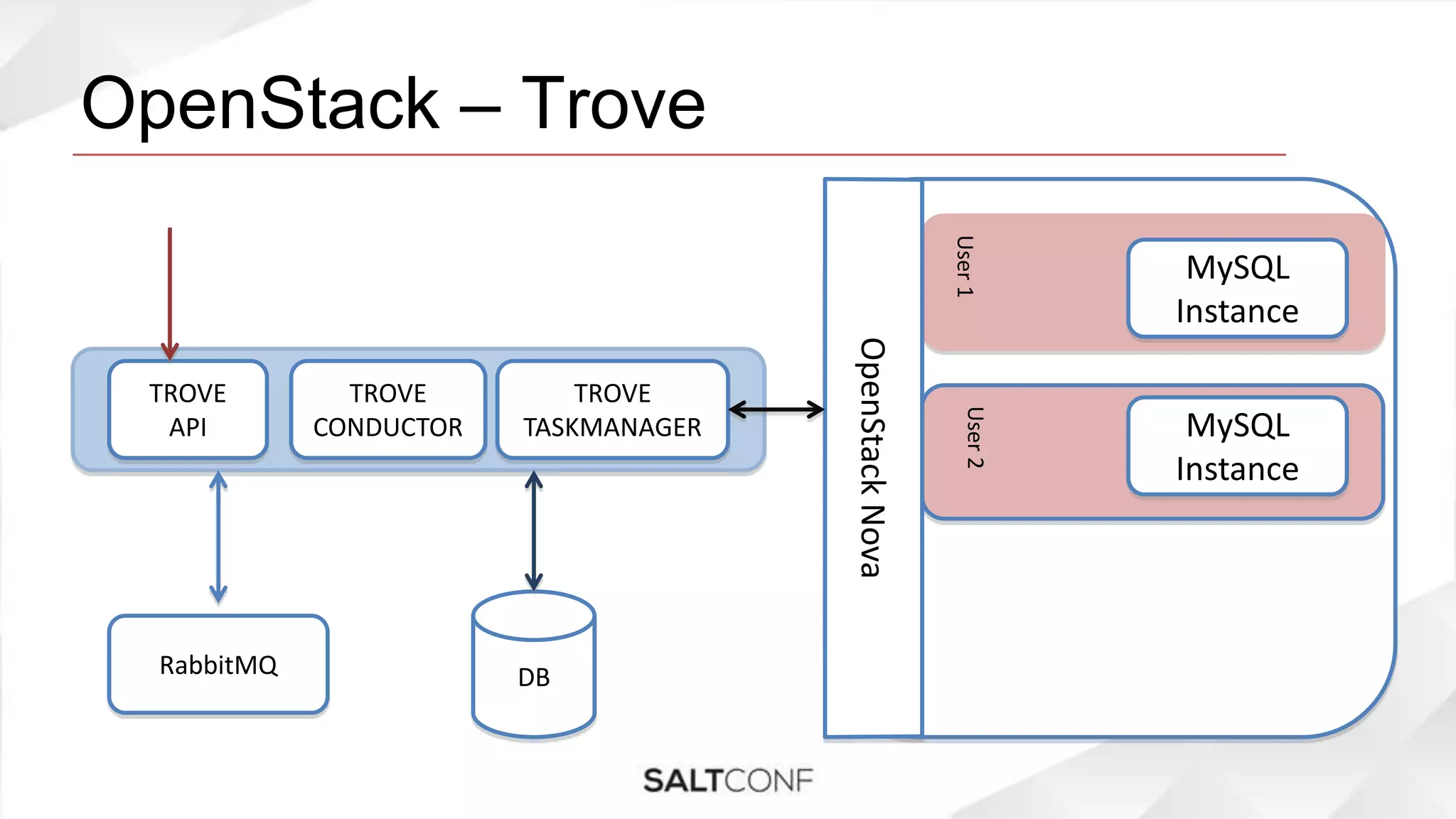
This document discusses automating operations and support using SaltStack in the context of OpenStack Trove, a Database as a Service project. It covers various aspects such as managing Salt environments, the importance of access control, and strategies for separating states to mitigate user errors. Additionally, it highlights challenges and best practices for securing sensitive data and auditing user actions.


![Writing states to catch user errors
• Writing state with necessary checks to help catch user
errors
• E.g while writing states for salt-master, make sure that its
getting executed on the master only. May be add a check
on grains[id]](https://image.slidesharecdn.com/saurabhsurana-automatingoperationsandsupportwithsaltstack-saltconf-140326172146-phpapp02/75/SaltConf14-Saurabh-Surana-HP-Cloud-Automating-operations-and-support-with-SaltStack-21-2048.jpg)