Guardian Week 8 H4D Stanford 2016
•Download as PPTX, PDF•
1 like•37,052 views
agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Report
Share
Report
Share
Recommended
Skynet Week 2 H4D Stanford 2016

agile, business model, corporate innovation, customer development, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank, bmnt, diux
Sentinel Week 3 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Narrative Mind Week 8 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Skynet Week 5 H4D Stanford 2016

agile, bent, business model, corporate innovation, customer development,dod,nsa,diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Skynet Week 4 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, socomm, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Skynet Lessons Learned H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, dod, h4d, hacking for defense, lean, lean launchpad, lean startup, nsa, stanford, steve blank
Guardian Week 7 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, dod, h4d, hacking for defense, lean, lean launchpad, lean startup, nsa, stanford, steve blank
Aqualink Week 2 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Recommended
Skynet Week 2 H4D Stanford 2016

agile, business model, corporate innovation, customer development, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank, bmnt, diux
Sentinel Week 3 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Narrative Mind Week 8 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Skynet Week 5 H4D Stanford 2016

agile, bent, business model, corporate innovation, customer development,dod,nsa,diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Skynet Week 4 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, socomm, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Skynet Lessons Learned H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, dod, h4d, hacking for defense, lean, lean launchpad, lean startup, nsa, stanford, steve blank
Guardian Week 7 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, dod, h4d, hacking for defense, lean, lean launchpad, lean startup, nsa, stanford, steve blank
Aqualink Week 2 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Skynet Week 9 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Narrative Mind Week 4 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, socomm, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Guardian Week 5 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Sentinel Week 7 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Aqualink Week 1 H4D Stanford 2016

agile, business model, corporate innovation, customer development, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Guardian Lessons Learned H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, dod, h4d, hacking for defense, lean, lean launchpad, lean startup, nsa, stanford, steve blank
Austra Lumina Hacking for Defense 2017

mission model, mission model canvas, customer development, Hacking for Defense, lean startup, stanford, startup, steve blank, Pete Newell, Joe Felter, minimum viable product
aquaLink Week 3 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Right of Boom Week 7 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Skynet Week 8 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Capella Space Week 7 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Sentinel Week 2 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Narrative Mind Lessons Learned H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, dod, h4d, hacking for defense, lean, lean launchpad, lean startup, nsa, stanford, steve blank
Guardian Week 3 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Narrative Mind Week 6 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Guardian Week 6 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Narrative Mind Week 5 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Guardian Week 9 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Sentinel Lessons Learned H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, dod, h4d, hacking for defense, lean, lean launchpad, lean startup, nsa, stanford, steve blank
Skynet Week 1 H4D Stanford 2016

agile, business model, corporate innovation, customer development, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Guardian Week 2 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
More Related Content
What's hot
Skynet Week 9 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Narrative Mind Week 4 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, socomm, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Guardian Week 5 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Sentinel Week 7 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Aqualink Week 1 H4D Stanford 2016

agile, business model, corporate innovation, customer development, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Guardian Lessons Learned H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, dod, h4d, hacking for defense, lean, lean launchpad, lean startup, nsa, stanford, steve blank
Austra Lumina Hacking for Defense 2017

mission model, mission model canvas, customer development, Hacking for Defense, lean startup, stanford, startup, steve blank, Pete Newell, Joe Felter, minimum viable product
aquaLink Week 3 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Right of Boom Week 7 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Skynet Week 8 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Capella Space Week 7 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Sentinel Week 2 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Narrative Mind Lessons Learned H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, dod, h4d, hacking for defense, lean, lean launchpad, lean startup, nsa, stanford, steve blank
Guardian Week 3 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Narrative Mind Week 6 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Guardian Week 6 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Narrative Mind Week 5 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Guardian Week 9 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Sentinel Lessons Learned H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, dod, h4d, hacking for defense, lean, lean launchpad, lean startup, nsa, stanford, steve blank
Skynet Week 1 H4D Stanford 2016

agile, business model, corporate innovation, customer development, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
What's hot (20)
Similar to Guardian Week 8 H4D Stanford 2016
Guardian Week 2 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Skynet Week 3 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Guardian Week 4 H4D Stanford 2016

agile, bmnt, business model, corporate innovation, customer development,dod,nsa, diux, h4d, hacking for defense, lean, lean launchpad, lean startup, stanford, steve blank
Advanced Malware Analysis Training Session 8 - Introduction to Android

This presentation is part of our Advanced Malware Analysis Training Series program.
For more details refer our Security Training page
http://securityxploded.com/security-training-advanced-malware-analysis.php
Tech Throwdown: Secure Containerization vs Whitelisting

