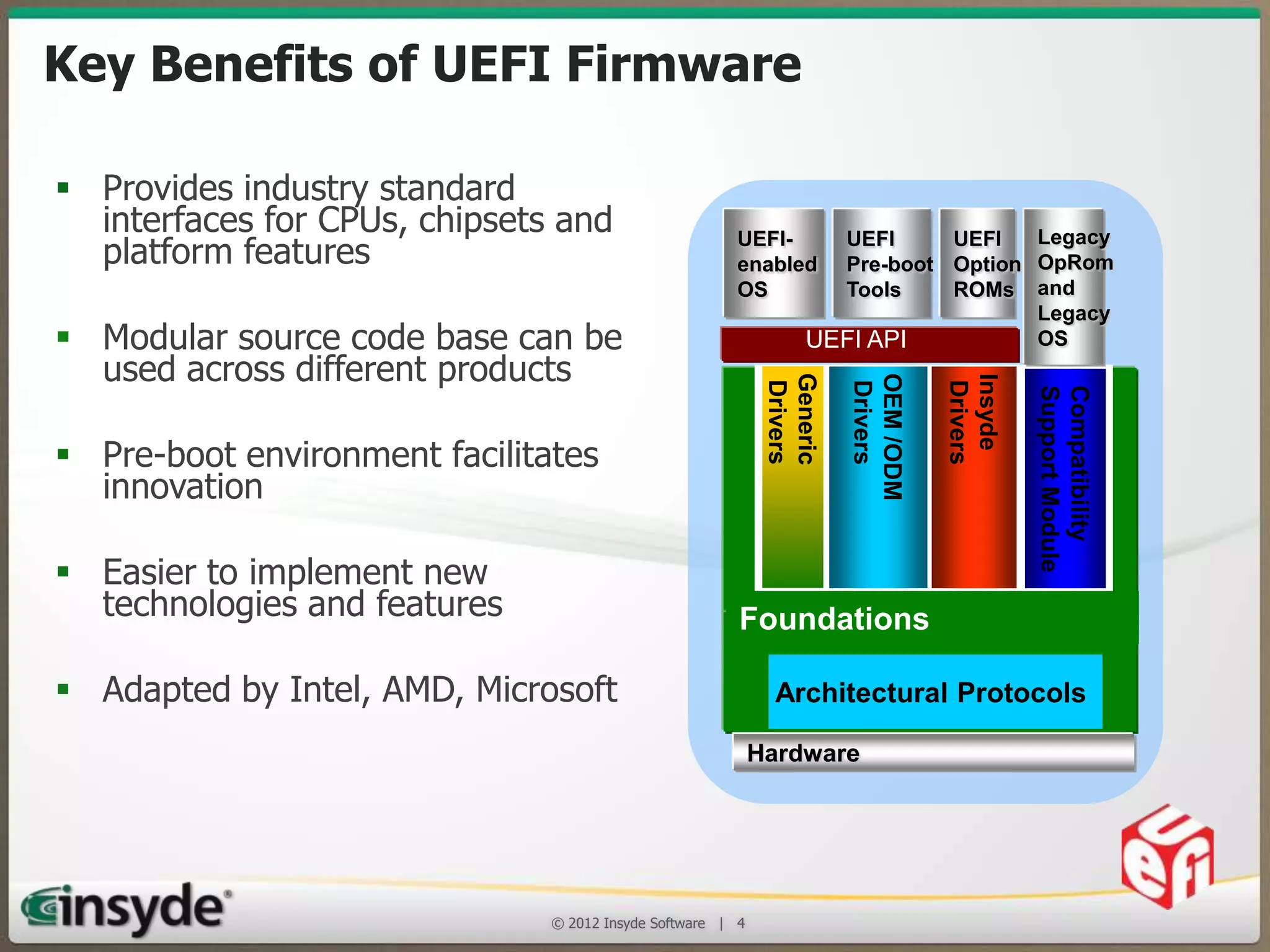
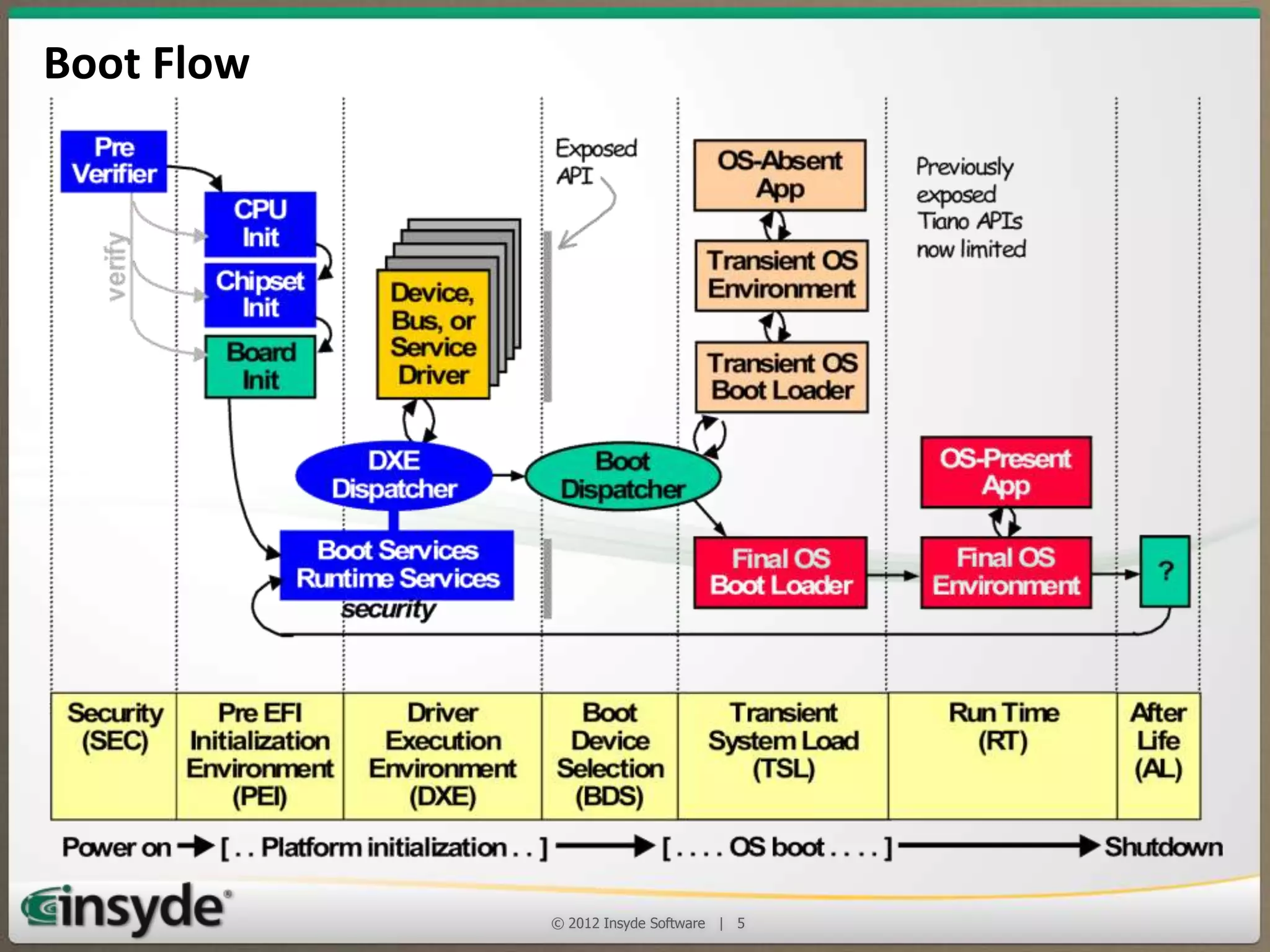
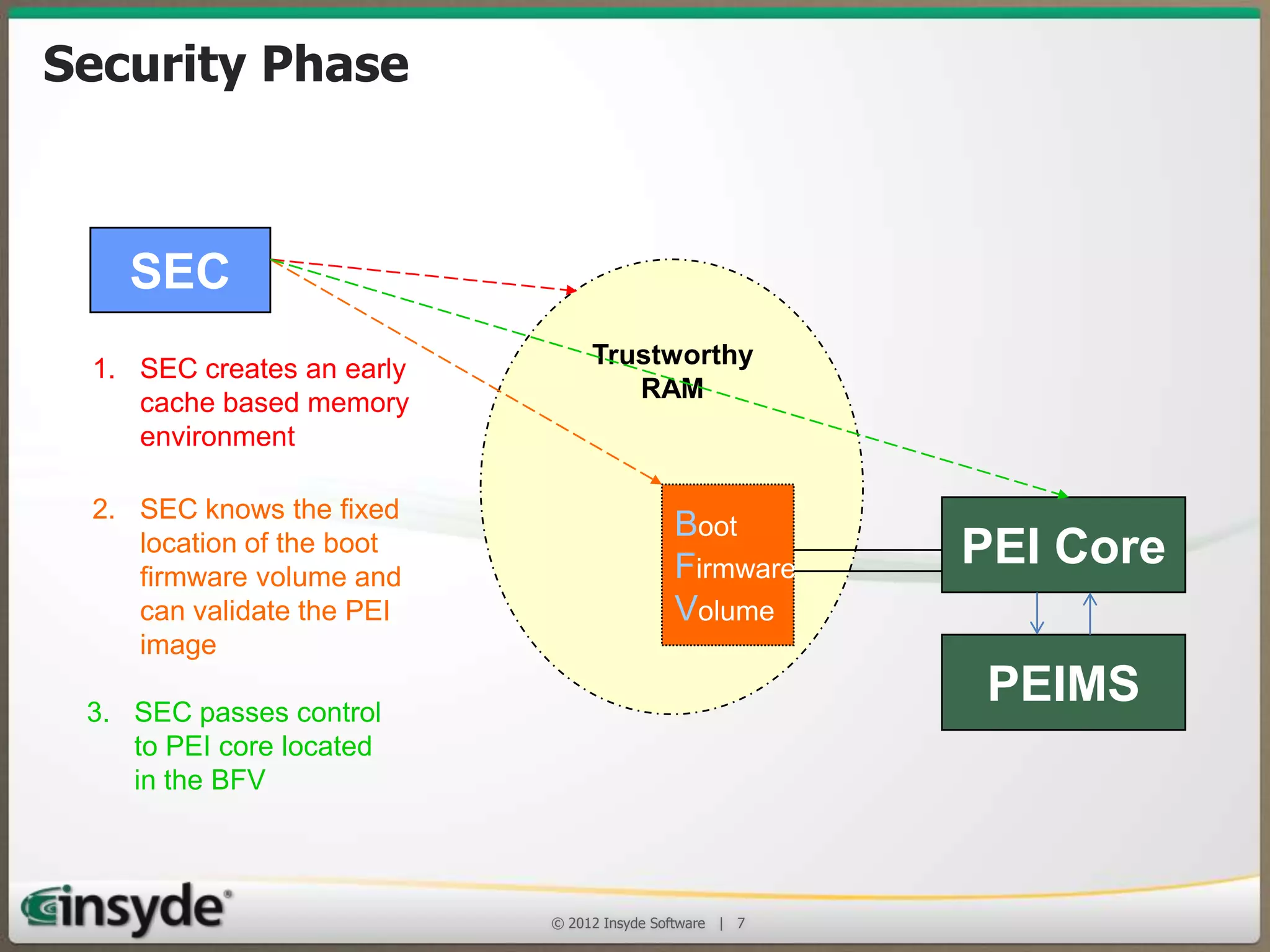
