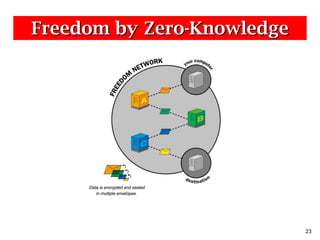
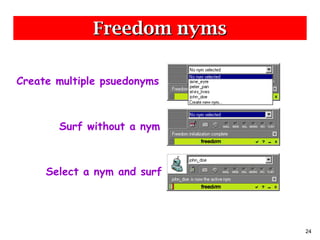
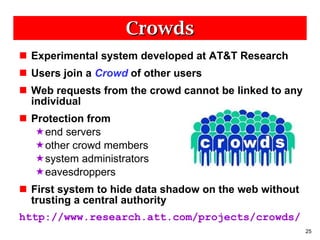
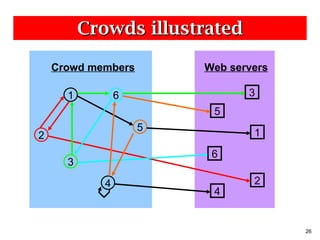
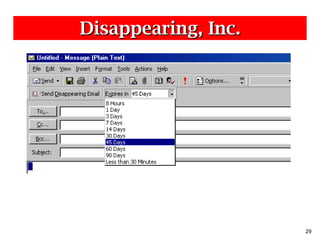
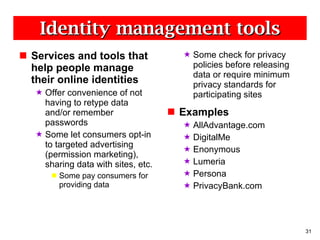
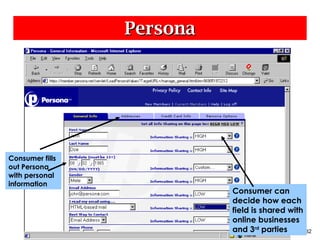
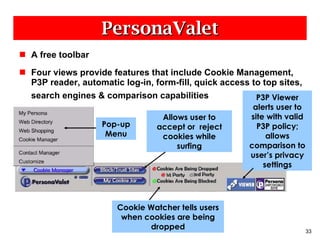
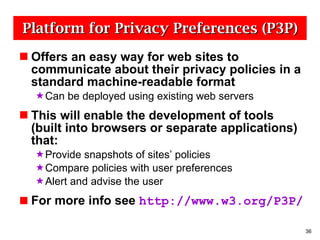
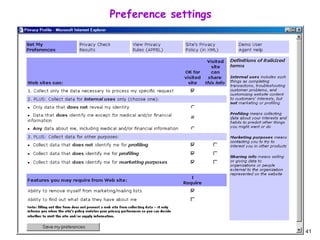
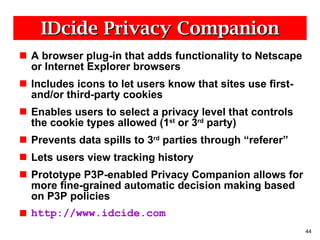
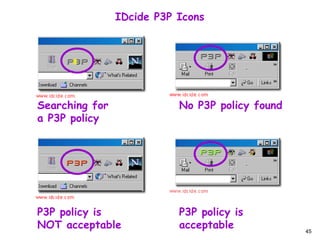
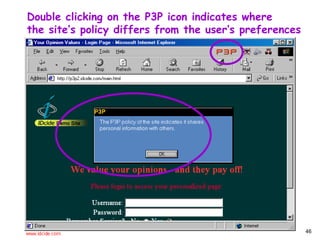
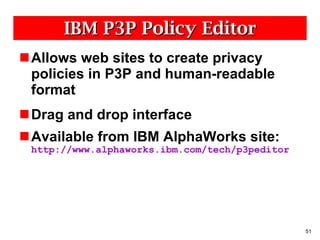
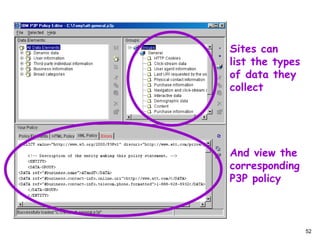
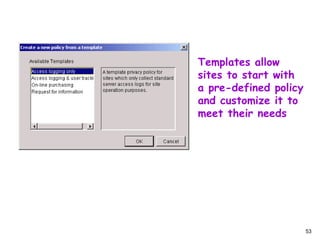
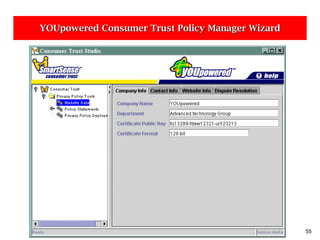
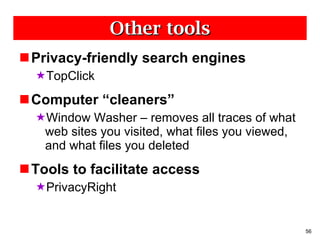
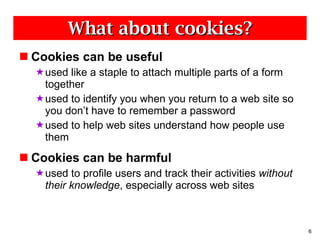
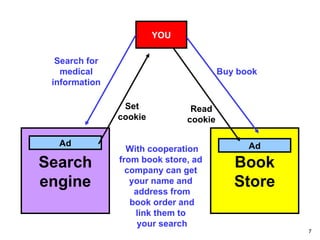
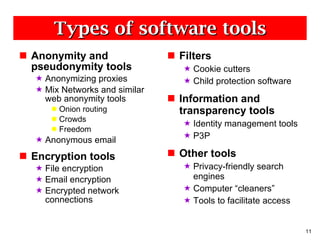
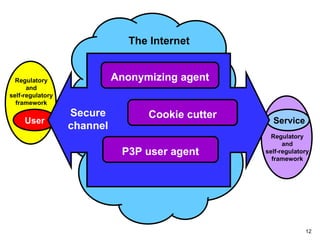
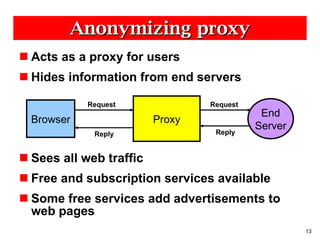
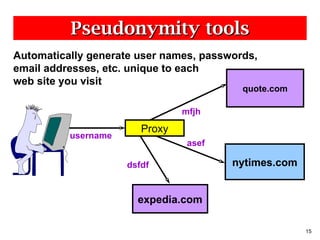
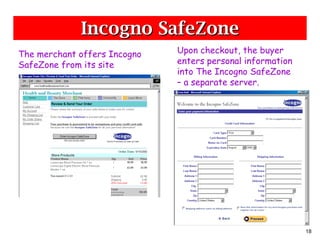
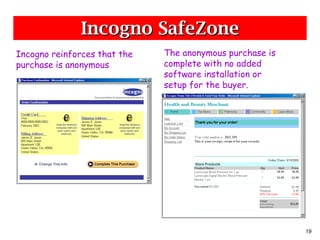
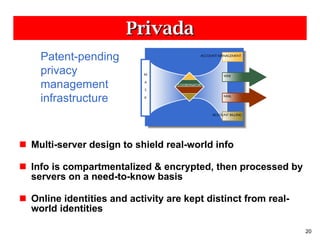
The document discusses various online privacy technologies and tools that can help protect user privacy and allow for more anonymous online activity. It describes technologies like anonymizing proxies, mix networks, onion routing, crowds, and encryption tools that help shield users' personal information and browsing activities from websites, advertisers, and other third parties. It also covers tools for filtering cookies and browser data, managing online identities, and reading websites' privacy policies. The goal is to provide an overview of the technical options available to help safeguard user privacy online.
