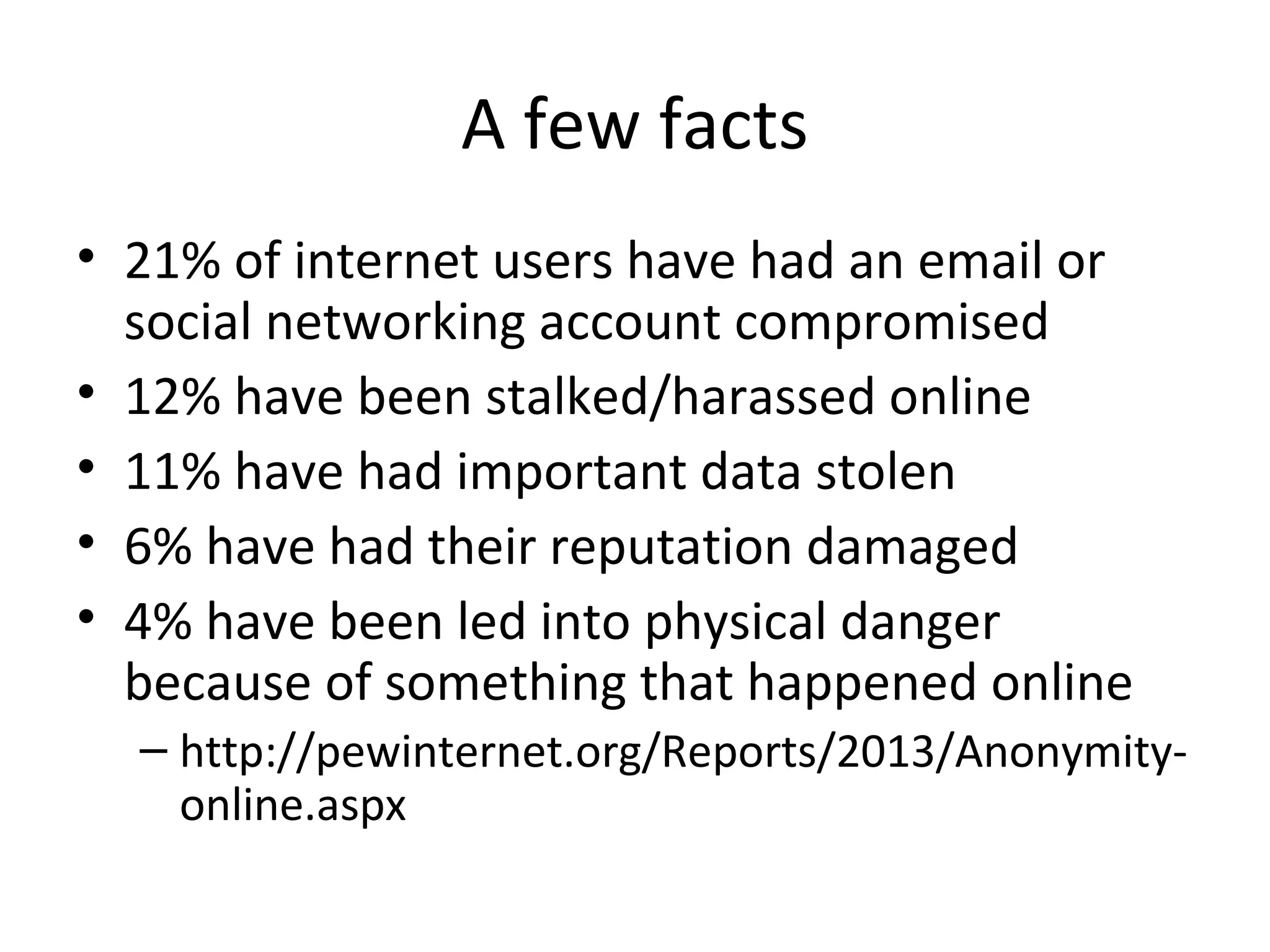
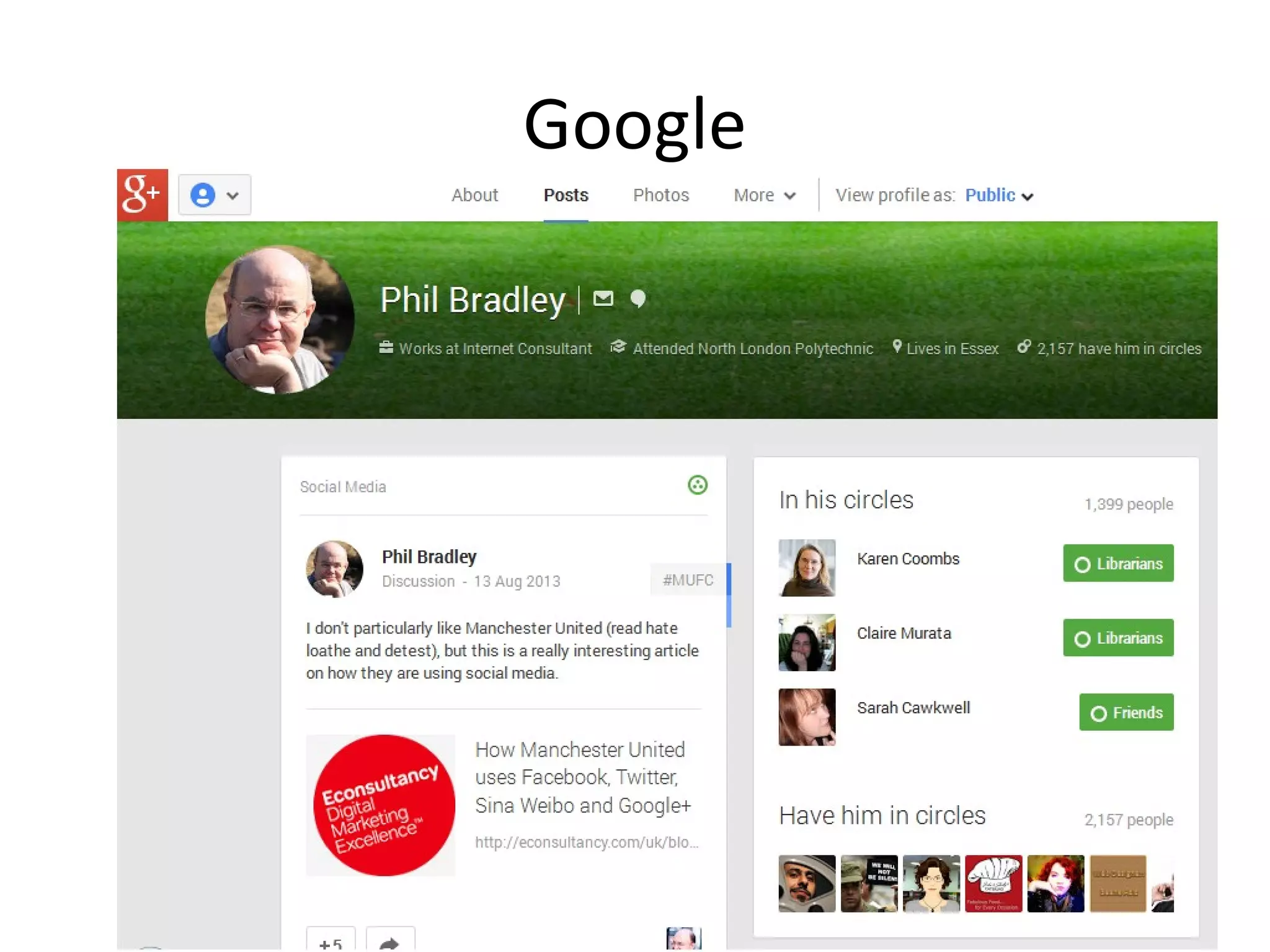
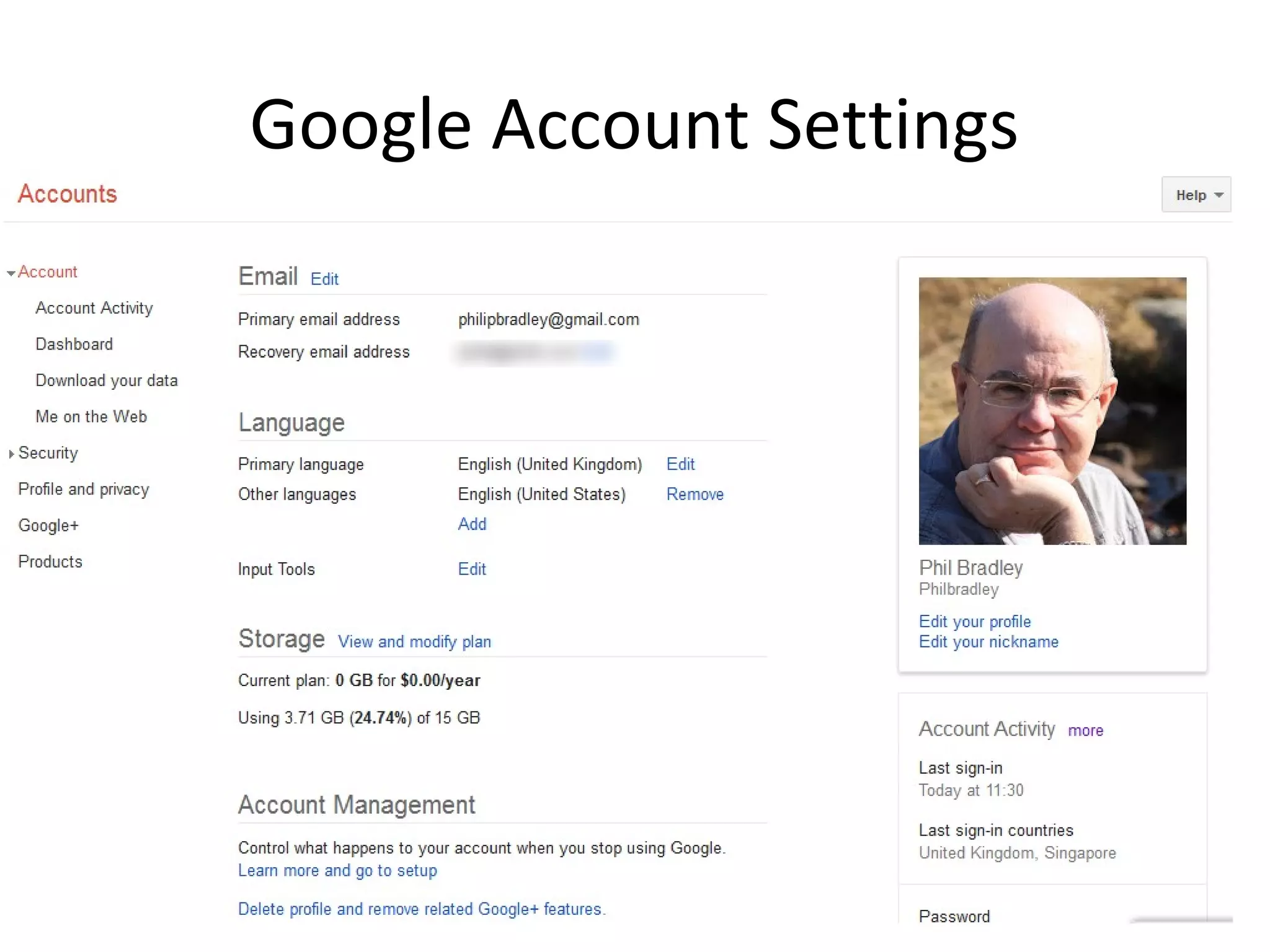
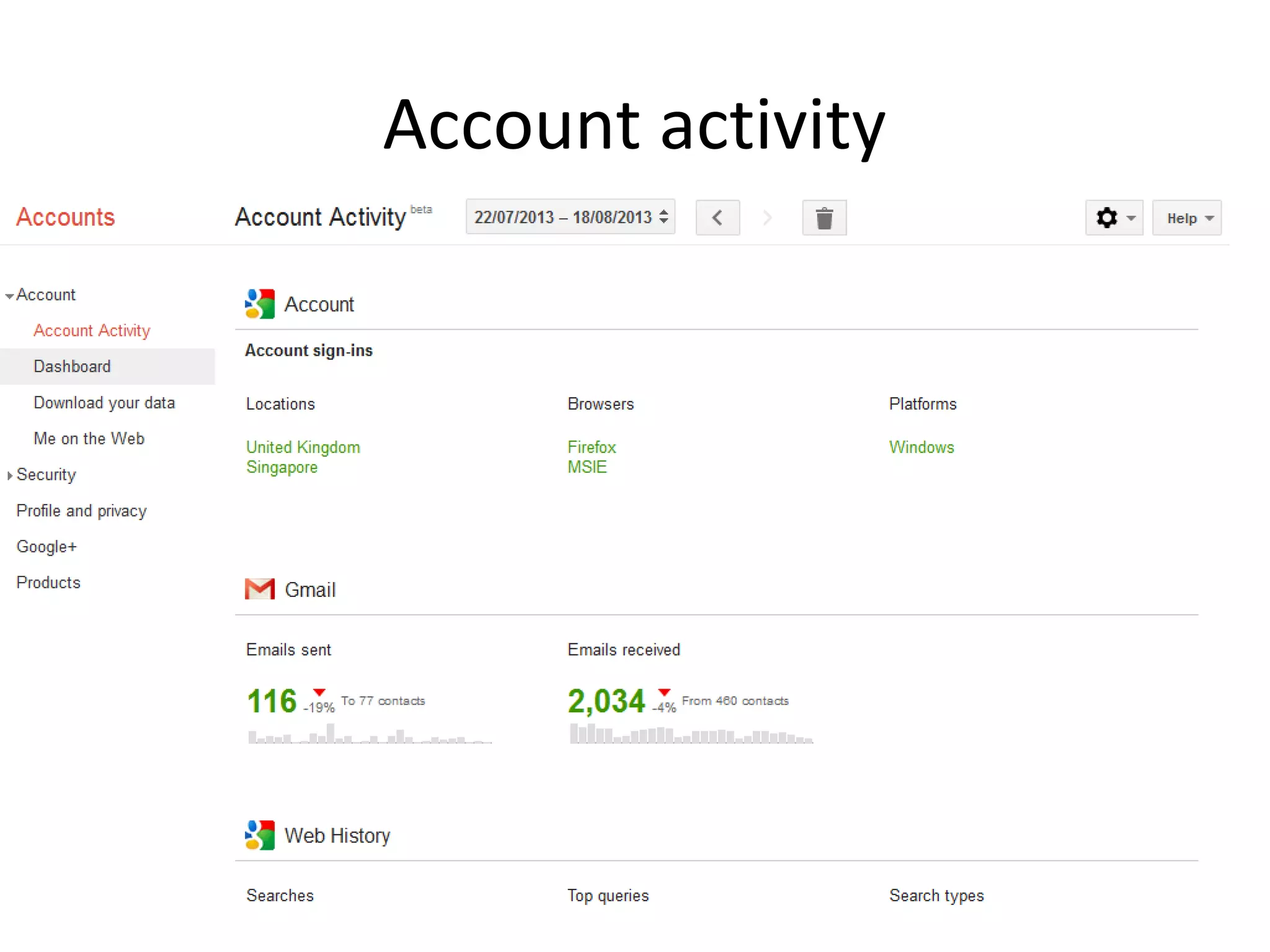
