1) A computer accepts data as input, processes it according to programmed instructions, and produces output which it can store for future use.
2) Data is represented by characters like letters, numbers and symbols that can be interpreted by humans or computers. Information is organized data that has meaning.
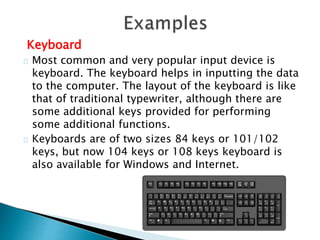
3) Common computer input devices include keyboards, mice, scanners, and microphones. Output devices display or print the results of processing and include monitors, printers, and speakers.