![A typical HTTP request GET /retail/searchresults.asp?qu= beer HTTP/1.0 Referer: http://www.us.buy.com/default.asp User-Agent: Mozilla/4.75 [en] (X11; U; NetBSD 1.5_ALPHA i386) Host: www.us.buy.com Accept: image/gif, image/jpeg, image/pjpeg, */* Accept-Language: en Cookie: buycountry=us ; dcLocName=Basket; dcCatID=6773; dcLocID=6773; dcAd=buybasket; loc=; parentLocName=Basket; parentLoc=6773; ShopperManager%2F=ShopperManager%2F=66FUQULL0QBT8MMTVSC5MMNKBJFWDVH7; Store=107; Category=0](https://image.slidesharecdn.com/ntia-0900-111027135458-phpapp02/85/Ntia-0900-5-320.jpg)
![iPrivacy private shipping labels CUSTOMER PC Public Identity Private Identity John Doe iPrivacy ABCDEF 1 MAIN ST 1 dQg85xP26 Kansas City, KS Kansas City, KS 11122 11122 Doe@ isp .com [email_address] WEB FORM Name : iPrivacy ABCDEF Address: : 1 dQg85xP26 City : Kansas City State : KS Zip : 11122 Email : ABCDEF @iPrivacy.com WEB e- Tailer Order Entry System Submit Credit Card If Authorized Ship Product Shipping Subsystem Input Private Identity Decode Address PRINT LABEL iPrivacy ABCDEF 1 MAIN ST Kansas City, KS 11122](https://image.slidesharecdn.com/ntia-0900-111027135458-phpapp02/85/Ntia-0900-16-320.jpg)

![Mixes [Chaum81] Sender routes message randomly through network of “Mixes”, using layered public-key encryption. Mix A Sender Destination Mix C Mix B B, k A C k B dest,msg k C C k B dest,msg k C dest,msg k C msg k X = encrypted with public key of Mix X](https://image.slidesharecdn.com/ntia-0900-111027135458-phpapp02/85/Ntia-0900-22-320.jpg)