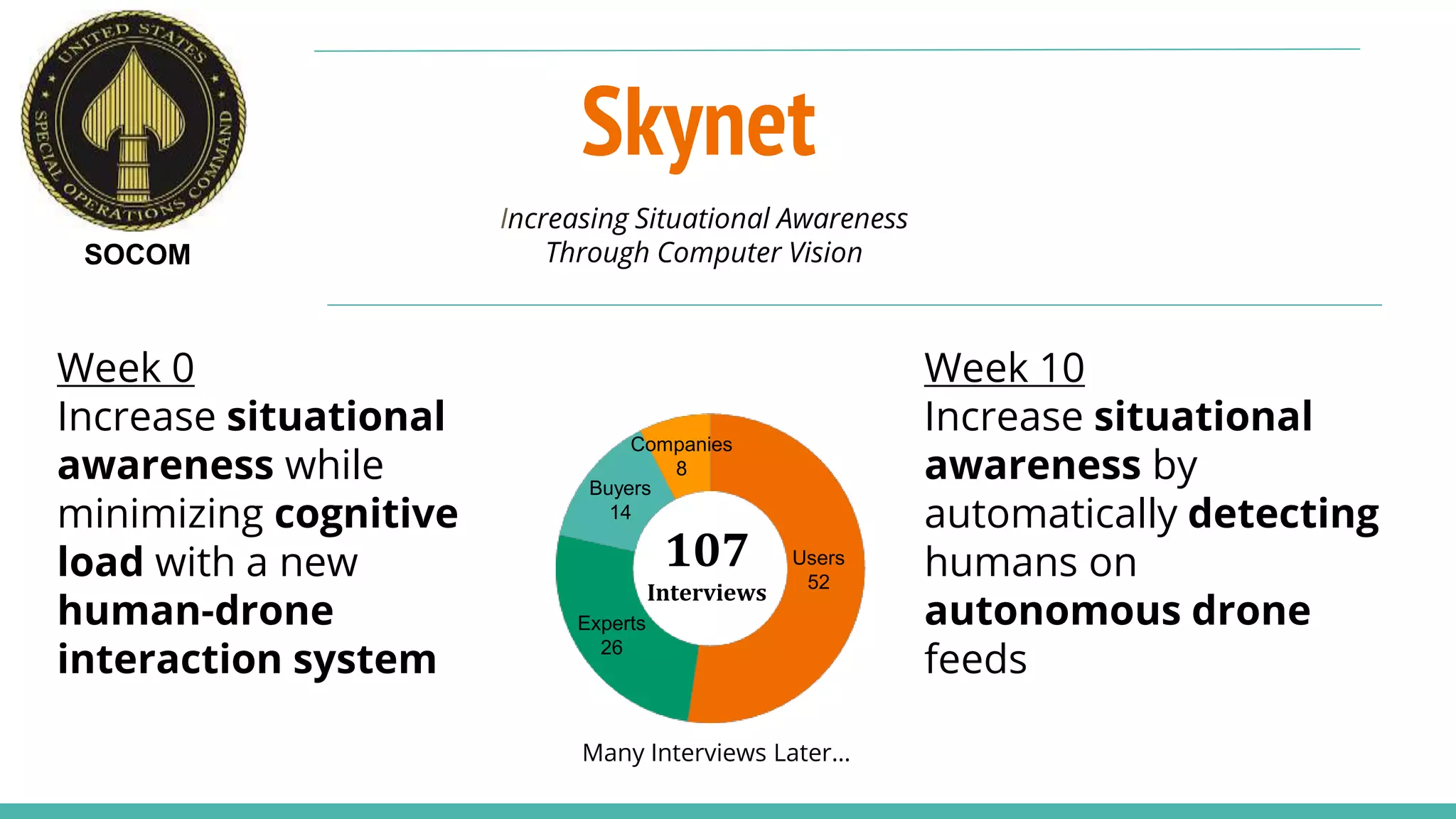
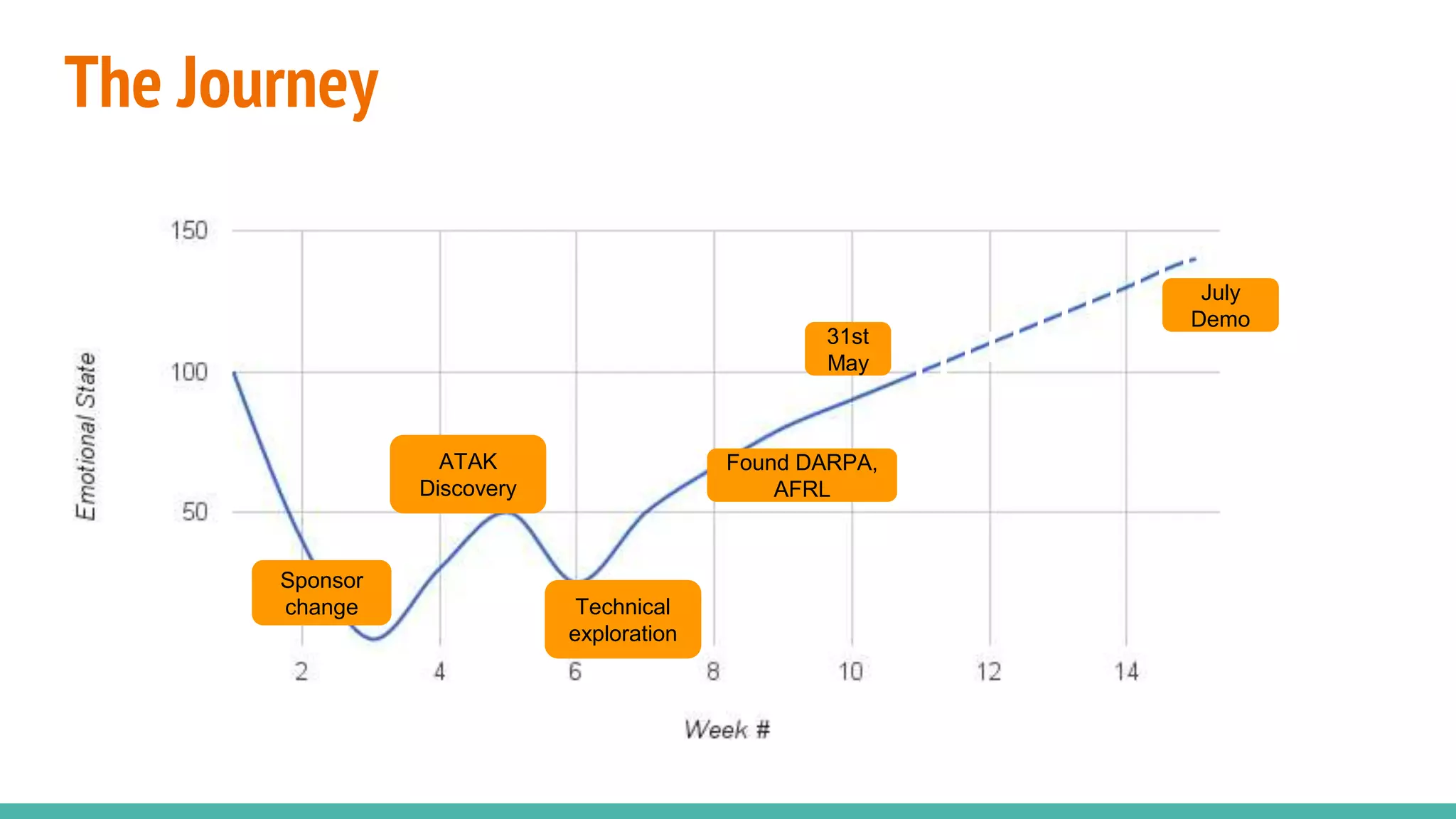
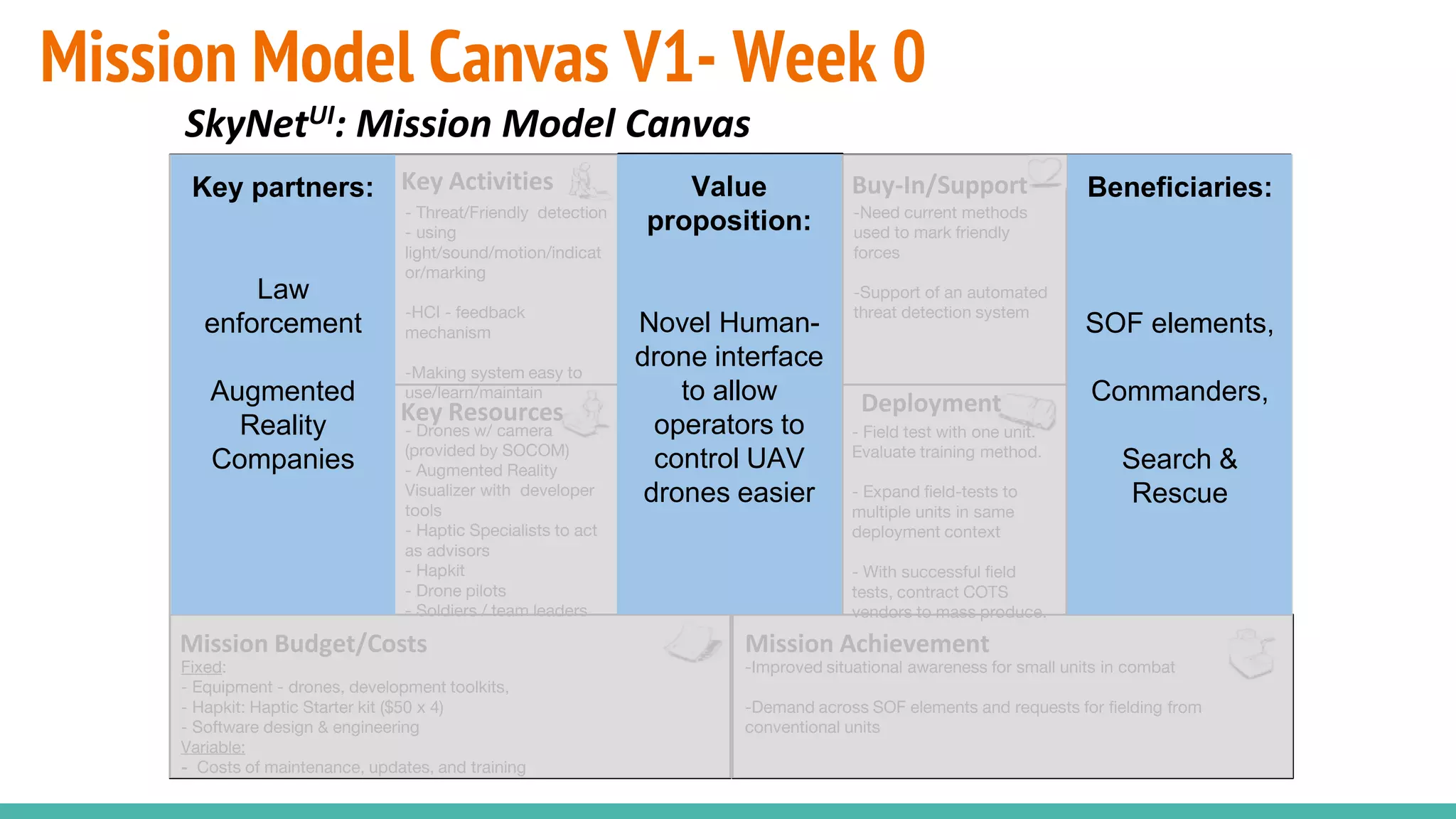