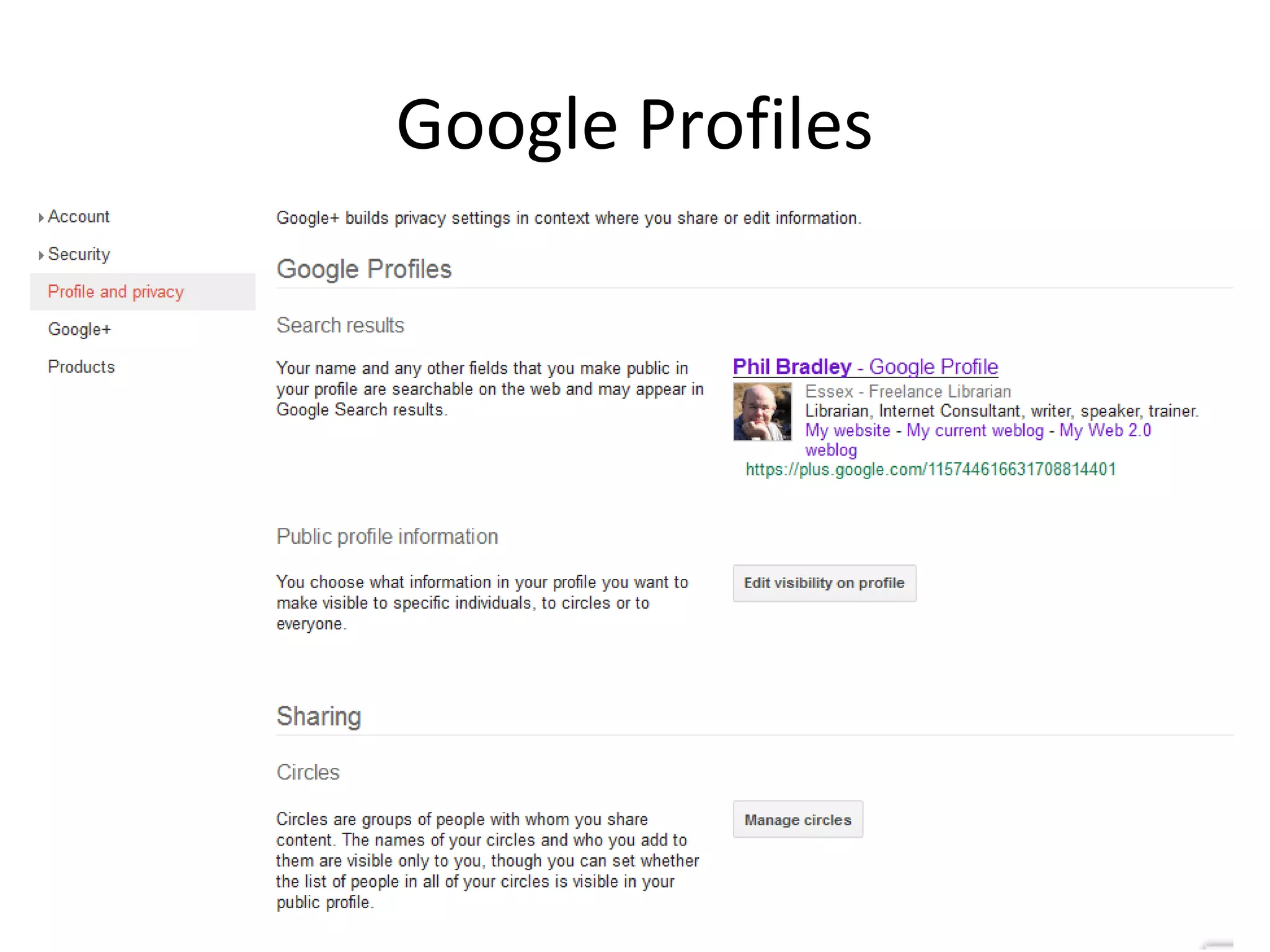
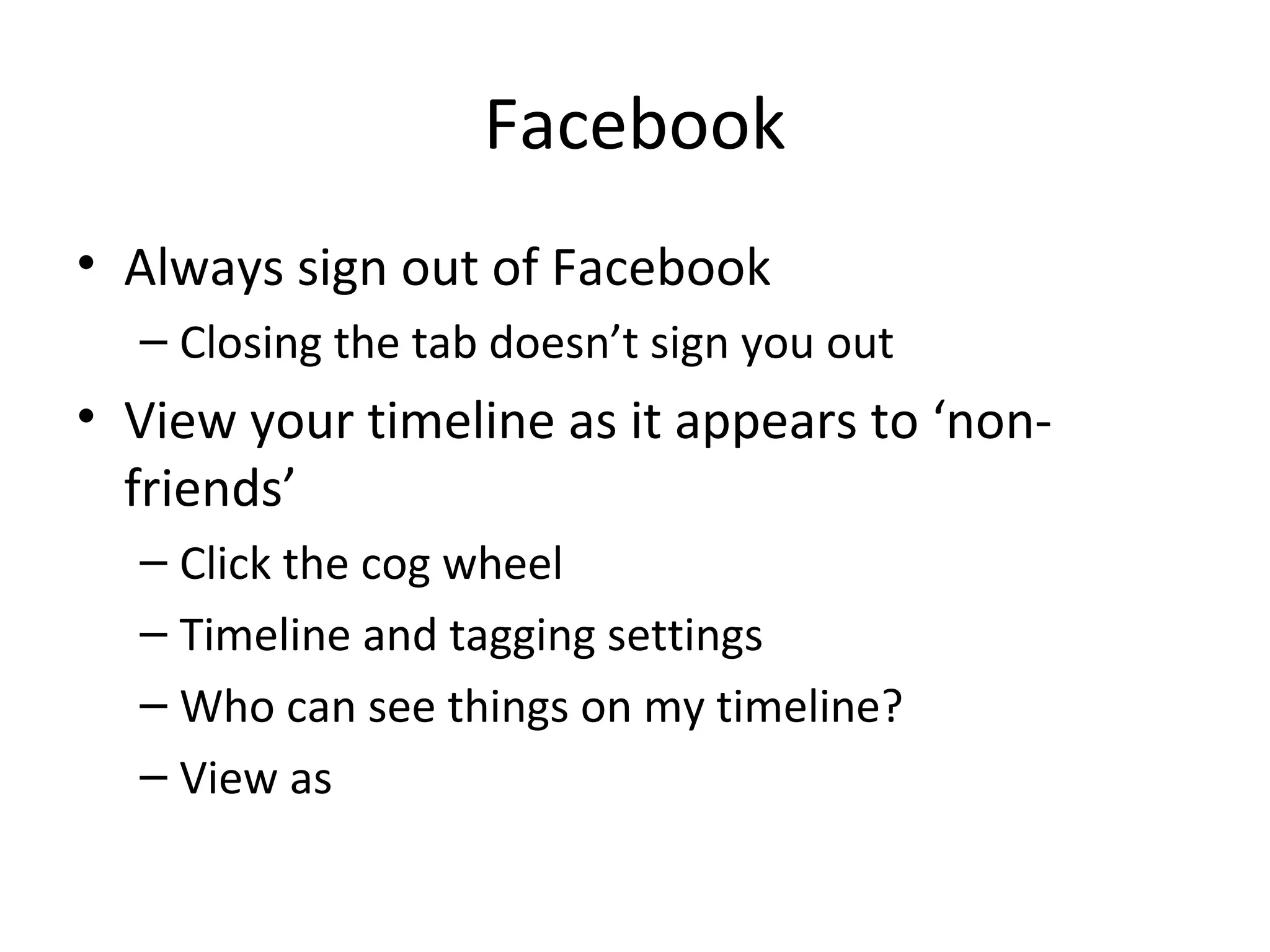
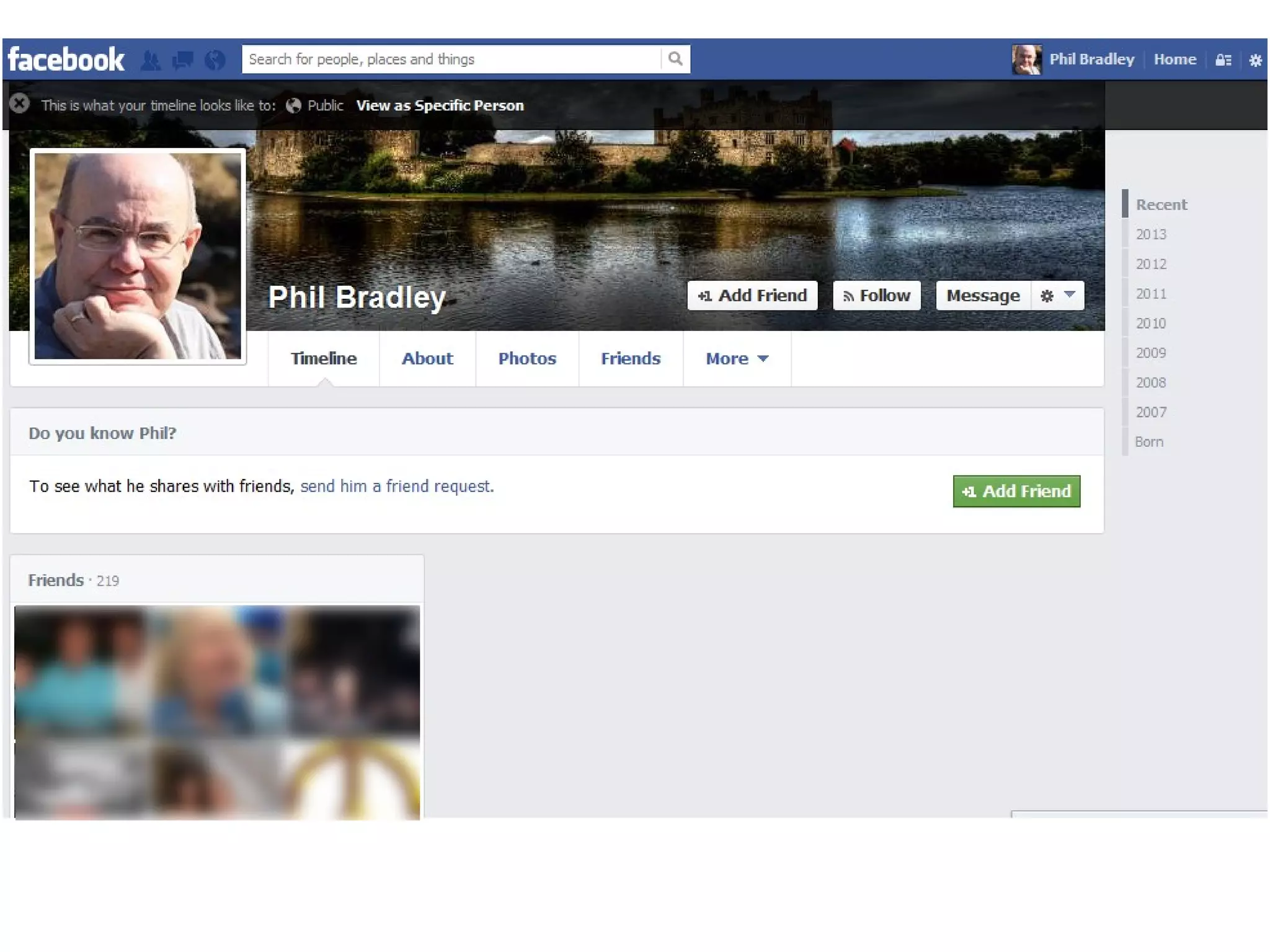
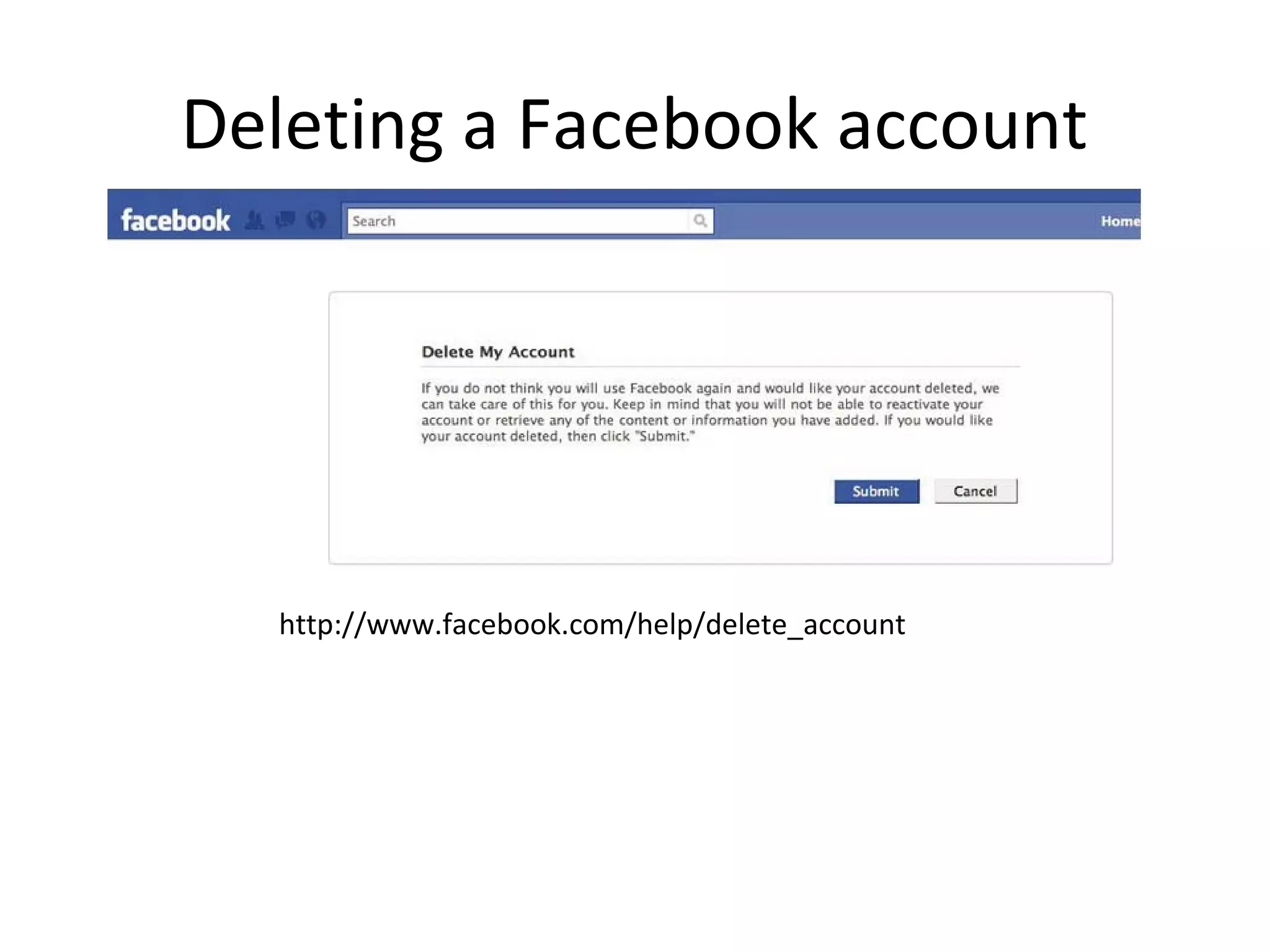
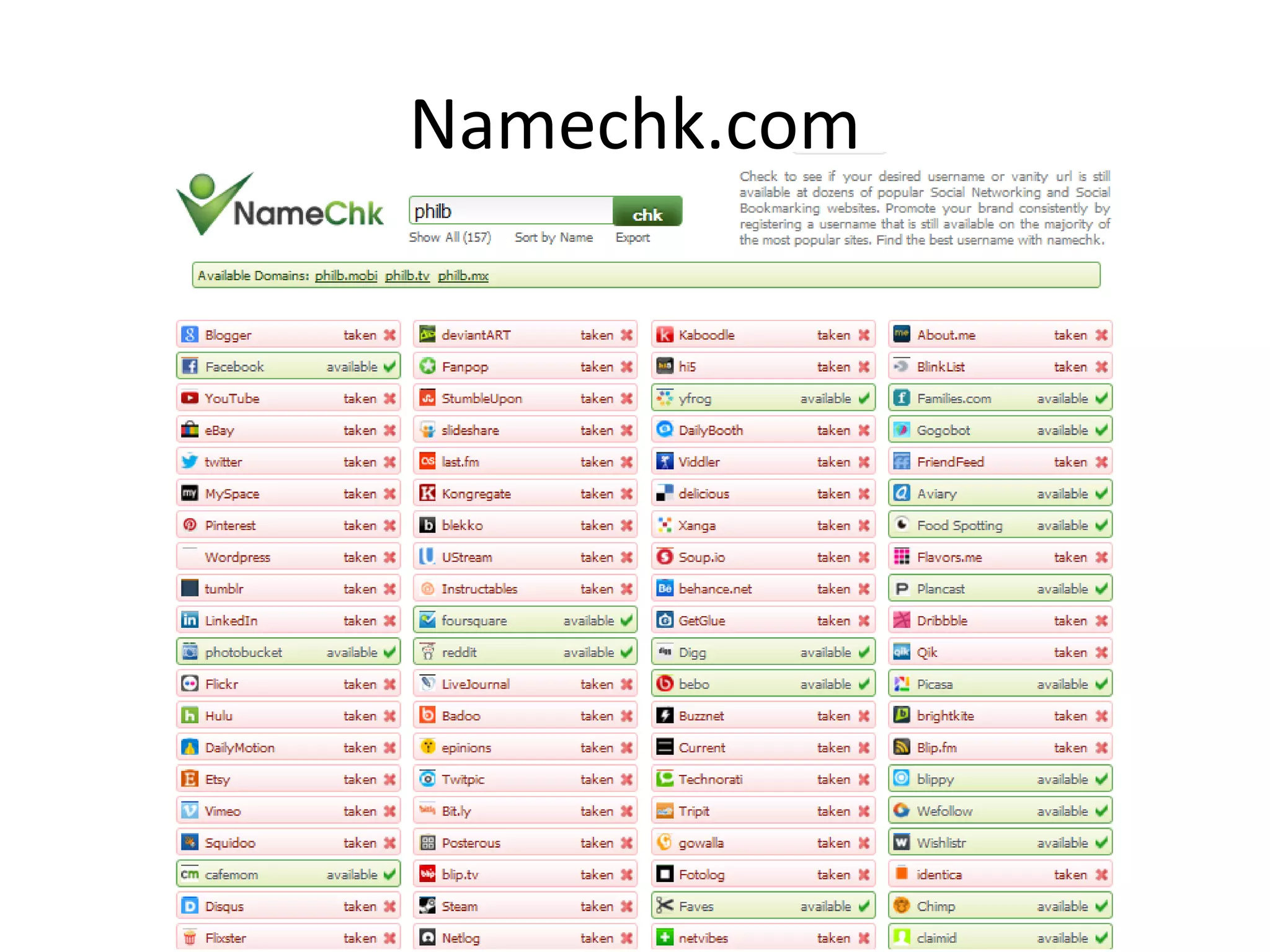