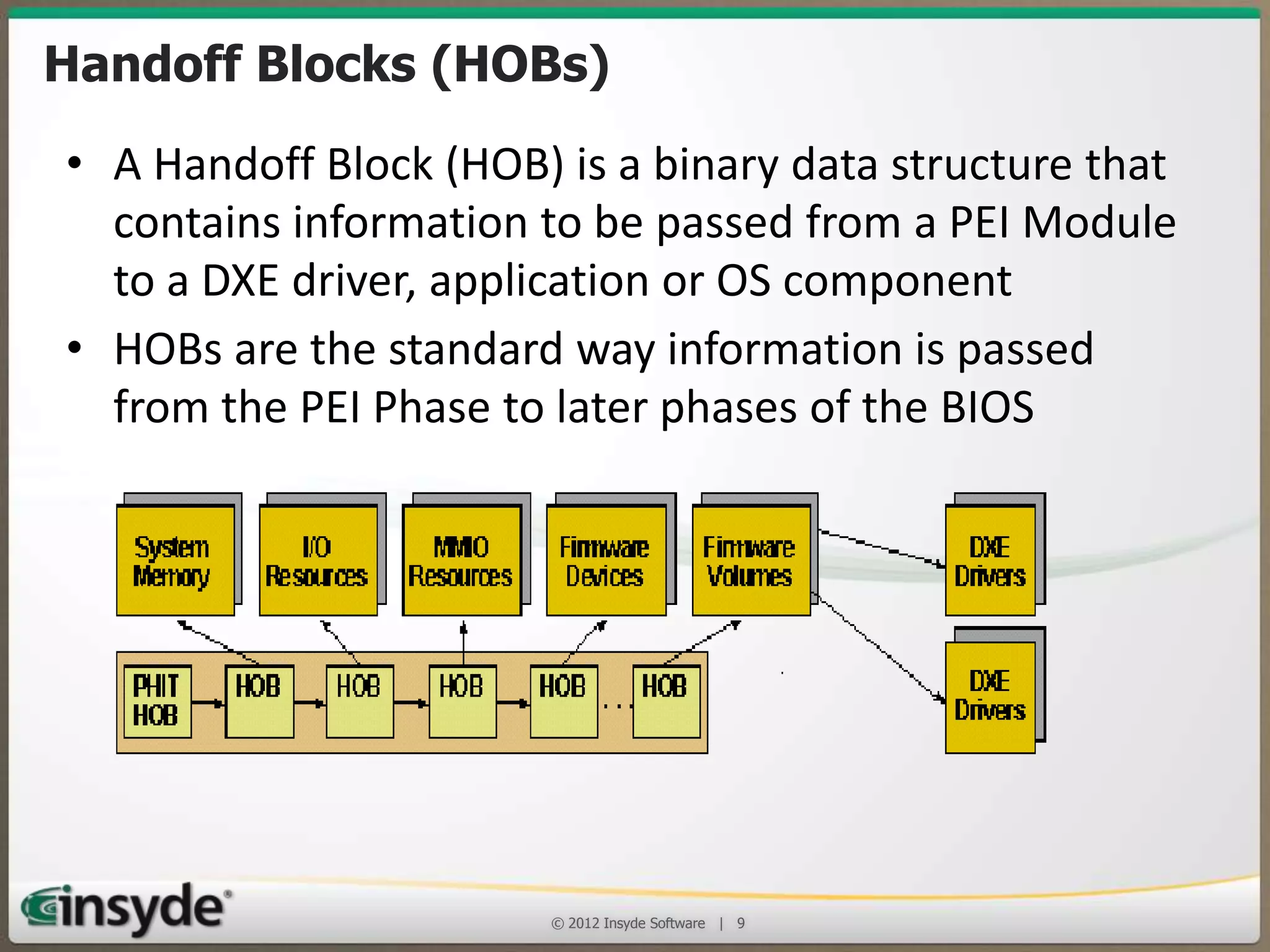
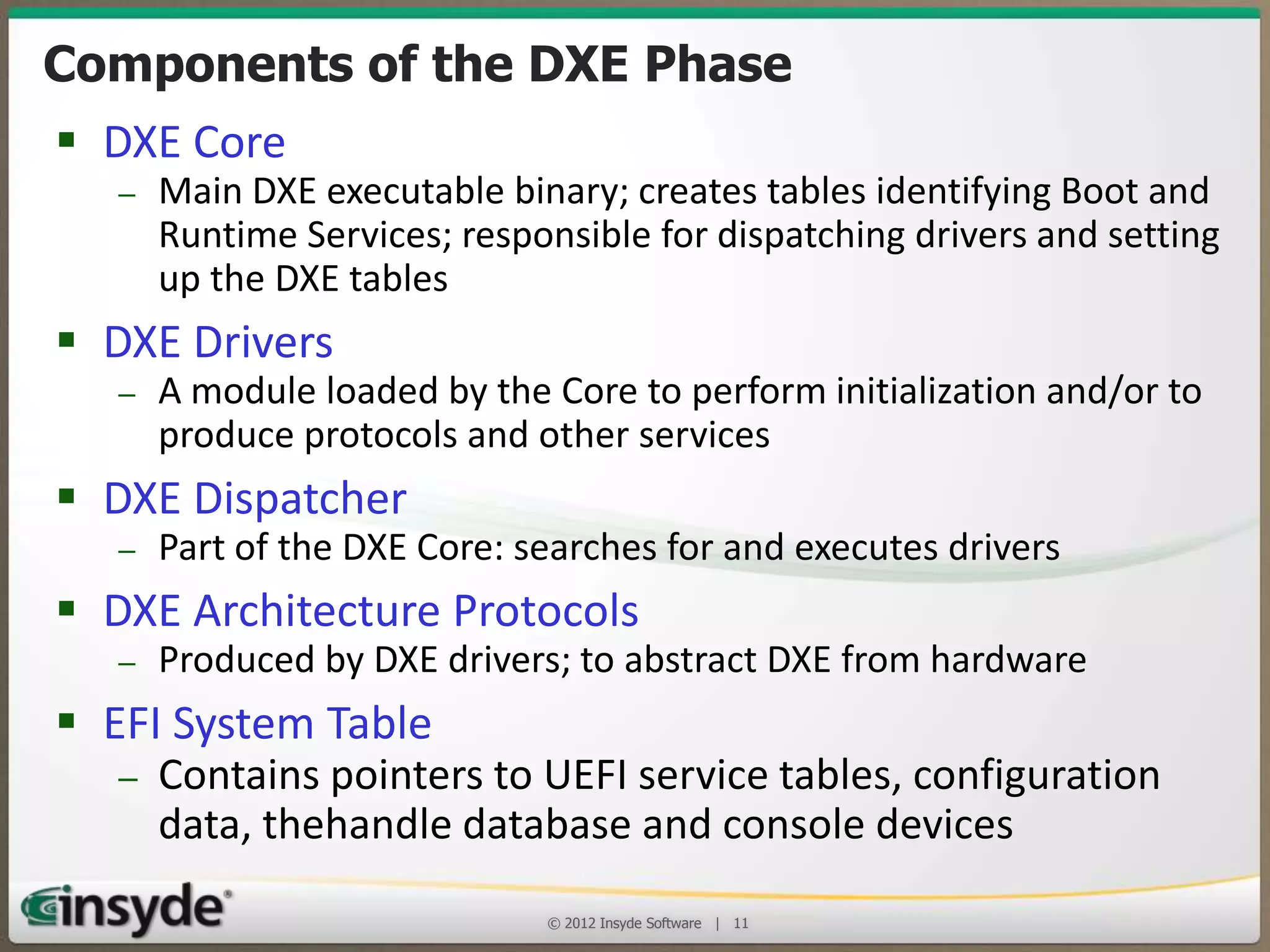