To address the inadequacy of traditional anti-virus solutions, white-listing and secure containerization approaches have both gained traction in the enterprise. Both approaches have the overarching goal of preventing a successful breach at the endpoint, but each works differently and also focus on different parts of the cyber kill chain.
Invincea, a secure containerization solution, inoculates high-risk and Internet-facing applications against attack by running them in secure virtual containers, which have restricted access to the underlying host OS. This effectively removes the most common means of delivering the infection (see figure below). Any successful exploits of targeted applications (such as IE, Java, Flash, etc.), including by 0-day exploits, are kept safely in quarantine where additional forensic details may be uncovered.
Whitelisting attempts to prevent infections by allowing only certain known executables to run. This means whitelisting solutions will not see initial exploits; rather, whitelisting focuses on the next step beyond the exploit where many attacks then attempt to launch 2<sup>nd</sup> stage (malicious) executables with additional goals such as privilege escalation, lateral movement, or data exfiltration. In other words, whitelisting solutions do not have visibility into exploits of existing programs and for memory-resident malware. In addition, whitelisting solutions that prevent unknown software from running will flag legitimate software (such as patches) that are not updated with the whitelist.
Drone Guardian: Countering the drone threat to commercial airports

L3 Technologies is currently live trailing its pioneering Drone Guardian technology in both commercial and non-commercial settings. Our whitepaper explores the risk factors associated with drones at commercial airports and considers how a flexible and scalable system such as Drone Guardian can be deployed to counter an ever-growing threat from the illegal and hostile use of both commercial and military drones.
MIT Bitcoin Expo 2018 - Hardware Wallets Security

Presentation at MIT Bitcoin Expo on 2018-19-03.
State of the Art Hardware Attacks.
https://youtu.be/ZmVzRmBVzWk?t=2h59m43s
Automated Cloud-Native Incident Response with Kubernetes and Service Mesh

Security incident response is a well-understood operation, with established best practices like the MITRE Att&ck Framework and the Lockheed Martin Kill Chain.
Tooling to aid and automate incident response exists, but not all of it is applicable to cloud-native platforms. For example, playbook apps are generally applicable, but the steps to move compromised workloads to an isolated forensics network are platform-specific, and new implementations are needed for the cloud-native world.
In this talk, Matt and Francesco will
* Recap incident response 101
* Introduce some cloud-native tech including Kubernetes, Istio, and GitOps
* Show an Operator built by Matt for dynamically adding complex layer-7 traffic rules in response to changes in the environment, which will be used as part of the demo
* Walk you through a response to a log4shell attack against a workload in a k8s cluster: sensor alert, SIEM analysis, IRP automation (honeypots, isolation), building the IoC, and killing the attack.
Adversary Emulation using CALDERA

Presentation that describes how CALDERA can be used for automated adversary emulation.
DRONES THE NEW WEAPON OF CHOICE - ALSO FOR HACKERS

My talk will be about drone threats in general and how you can assess drone based threats. I will show the comprehensive threat assessment methodology and the countermeasures you can take against the drone threat. The threat assessment is based on a catalog of about 140 items. Particularly interesting will be looking at the drone threats in relation to:
Planting payload at specific locations (i.e. hacking equipment transported to target location for instance)
Tampering communication equipment with the help of drones
Insider threat communicate with an insider with the help of a drone
Hacking the communication of a drone
Privacy violations
etc.
Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.

Simon Wong and Chris Cram, Scalar security experts, discuss how Palo Alto Networks technology disrupts the entire malware kill chain. Attendees will also gain insight on flexible deployment options to better serve their mobile users, and how to get the most out of their Palo Alto Networks deployment.
The Need for Drone Forensic Investigation Standardisation (Evangelos Mantas) ...

Evangelos Mantas (Infili Intelligence)
Talk Recording: https://www.youtube.com/watch?v=W0ZNpj7QZtM
The Global Drone Security Network (GDSN) is the only event of its kind focusing on Cyber-UAV security, Drone Threat Intelligence, Counter-UAS, and UTM security. Watch the full recording here: https://www.youtube.com/watch?v=vZ6sRr65cSk
Speaker: https://www.linkedin.com/in/evangelos-mantas-0aa82619a/
DroneSec is a cyber-uav security and threat intelligence company who hosted this second series of the GDSN community event.
https://dronesec.com/
Advanced malware analysis training session8 introduction to android

Advanced malware analysis training session8 introduction to android
Cyber Security Threat Modeling

