This document describes a proposed soft-computing system for identifying computer viruses using genetic algorithms, fuzzy logic, and neural networks. It discusses computer viruses and their types/characteristics. Seven key parameters for virus identification are identified: decline in system speed, numerous errors, persistent logoffs, disabled security software, abnormal internet behavior, obvious desktop changes, and continuous hard drive noise. The system would use fuzzy logic to set boundaries for the vague virus identification parameters. Genetic algorithms would optimize the fuzzy sets. Neural networks would provide self-learning abilities. Together this soft-computing approach aims to precisely and optimally recognize computer viruses.







![International Journal of Fuzzy Logic Systems (IJFLS) Vol.3, No2, April 2013
71
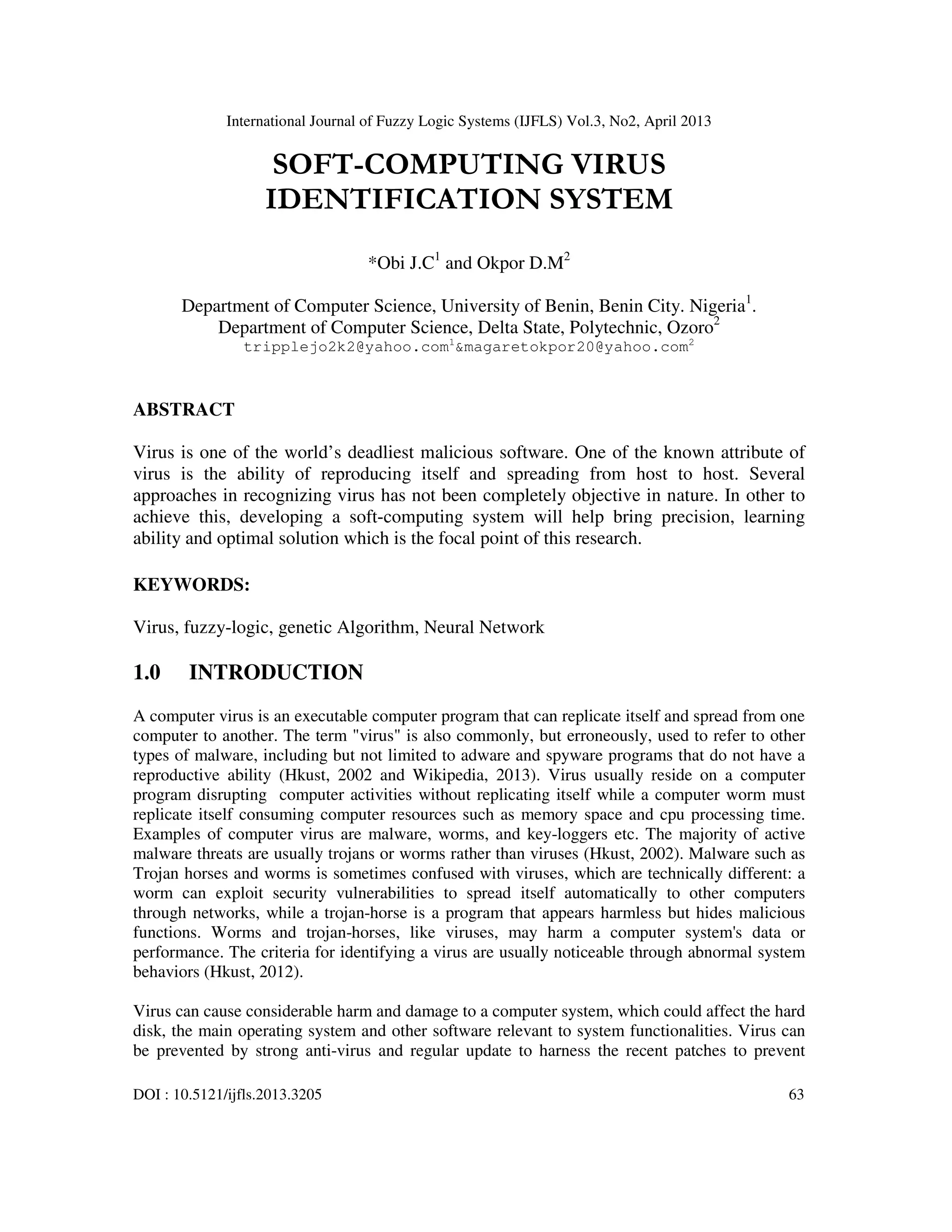
single bold bit signifies mutation of that bit and an italicized chromosomes signifies elitism. The
best fourth generation (stopping criterion) is that with the best fitness function, 54. This implies
that the clusters of the various parameters has been searched and optimized to 0.54. Therefore
combination of parameters which produce a membership function < 0.54 = C1, 0.54 = C2 and ≥
0.54 = C3 as presented in Figure 4.
