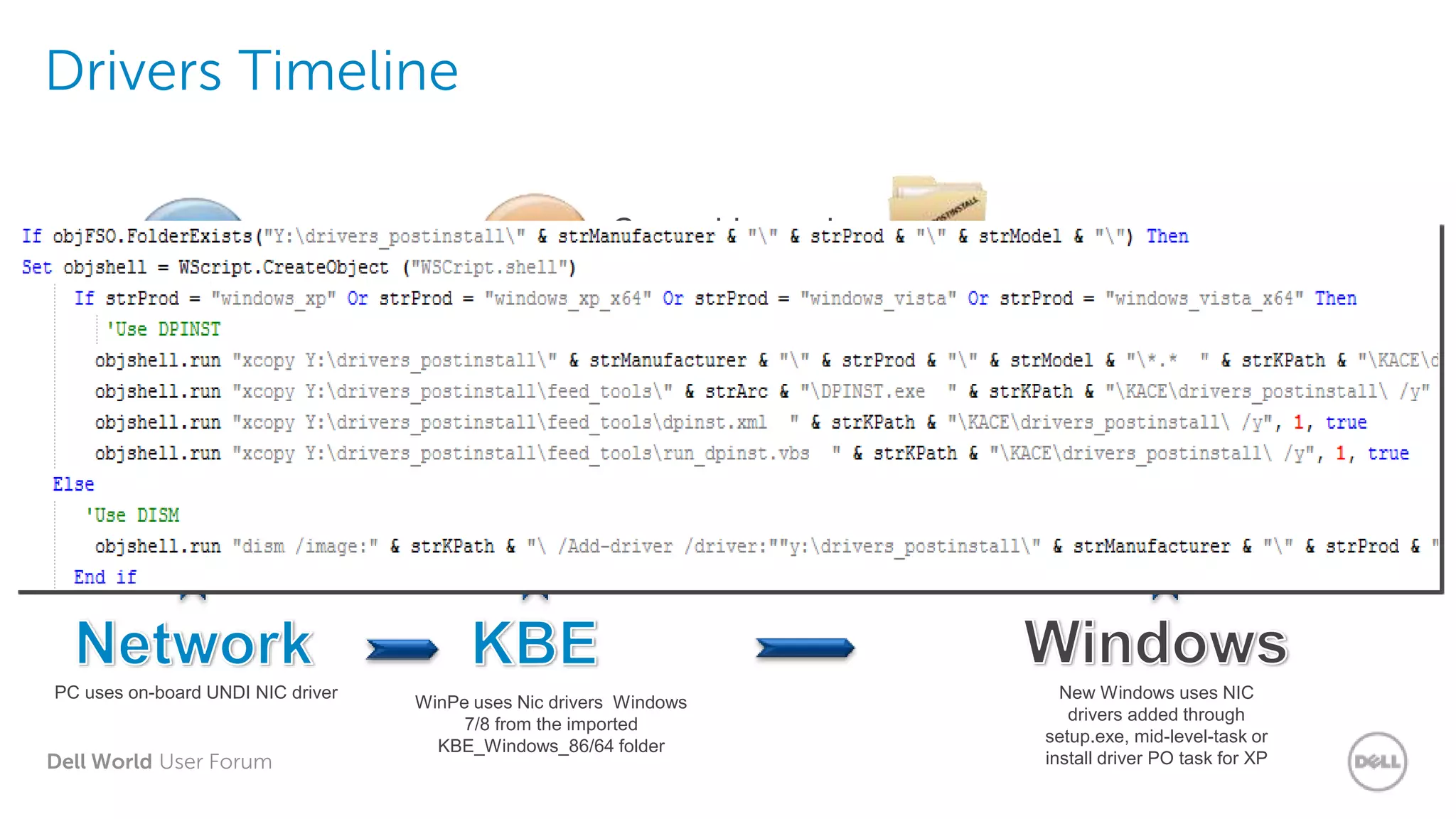
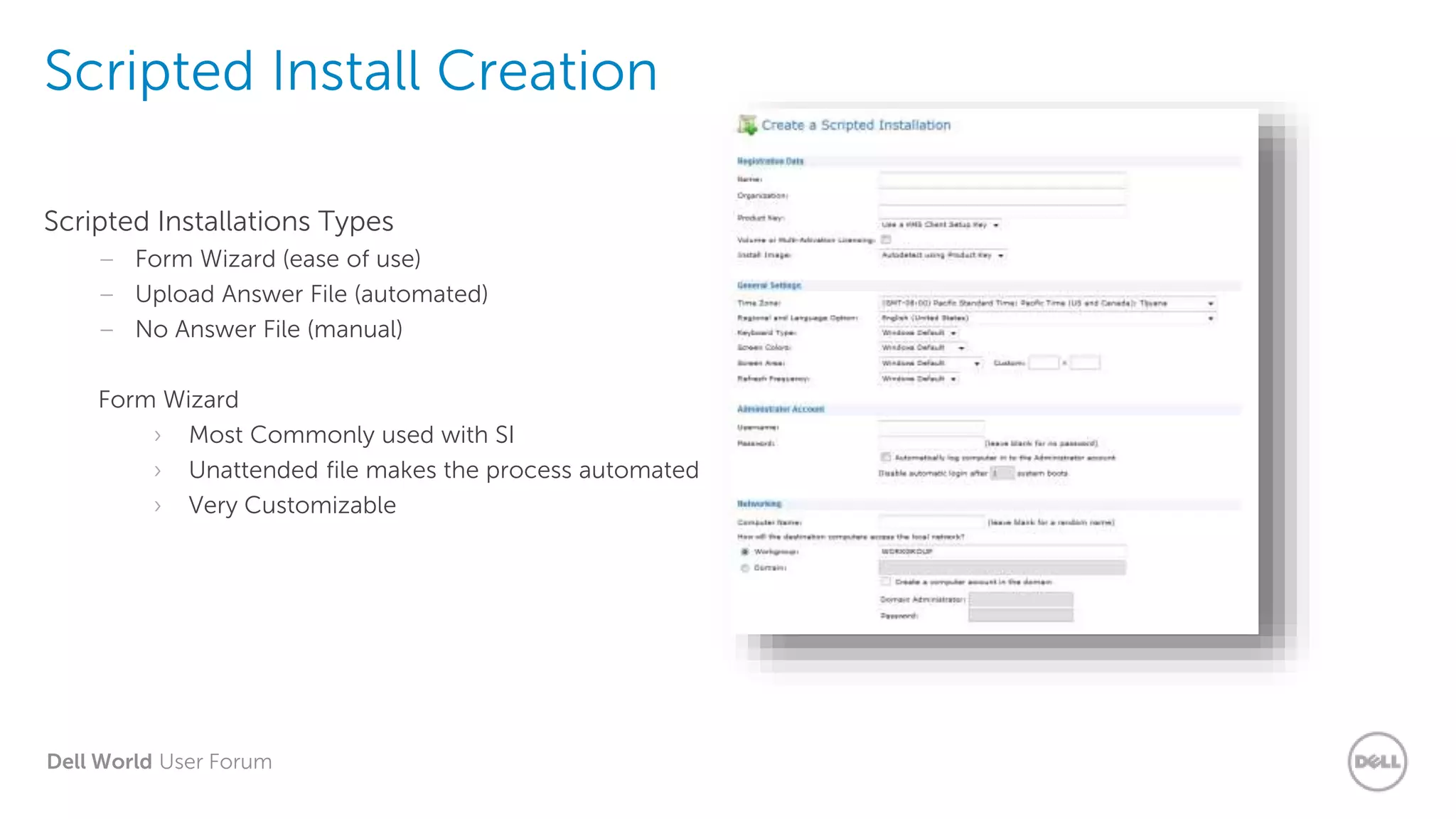
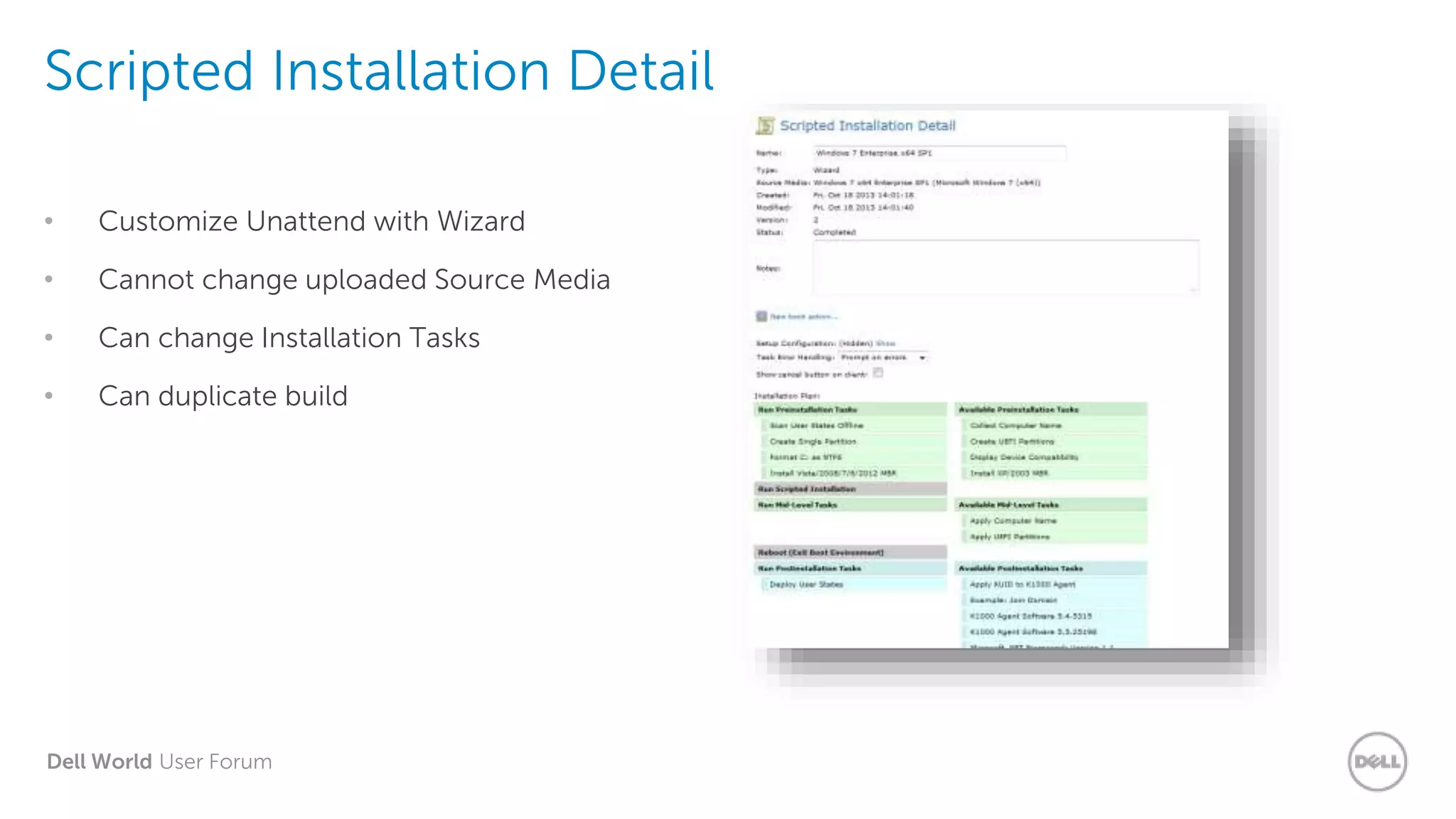