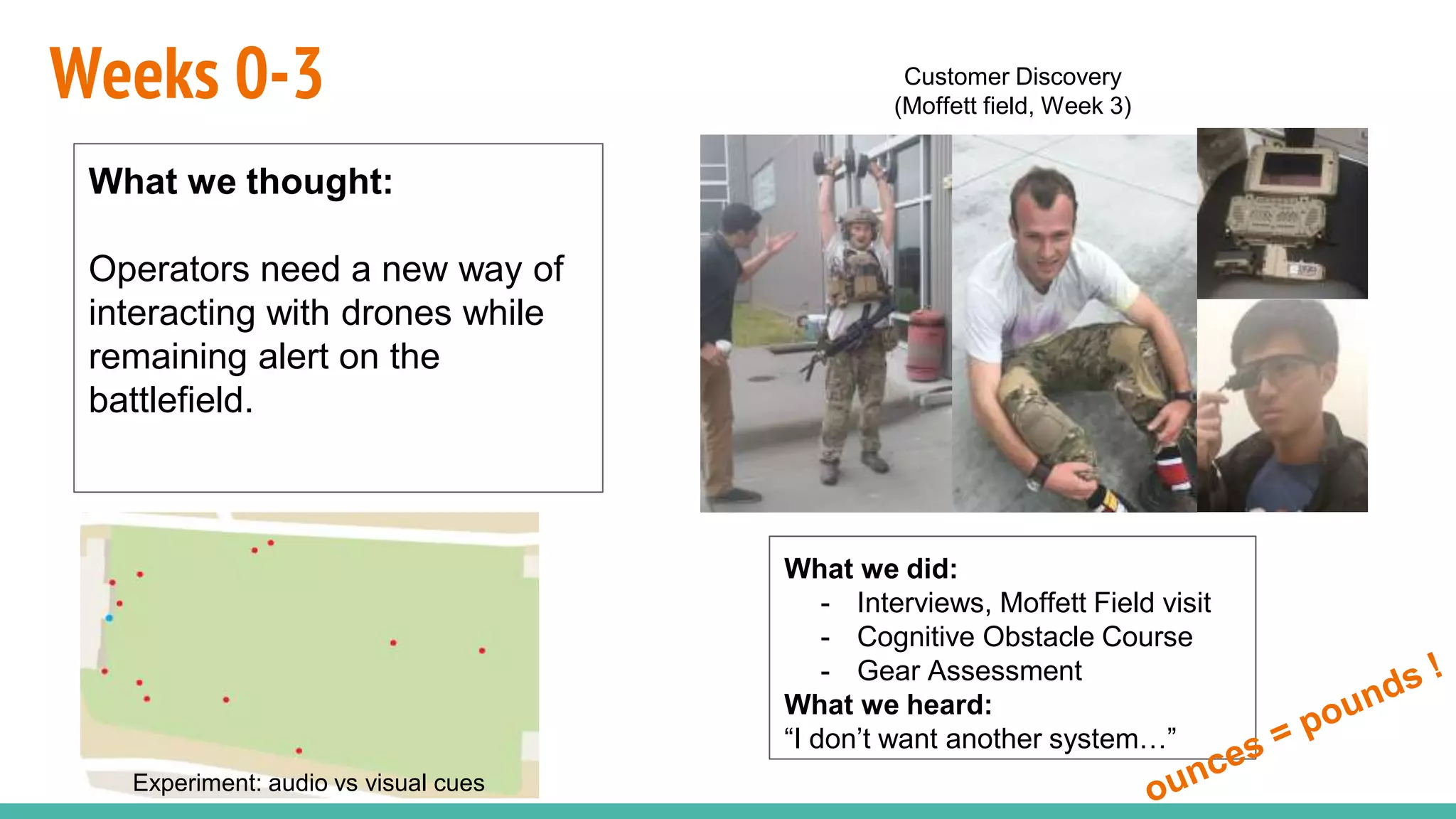
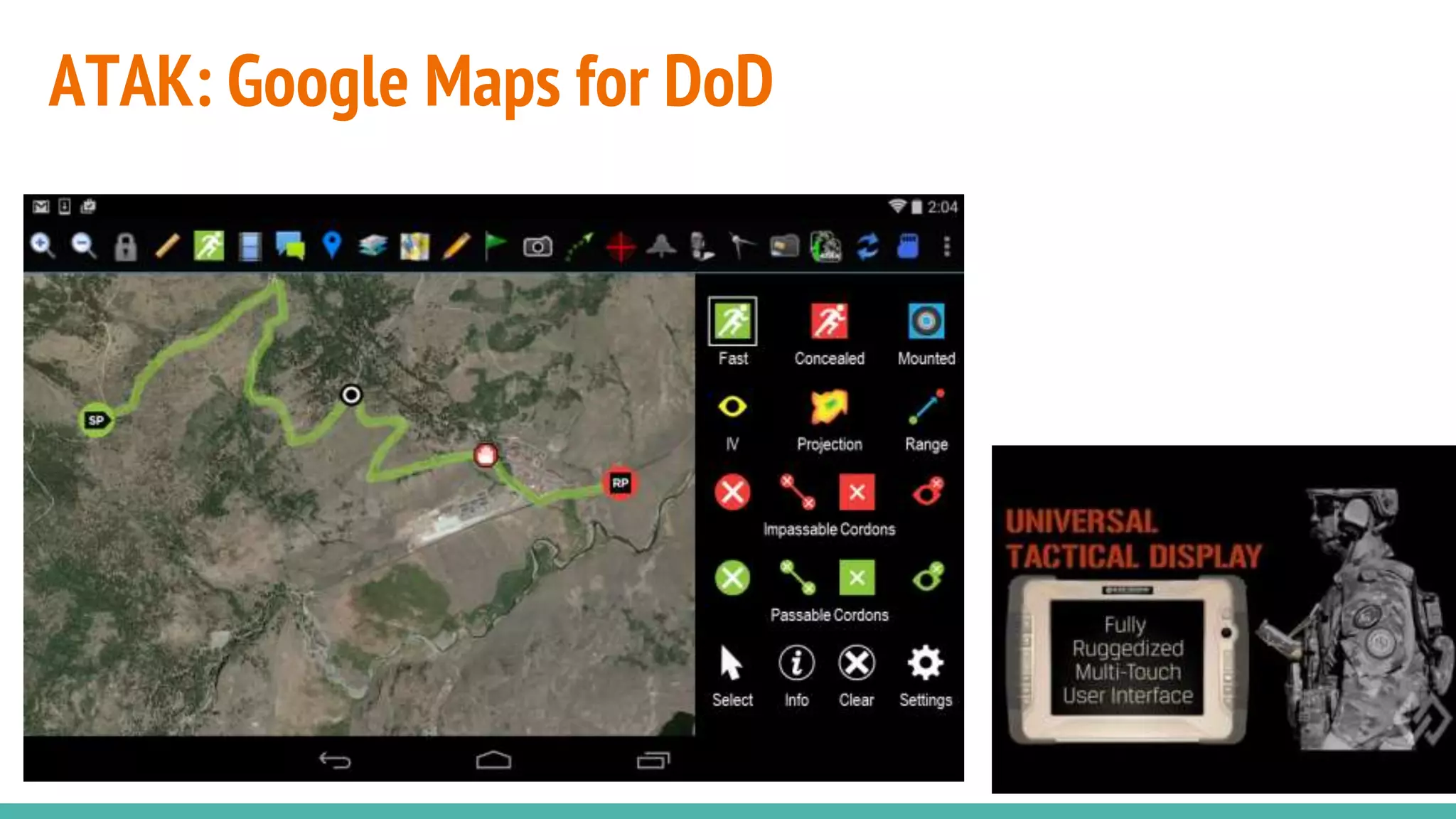
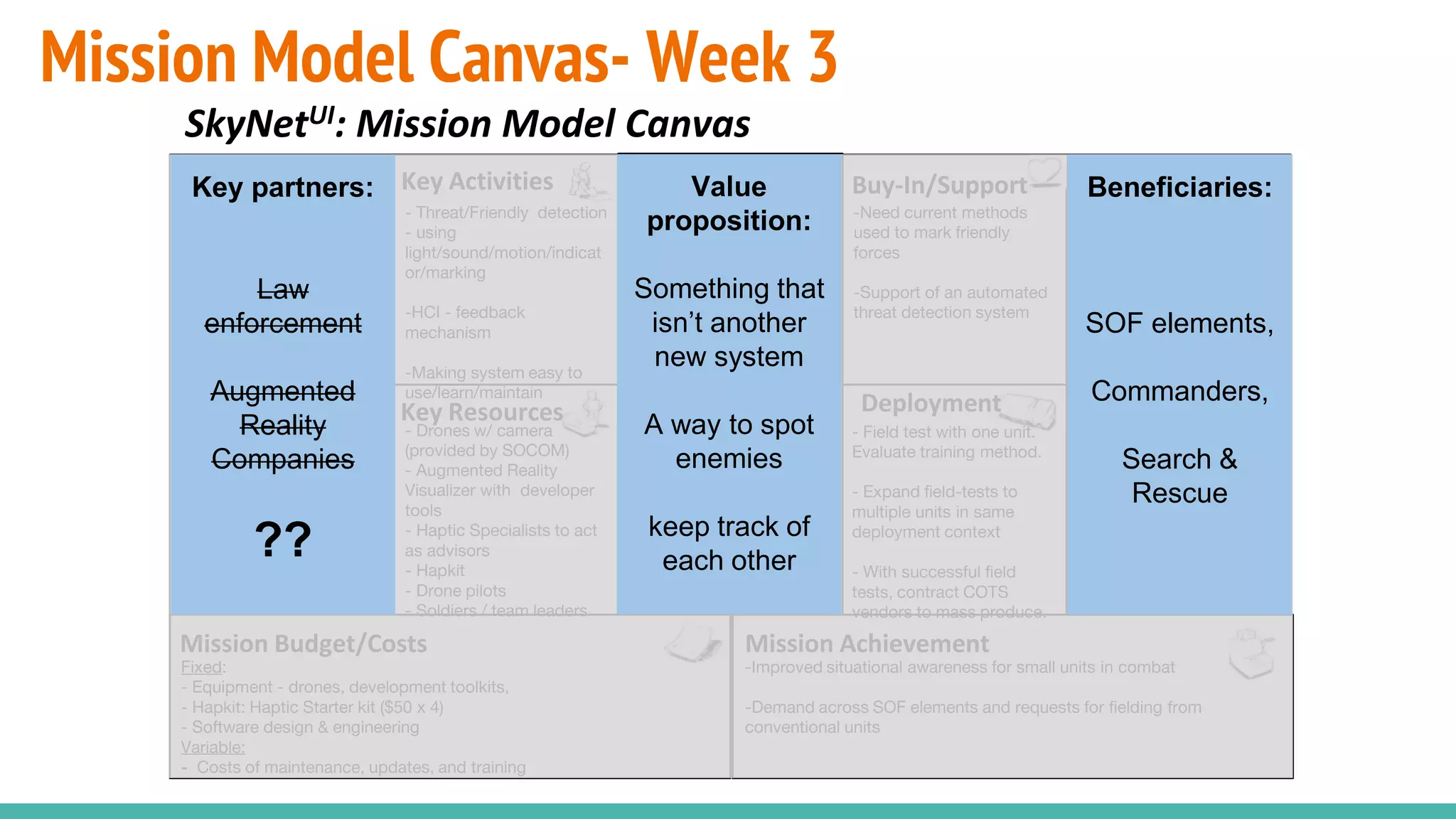