This presentation provides overview about the different threat modeling approach with examples from Automotive. This presentation was given in IEEE VTS Event on 4 Sep - "Safe and Secure Automotive" Workshop
Automotive Cybersecurity: Test Like a Hacker

Learn the techniques used by award-winning hacking teams (as well as in some real-world attacks) to identify and exploit vulnerabilities in OEM components and other automotive software. This presentation covers fundamental principles, as well as how to easily incorporate these techniques into unit or functional test stages - bringing an extra layer of protection to connected automobiles. We'll cover both how to best fit this type of testing into your pipeline to maximize speed and coverage, as well as discuss how to fit this offensive cyber security approach alongside your existing vulnerability scanning programs. Whether you're a vehicle manufacturer, integrator, or OEM - we'll discuss how to leverage hacking-based security techniques to improve protection across the supply chain and keep vehicles and drivers safer. What we'll cover:
- Successful exploits of components and vehicles - what these attacks had in common
- Layering offensive techniques atop existing security programs - what to do and what to avoid
- How to test integrated systems with multiple components from different OEMs working in tandem
- Integrating offensive testing into different stages in software development and component integration
Originally presented at https://www.automotive-iq.com/events-automotive-cybersecurity
Similar to Guardian Week 8 H4D Stanford 2016 (20)
Advanced Malware Analysis Training Session 8 - Introduction to Android

Advanced Malware Analysis Training Session 8 - Introduction to Android
Tech Throwdown: Secure Containerization vs Whitelisting

Tech Throwdown: Secure Containerization vs Whitelisting
Drone Guardian: Countering the drone threat to commercial airports

Drone Guardian: Countering the drone threat to commercial airports
Automated Cloud-Native Incident Response with Kubernetes and Service Mesh

Automated Cloud-Native Incident Response with Kubernetes and Service Mesh
DRONES THE NEW WEAPON OF CHOICE - ALSO FOR HACKERS

DRONES THE NEW WEAPON OF CHOICE - ALSO FOR HACKERS
Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.

Disrupting the Malware Kill Chain - What's New from Palo Alto Networks.
The Need for Drone Forensic Investigation Standardisation (Evangelos Mantas) ...

The Need for Drone Forensic Investigation Standardisation (Evangelos Mantas) ...
Advanced malware analysis training session8 introduction to android

Advanced malware analysis training session8 introduction to android
More from Stanford University
Team Networks - 2022 Technology, Innovation & Great Power Competition

Technology Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, networks
Team LiOn Batteries - 2022 Technology, Innovation & Great Power Competition

Technology Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, LiOn Batteries
Team Quantum - 2022 Technology, Innovation & Great Power Competition

Technology Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, Quantum
Team Disinformation - 2022 Technology, Innovation & Great Power Competition

Technology Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, Disinformation
Team Wargames - 2022 Technology, Innovation & Great Power Competition

Technology Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, Wargames
Team Acquistion - 2022 Technology, Innovation & Great Power Competition 

Technology Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, Acquistion
Team Climate Change - 2022 Technology, Innovation & Great Power Competition 

Technology Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, climate
Gordian Knot Center Roundtable w/Depty SecDef 

Kathleen Hicks - Deputy secretary of defense- visit to the Stanford Gordian Knot Center for National Security Innovation
Team Army venture capital - 2021 Technology, Innovation & Great Power Competi...

Technology, Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, unmanned, autonomy, Army venture capital
Team Army venture capital - 2021 Technology, Innovation & Great Power Competi...

Technology, Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve Blank, Army Venture capital
Team Catena - 2021 Technology, Innovation & Great Power Competition

Technology, Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, unmanned, autonomy, economic coercion,
Team Apollo - 2021 Technology, Innovation & Great Power Competition

Technology, Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, unmanned, autonomy, space force
Team Drone - 2021 Technology, Innovation & Great Power Competition

Technology, Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, unmanned, autonomy, c3i, command and control
Team Short Circuit - 2021 Technology, Innovation & Great Power Competition

Technology, Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, unmanned, autonomy, semiconductors
Team Aurora - 2021 Technology, Innovation & Great Power Competition

Technology, Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, unmanned, autonomy, Army venture capital
Team Conflicted Capital Team - 2021 Technology, Innovation & Great Power Comp...

