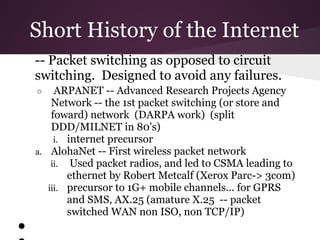
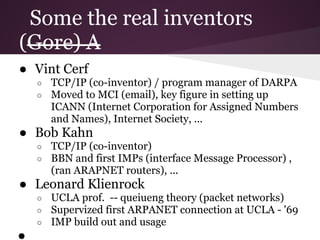
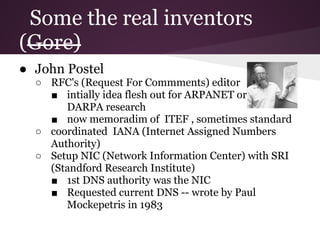
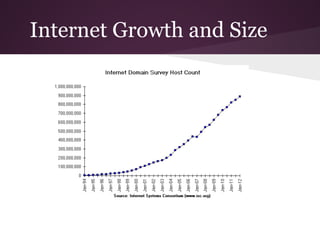
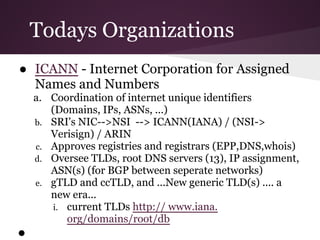
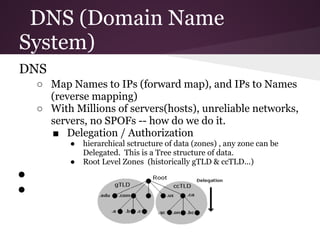
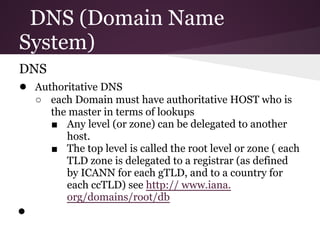
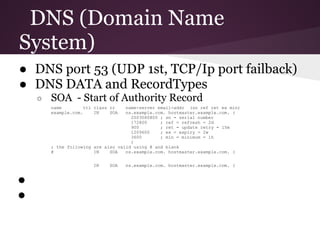
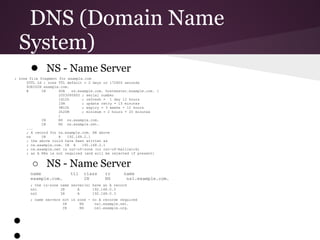
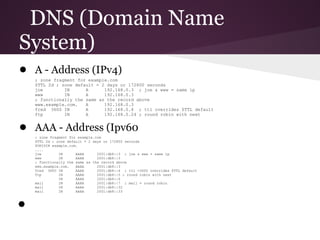
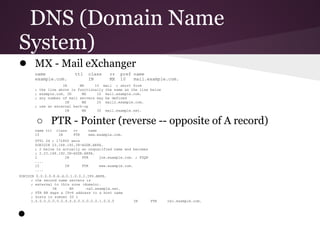
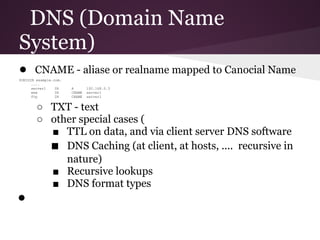
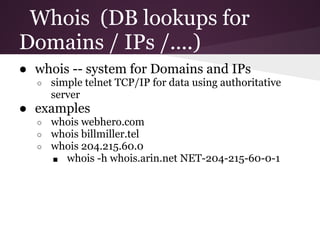
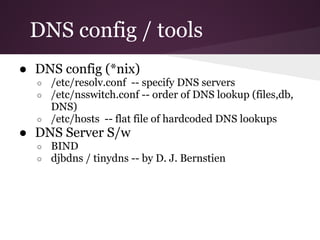
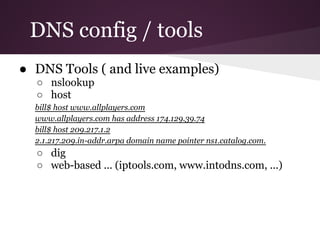
The document provides a brief history of the Internet and an overview of the Domain Name System (DNS). It discusses the development of early packet networks like ARPANET and the invention of TCP/IP. It also describes the roles of organizations like ICANN and ARIN in managing domain names, IP addresses, and other Internet resources. Finally, it explains the basic functioning of DNS through record types like A, MX, NS, and PTR that map domain names to IP addresses and vice versa.