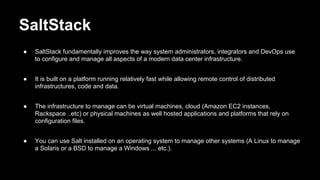
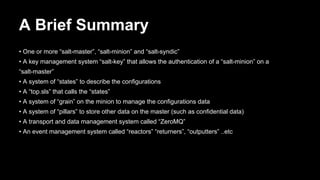
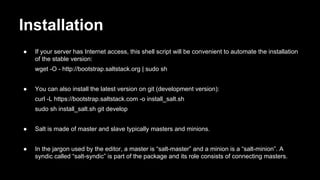
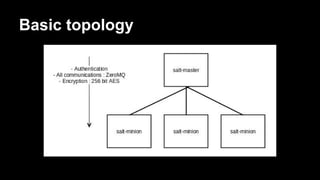
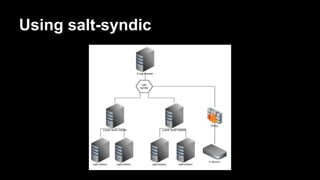
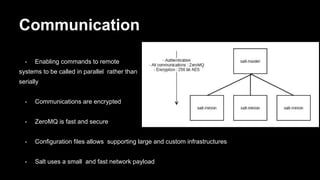
The document introduces SaltStack, emphasizing its importance in configuration management and automation for modern data center infrastructures. It outlines the roles of salt-master, salt-minion, and salt-syndic, as well as key concepts such as grains, pillars, and remote execution. The author, Aymen El Amri, shares insights from his experience as a Linux/web engineer and DevOps advocate, promoting his book 'SaltStack for DevOps' and personal blog.