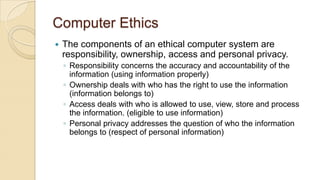
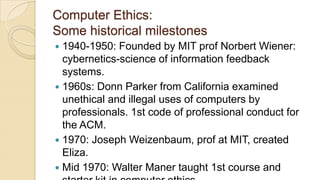
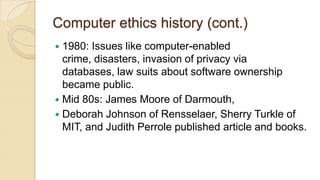
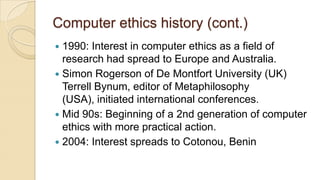
This document discusses professional practices and computer ethics. It begins with background on ethics according to Socrates, defining ethics as knowing the difference between right and wrong. It then defines computer ethics and its components: responsibility, ownership, access, and personal privacy. The document then discusses the impact of cybercrime such as fraud, sabotage, and hacking. It provides examples of computer ethics cases and concludes with discussing the 10 commandments of computer ethics.