Technology, Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, unmanned, autonomy, venture capital
Lecture 8 - Technology, Innovation and Great Power Competition - Cyber

Technology, Innovation and Great Power Competition,TIGPC, Gordian knot Center, DIME-FIL, department of defense, dod, hacking for defense, intlpol 340, joe felter, ms&e296, raj shah, stanford, Steve blank, AI, ML, AI/ML, china, unmanned, autonomy, Michael Sulmeyer, cybercom,USCYBERCOM
More from Stanford University (20)
Team Networks - 2022 Technology, Innovation & Great Power Competition

Team Networks - 2022 Technology, Innovation & Great Power Competition
Team LiOn Batteries - 2022 Technology, Innovation & Great Power Competition

Team LiOn Batteries - 2022 Technology, Innovation & Great Power Competition
Team Quantum - 2022 Technology, Innovation & Great Power Competition

Team Quantum - 2022 Technology, Innovation & Great Power Competition
Team Disinformation - 2022 Technology, Innovation & Great Power Competition

Team Disinformation - 2022 Technology, Innovation & Great Power Competition
Team Wargames - 2022 Technology, Innovation & Great Power Competition

Team Wargames - 2022 Technology, Innovation & Great Power Competition
Team Acquistion - 2022 Technology, Innovation & Great Power Competition 

Team Acquistion - 2022 Technology, Innovation & Great Power Competition
Team Climate Change - 2022 Technology, Innovation & Great Power Competition 

Team Climate Change - 2022 Technology, Innovation & Great Power Competition
Team Army venture capital - 2021 Technology, Innovation & Great Power Competi...

Team Army venture capital - 2021 Technology, Innovation & Great Power Competi...
Team Army venture capital - 2021 Technology, Innovation & Great Power Competi...

Team Army venture capital - 2021 Technology, Innovation & Great Power Competi...
Team Catena - 2021 Technology, Innovation & Great Power Competition

Team Catena - 2021 Technology, Innovation & Great Power Competition
Team Apollo - 2021 Technology, Innovation & Great Power Competition

Team Apollo - 2021 Technology, Innovation & Great Power Competition
Team Drone - 2021 Technology, Innovation & Great Power Competition

Team Drone - 2021 Technology, Innovation & Great Power Competition
Team Short Circuit - 2021 Technology, Innovation & Great Power Competition

Team Short Circuit - 2021 Technology, Innovation & Great Power Competition
Team Aurora - 2021 Technology, Innovation & Great Power Competition

Team Aurora - 2021 Technology, Innovation & Great Power Competition
Team Conflicted Capital Team - 2021 Technology, Innovation & Great Power Comp...

Team Conflicted Capital Team - 2021 Technology, Innovation & Great Power Comp...
Lecture 8 - Technology, Innovation and Great Power Competition - Cyber

Lecture 8 - Technology, Innovation and Great Power Competition - Cyber
Recently uploaded
June 3, 2024 Anti-Semitism Letter Sent to MIT President Kornbluth and MIT Cor...

Letter from the Congress of the United States regarding Anti-Semitism sent June 3rd to MIT President Sally Kornbluth, MIT Corp Chair, Mark Gorenberg
Dear Dr. Kornbluth and Mr. Gorenberg,
The US House of Representatives is deeply concerned by ongoing and pervasive acts of antisemitic
harassment and intimidation at the Massachusetts Institute of Technology (MIT). Failing to act decisively to ensure a safe learning environment for all students would be a grave dereliction of your responsibilities as President of MIT and Chair of the MIT Corporation.
This Congress will not stand idly by and allow an environment hostile to Jewish students to persist. The House believes that your institution is in violation of Title VI of the Civil Rights Act, and the inability or
unwillingness to rectify this violation through action requires accountability.
Postsecondary education is a unique opportunity for students to learn and have their ideas and beliefs challenged. However, universities receiving hundreds of millions of federal funds annually have denied
students that opportunity and have been hijacked to become venues for the promotion of terrorism, antisemitic harassment and intimidation, unlawful encampments, and in some cases, assaults and riots.
The House of Representatives will not countenance the use of federal funds to indoctrinate students into hateful, antisemitic, anti-American supporters of terrorism. Investigations into campus antisemitism by the Committee on Education and the Workforce and the Committee on Ways and Means have been expanded into a Congress-wide probe across all relevant jurisdictions to address this national crisis. The undersigned Committees will conduct oversight into the use of federal funds at MIT and its learning environment under authorities granted to each Committee.
• The Committee on Education and the Workforce has been investigating your institution since December 7, 2023. The Committee has broad jurisdiction over postsecondary education, including its compliance with Title VI of the Civil Rights Act, campus safety concerns over disruptions to the learning environment, and the awarding of federal student aid under the Higher Education Act.
• The Committee on Oversight and Accountability is investigating the sources of funding and other support flowing to groups espousing pro-Hamas propaganda and engaged in antisemitic harassment and intimidation of students. The Committee on Oversight and Accountability is the principal oversight committee of the US House of Representatives and has broad authority to investigate “any matter” at “any time” under House Rule X.
• The Committee on Ways and Means has been investigating several universities since November 15, 2023, when the Committee held a hearing entitled From Ivory Towers to Dark Corners: Investigating the Nexus Between Antisemitism, Tax-Exempt Universities, and Terror Financing. The Committee followed the hearing with letters to those institutions on January 10, 202
Mule 4.6 & Java 17 Upgrade | MuleSoft Mysore Meetup #46

