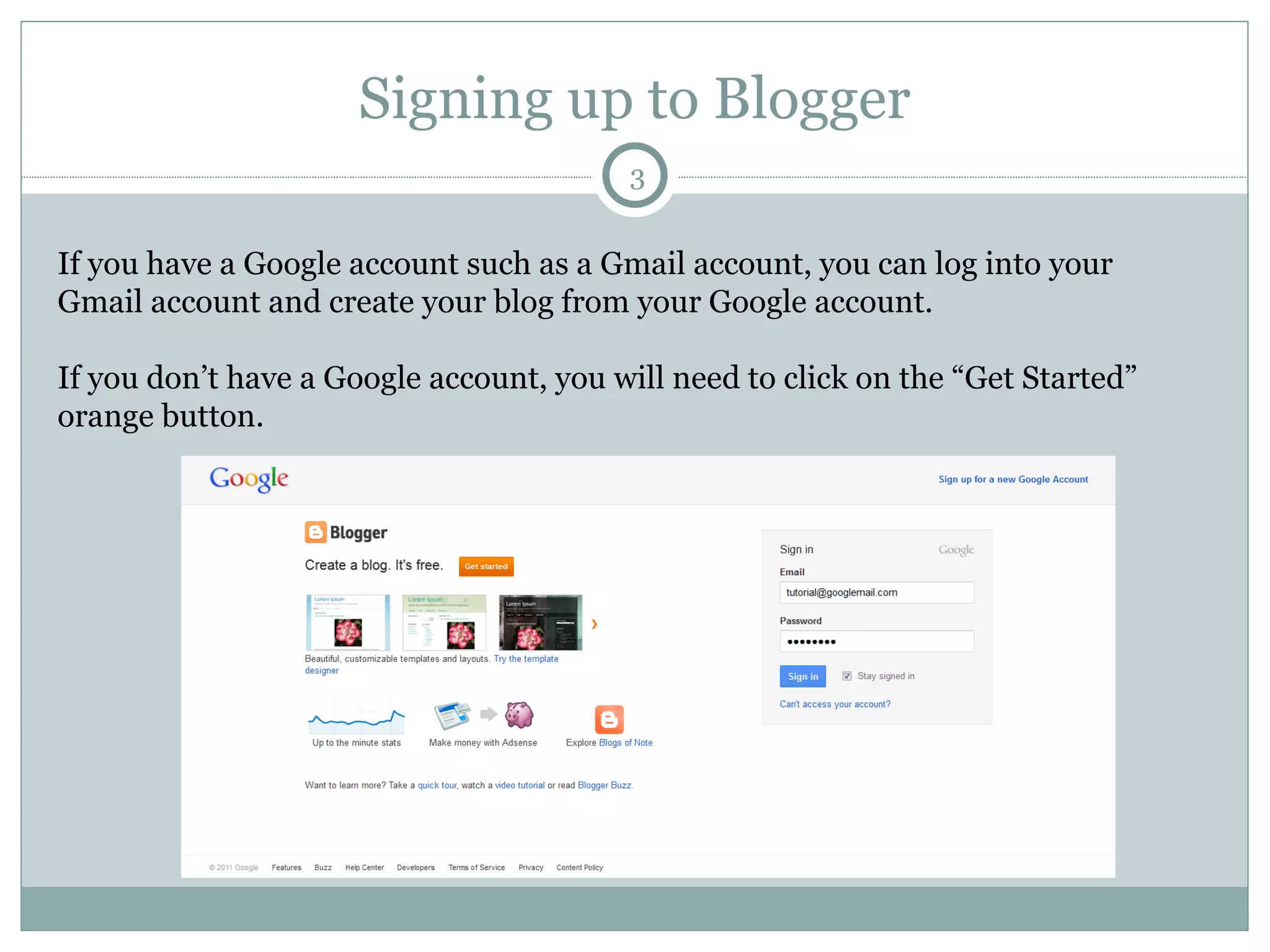
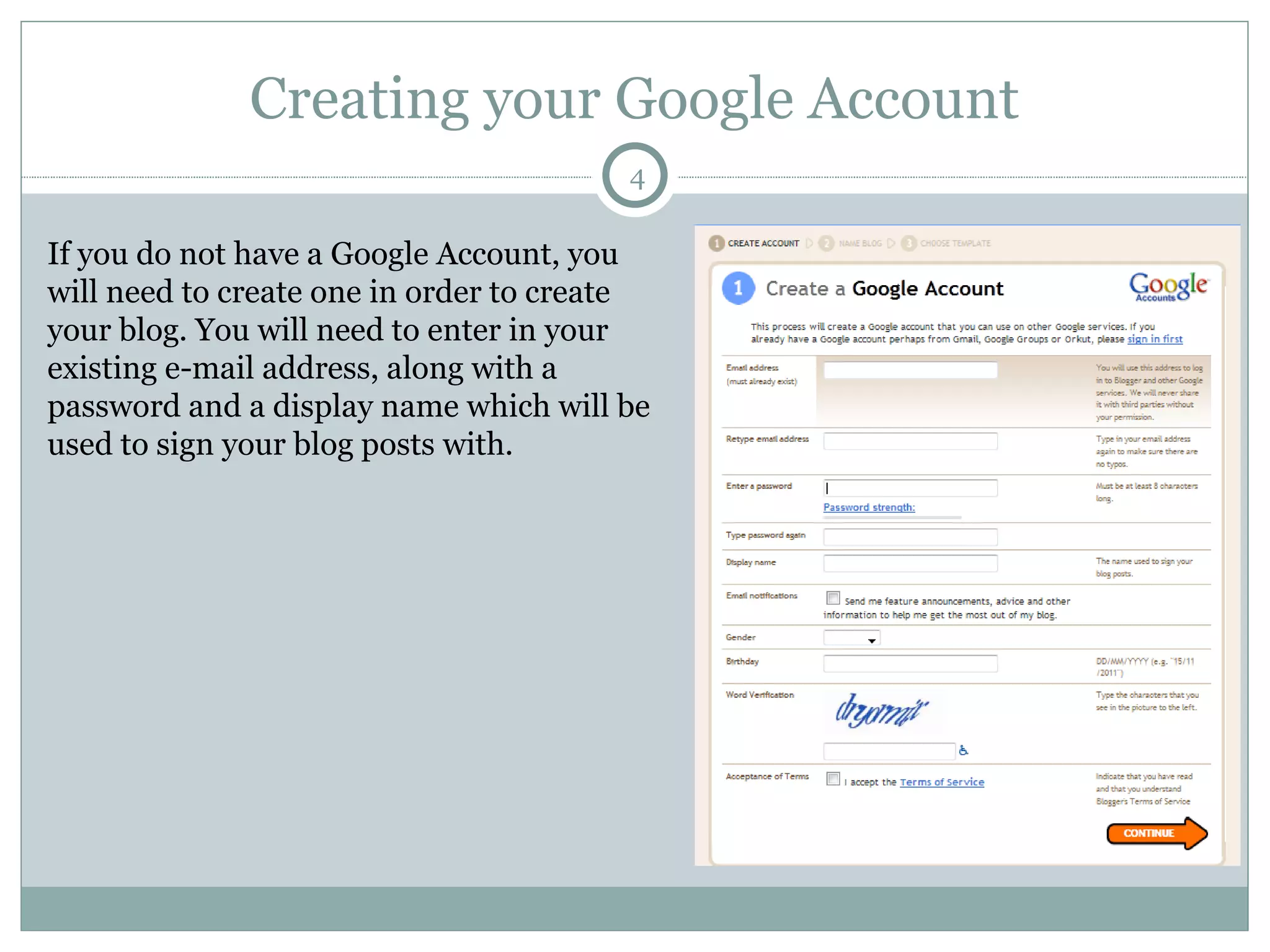