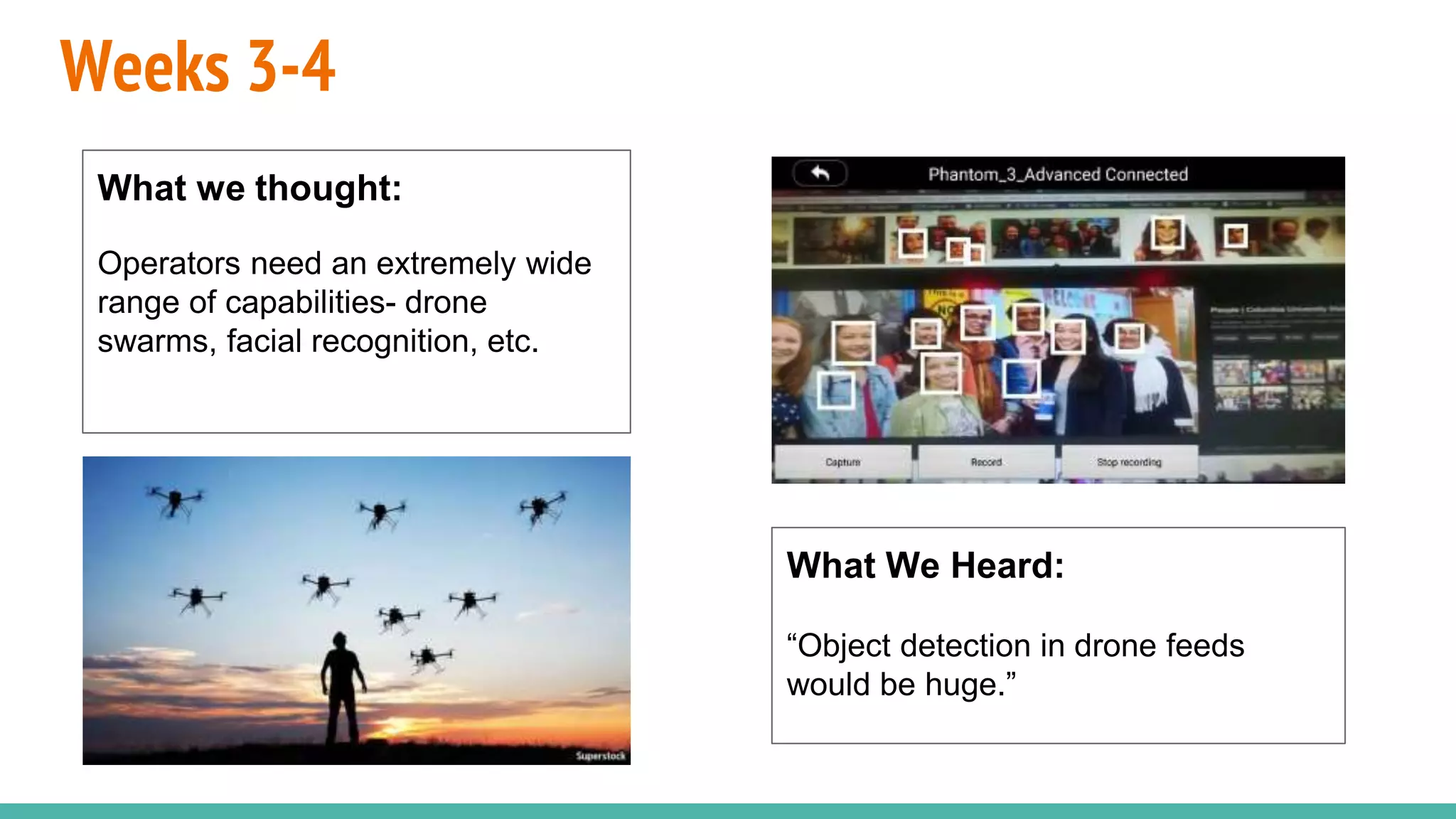
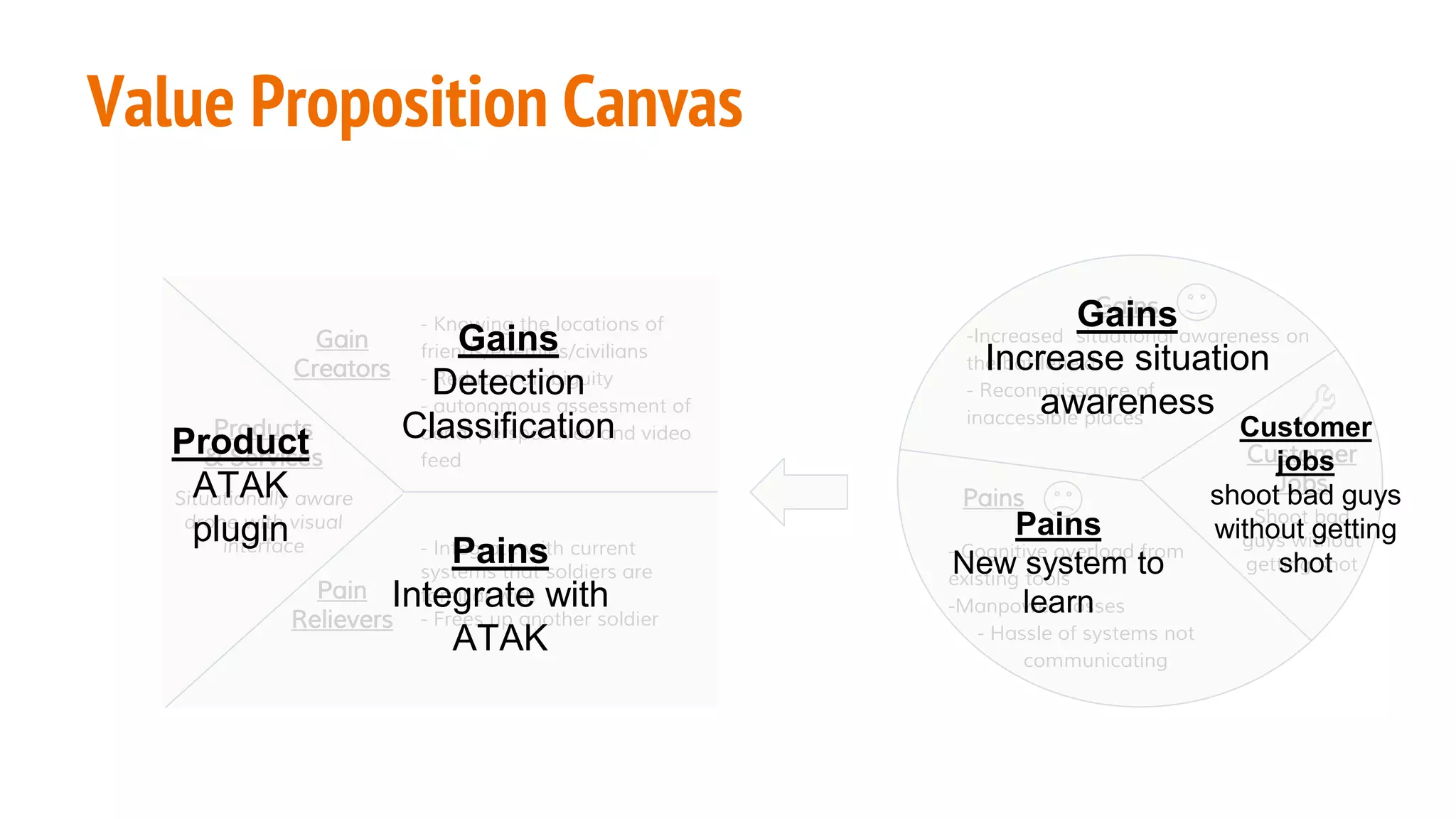