Mule 4.6 & Java 17 Upgrade | MuleSoft Mysore Meetup #46
Event Link:-
https://meetups.mulesoft.com/events/details/mulesoft-mysore-presents-exploring-gemini-ai-and-integration-with-mulesoft/
Agenda
● Java 17 Upgrade Overview
● Why and by when do customers need to upgrade to Java 17?
● Is there any immediate impact to upgrading to Mule Runtime 4.6 and beyond?
● Which MuleSoft products are in scope?
For Upcoming Meetups Join Mysore Meetup Group - https://meetups.mulesoft.com/mysore/
YouTube:- youtube.com/@mulesoftmysore
Mysore WhatsApp group:- https://chat.whatsapp.com/EhqtHtCC75vCAX7gaO842N
Speaker:-
Shubham Chaurasia - https://www.linkedin.com/in/shubhamchaurasia1/
Priya Shaw - https://www.linkedin.com/in/priya-shaw
Organizers:-
Shubham Chaurasia - https://www.linkedin.com/in/shubhamchaurasia1/
Giridhar Meka - https://www.linkedin.com/in/giridharmeka
Priya Shaw - https://www.linkedin.com/in/priya-shaw
Shyam Raj Prasad-
https://www.linkedin.com/in/shyam-raj-prasad/
Embracing GenAI - A Strategic Imperative

Artificial Intelligence (AI) technologies such as Generative AI, Image Generators and Large Language Models have had a dramatic impact on teaching, learning and assessment over the past 18 months. The most immediate threat AI posed was to Academic Integrity with Higher Education Institutes (HEIs) focusing their efforts on combating the use of GenAI in assessment. Guidelines were developed for staff and students, policies put in place too. Innovative educators have forged paths in the use of Generative AI for teaching, learning and assessments leading to pockets of transformation springing up across HEIs, often with little or no top-down guidance, support or direction.
This Gasta posits a strategic approach to integrating AI into HEIs to prepare staff, students and the curriculum for an evolving world and workplace. We will highlight the advantages of working with these technologies beyond the realm of teaching, learning and assessment by considering prompt engineering skills, industry impact, curriculum changes, and the need for staff upskilling. In contrast, not engaging strategically with Generative AI poses risks, including falling behind peers, missed opportunities and failing to ensure our graduates remain employable. The rapid evolution of AI technologies necessitates a proactive and strategic approach if we are to remain relevant.
Introduction to AI for Nonprofits with Tapp Network

Dive into the world of AI! Experts Jon Hill and Tareq Monaur will guide you through AI's role in enhancing nonprofit websites and basic marketing strategies, making it easy to understand and apply.
CACJapan - GROUP Presentation 1- Wk 4.pdf

Macroeconomics- Movie Location
This will be used as part of your Personal Professional Portfolio once graded.
Objective:
Prepare a presentation or a paper using research, basic comparative analysis, data organization and application of economic information. You will make an informed assessment of an economic climate outside of the United States to accomplish an entertainment industry objective.
678020731-Sumas-y-Restas-Para-Colorear.pdf

KKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKKK
The approach at University of Liverpool.pptx

How libraries can support authors with open access requirements for UKRI funded books
Wednesday 22 May 2024, 14:00-15:00.
Home assignment II on Spectroscopy 2024 Answers.pdf

Answers to Home assignment on UV-Visible spectroscopy: Calculation of wavelength of UV-Visible absorption
The Roman Empire A Historical Colossus.pdf