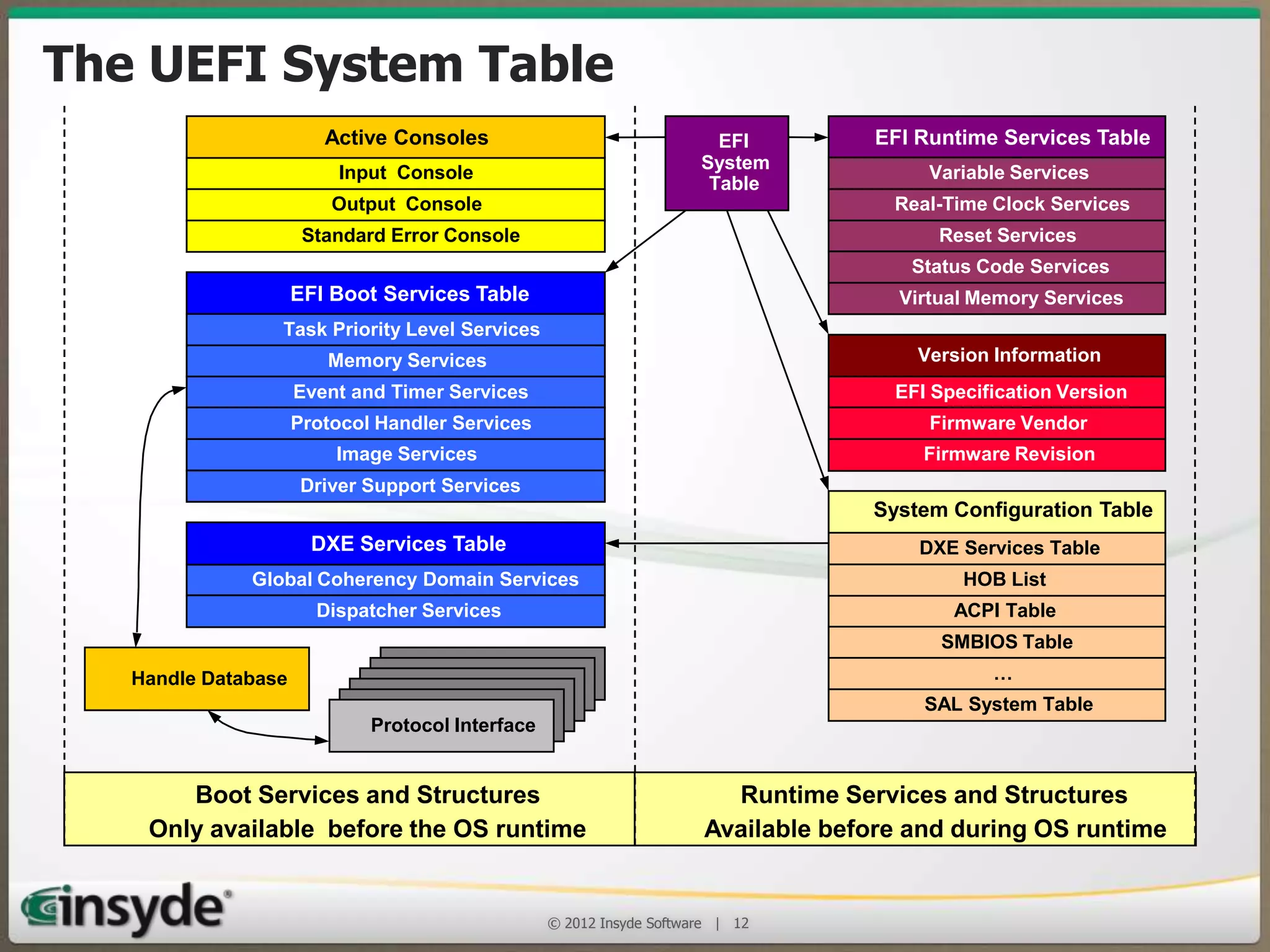
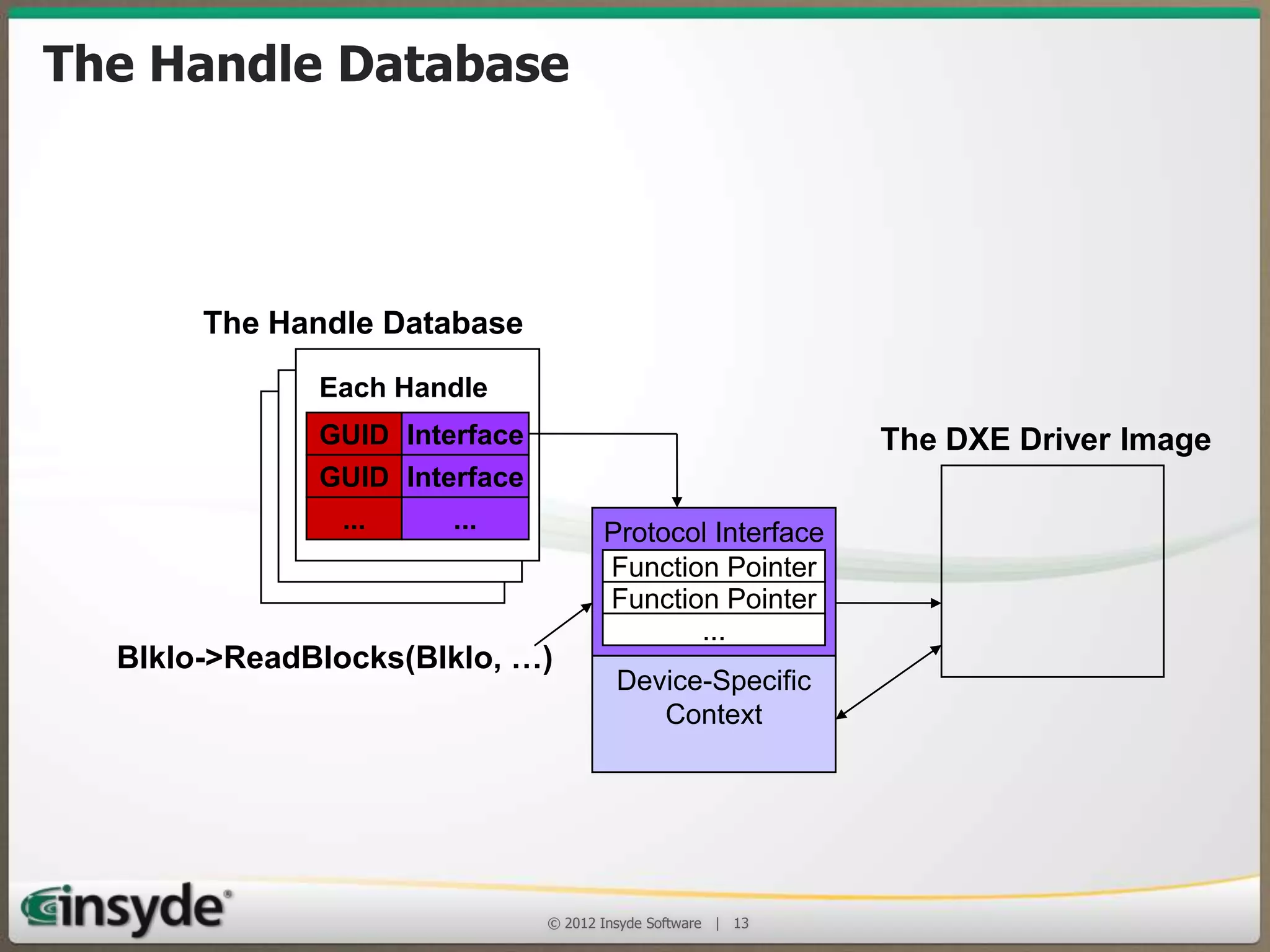
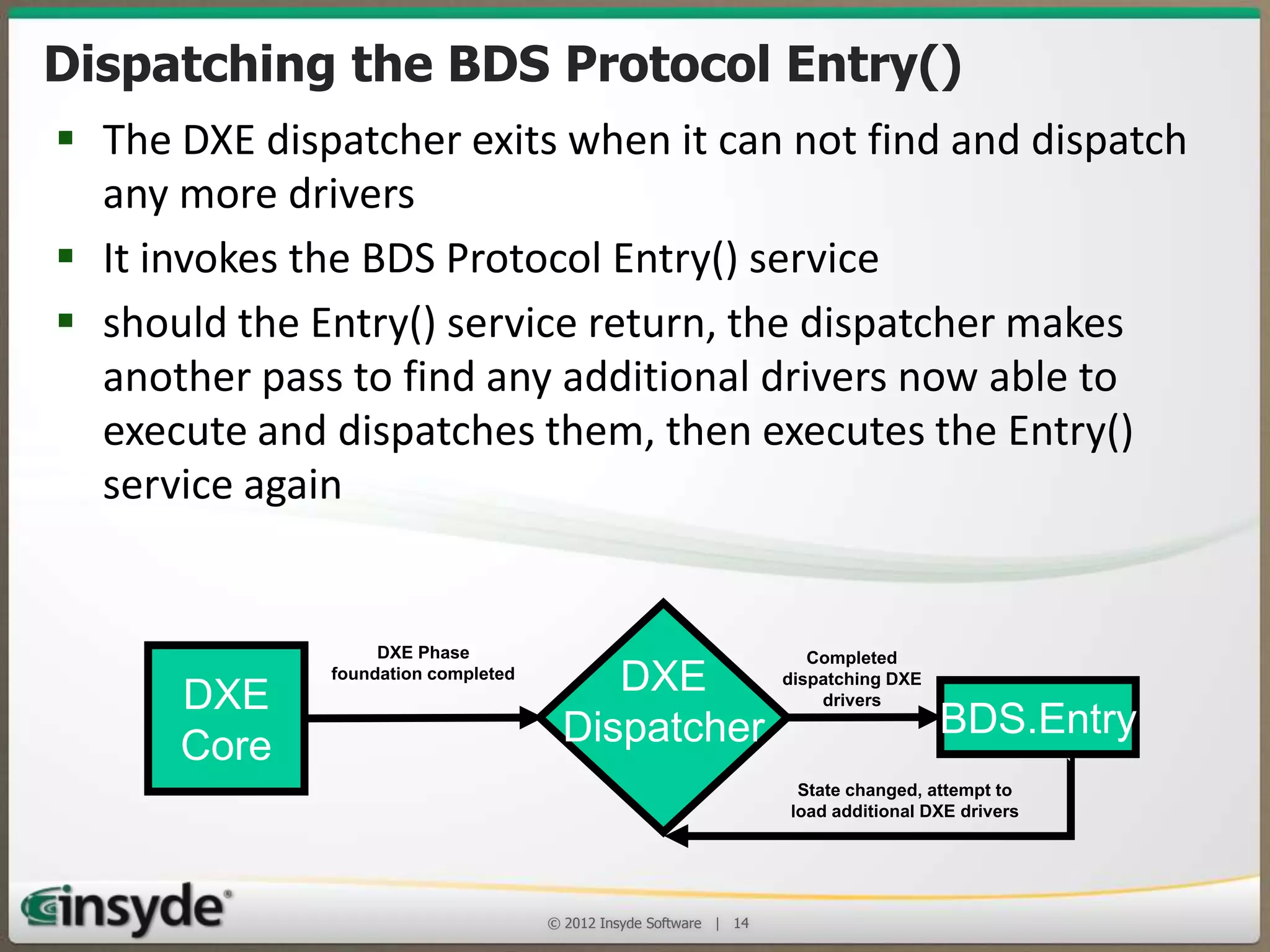