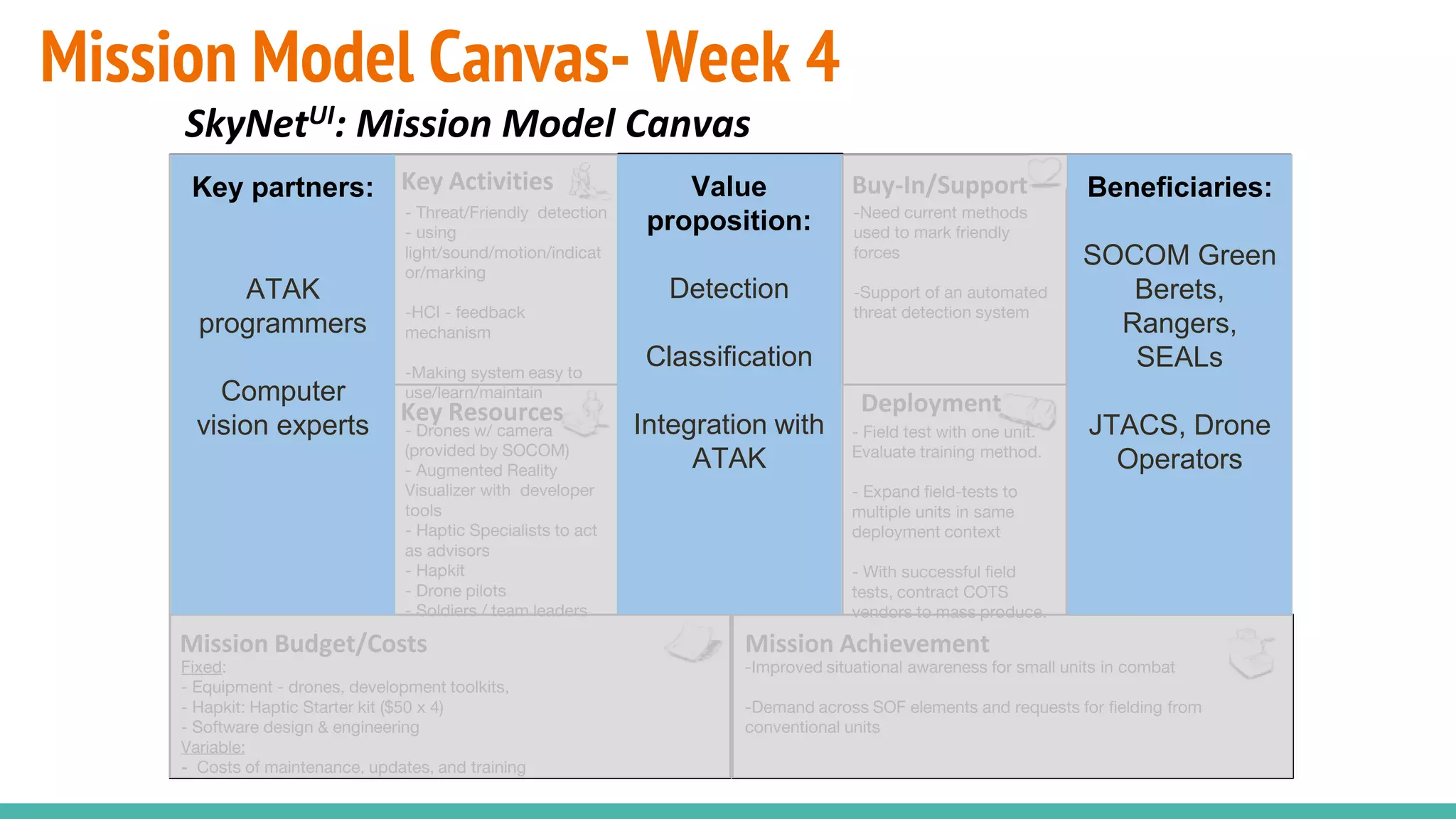
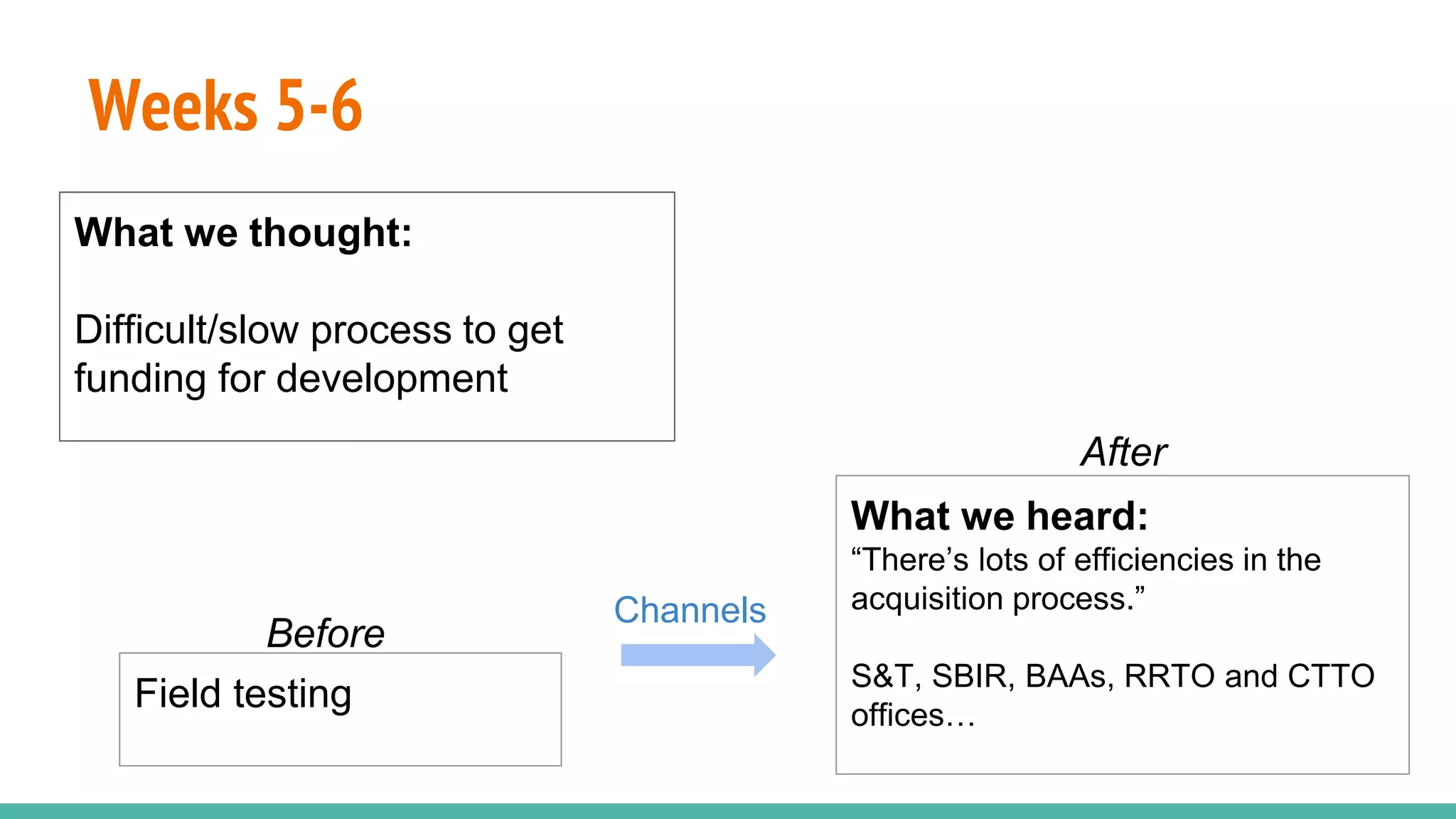
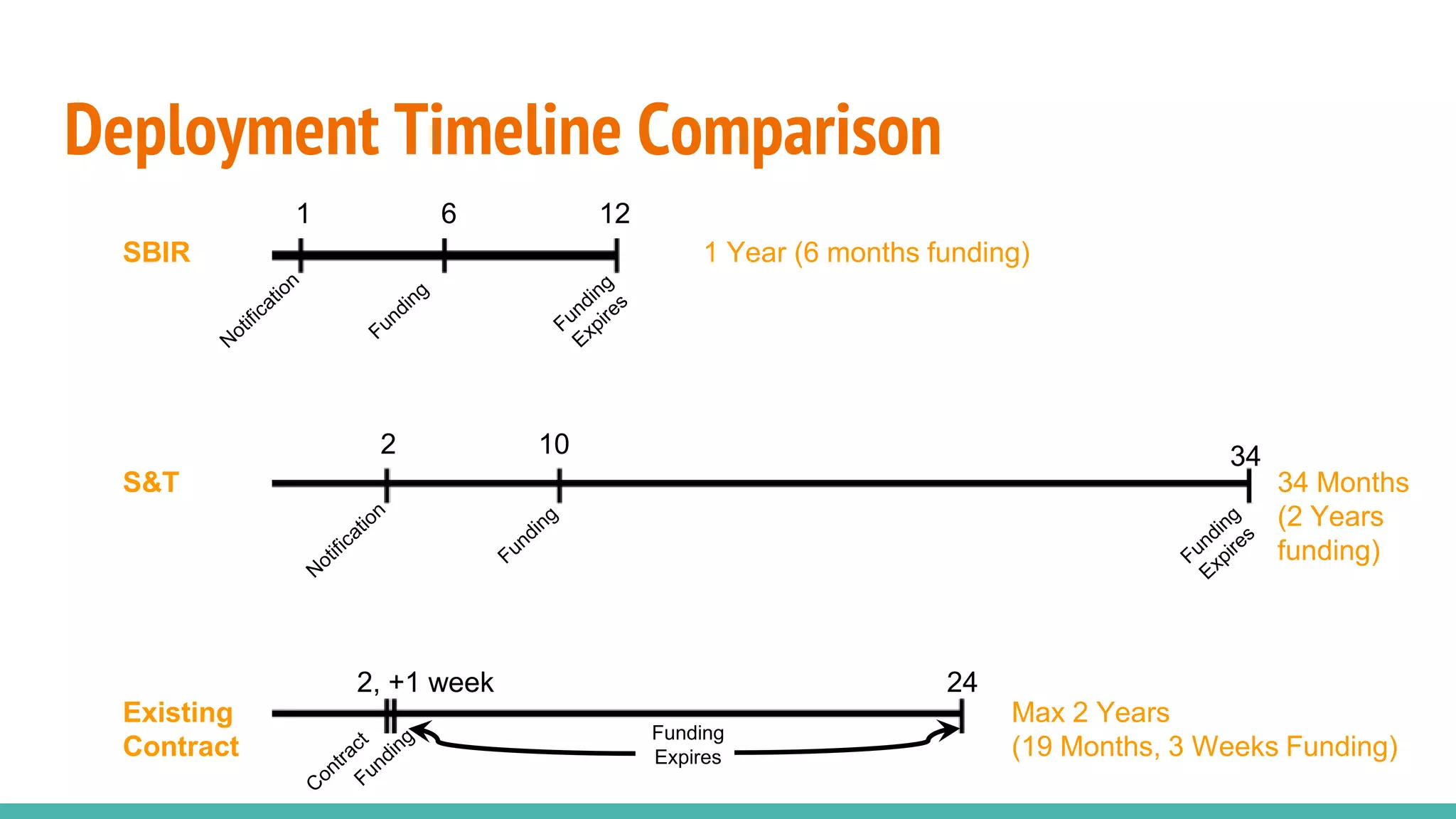