The Roman Empire, a vast and enduring power, stands as one of history's most remarkable civilizations, leaving an indelible imprint on the world. It emerged from the Roman Republic, transitioning into an imperial powerhouse under the leadership of Augustus Caesar in 27 BCE. This transformation marked the beginning of an era defined by unprecedented territorial expansion, architectural marvels, and profound cultural influence.
The empire's roots lie in the city of Rome, founded, according to legend, by Romulus in 753 BCE. Over centuries, Rome evolved from a small settlement to a formidable republic, characterized by a complex political system with elected officials and checks on power. However, internal strife, class conflicts, and military ambitions paved the way for the end of the Republic. Julius Caesar’s dictatorship and subsequent assassination in 44 BCE created a power vacuum, leading to a civil war. Octavian, later Augustus, emerged victorious, heralding the Roman Empire’s birth.
Under Augustus, the empire experienced the Pax Romana, a 200-year period of relative peace and stability. Augustus reformed the military, established efficient administrative systems, and initiated grand construction projects. The empire's borders expanded, encompassing territories from Britain to Egypt and from Spain to the Euphrates. Roman legions, renowned for their discipline and engineering prowess, secured and maintained these vast territories, building roads, fortifications, and cities that facilitated control and integration.
The Roman Empire’s society was hierarchical, with a rigid class system. At the top were the patricians, wealthy elites who held significant political power. Below them were the plebeians, free citizens with limited political influence, and the vast numbers of slaves who formed the backbone of the economy. The family unit was central, governed by the paterfamilias, the male head who held absolute authority.
Culturally, the Romans were eclectic, absorbing and adapting elements from the civilizations they encountered, particularly the Greeks. Roman art, literature, and philosophy reflected this synthesis, creating a rich cultural tapestry. Latin, the Roman language, became the lingua franca of the Western world, influencing numerous modern languages.
Roman architecture and engineering achievements were monumental. They perfected the arch, vault, and dome, constructing enduring structures like the Colosseum, Pantheon, and aqueducts. These engineering marvels not only showcased Roman ingenuity but also served practical purposes, from public entertainment to water supply.
Digital Tools and AI for Teaching Learning and Research

This Presentation in details discusses on Digital Tools and AI for Teaching Learning and Research
A Strategic Approach: GenAI in Education

Artificial Intelligence (AI) technologies such as Generative AI, Image Generators and Large Language Models have had a dramatic impact on teaching, learning and assessment over the past 18 months. The most immediate threat AI posed was to Academic Integrity with Higher Education Institutes (HEIs) focusing their efforts on combating the use of GenAI in assessment. Guidelines were developed for staff and students, policies put in place too. Innovative educators have forged paths in the use of Generative AI for teaching, learning and assessments leading to pockets of transformation springing up across HEIs, often with little or no top-down guidance, support or direction.
This Gasta posits a strategic approach to integrating AI into HEIs to prepare staff, students and the curriculum for an evolving world and workplace. We will highlight the advantages of working with these technologies beyond the realm of teaching, learning and assessment by considering prompt engineering skills, industry impact, curriculum changes, and the need for staff upskilling. In contrast, not engaging strategically with Generative AI poses risks, including falling behind peers, missed opportunities and failing to ensure our graduates remain employable. The rapid evolution of AI technologies necessitates a proactive and strategic approach if we are to remain relevant.
2024.06.01 Introducing a competency framework for languag learning materials ...

http://sandymillin.wordpress.com/iateflwebinar2024
Published classroom materials form the basis of syllabuses, drive teacher professional development, and have a potentially huge influence on learners, teachers and education systems. All teachers also create their own materials, whether a few sentences on a blackboard, a highly-structured fully-realised online course, or anything in between. Despite this, the knowledge and skills needed to create effective language learning materials are rarely part of teacher training, and are mostly learnt by trial and error.
Knowledge and skills frameworks, generally called competency frameworks, for ELT teachers, trainers and managers have existed for a few years now. However, until I created one for my MA dissertation, there wasn’t one drawing together what we need to know and do to be able to effectively produce language learning materials.
This webinar will introduce you to my framework, highlighting the key competencies I identified from my research. It will also show how anybody involved in language teaching (any language, not just English!), teacher training, managing schools or developing language learning materials can benefit from using the framework.
How libraries can support authors with open access requirements for UKRI fund...

How libraries can support authors with open access requirements for UKRI funded books
Wednesday 22 May 2024, 14:00-15:00.
Unit 2- Research Aptitude (UGC NET Paper I).pdf

This slide describes the research aptitude of unit 2 in the UGC NET paper I.
Acetabularia Information For Class 9 .docx

Acetabularia acetabulum is a single-celled green alga that in its vegetative state is morphologically differentiated into a basal rhizoid and an axially elongated stalk, which bears whorls of branching hairs. The single diploid nucleus resides in the rhizoid.
Welcome to TechSoup New Member Orientation and Q&A (May 2024).pdf

In this webinar you will learn how your organization can access TechSoup's wide variety of product discount and donation programs. From hardware to software, we'll give you a tour of the tools available to help your nonprofit with productivity, collaboration, financial management, donor tracking, security, and more.
How to Make a Field invisible in Odoo 17

