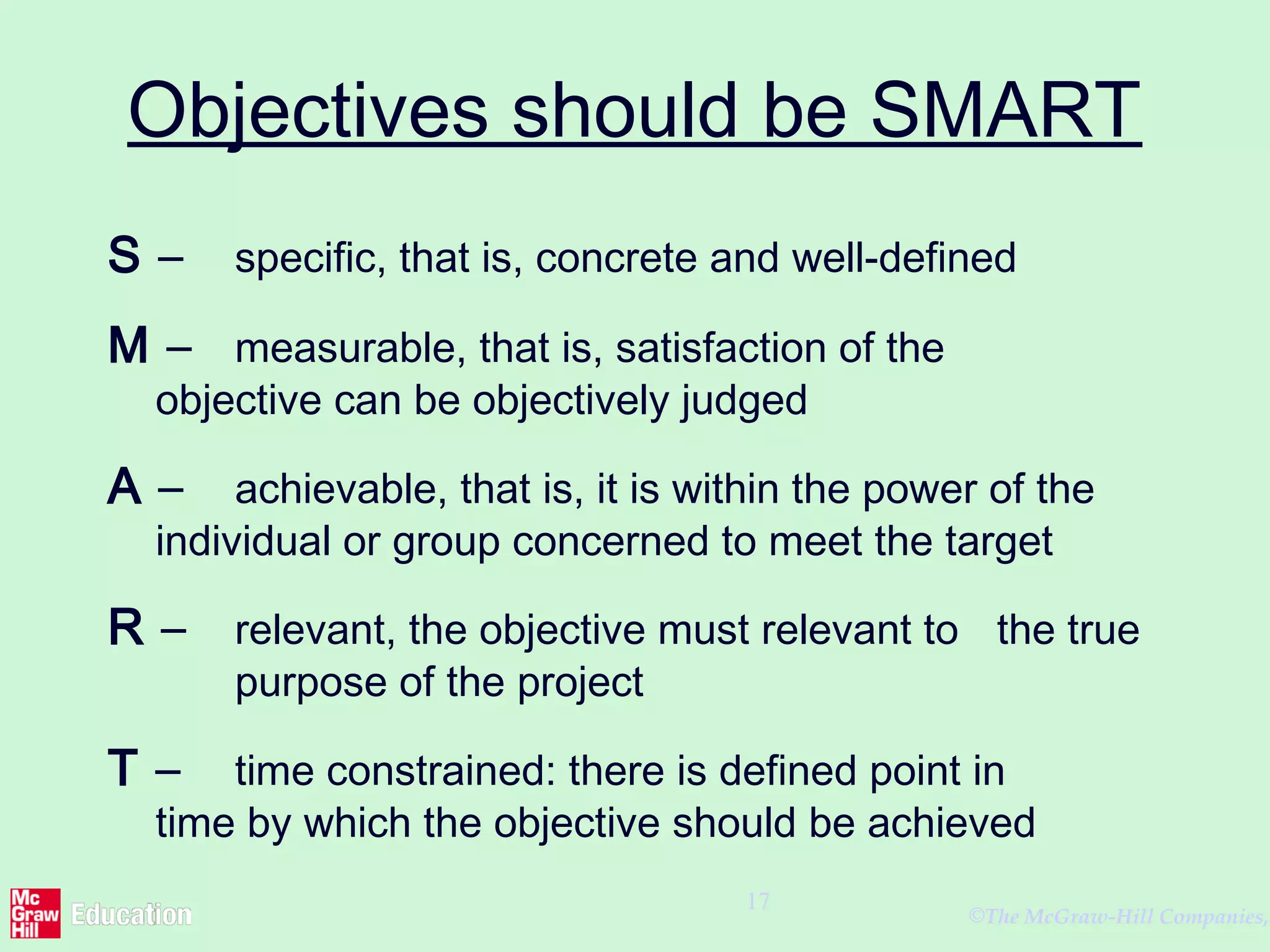
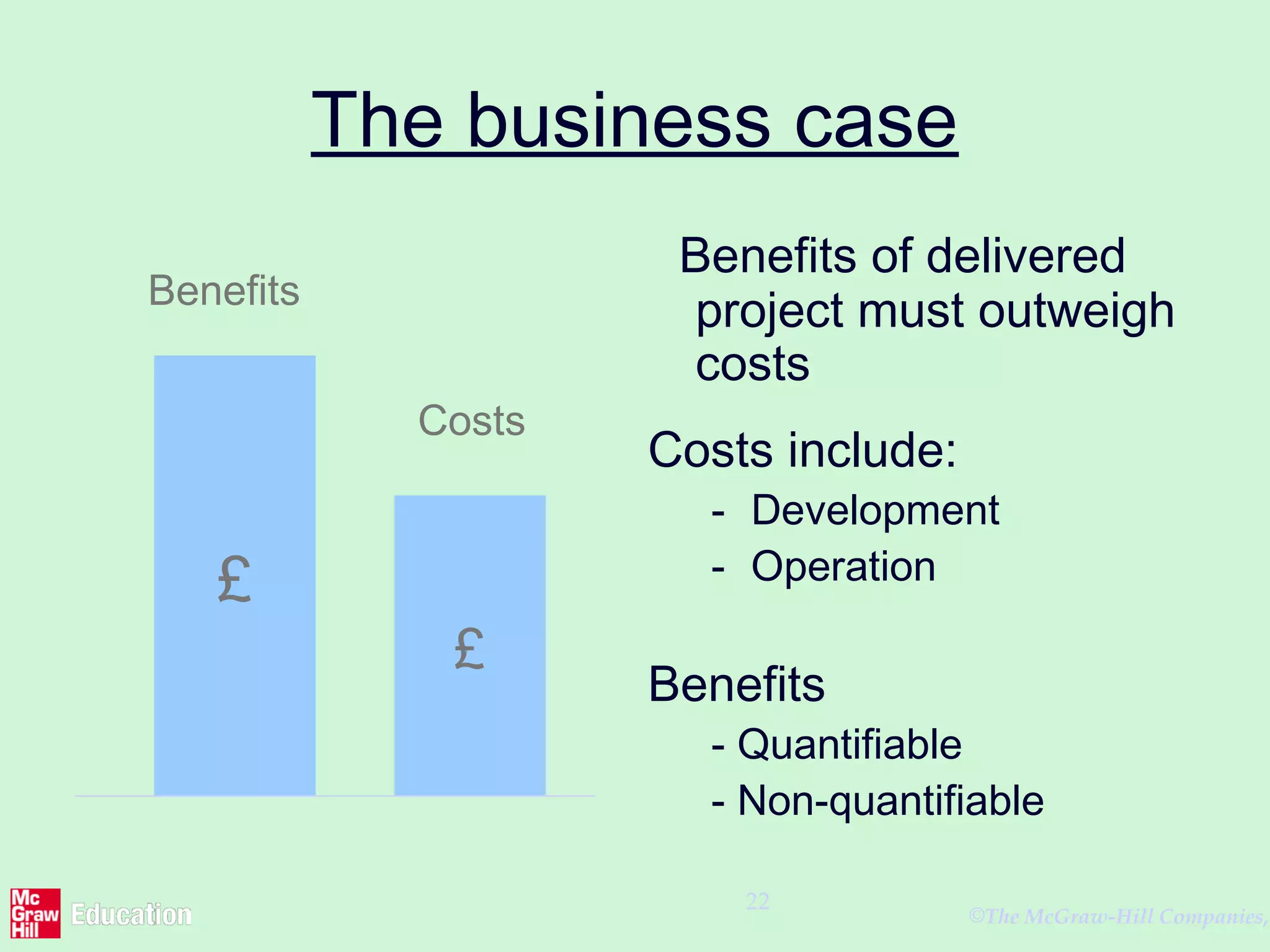
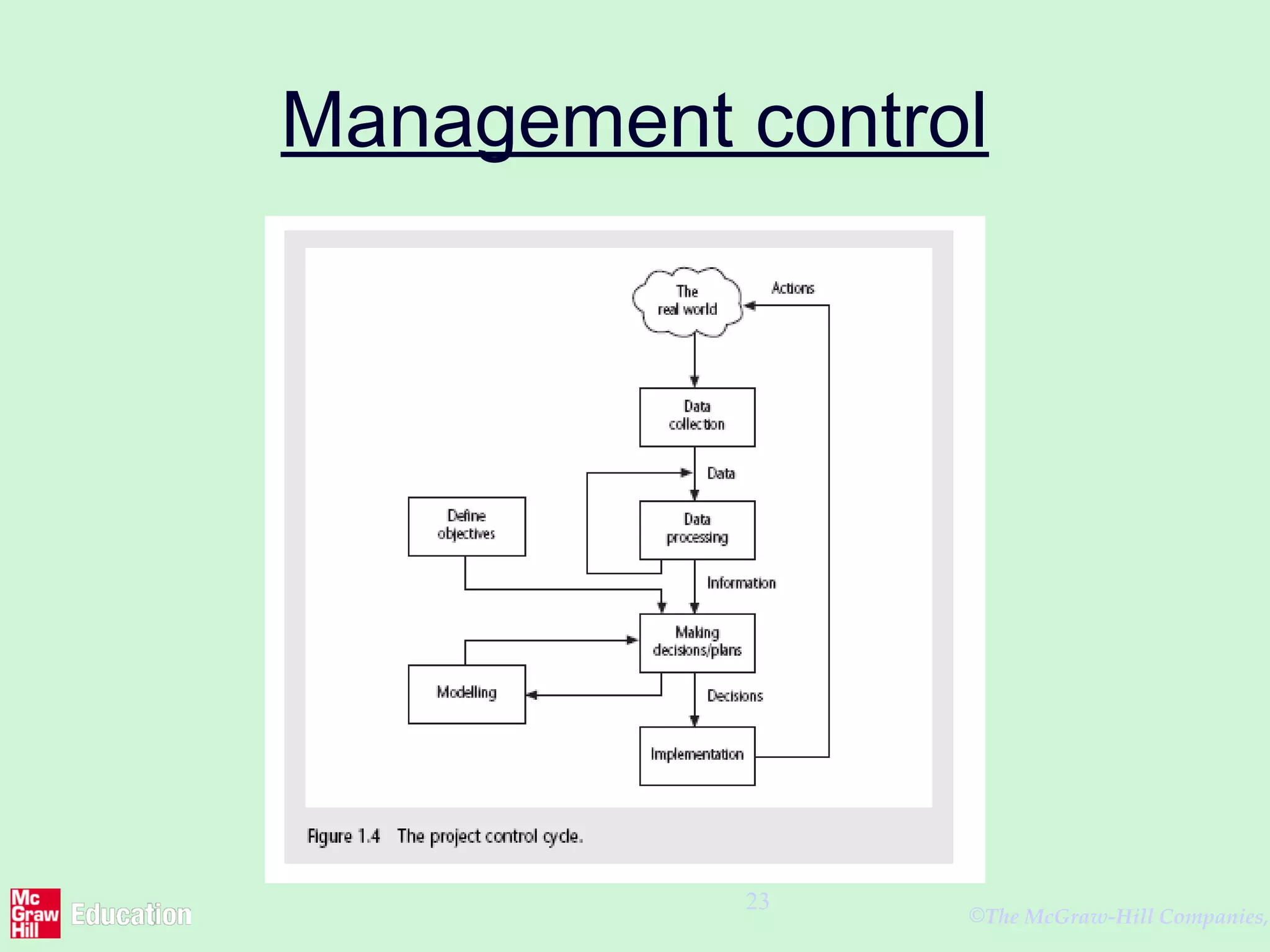
This document discusses software project management. It defines what constitutes a project and how software projects differ from other types of projects due to characteristics like invisibility and complexity. The document outlines the typical phases of a software development life cycle according to ISO 12207 standards. It also discusses the importance of setting clear, measurable objectives and establishing management controls to track progress and make adjustments throughout the project.