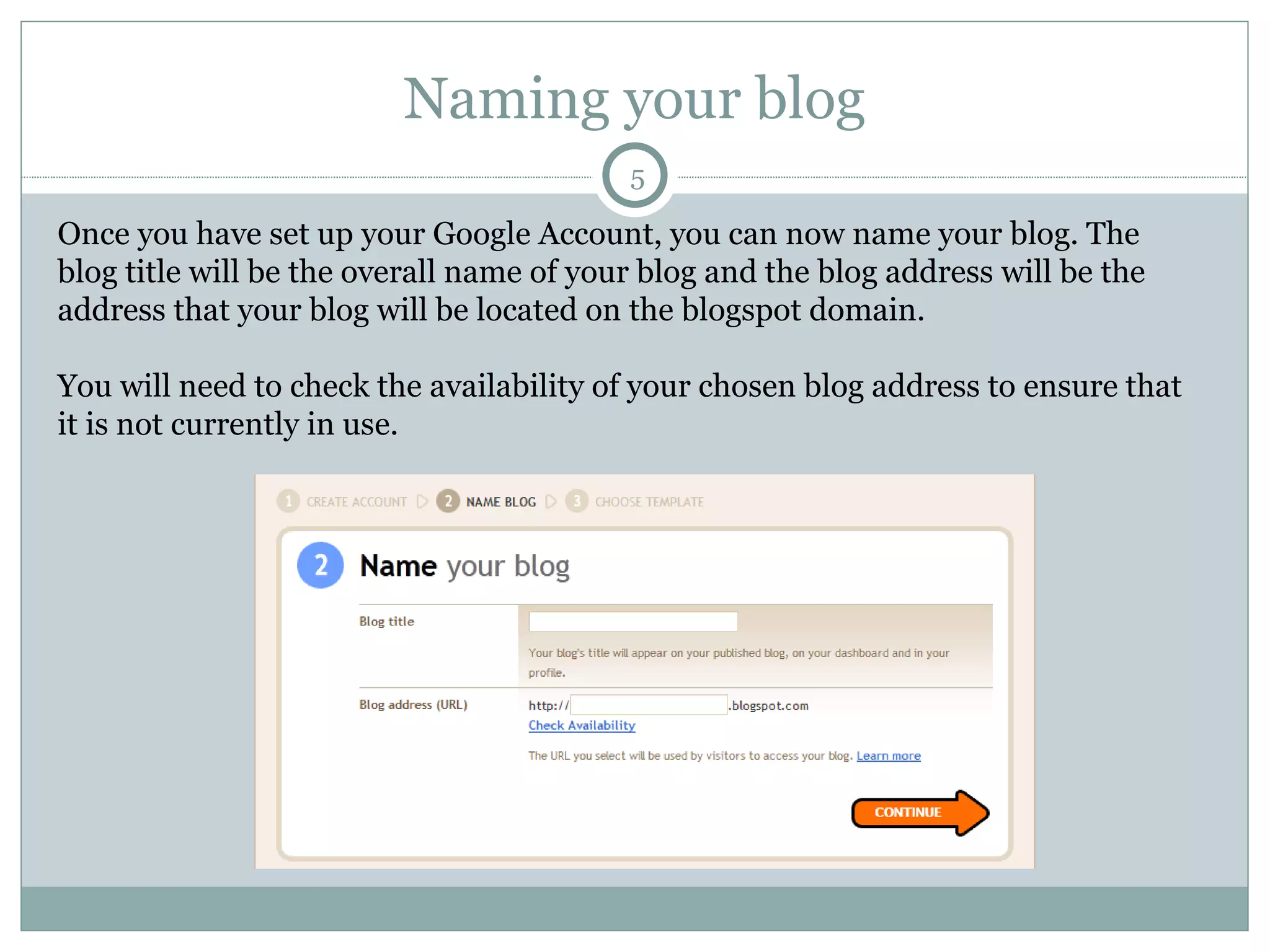
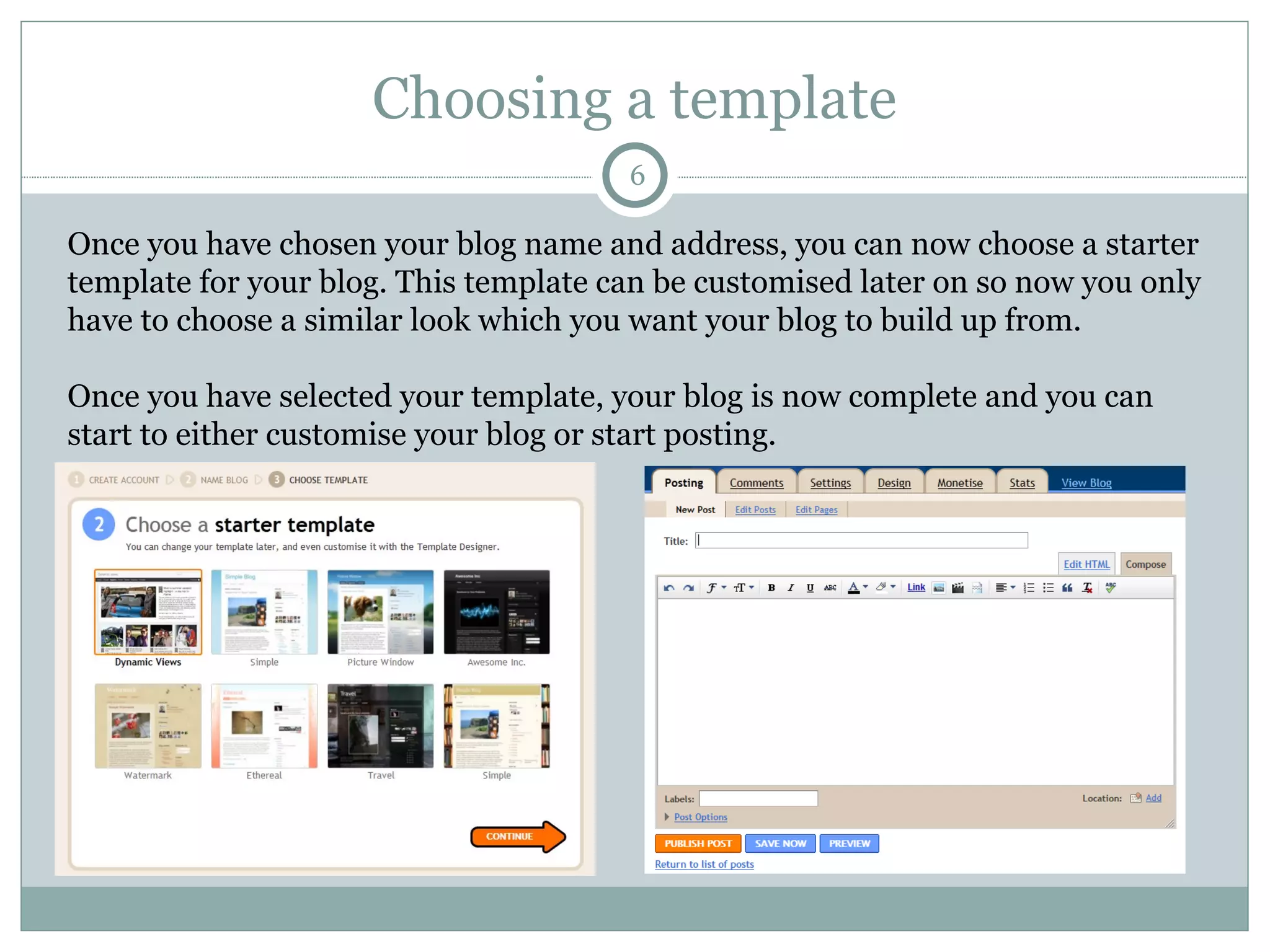
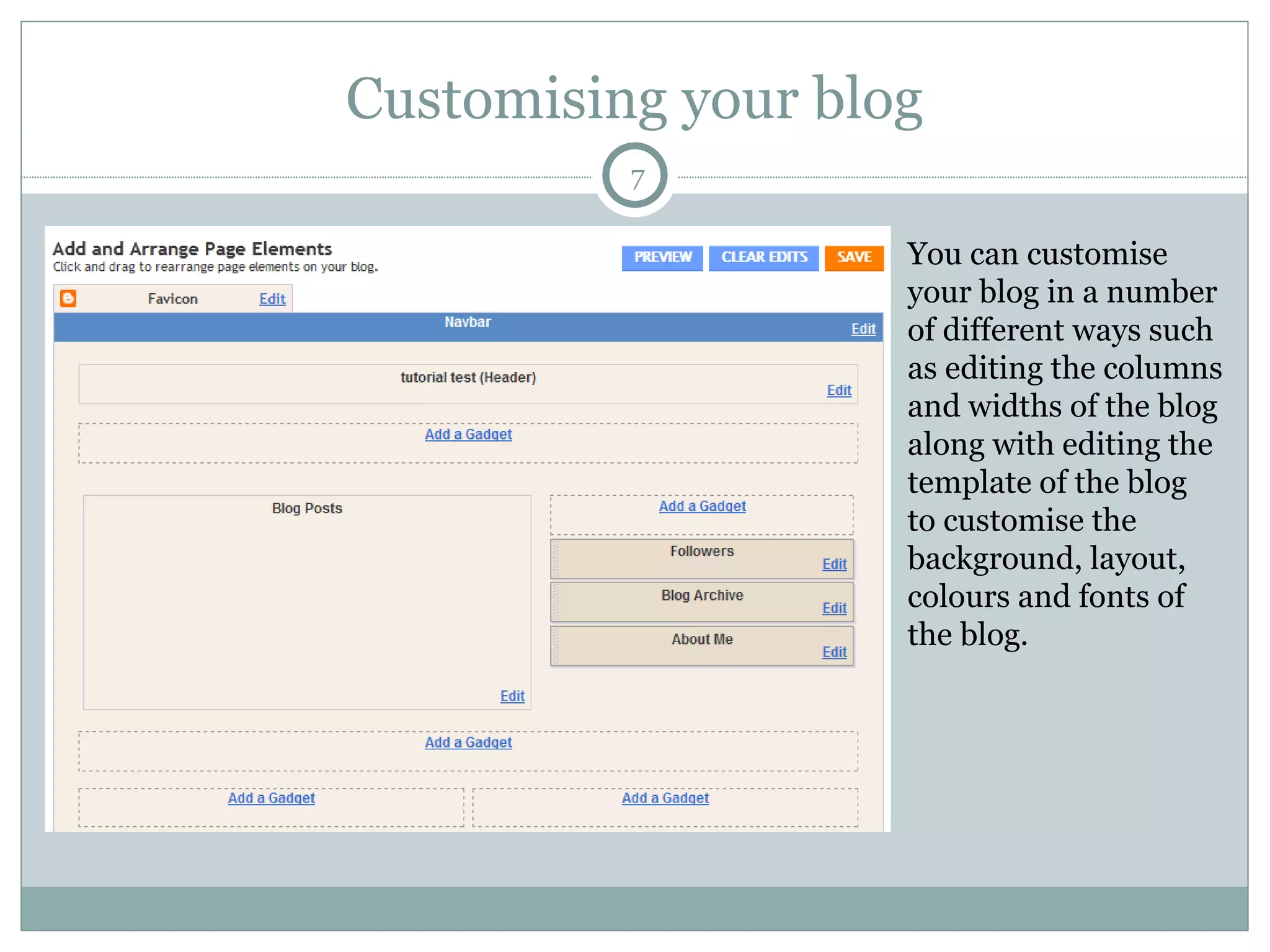