It is possible to hide or invisible some fields in odoo. Commonly using “invisible” attribute in the field definition to invisible the fields. This slide will show how to make a field invisible in odoo 17.
Synthetic Fiber Construction in lab .pptx

Synthetic fiber production is a fascinating and complex field that blends chemistry, engineering, and environmental science. By understanding these aspects, students can gain a comprehensive view of synthetic fiber production, its impact on society and the environment, and the potential for future innovations. Synthetic fibers play a crucial role in modern society, impacting various aspects of daily life, industry, and the environment. ynthetic fibers are integral to modern life, offering a range of benefits from cost-effectiveness and versatility to innovative applications and performance characteristics. While they pose environmental challenges, ongoing research and development aim to create more sustainable and eco-friendly alternatives. Understanding the importance of synthetic fibers helps in appreciating their role in the economy, industry, and daily life, while also emphasizing the need for sustainable practices and innovation.
Recently uploaded (20)
June 3, 2024 Anti-Semitism Letter Sent to MIT President Kornbluth and MIT Cor...

June 3, 2024 Anti-Semitism Letter Sent to MIT President Kornbluth and MIT Cor...
Mule 4.6 & Java 17 Upgrade | MuleSoft Mysore Meetup #46

Mule 4.6 & Java 17 Upgrade | MuleSoft Mysore Meetup #46
Introduction to AI for Nonprofits with Tapp Network

Introduction to AI for Nonprofits with Tapp Network
Home assignment II on Spectroscopy 2024 Answers.pdf

Home assignment II on Spectroscopy 2024 Answers.pdf
Digital Tools and AI for Teaching Learning and Research

Digital Tools and AI for Teaching Learning and Research
2024.06.01 Introducing a competency framework for languag learning materials ...

2024.06.01 Introducing a competency framework for languag learning materials ...
How libraries can support authors with open access requirements for UKRI fund...

How libraries can support authors with open access requirements for UKRI fund...
Welcome to TechSoup New Member Orientation and Q&A (May 2024).pdf