Table 6: Data Set showing the Degree of membership of Operating System Process
4.0 CONCLUSION
A complete soft-computing client-side system for the identification of virus has been developed.
The developed system will indicate the recent state of a user system based on the aforementioned
parameters for the recognition of virus. Full Implementation of such system will go a long way in
curbing the spread of virus on computer systems.
REFERENCE
[1] AbdelnassirA. (2005), “Torque Ripple Minimization in Direct Torque Control of Induction
Machines” A Thesis Presented to The Graduate Faculty of the University of Akron In Partial
Fulfillment of the Requirements for the Degree Master of Science, retrieved online from
http://etd.ohiolink.edu/send-pdf.cgi/Abdalla%2520Abdelnassir.pdf?akron1116121267
[2] Arnold A. (2012), “Computer Virus Symptom List”, retrieved online from
http://www.ehow.com/list_6594924_computer-virus-symptomlist.html#ixzz2Mrmvxn6o.
Parameters Or Fuzzy Sets
Of Operating System Process
Codes Degree of Membership
Cluster 1
(C1)
Cluster 2
(C2)
Cluster 3
(C3)
Decline system speed R01 0.50 0.15 0.35
Numerous stem errors R02 0.20 0.20 0.60
Persistent logoff R03 0.10 0.80 0.10
Disable security software R04 0.20 0.10 0.70
Obvious desktop change R05 0.30 0.60 0.10
Abnormal internet system behaviors R06 0.05 0.05 0.90
Continuous hard change R07 0.00 0.50 0.50
Result Virus
Infected
System
Moderatel
y Secured
System
Secure
System](https://image.slidesharecdn.com/ijfls05-130514034233-phpapp01/85/Ijfls05-9-320.jpg)
![International Journal of Fuzzy Logic Systems (IJFLS) Vol.3, No2, April 2013
72
[3] BabakB. R.., Maslin M. and Suhaimi I. (2011), “Evolution of Computer Virus Concealment and Anti-
Virus Techniques: A Short Survey”,International Journal of Computer Science Issues (IJCSI), Vol. 8, Issue 1, pp.
113-121.
[4] Cengiz K., Sezi C., Nufer Y.A. and Murat G. (2007), “Fuzzy multi-criteria evaluation of industrial
robotic systems” , Computers & Industrial Engineering, Vol. 52, Issue 4, Pages 414–433.
[5] Christian J. and Gustav E. (2003), “Optimizing Genetic Algorithms for Time Critical
Problems”,Department of Software Engineering and Computer Sciencelekinge Institute of
Technology Box 520 SE ä 372 25 Ronneby Sweden.
[6] Christos S. and Dimitros S. (2008) “Neural Network”, retrieved from
http://www.docstoc.com/docs/15050/neural-networks.
[7] Larry A. (2013), “How to Identify Computer Virus Symptoms” retrieved online from
http://www.ehow.com/how_4903119_identify-computer-virus-symptoms.html#ixzz2Mr
[8] Hkust,(2002), Types of Virus”, retrieved online from
http://www.ust.hk/itsc/antivirus/general/types.html
[9] Kasabov N. K. (1998), “Foundations of neural networks, fuzzy systems, and knowledge
engineering”, A Bradford Book, The MIT Press Cambridge, Massachusetts London, England, ISBN
0-262-11212-4.
[10] Leondes C (2010), “The Technology of Fuzzy Logic Algorithm retrieved from
Suite101.com/examples-of-expert-System-application-in-artificial Intelligence.
[11] Mathias K. (2003), “A Critical Look at the regulations of Computer Viruses”, International Journal
of Law and Information technology, Retrieved online from http://www.digital-rights.net/wp-
content/uploads/2008/01/klang_virus_ijlit.pdf.
[12] Nitesh K. D., Lokesh m., Mahendra S. C. and Bhabesh K. D., (2012), “The New Age
OfComputer Virus And Their Detection”, International Journal of Network Security & Its
Applications (IJNSA), Vol.4, No.3, retrieved on from http://airccse.org/journal/jnsa12_current.html
[13] Robert F. (1995), “Neural Fuzzy Systems”retrieved online from
http://faculty.petra.ac.id/resmana/basiclab/fuzzy/fuzzy_book.pdf.
[14] Simon S.H. (1999), “Neural Network: A comprehensive Foundation, Pretice Hall, Chapter 1-15, Pp.
1-889)
[15] Tom B. (2002), “Retail Market Basket Analysis: A Quantitative Modelling Approach” Dissertation
submitted to obtain the degree of Doctor in Applied Economic Sciences at the Limburg University
Center.
[16] Wikipedia (2013), “Computer virus” retrieved online from en.wikipedia.org/wiki/
[17] Zadeh L. A. (1965), “Fuzzy sets, Information and Control”, Vol.8, pp.338-353.](https://image.slidesharecdn.com/ijfls05-130514034233-phpapp01/85/Ijfls05-10-320.jpg)