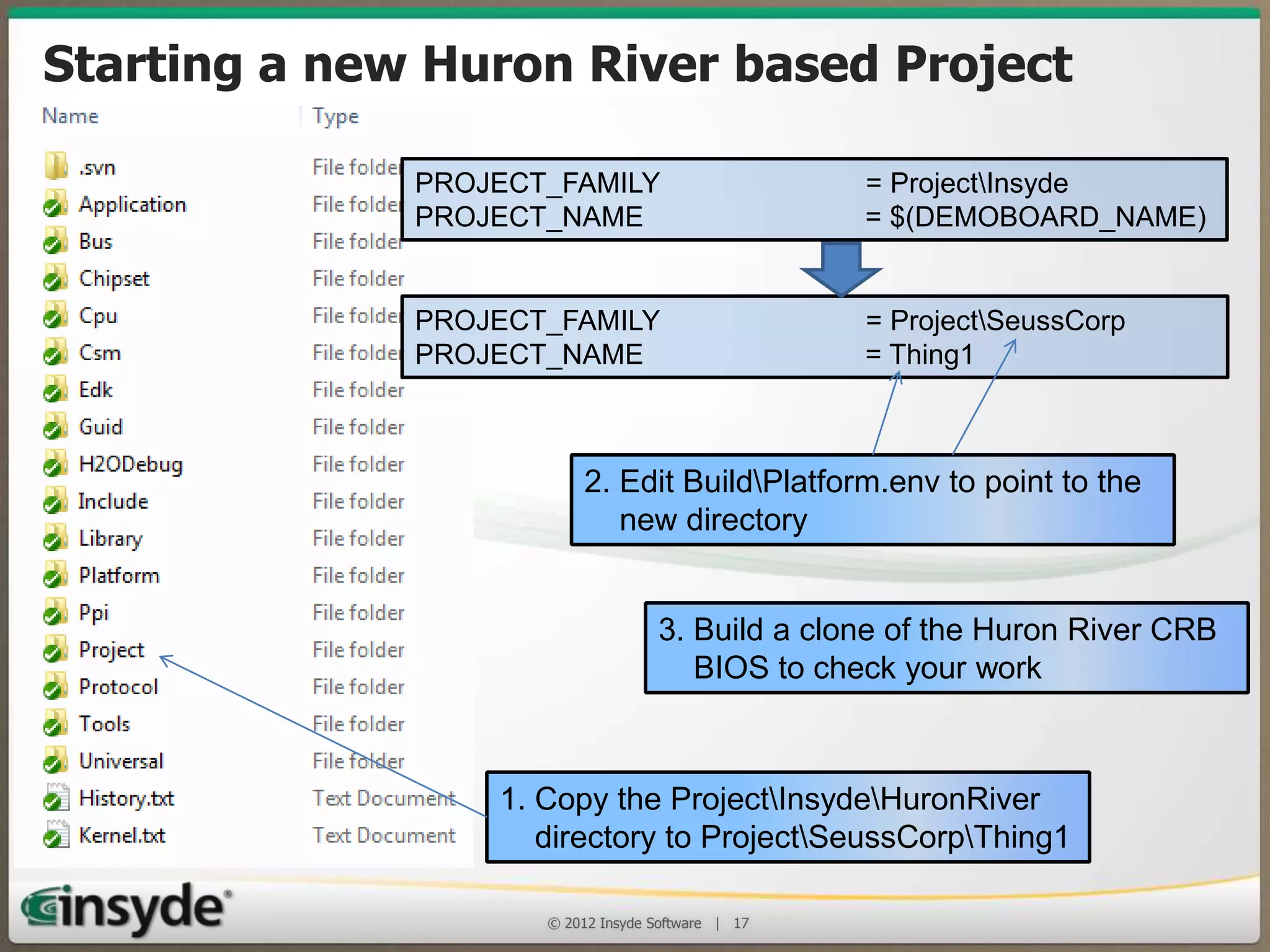
The document outlines Insyde Software's implementation of UEFI BIOS in embedded systems, emphasizing its compatibility with various platforms and benefits such as standard interfaces for hardware. It details the phases of UEFI, including Security Phase, Pre-EFI Initialization, and Driver Execution, along with the structure of handoff blocks and the EFI system table. Additionally, it highlights support options available for developers, including engineering support and training.