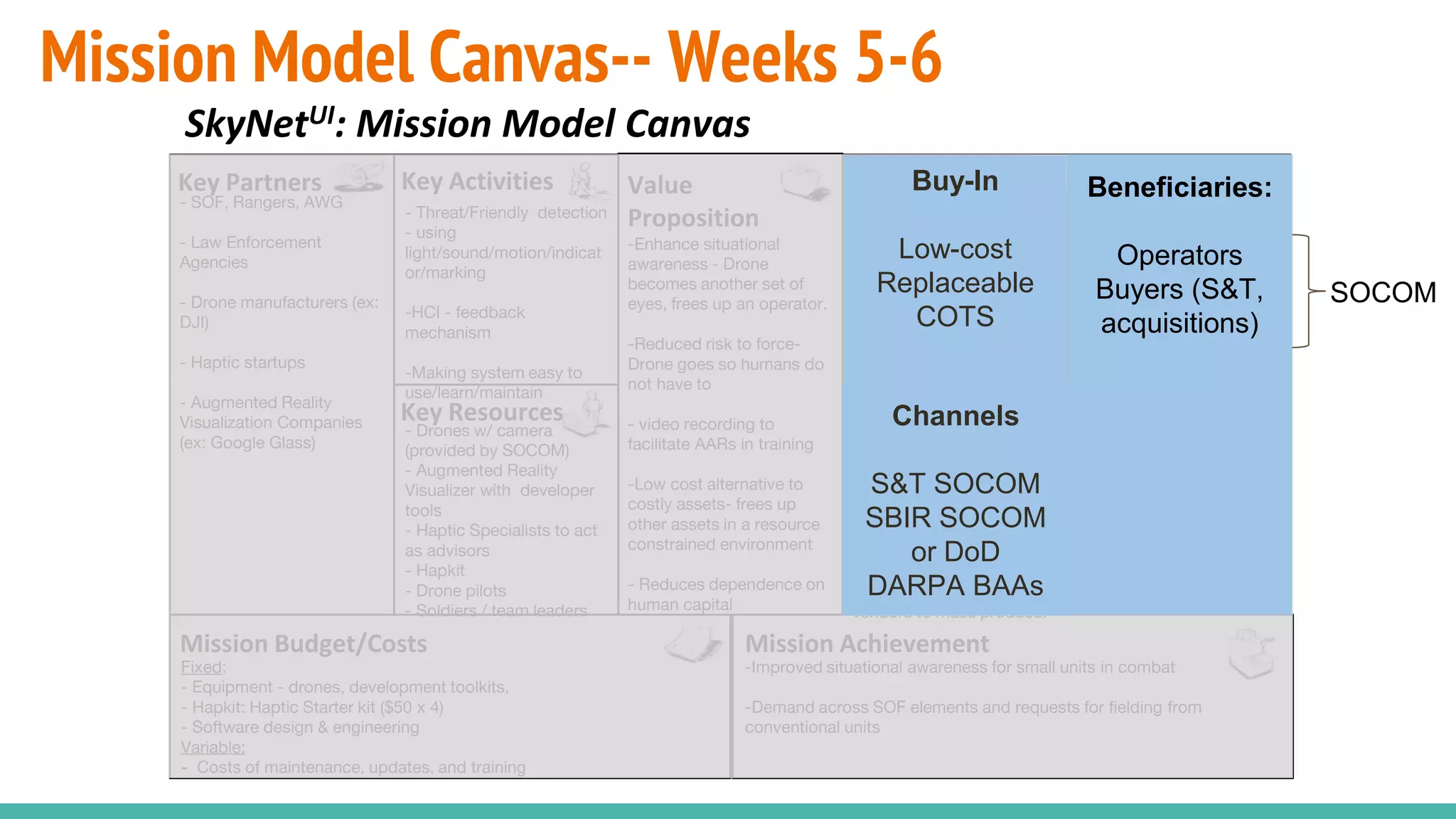
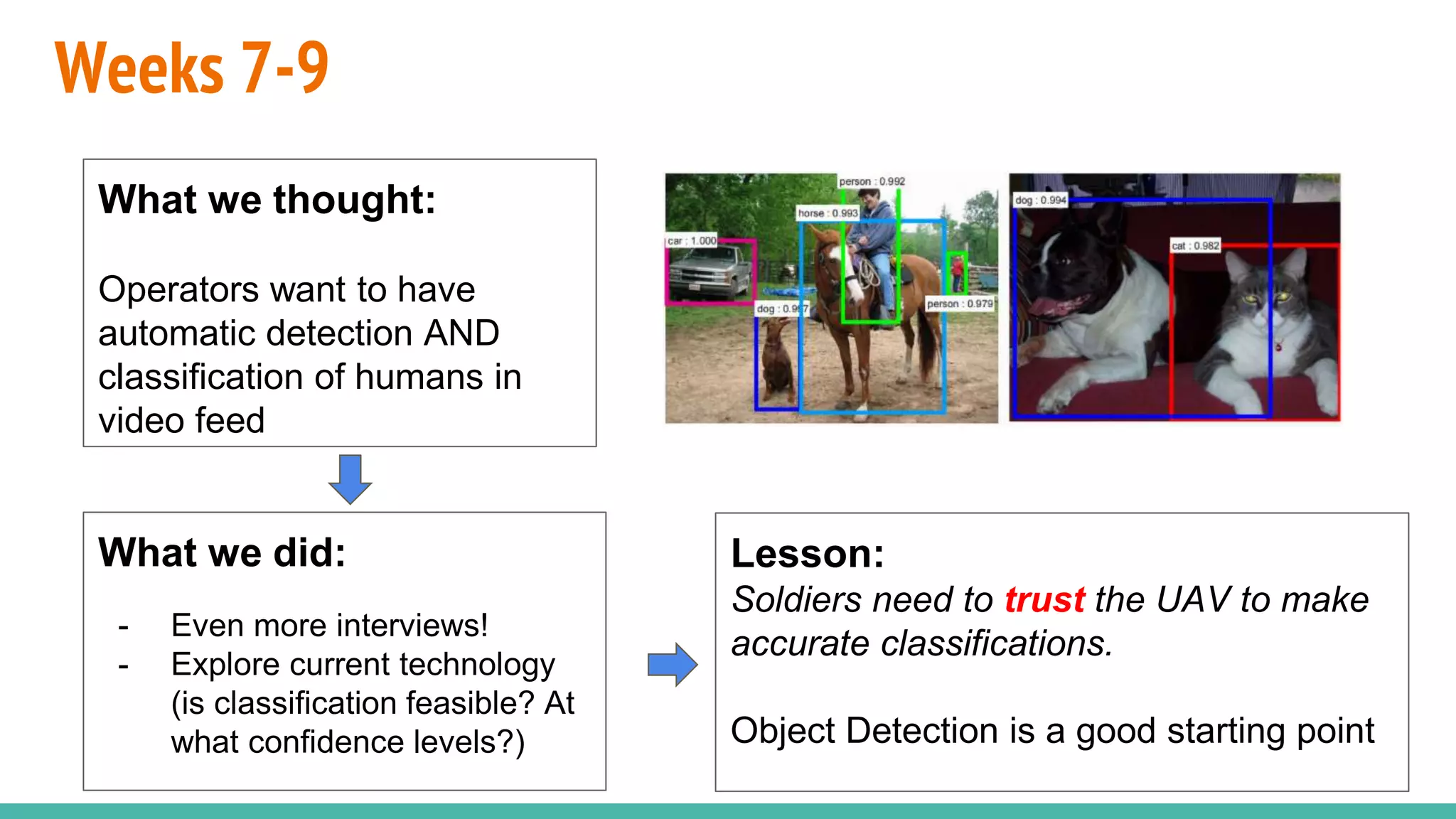
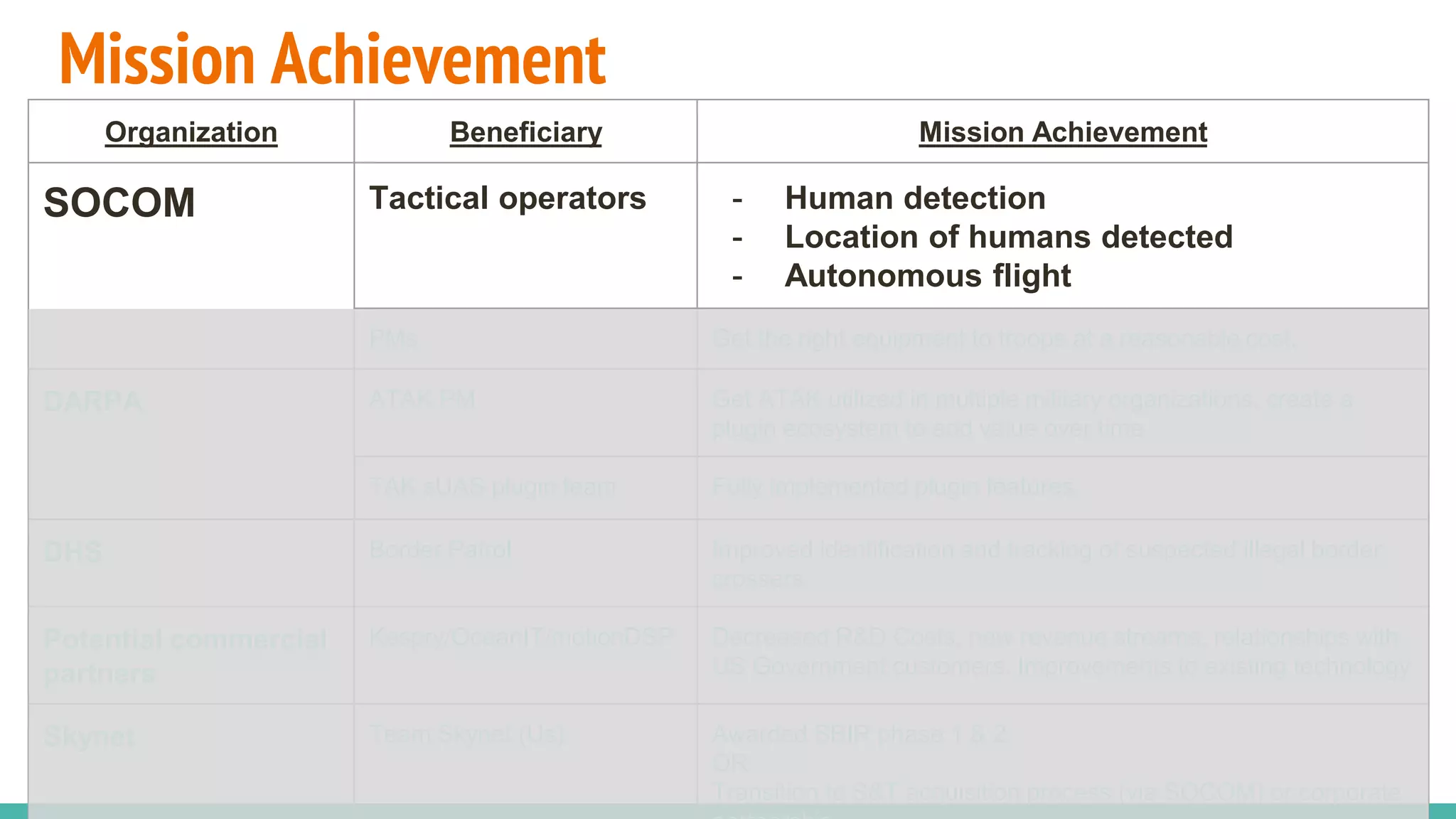