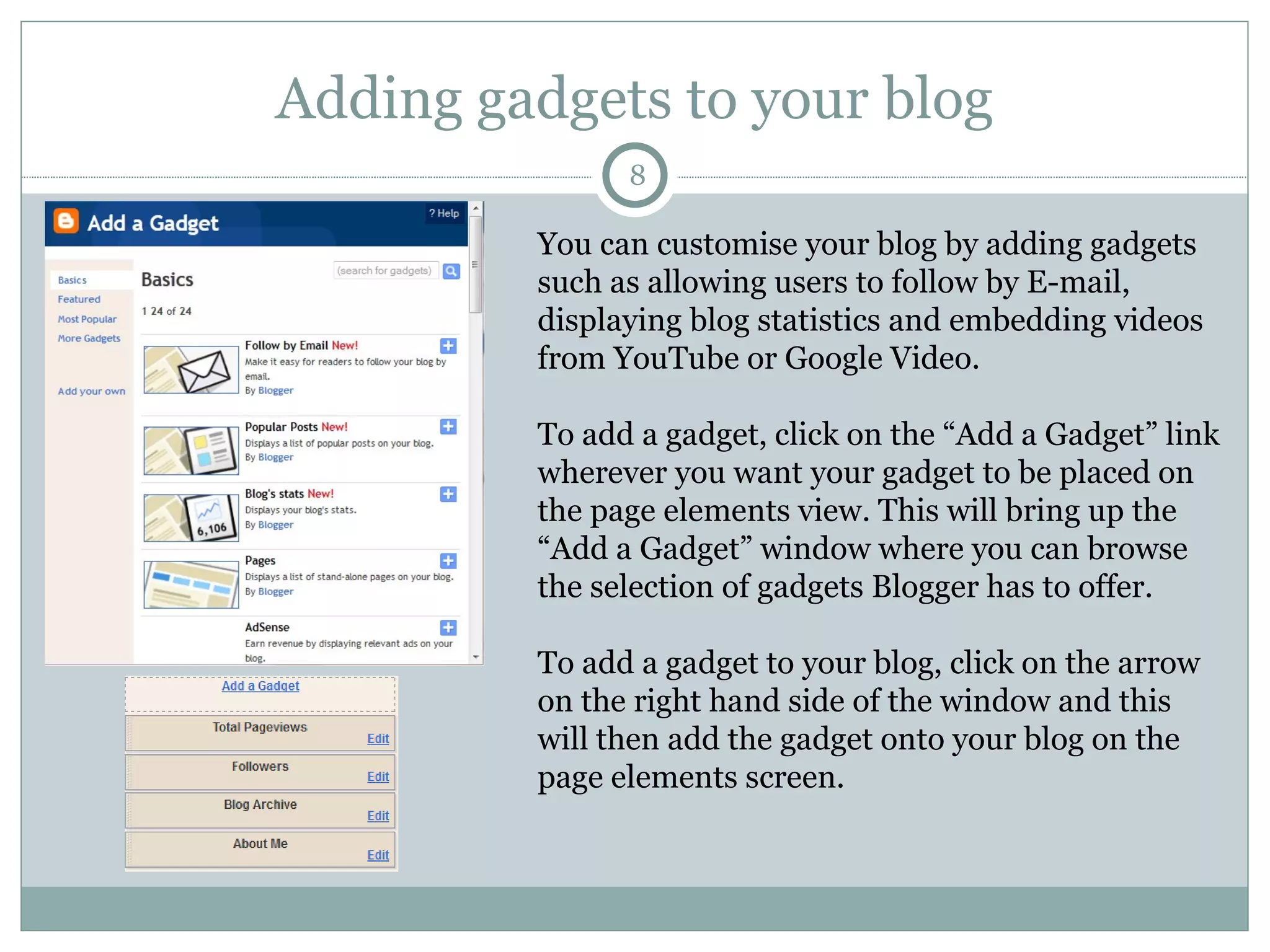
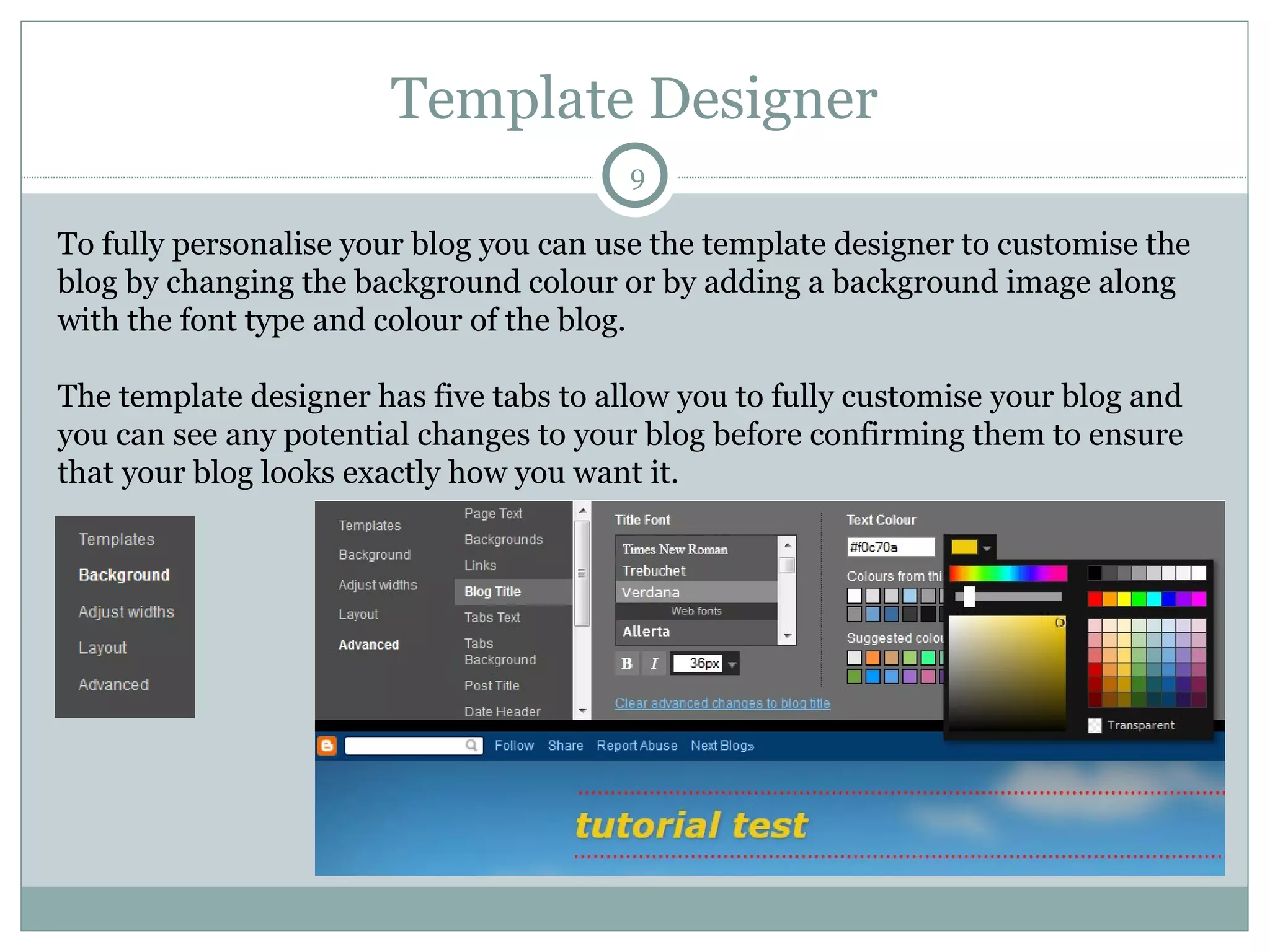
