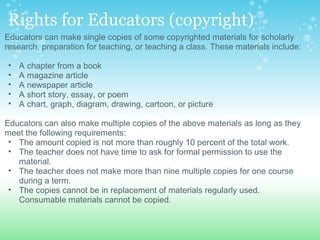
The document discusses several topics related to computer issues including computer fraud, copyright, individual privacy, computer viruses and hackers, and dangers of new technology. It provides information on each topic, such as defining computer fraud and ways to prevent it, outlining copyright law and what is protected, discussing concerns about individual privacy and what cookies are, explaining computer viruses and hackers and how to prevent being affected by them, and noting some potential health, social, and educational dangers of new technology.