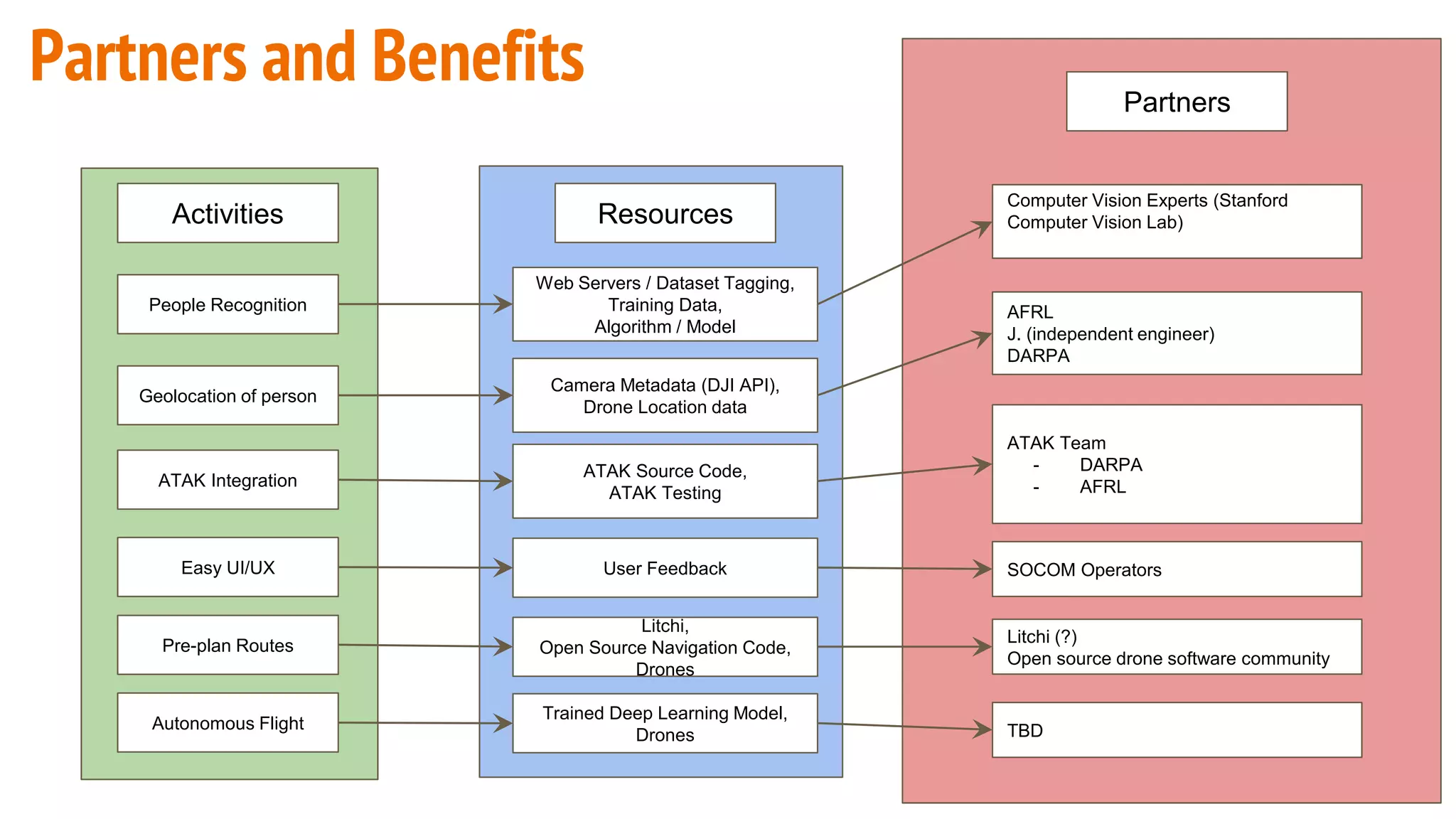
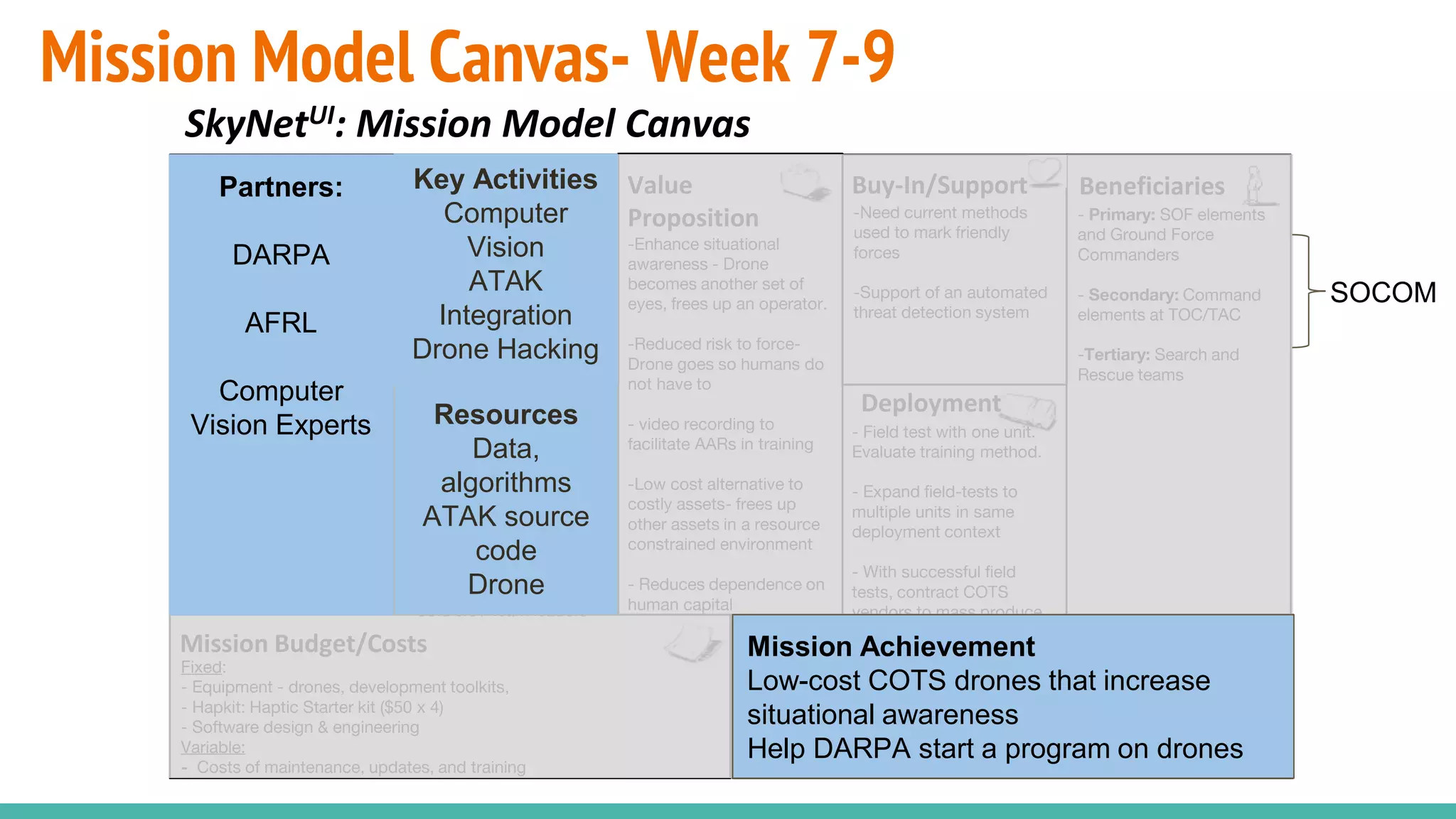