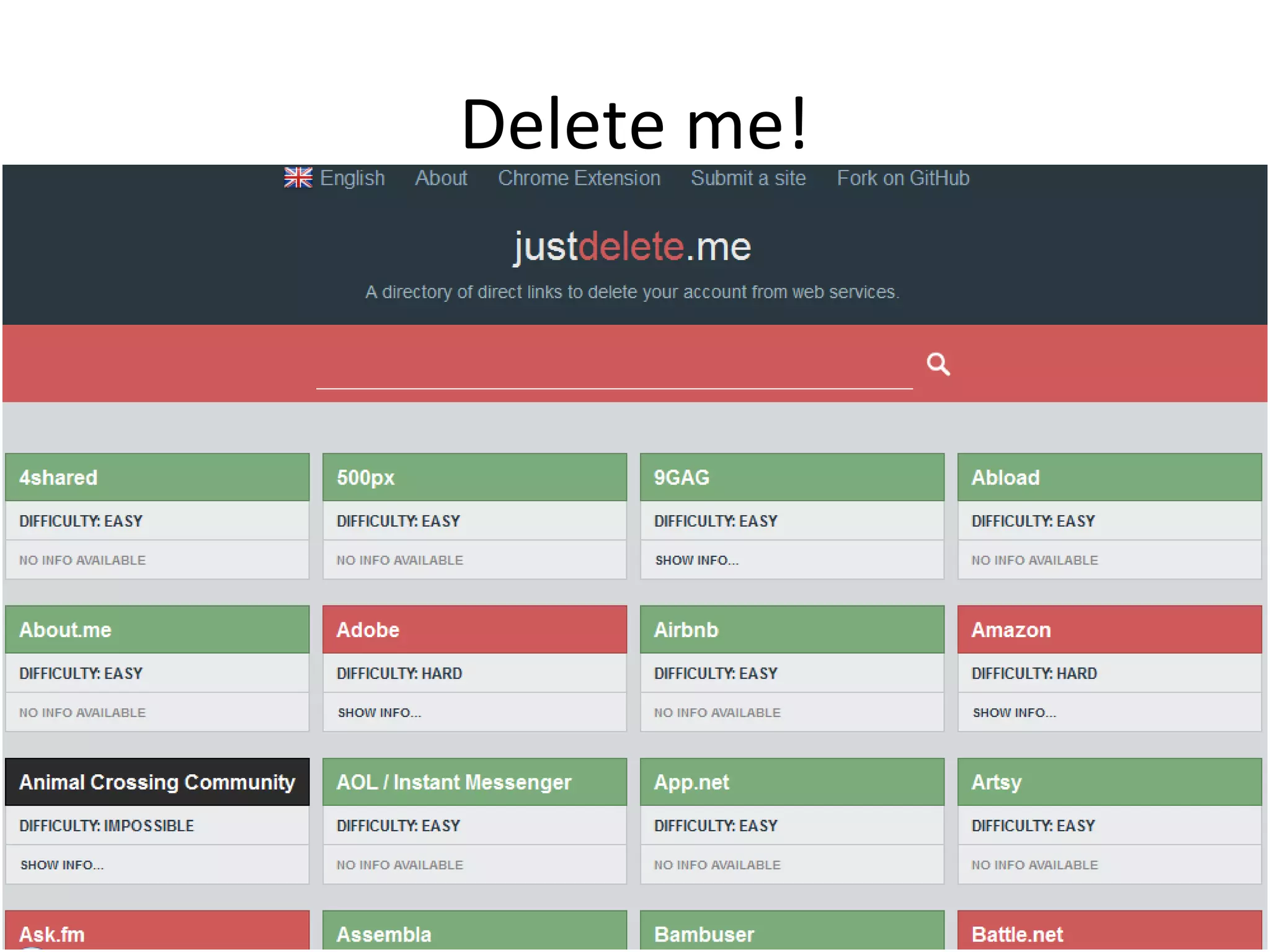
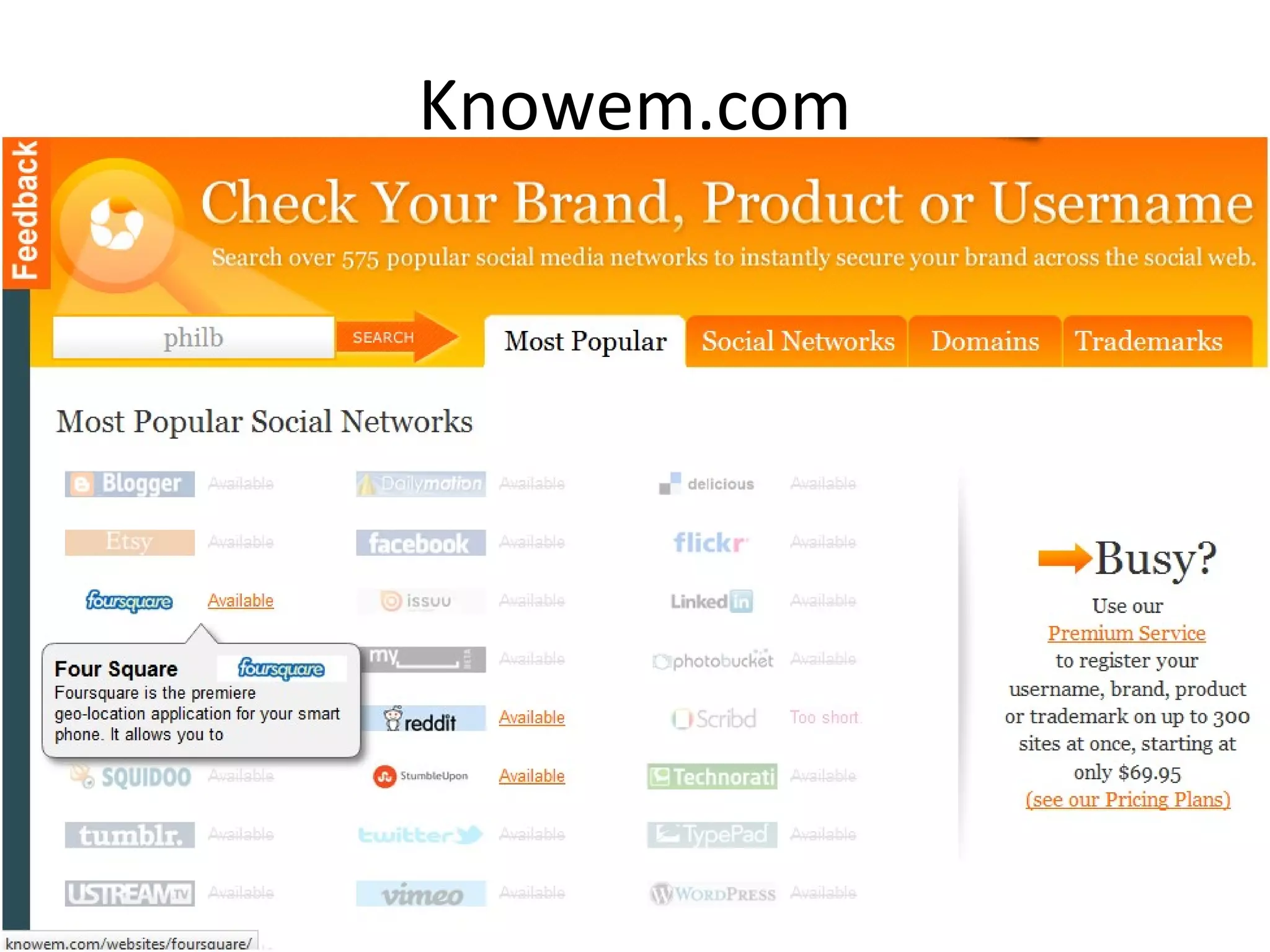
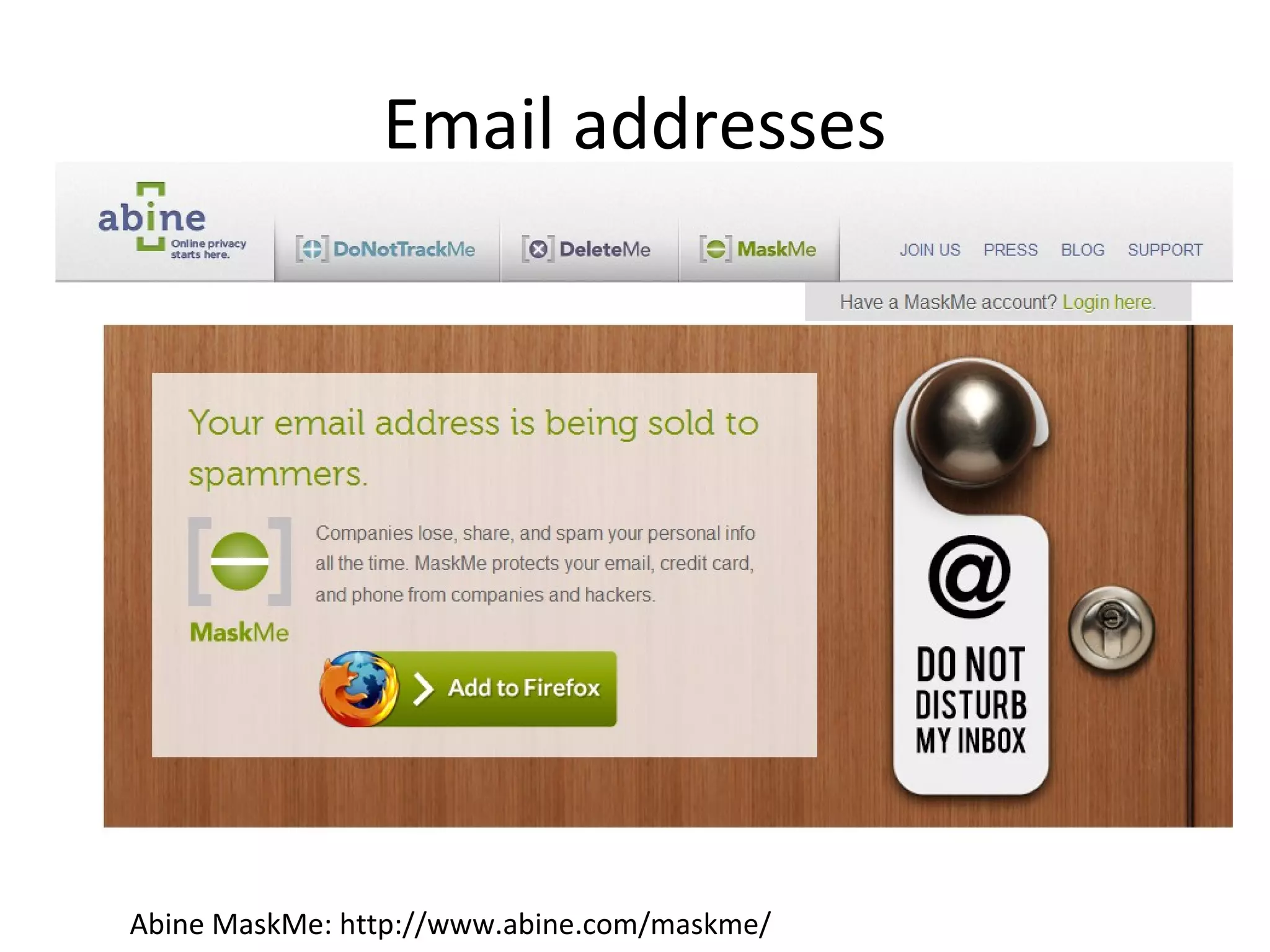
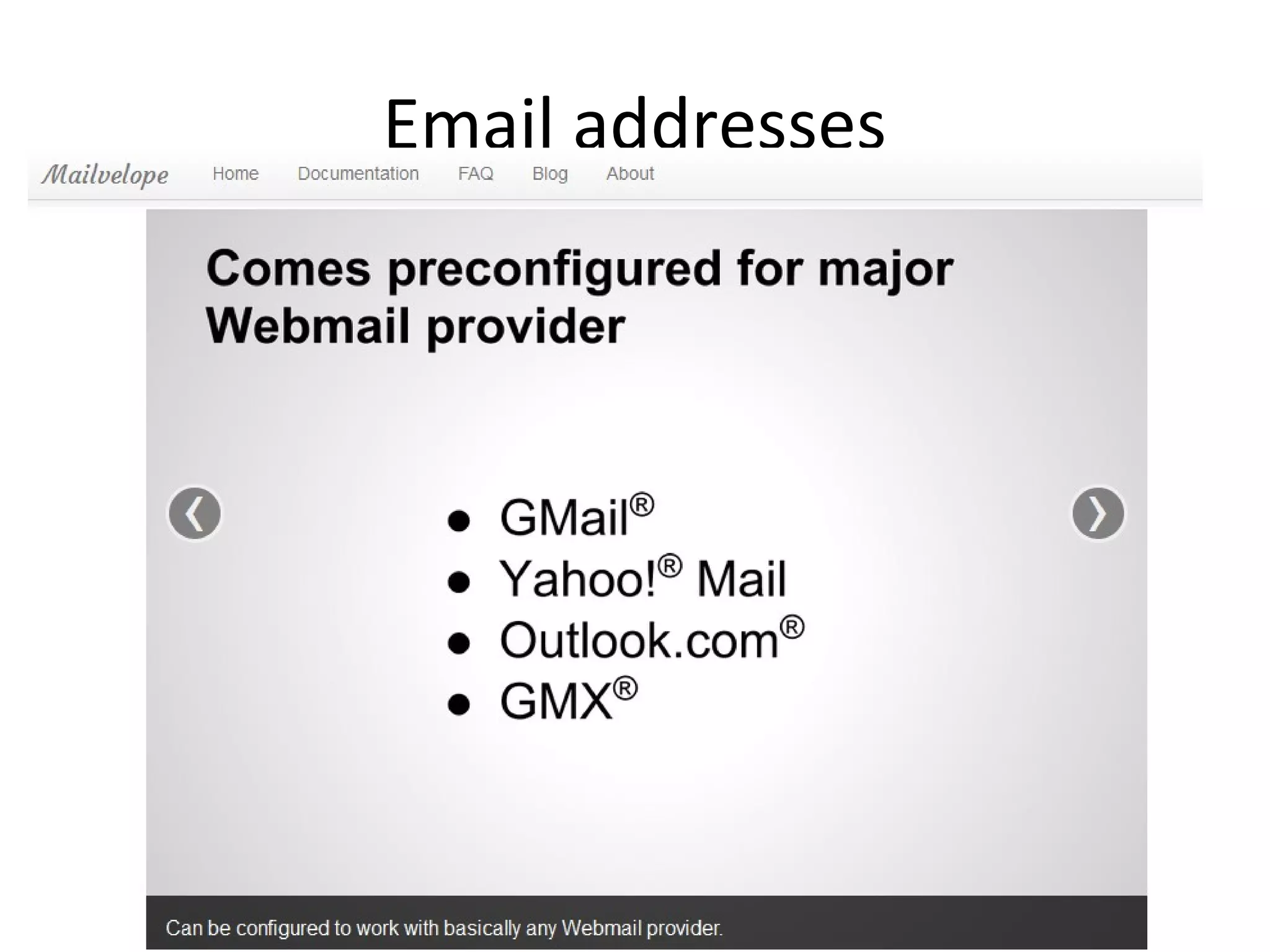
