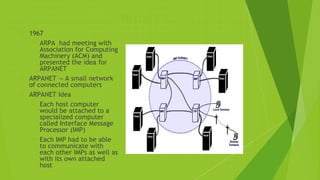
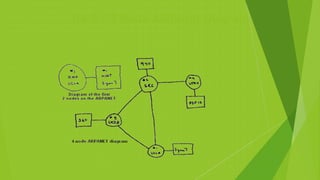
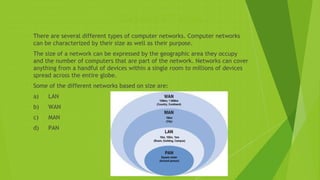
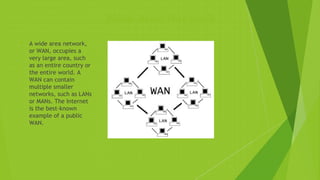
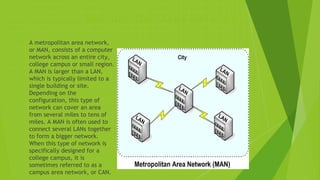
Networks connect computers and devices to allow sharing of resources and information. The first computer network, ARPANET, was developed in the 1960s to enable researchers to share information. Today's networks fulfill business needs for quick access to secure data and decision making. There are several types of networks classified by size, including personal area networks (PANs), local area networks (LANs), metropolitan area networks (MANs), wide area networks (WANs), and the largest network, the Internet, which connects millions worldwide.