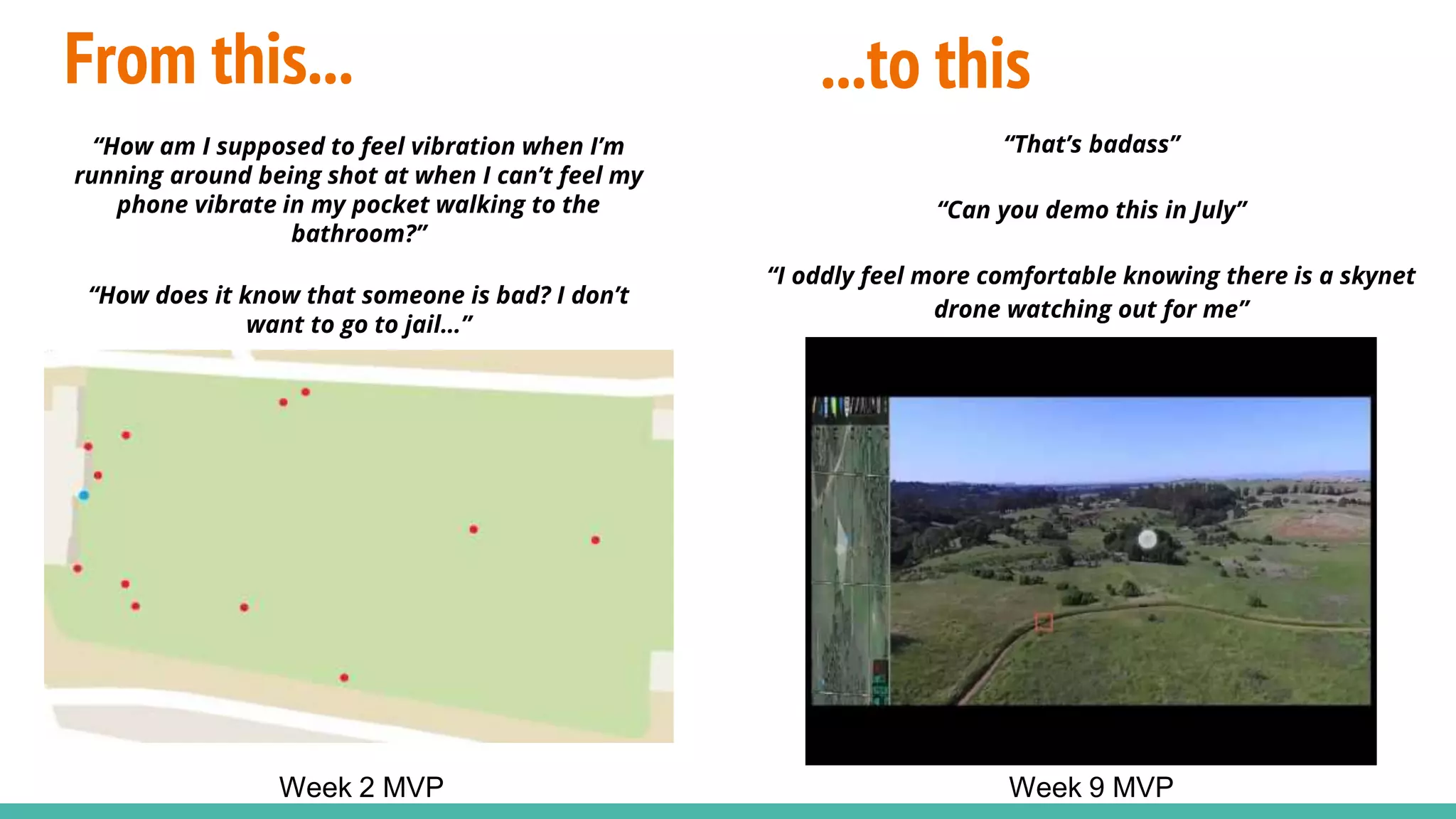
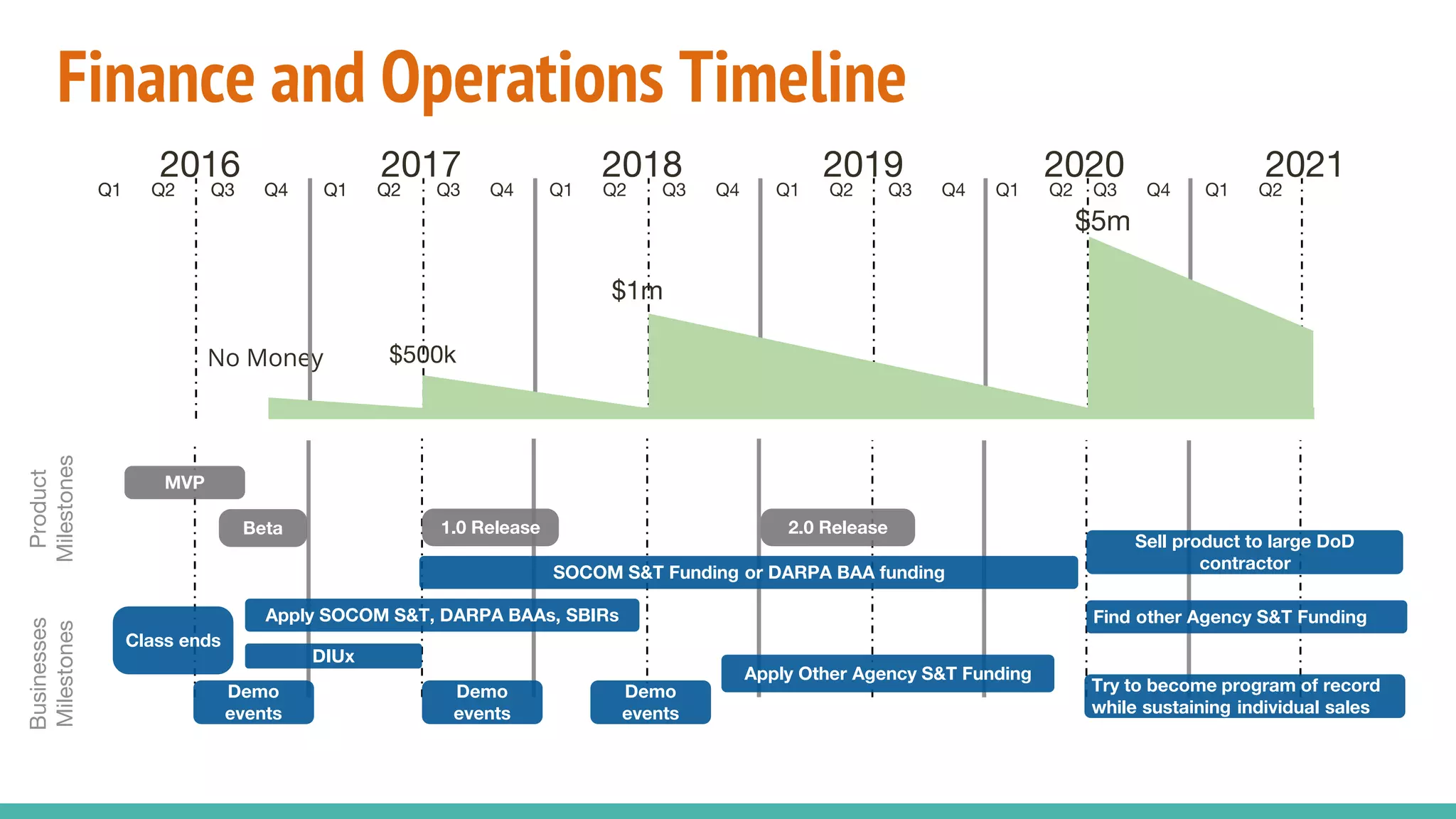
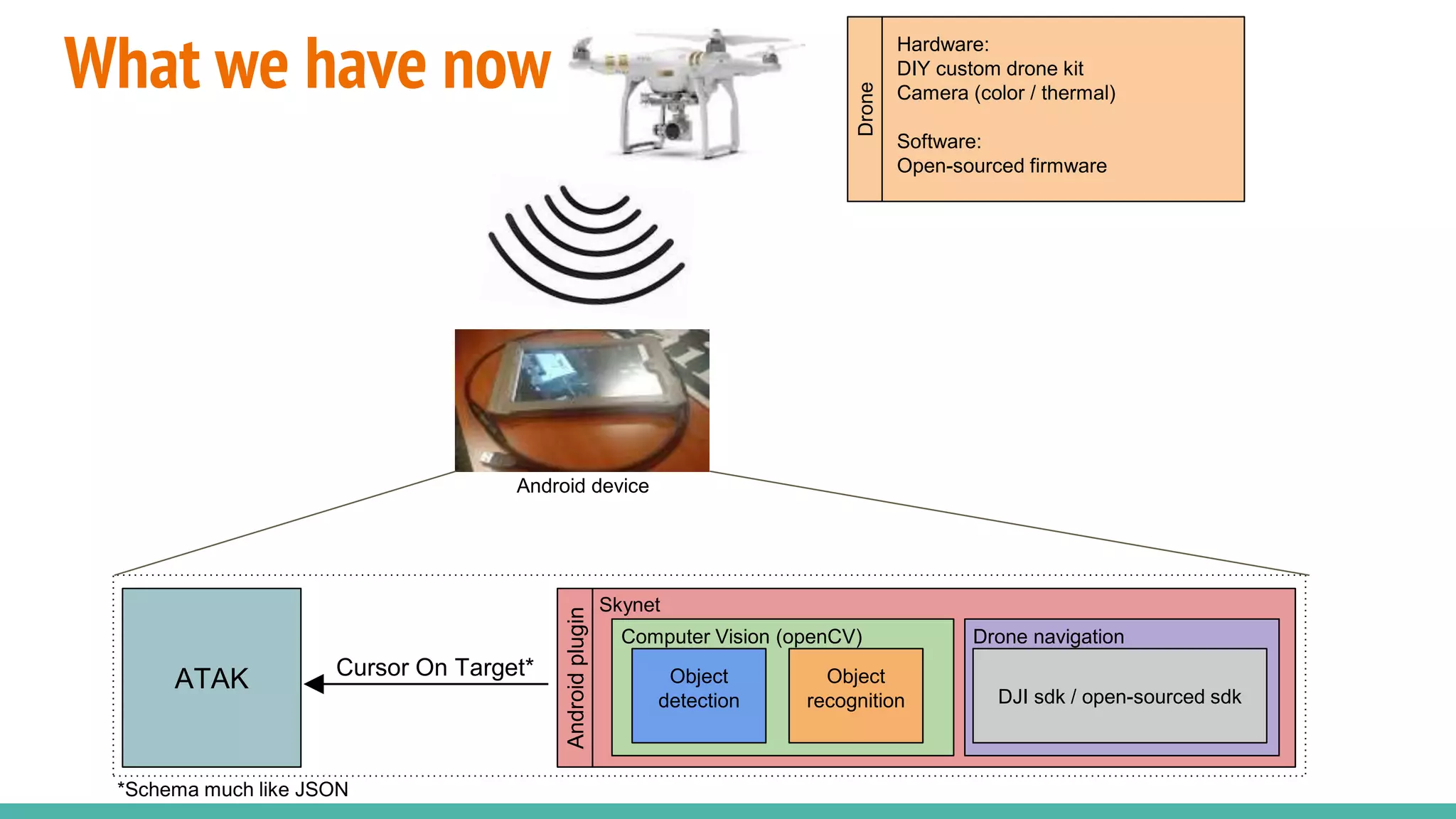