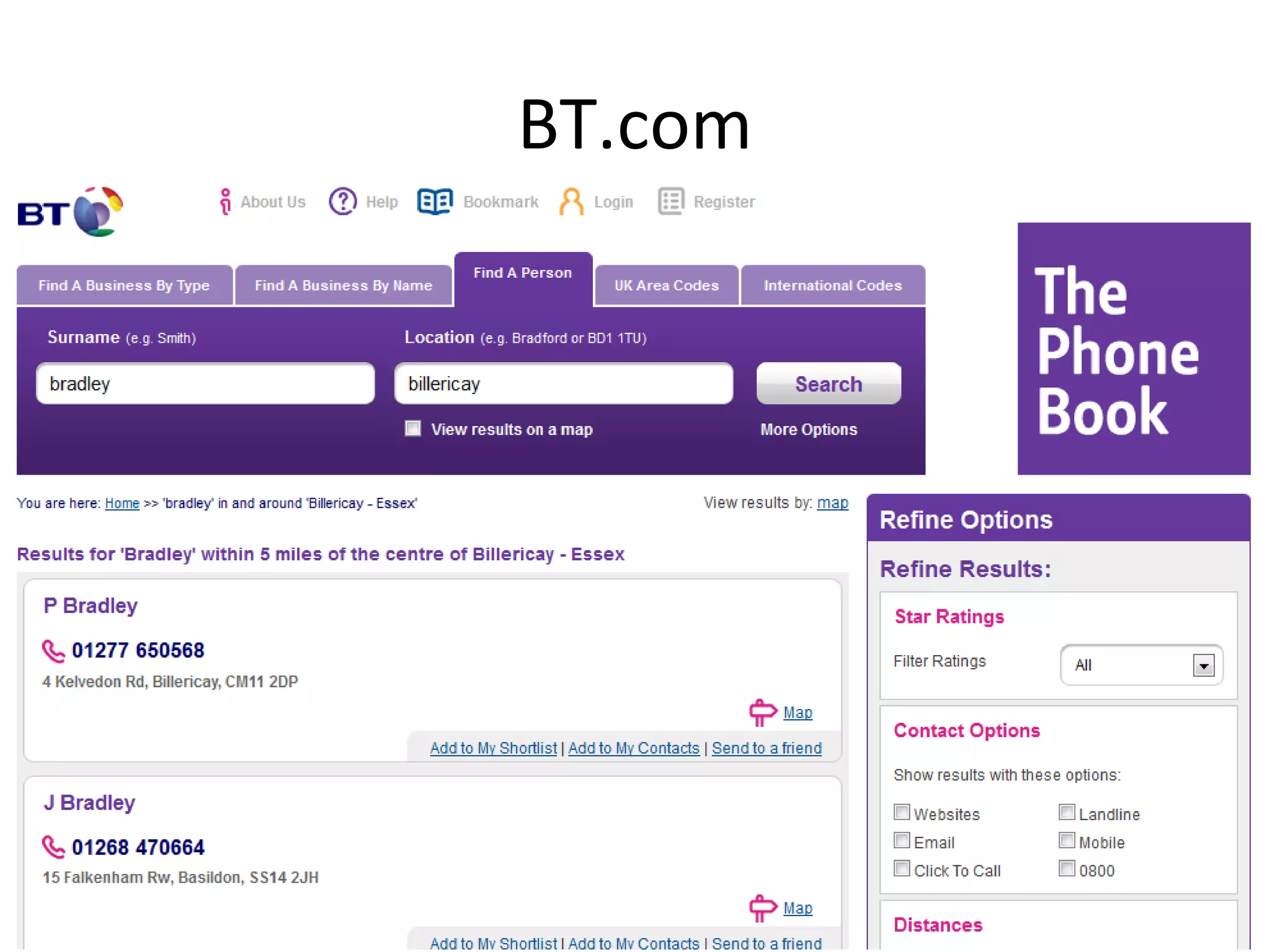
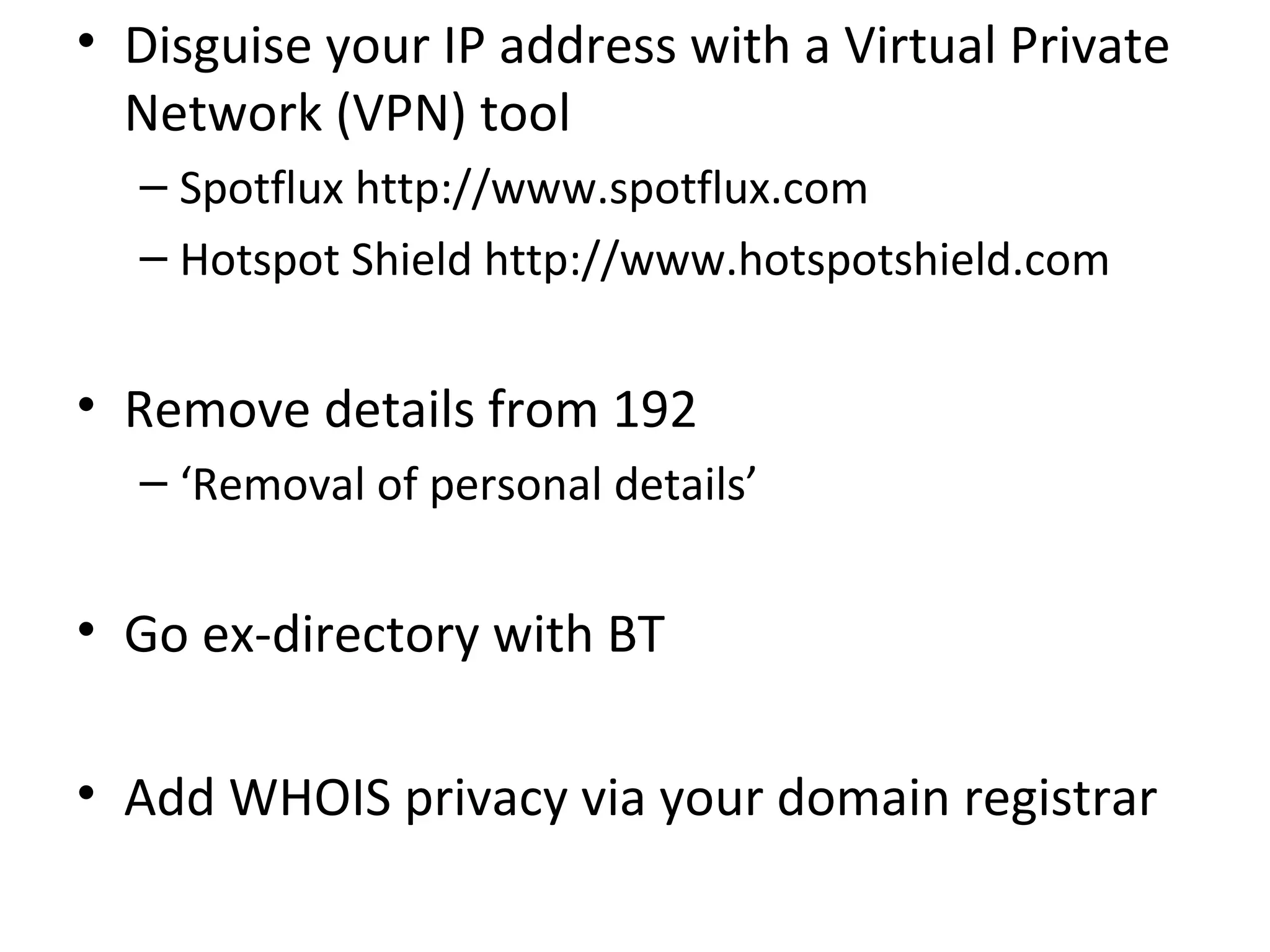
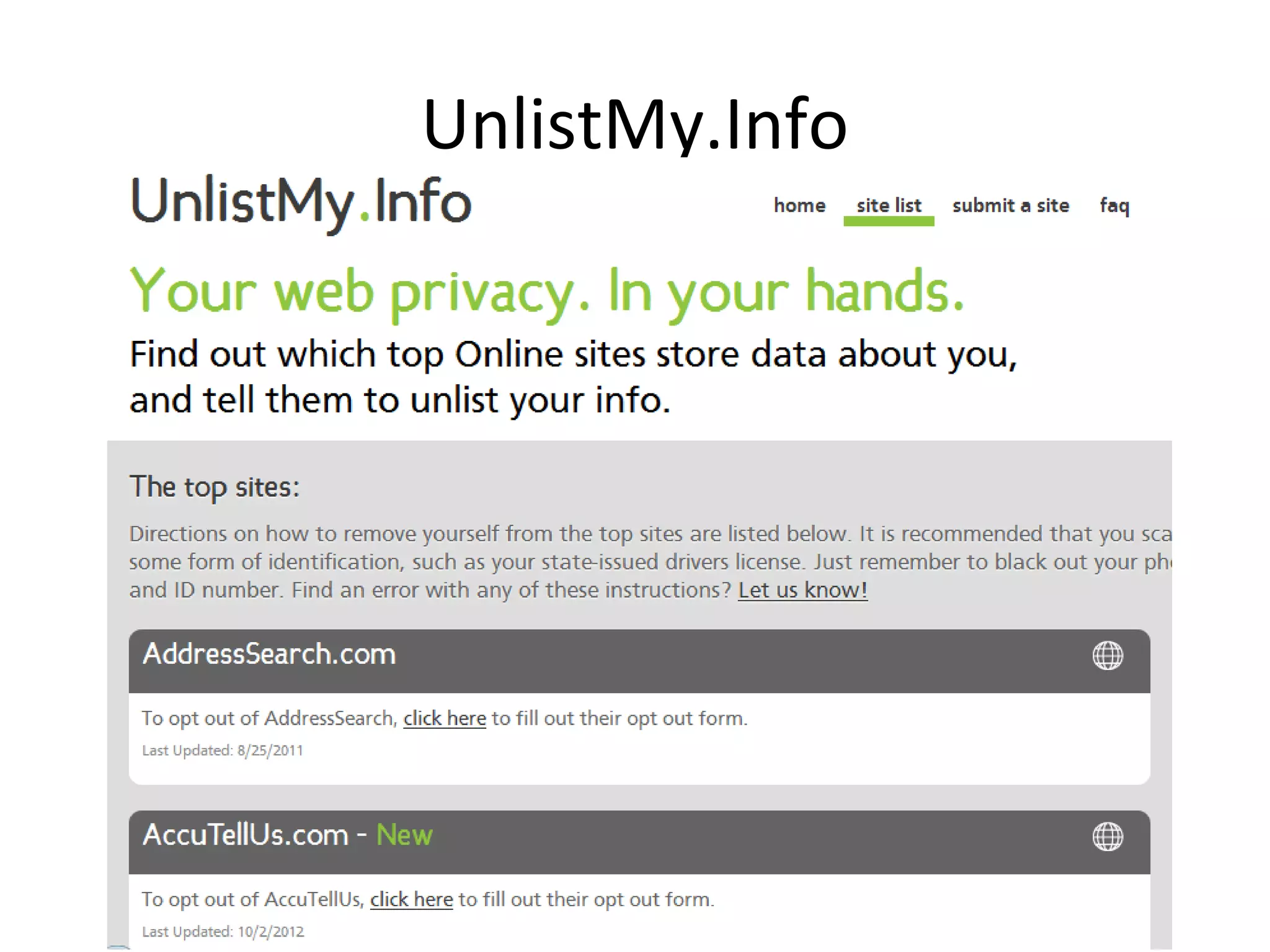
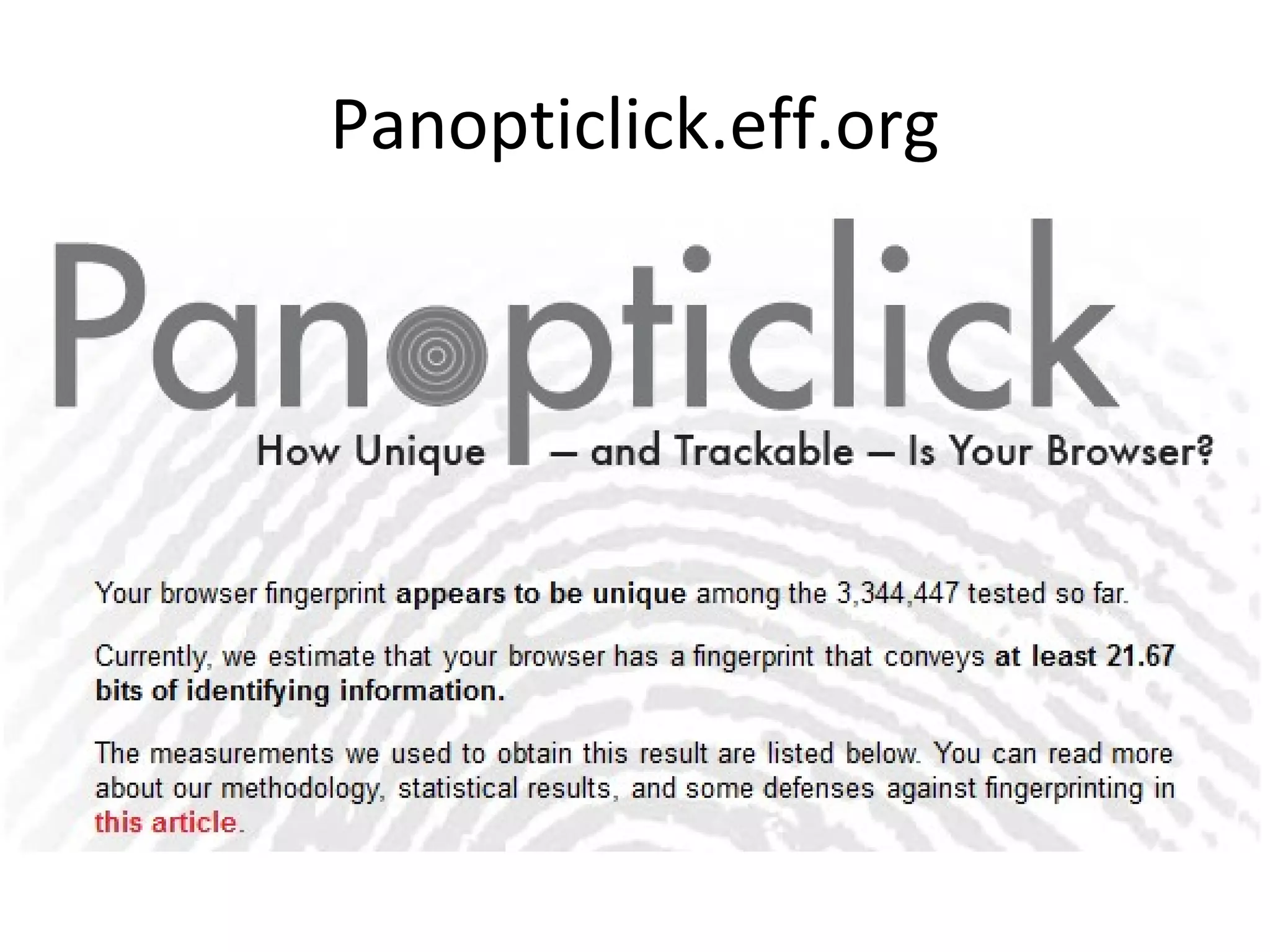