Welcome to TechSoup New Member Orientation and Q&A (May 2024).pdf
Guardian Week 8 H4D Stanford 2016
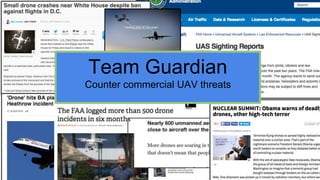
- 1. Team Guardian Counter commercial UAV threats
- 2. Team Guardian Protection against commercial off the shelf drones Number of Stakeholders Spoken to: 10 Total Number of Stakeholders Spoken to: 107 Activities last week: Prototyping sensing / classification system Feedback from buyers and users Project: Countering Asymmetric Drone Activities Military Liaisons: John and Scott Interview dashboard Week 8 Total to date Users 1 23 Buyers 5 37 Experts 4 47 Total 10 107
- 3. MVP: Classification and Threat Analysis Analyzing signals from multiple technologies Characteristics Action Manufacture: 3DR Model: SA11A Payload: camera Last seen: 7 days ago Warning in effects: non Threat level: low Keep tracking Manufacture: DJI Model: Phantom 3 Payload: non Last seen: 3 hours ago Warnings in effect: popular model Threat level: low Keep tracking Manufacturer: CyPhy's Model: LVL 1 Carries: unknown object Last seen: 2 week ago Warning in effect: known to be possessed by local terrorists group Threat level : High 1) Evacuate Facility 2) Activate counterme asure
- 4. Critical Activities Pre-prototype Post prototype Software development: ○ Training ○ Database formation Deployment: ○ Integration with existing systems ○ Operator training Hardware development: ○ Sensor communication ○ DSP Feature extraction Maintenance: ○ Update database ○ Technical support
- 5. Critical Resources Physical Financial Human Intellectual - Lab (San Francisco Bay Area) Pre-prototype: - Government grants (SBIR) - Angels Post-prototype: - VC - Corporate Partners - Engineering Team - Advisors from DoD (AWG) - Mentors / Board (senior US military / veterans) - Contract with DoD - Patents
- 6. Key Partners What critical partners do you need to fill gap in your resources? what is their equity in helping you? Partner Gap they fill Equity Sensor Manufactures Funding (pre-prototype) share in company VC Funding (post prototype) share in company AWG Connection with DoD / Advisors our product supports their mission achievement
- 7. Guardian: Mission Model Canvas Requirements Engineering Understanding of FOB scenarios and capability gaps - Concept definition System design - System and components engineering - Reverse engineering on commercial drones Pre-prototype: - Software development - Hardware development Post prototype: - Deployment - Maintenance - U.S. Army Asymmetric Warfare Group - REF - Ground forces - Commercial drone manufacturers (e.g. DJI) - Other agencies working on the same problem: - JIDA - DHS - CTTSO - I2WD (Intelligence and Information Warfare Directorate) - US Marine Corps - Other companies working on countermeasures and detection: - ELTA - Skyview - VERUS - Battelle - Blacksage Technologies FOBs: (1) ● Lieutenant/Captain in charge on FOB protection Private at guard tower (front line) ● Technician in Control Center Air Force personnel in control center surveilling the air space (2) Program Manager, concept generator, requirement writer in U.S Army Asymmetric Warfare Group (3) Countermeasure providers /manufacturer (alerting, jamming, kinetic) - Effective countering regardless of specific drone - Classify and counter reconnaissance - Bring drone down without crashing - Provide modular solution to escalate the situation proportionally to the threat (sequential) - Gain intelligence while mitigating threat - Scalability for swarms - Low training need, easy to use - Symmetric solution: costs of countering is symmetric to cost of attack - Geo-localizing operator Current focus: classification - identify type of drone, payload and potential threat: - Autonomous - Provides data essential for interception / jamming - Scalable (part of a large air- control system) - Provide counter-drone capabilities to FOBs within 2 years - Provide drone detection and threat assessment capabilities - Provide a platform for existing and future countermeasure - Demonstration day - Modification (based on testing results) - Prototype After initial contract: - Limited User Assessment - Train field operators Variable - Purchase equipment for testing including drones(DJI + Micro) - Purchase jamming equipment and power attenuators - Access to relevant ground forces to define relevant scenarios - U.S. Army Asymmetric Warfare Group to define relevant set of capabilities - Other agencies working on the same problem - Hardware to test Pre-prototype: - Lab - Initial Funding - Engineering Team - Patent - Advisors from DoD (AWG) Post prototype: - Partners - Contract Asymmetric Warfare Group using RDT&E (from REF): single contract from concept to deployment - SBIR - Military VC - IRAD - Angel Beneficiaries Mission Achievement Mission Budget/Costs Buy-In/Support Deployment Value PropositionKey Activities Key Resources Key Partners
- 8. Value Proposition Canvas Products & Services - Sensor fusion - Classification capabilities - Threat analysis system - Data from multiple sensing technologies Customer Jobs Provide UAV countermeasures (alerting, kinetic, jamming) - no existing localization capabilities - no existing classification capabilities - detection is inaccurate and unreliable - no existing automatic threat analysis Countermeasure Manufacturer Gains Pains Gain Creators Pain Relievers - Accurate real-time UAV location - Threat classification and characterization - Large and dynamic sensing range - Accurate location - Differentiation between UAV and other low-altitude flying objects - API - API for the following features: + tracking target + target information + threat analysis
- 9. Value Proposition Canvas Products & Services - Countering with basic training - Countering regardless of specific drone - Layered solution, countering multiple threats posed by commercial drones Customer Jobs Protect FOB: frontline protection responsible on a specific section - Threats( Reconnaisse, weaponized, swarms…) - No easy way to take down next gen UAVs - No existing solution tailored for off-the-shelf drone threat Private in guard tower Gains Pains Gain Creators Pain Relievers - Can react to threat with easy to use equipment - Can act rapidly and efficiently - Reduce mission irritation from drones - Mitigate threat - Minimal training, easy to use - Drone counter measure - Drone Classification
- 10. Value Proposition Canvas Products & Services -Countering without crashing - Highly autonomous system -Classification capability - Fast reaction period Customer Jobs Protect FOB - Surveillance - Unresolved threat Lieutenant/Captain Gains Pains Gain Creators Pain Relievers - Focus on mission without worrying about surveillance, or by spending less time on threats posed by commercial drones - Capturing the drone without crashing provides the opportunity to exploit the drone and trace back to origin for further mission - Reduce mission irritation from drones - Mitigate threat - Drone counter measure - Drone Classification
- 11. Value Proposition Canvas Products & Services Gain capability: 1. Countering drone without crashing and potentially exploiting data from it 2. Scalability: countering swarm of drones 3. Classification of drone threats 4. Solution can be deployed within 2 years Customer Jobs Bridge capability gaps in asymmetric warfare against for US forces - Unresolved emerging threat Asymmetric warfare group(Program Manager/Concept Generator/Requirement Writer…) Gains Pains Gain Creators Pain Relievers - Provide counter-drone capability to US forces -Fill in capability gaps between current technologies -Mitigate threat - Drone counter measure - Drone classification