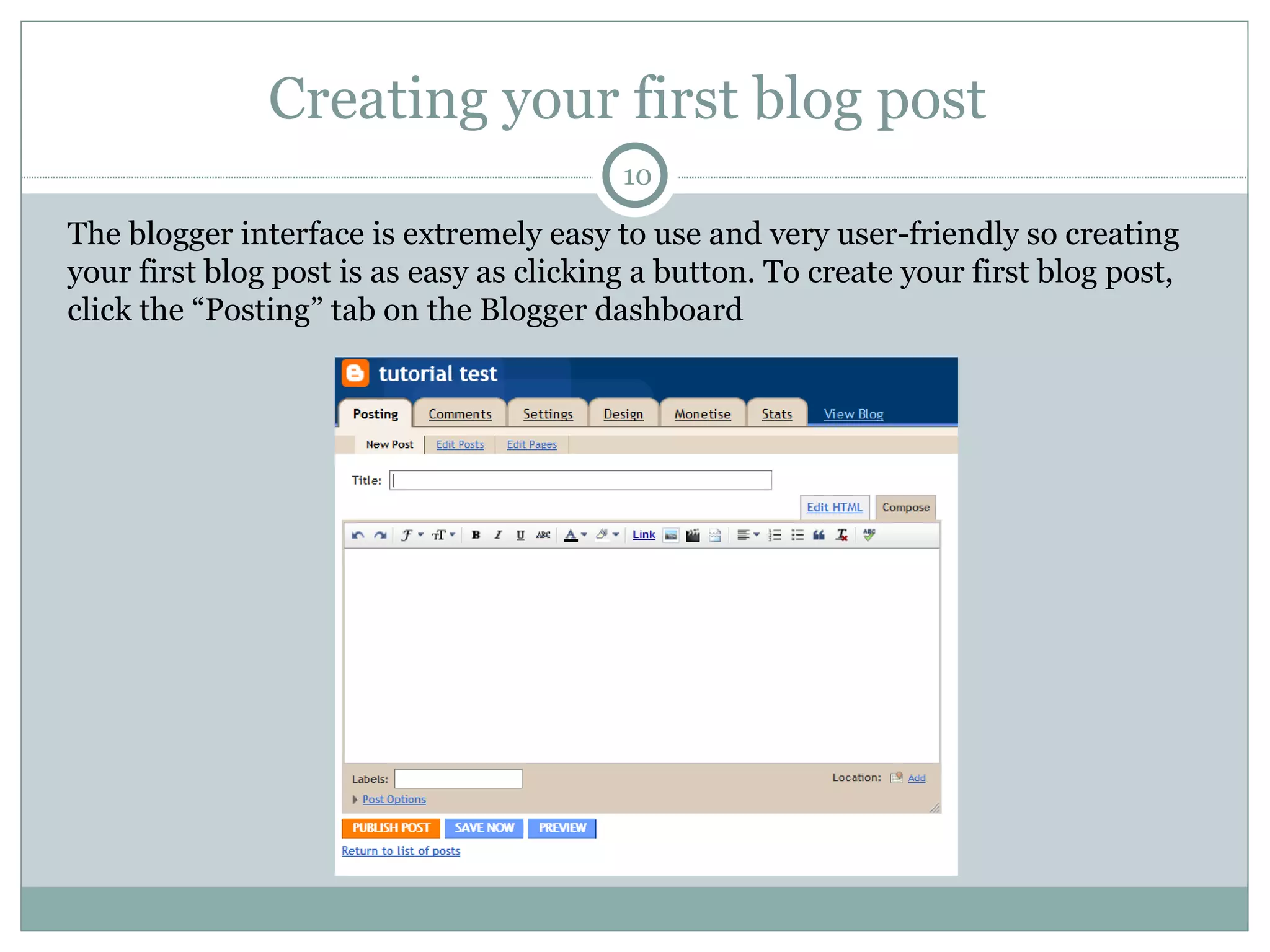
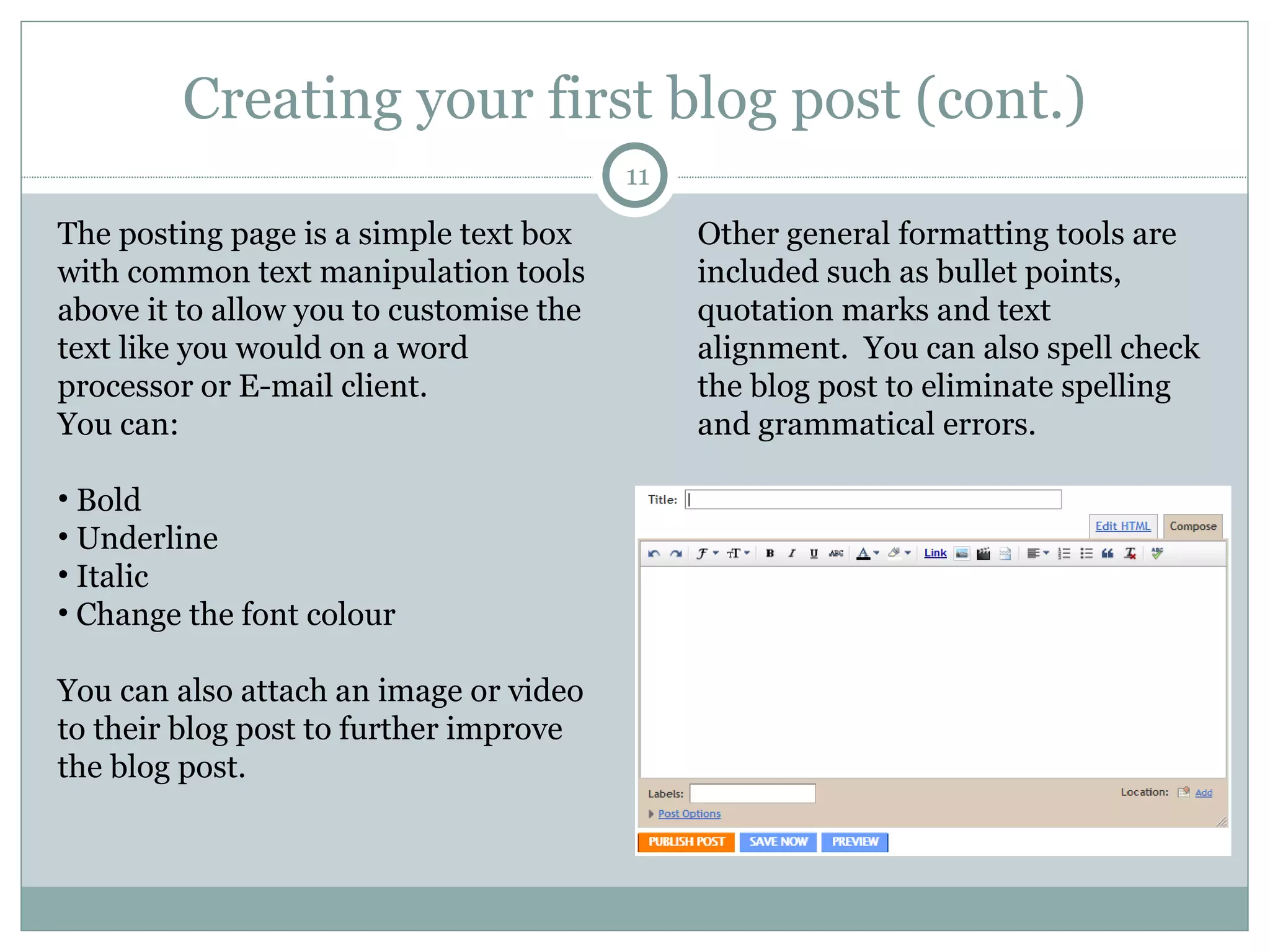
This tutorial shows how to set up a blog using Blogger. It covers signing up for an account, naming your blog, choosing a template, customizing the blog by editing colors and fonts, adding gadgets, using the template designer, and creating and publishing your first blog post. The tutorial provides step-by-step instructions on the entire process of setting up a blog on Blogger from start to finish.