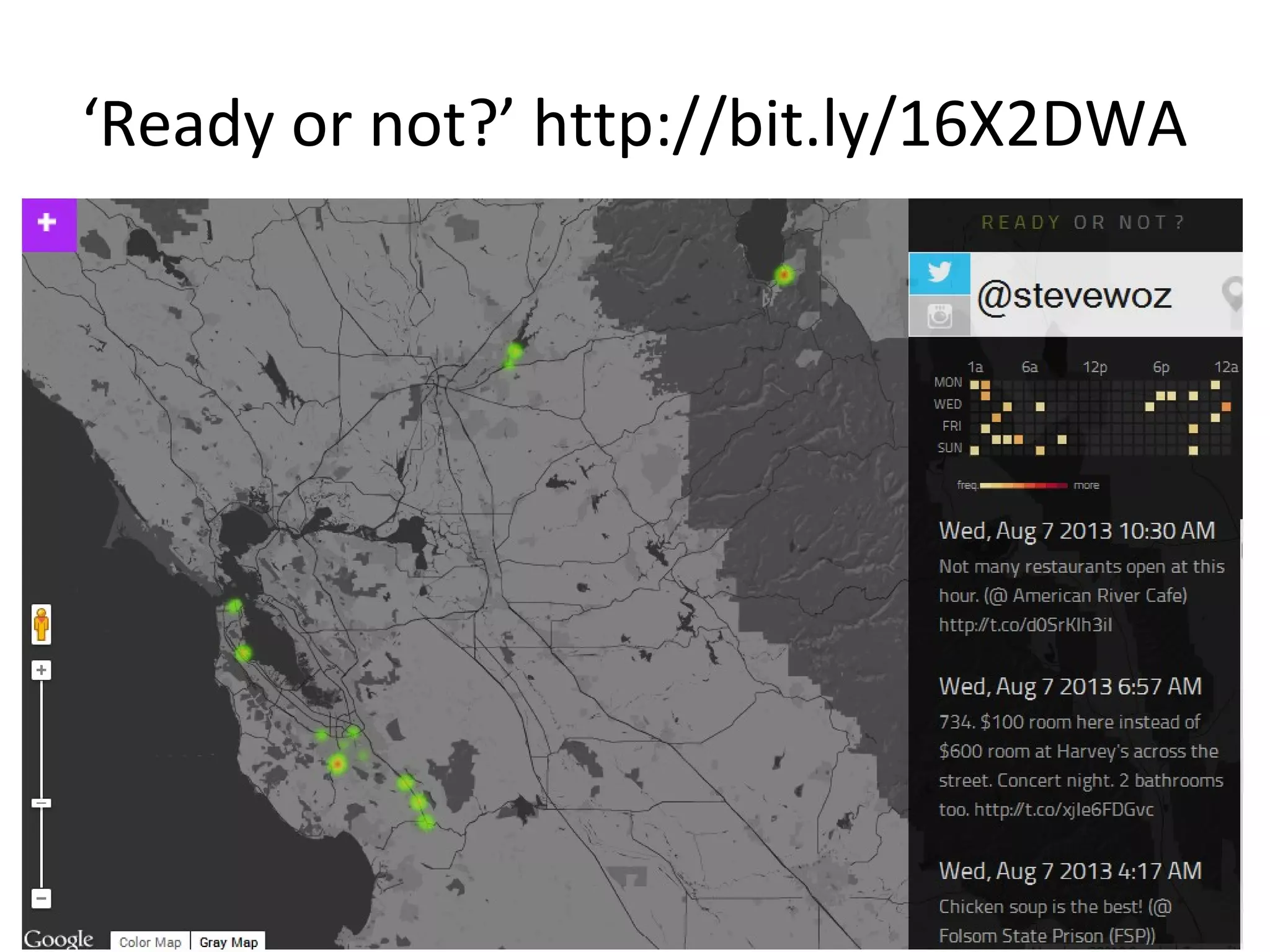
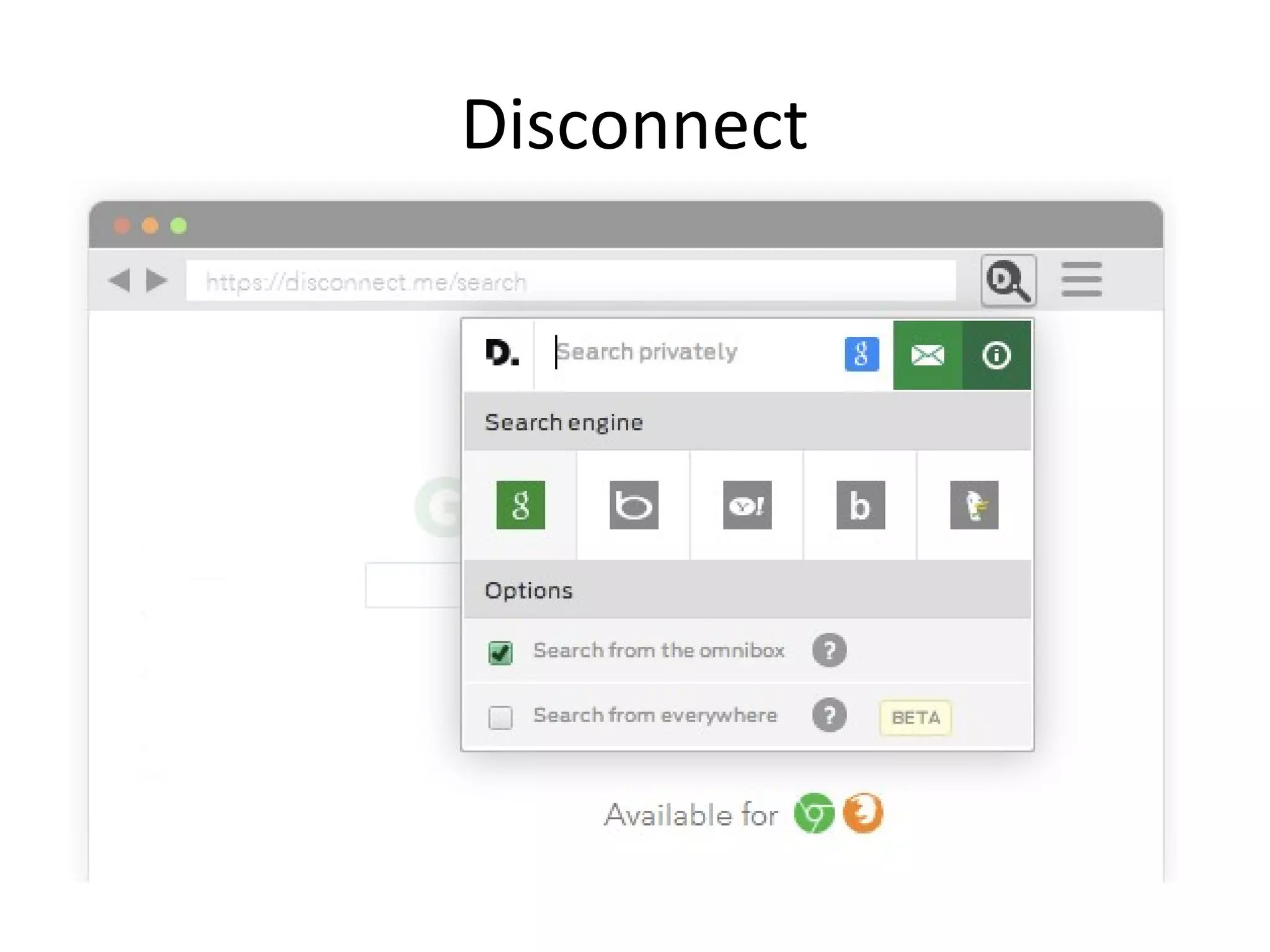
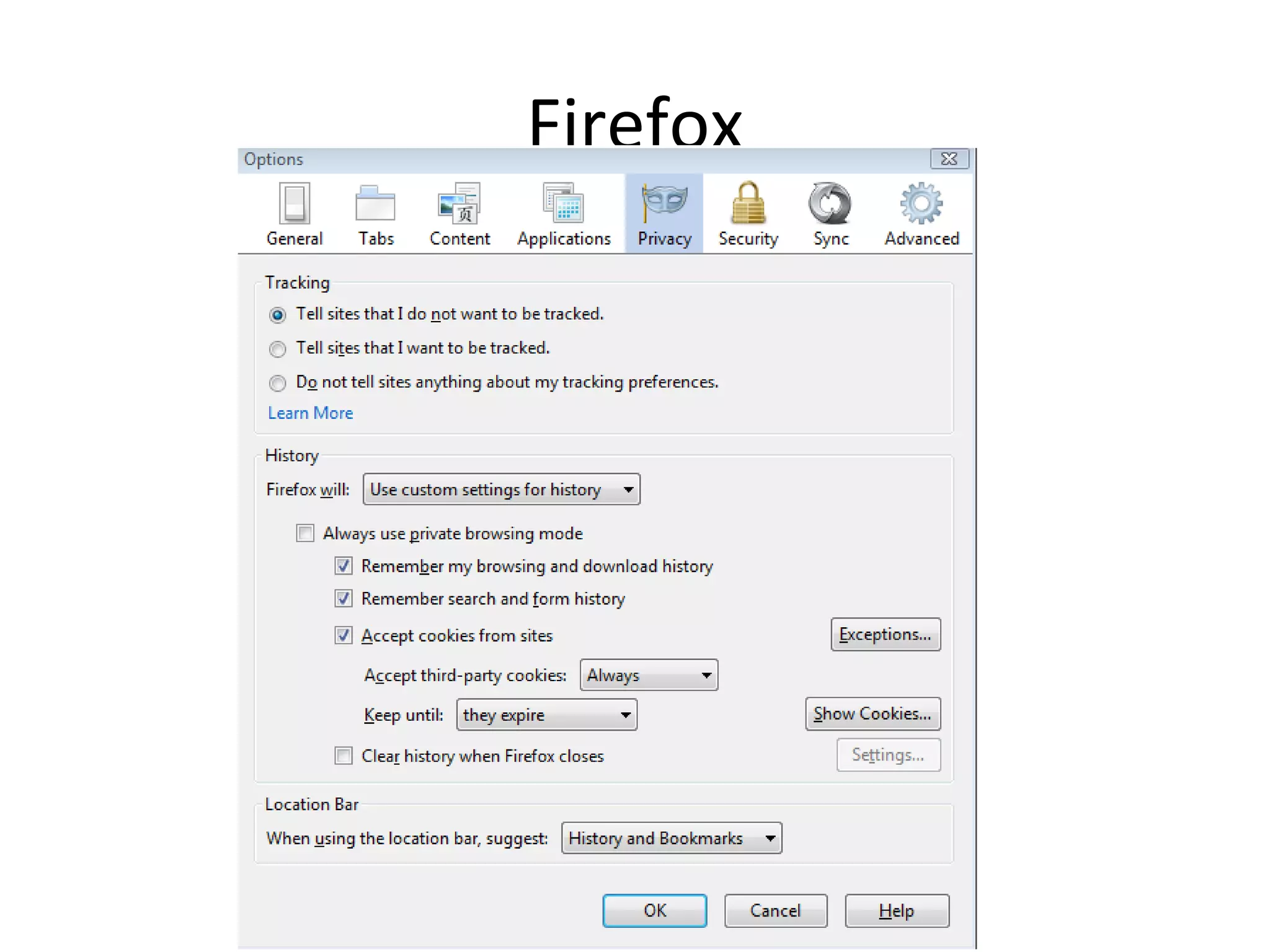
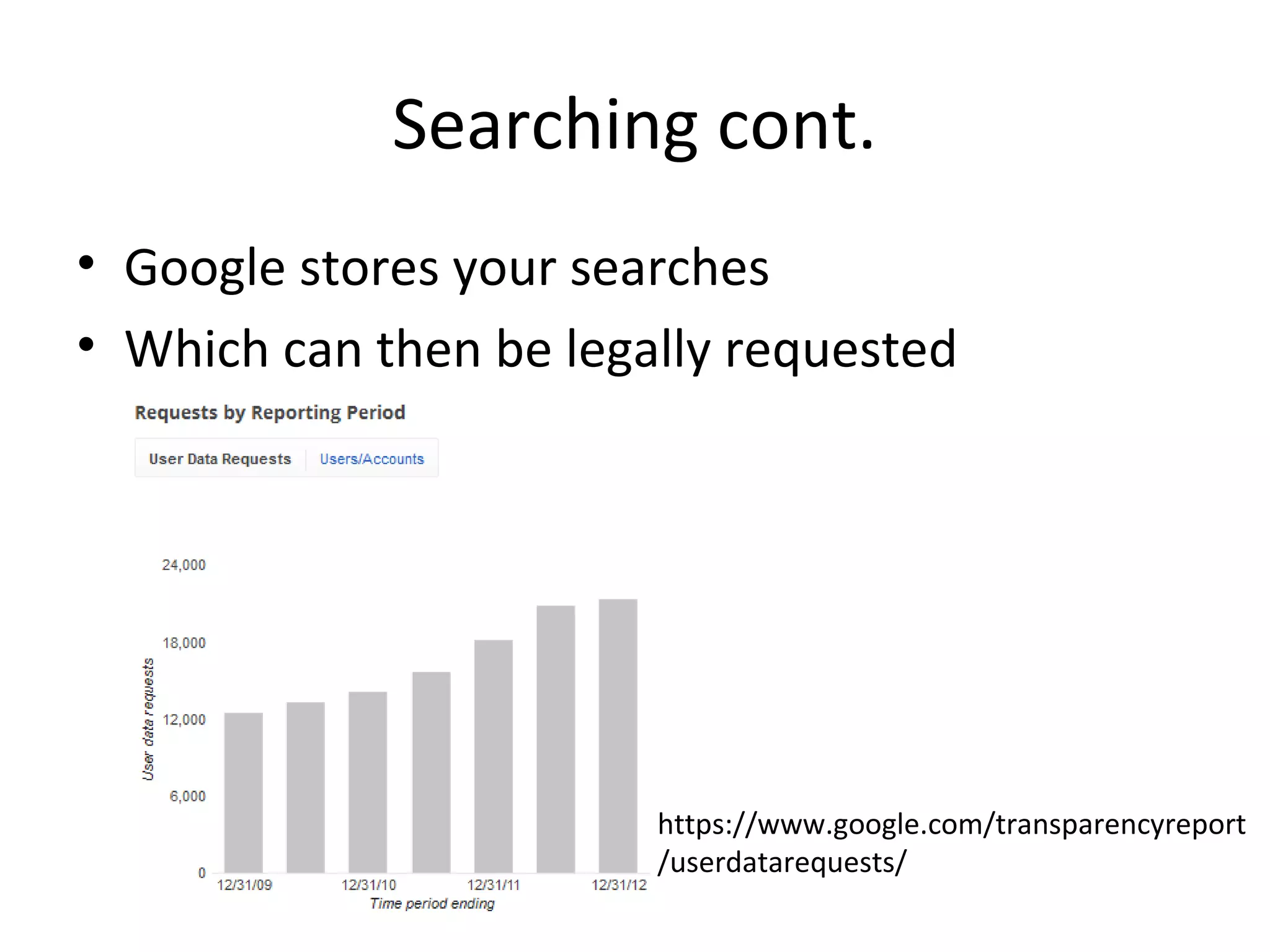
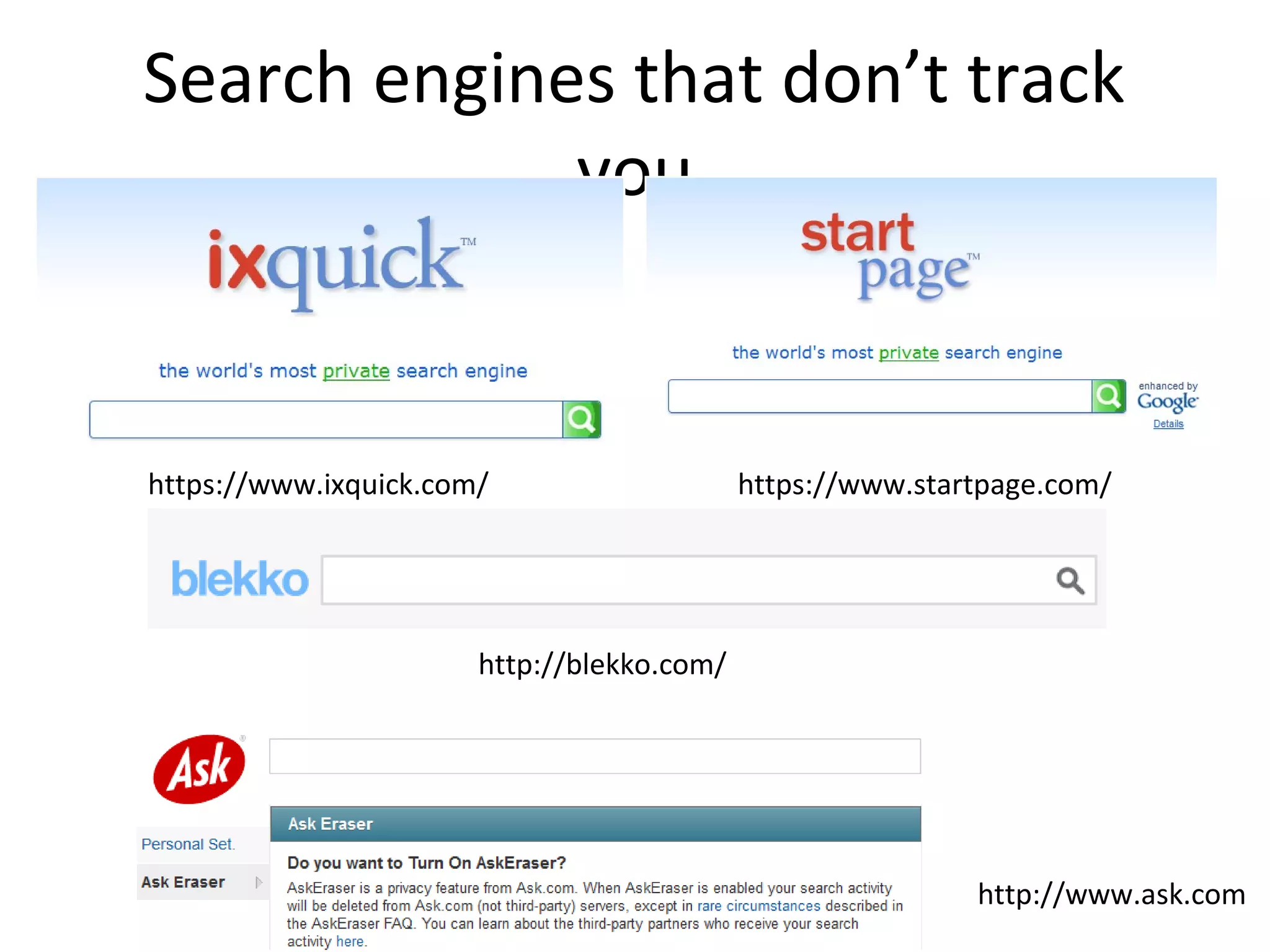
