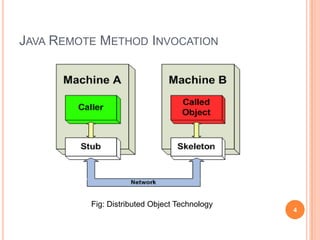
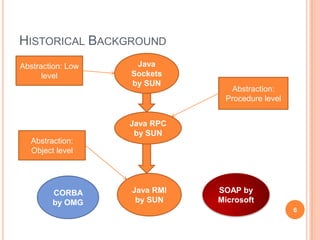
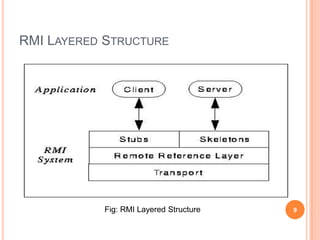
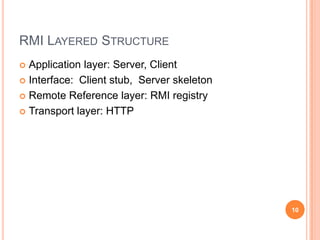
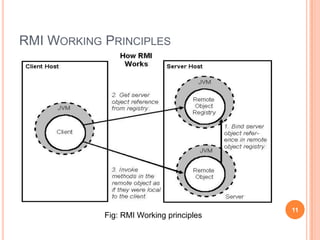
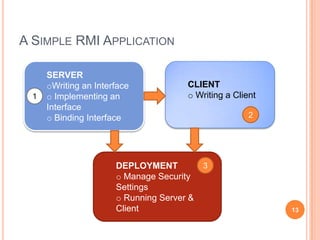
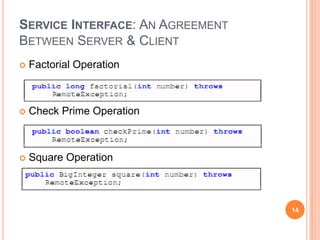
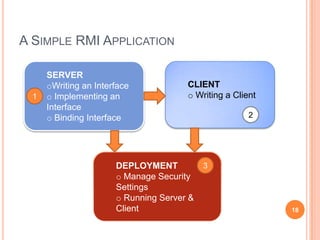
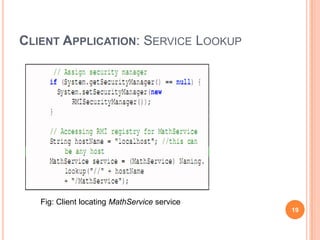
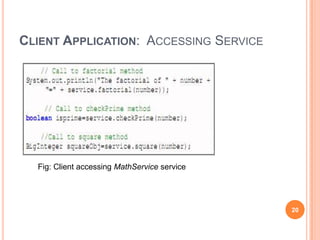
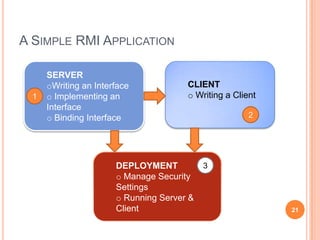
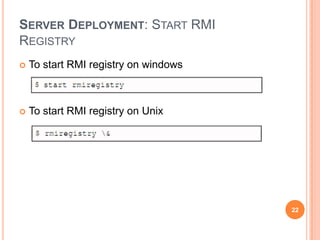
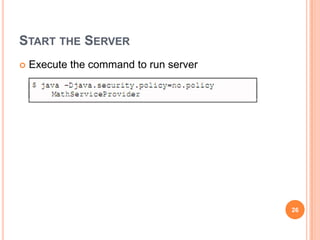
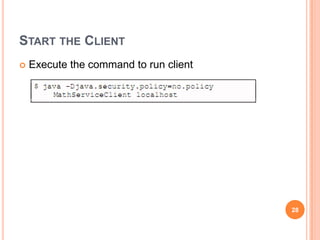
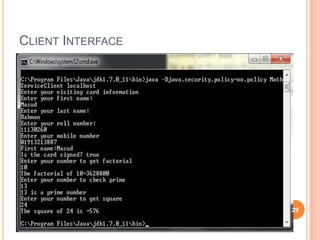
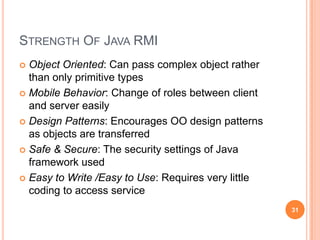
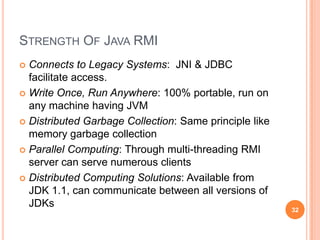
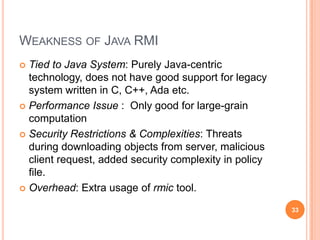
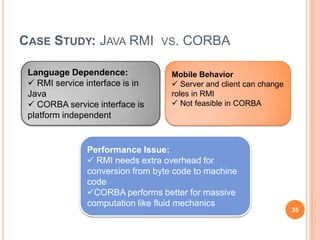
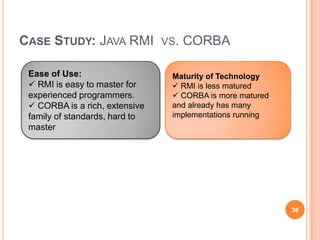
This document provides an overview of Java Remote Method Invocation (RMI). It discusses the historical background and related technologies like RPC and CORBA. The document describes the layered architecture of RMI including the application, interface, reference, and transport layers. It also explains the working principles of RMI with client/server communication and object serialization. An example RMI application is demonstrated involving writing interfaces and classes, deploying the server, and accessing services from the client. Strengths and weaknesses of RMI are analyzed in comparison to CORBA. The document is intended as a tutorial on building distributed applications with Java RMI.


![REFERENCES
[1].Advantages of java RMI
http://www.oracle.com/technetwork/java/javase/tech/index-jsp-138781.html
[2] Java RMI architecture. http://www.cs.mun.ca/michael/java/jdk1.1-beta2docs/guide/rmi/rmi-arch.doc.html
[3] Introduction to java RMI
http://www.javacoffeebreak.com/articles/javarmi/javarmi.html.
[4] Java RMI: Remote method invocation.
http://www1.cs.columbia.edu/dcc/nestor/presentations/java-rmi/java-rmihandouts.pdf
[5] Disadvantages of RMI. http://www.coderanch.com/t/180297/javadeveloperSCJD/certification/RMI-Advantages-Disadvantages.
[6] Background of java rmi.
http://docs.oracle.com/javase/1.5.0/docs/guide/rmi/spec/rmi-intro2.html.
[7] How RMI works.
http://www.sce.carleton.ca/netmanage/simulator/rmi/RMIExplanation.htm
Please contact mor543@mail.usask.ca to get more.
42](https://image.slidesharecdn.com/final-javaremotemethodinvocation-140103204654-phpapp01/85/Java-RMI-Presentation-42-320.jpg)