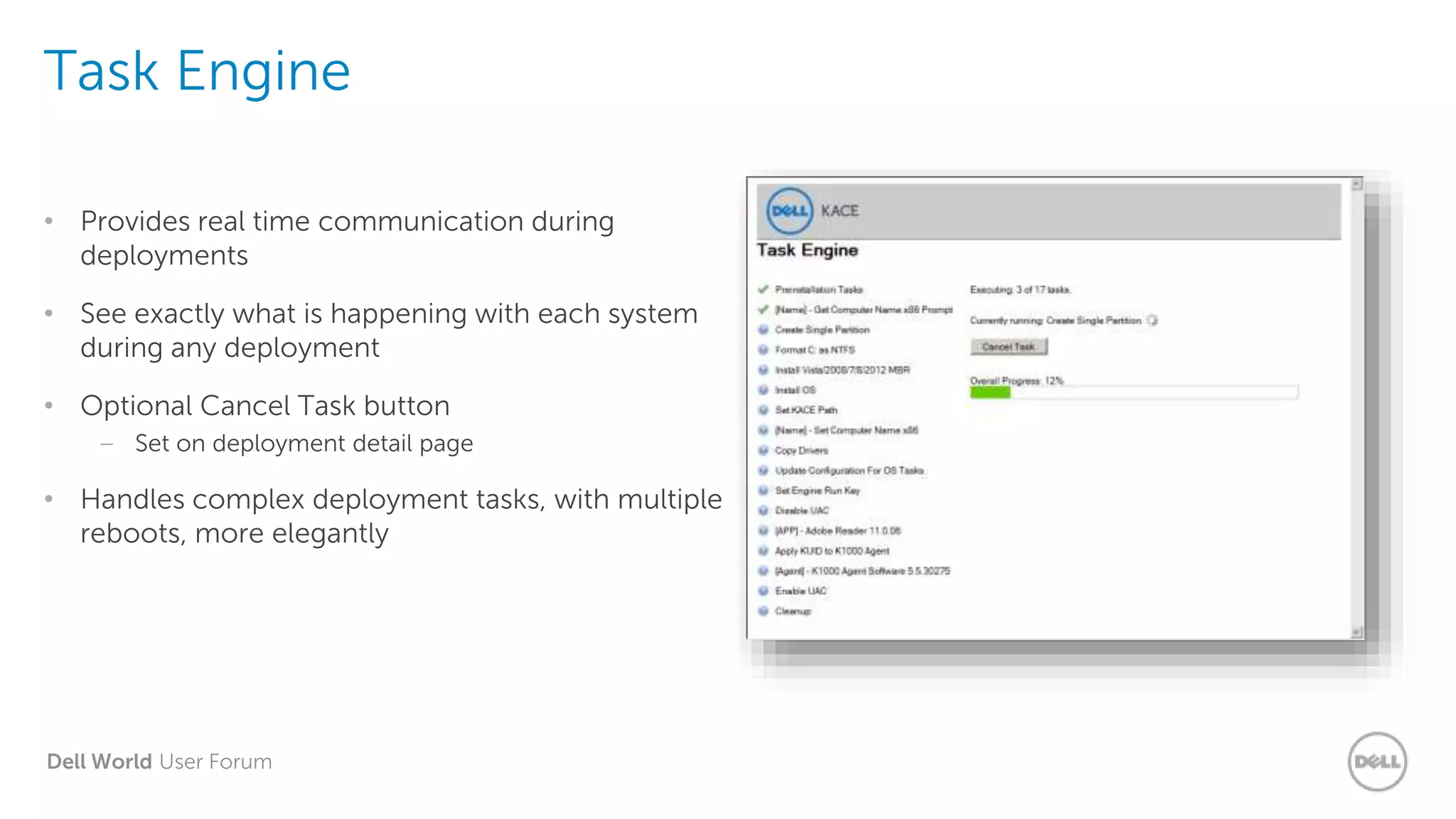
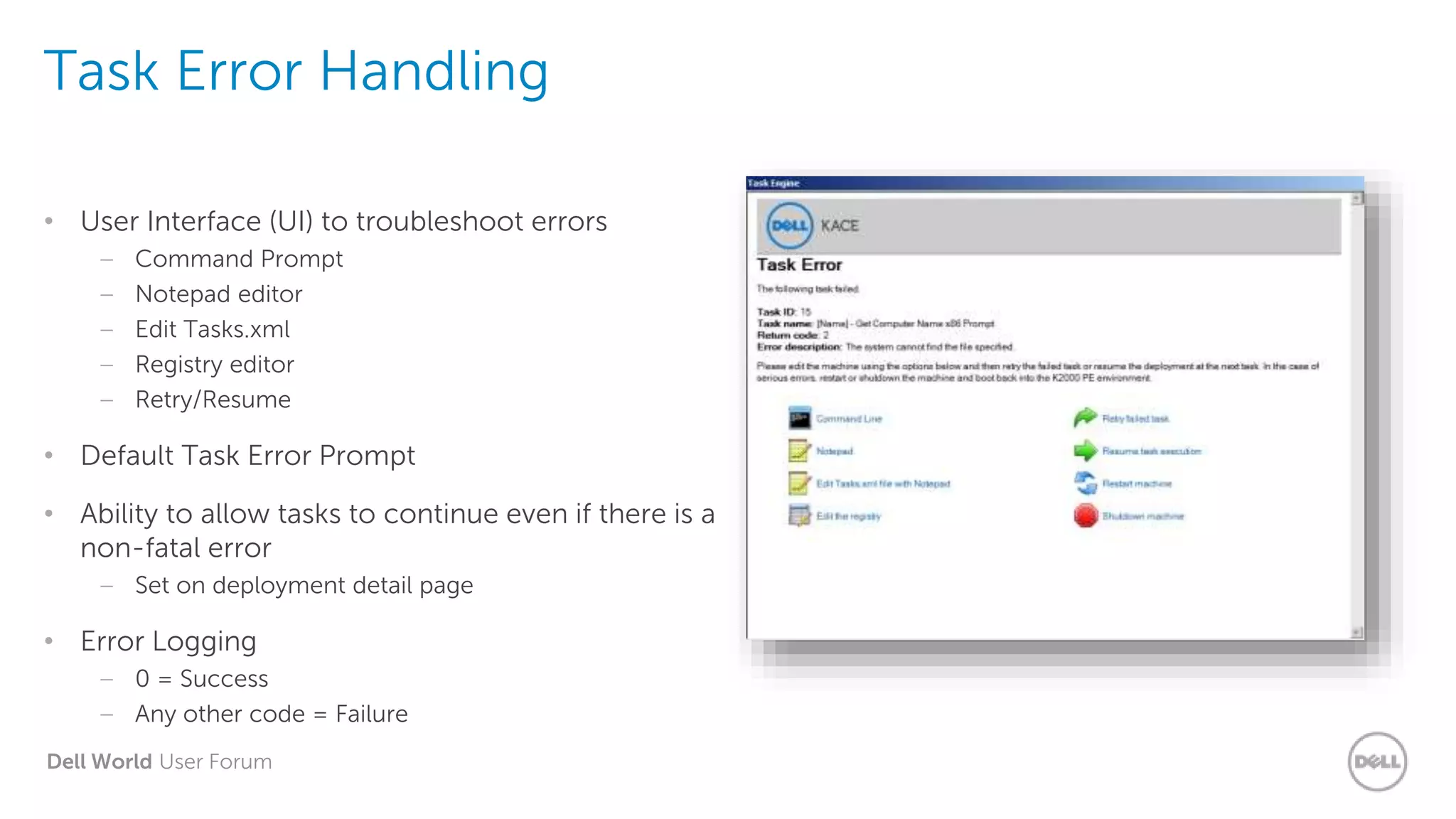
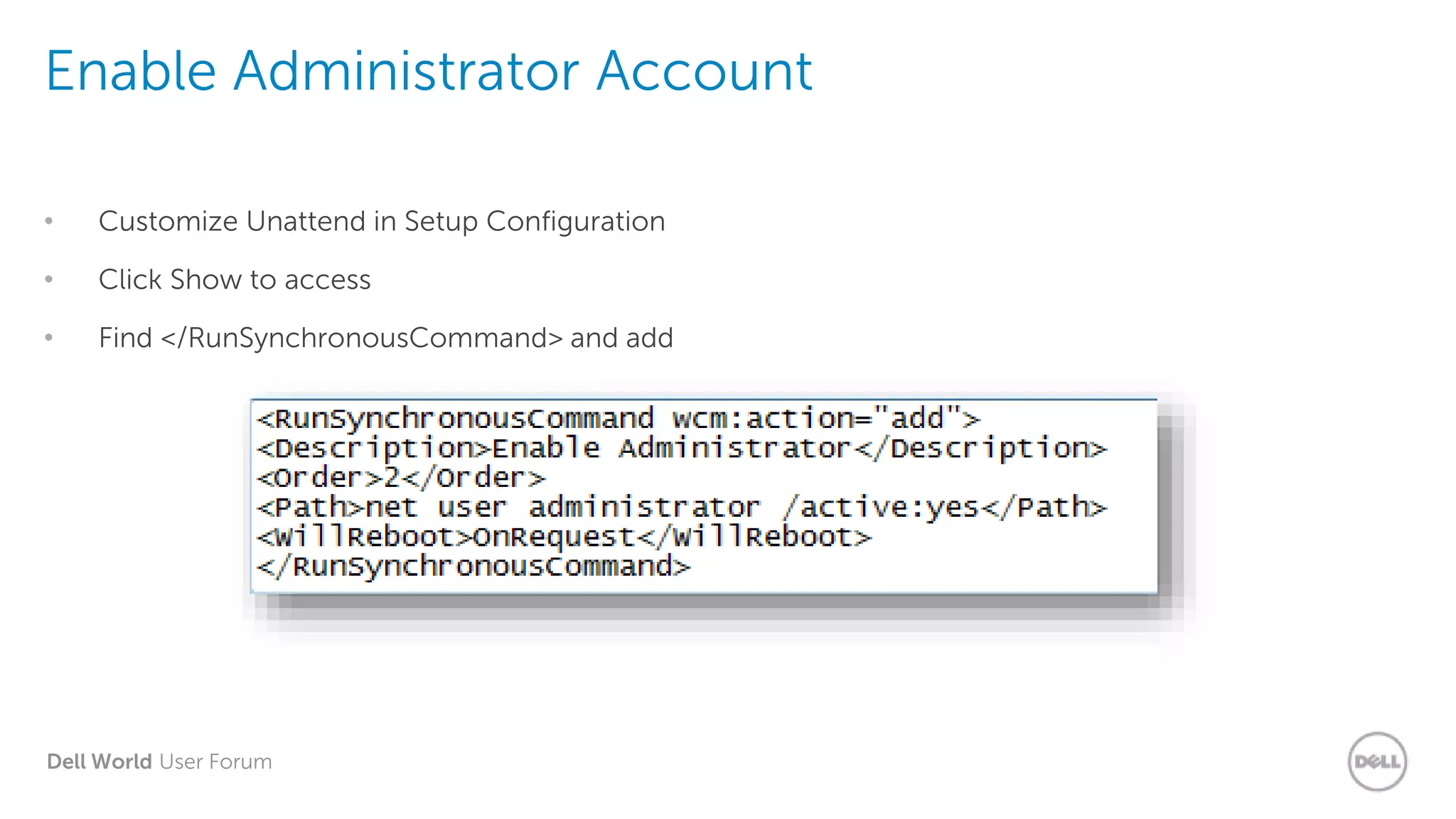
