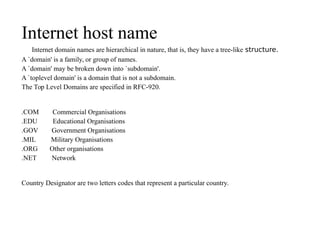
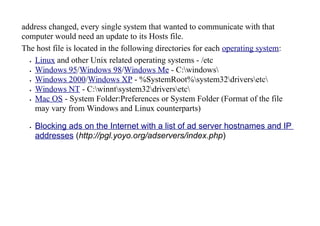
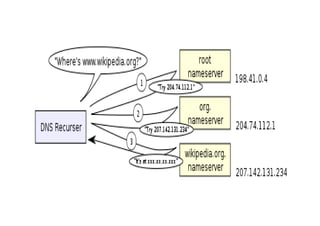
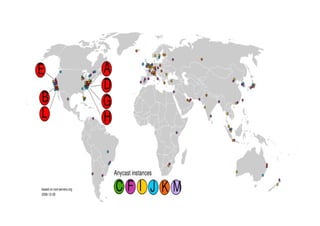
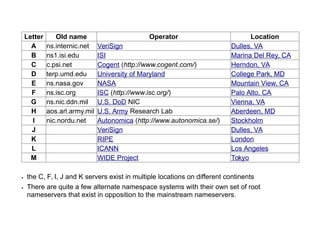
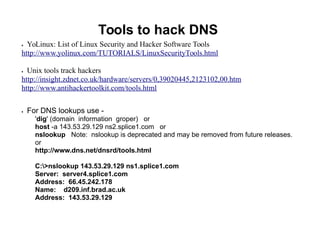
The document discusses Internet domain names and the Domain Name System (DNS). It explains that domain names have a hierarchical tree structure with top-level domains like .com and country-specific domains like .uk. DNS servers convert domain names to IP addresses, allowing communication between devices on the Internet. The DNS hierarchy is managed by organizations like ICANN and domain name registries to coordinate a globally unique addressing system.
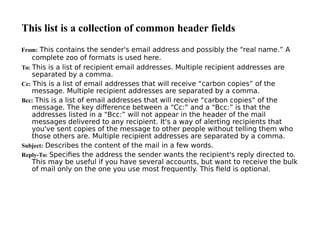
![A typical mail header may look like this:
Return-Path: <ph10@cus.cam.ac.uk>
Received: ursa.cus.cam.ac.uk (cusexim@ursa.cus.cam.ac.uk [131.111.8.6]) by
al.animats.net (8.9.3/8.9.3/Debian 8.9.3-6) with ESMTP id WAA04654 for
<terry@animats.net>; Sun, 30 Jan 2000 22:30:01 +1100
Received: from ph10 (helo=localhost) by ursa.cus.cam.ac.uk with local-smtp
(Exim 3.13 #1) id 12EsYC-0001eF-00; Sun, 30 Jan 2000 11:29:52 +0000
Date: Sun, 30 Jan 2000 11:29:52 +0000 (GMT)
From: Philip Hazel <ph10@cus.cam.ac.uk>
Reply-To: Philip Hazel <ph10@cus.cam.ac.uk>
To: Terry Dawson <terry@animats.net>, Andy Oram <andyo@oreilly.com>
Subject: Electronic mail chapter
In-Reply-To: <38921283.A58948F2@animats.net>
Message-ID: <Pine.SOL.3.96.1000130111515.5800A-
200000@ursa.cus.cam.ac.uk>](https://image.slidesharecdn.com/hu0iaqw2slmd04iy4o89-signature-cd8ecd5b5dfde0a3b303daa66c44856412c9d6cb2cd34514d68cefadeef76e9a-poli-150905074055-lva1-app6892/85/Internet-Domains-21-320.jpg)