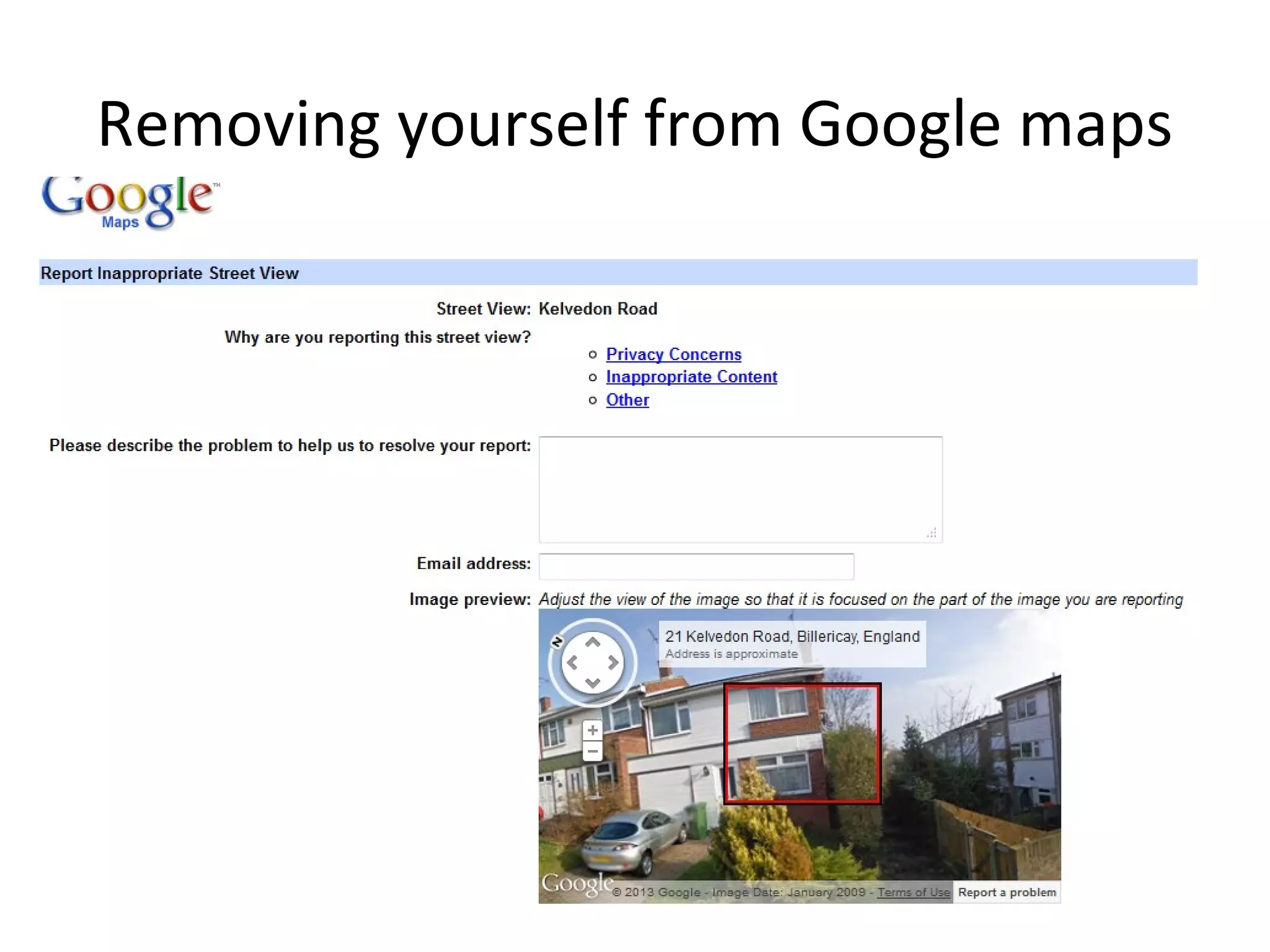
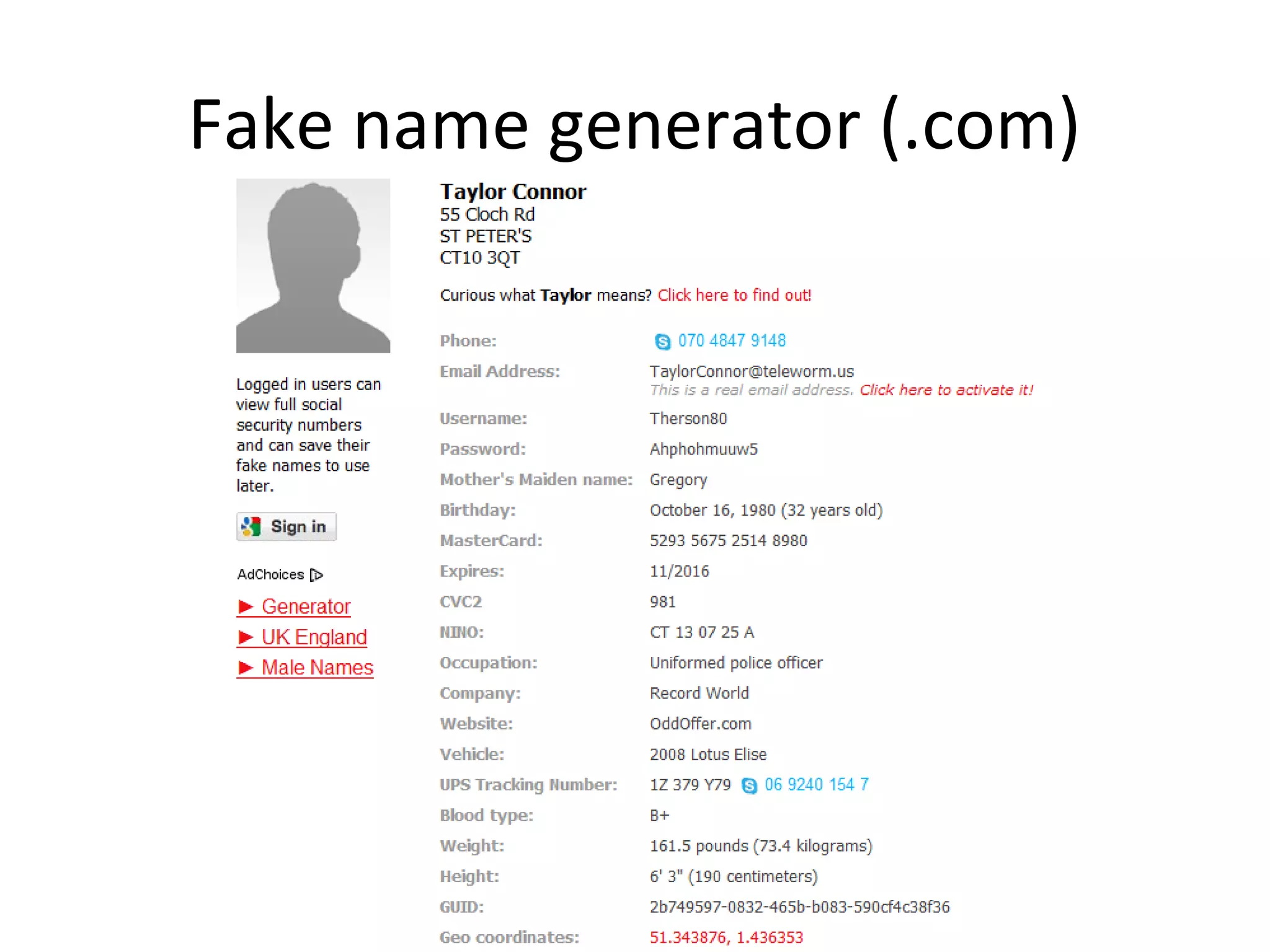
The document discusses various privacy concerns related to the internet, including data tracking, online harassment, and government surveillance. It highlights statistics on compromised accounts and emphasizes the importance of protecting personal information through tools like VPNs and alternative search engines. Additionally, it provides tips for managing privacy on social media and suggests organizations for further assistance.