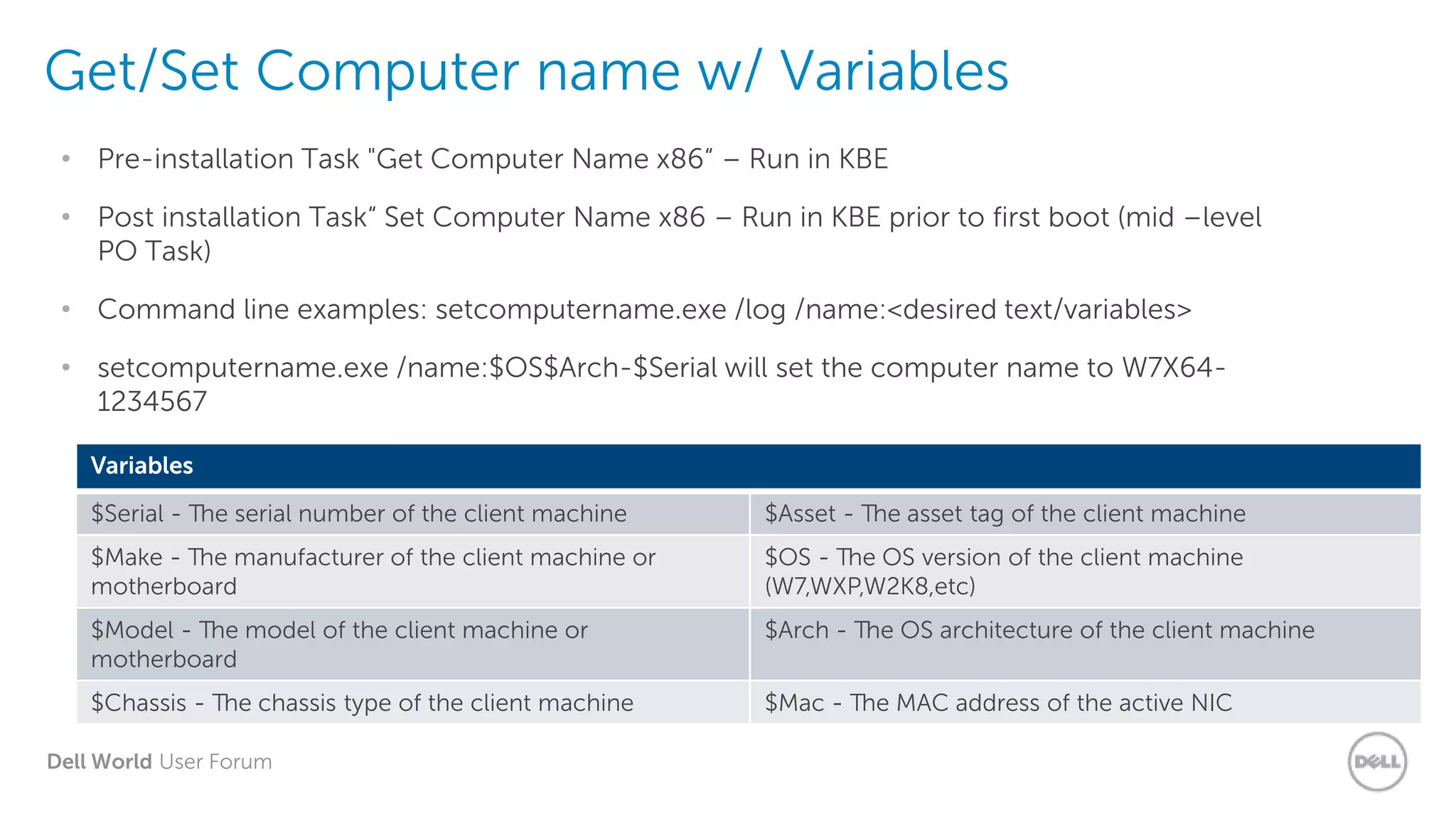
The document outlines the processes for creating and deploying scripted installations using Dell's KACE systems, covering important topics such as preparation, types of media, driver management, and error handling. It emphasizes the use of customized unattend files, updating processes for OS patches, and troubleshooting methods during installations. Additionally, it provides detailed instructions for naming conventions and configurations for deployments, enhancing automation and user state management.