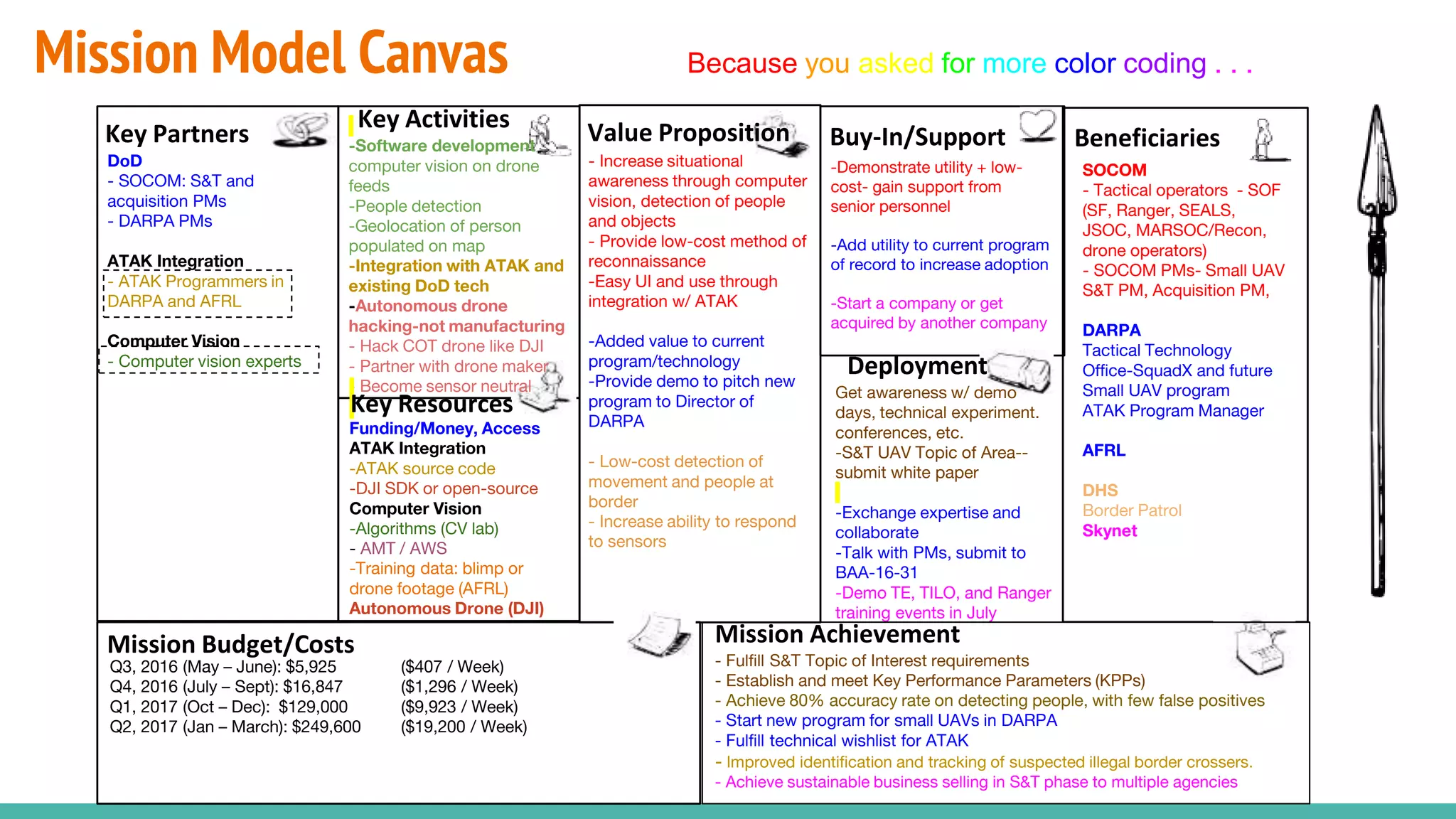
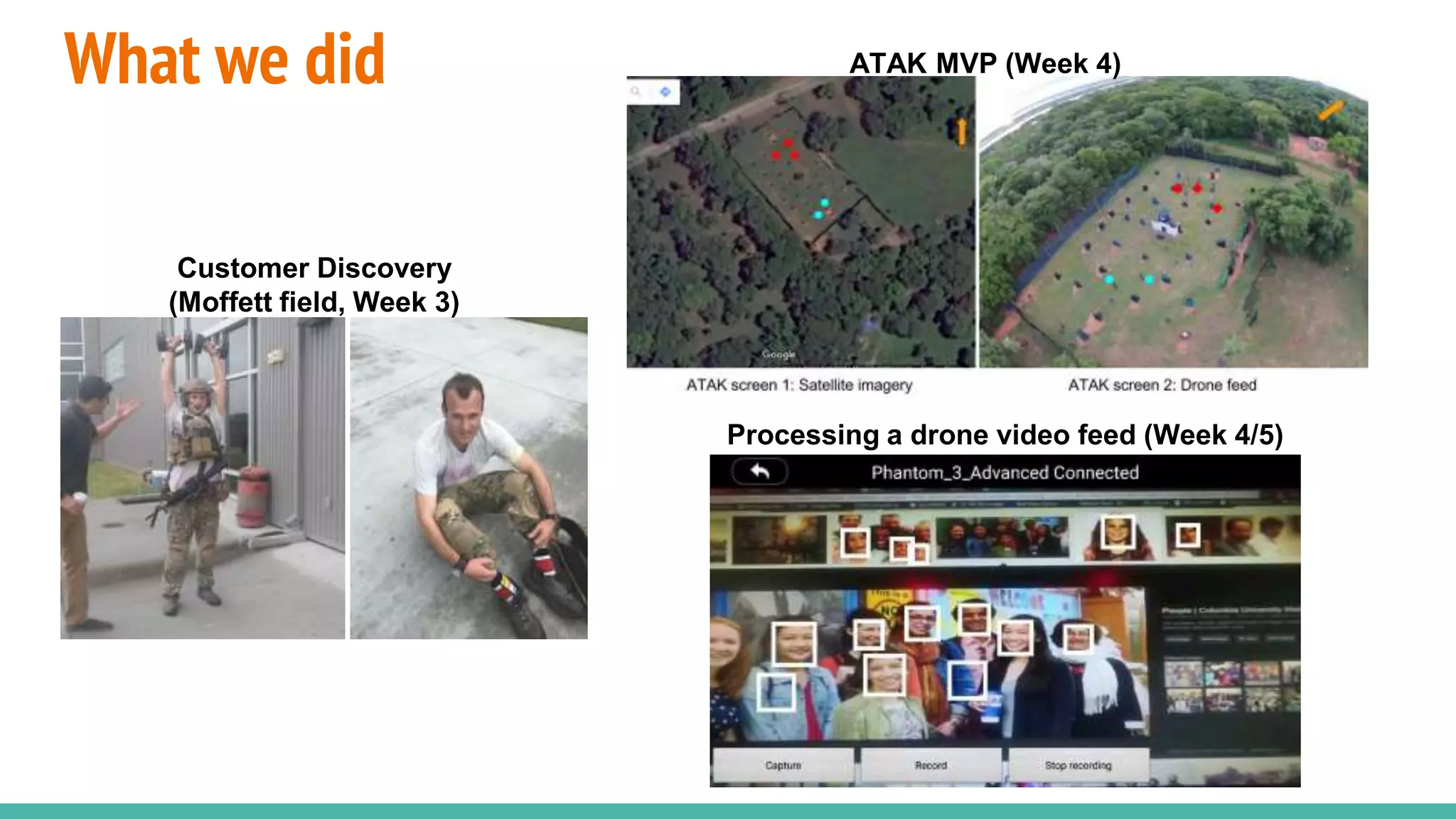
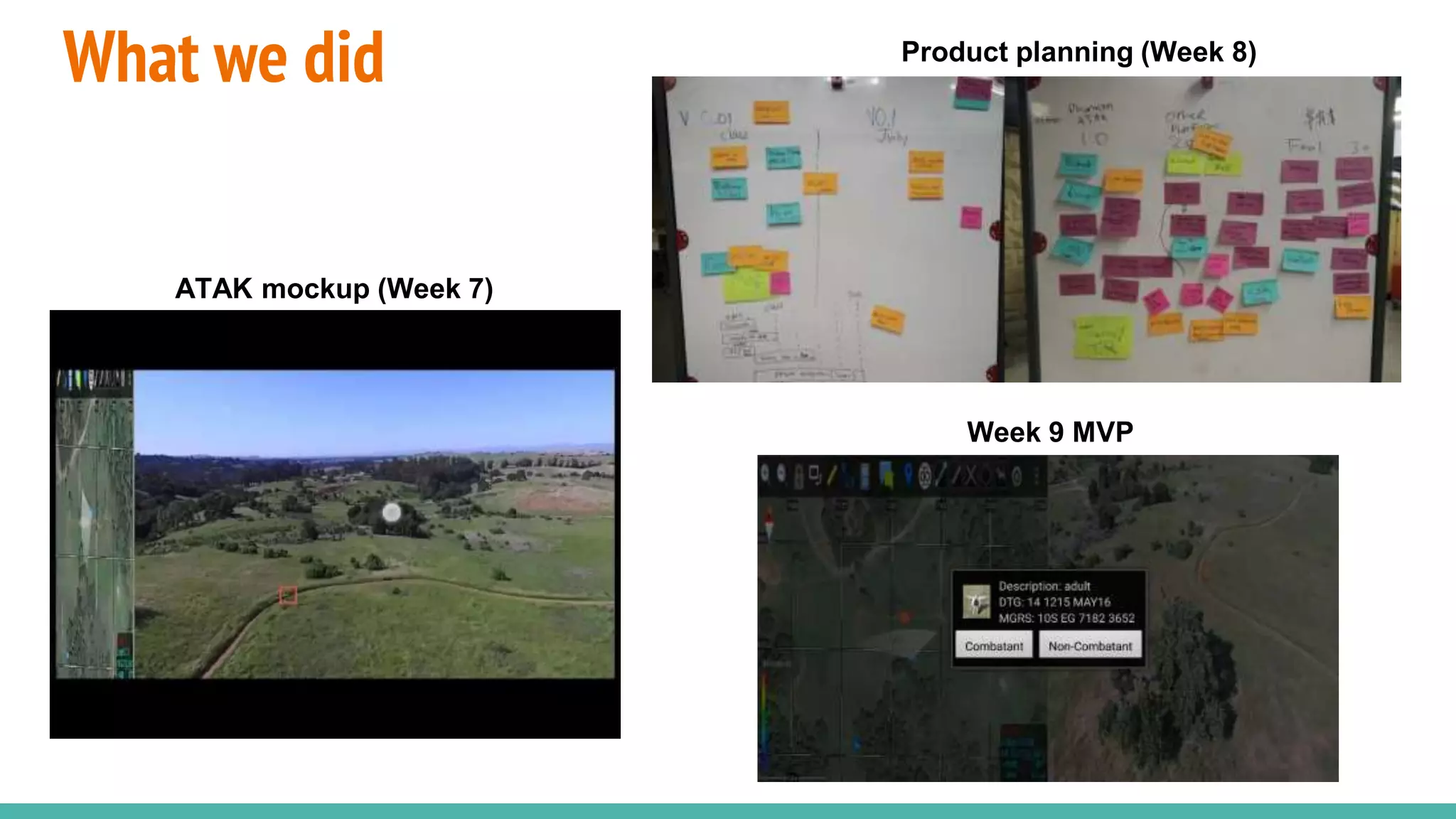
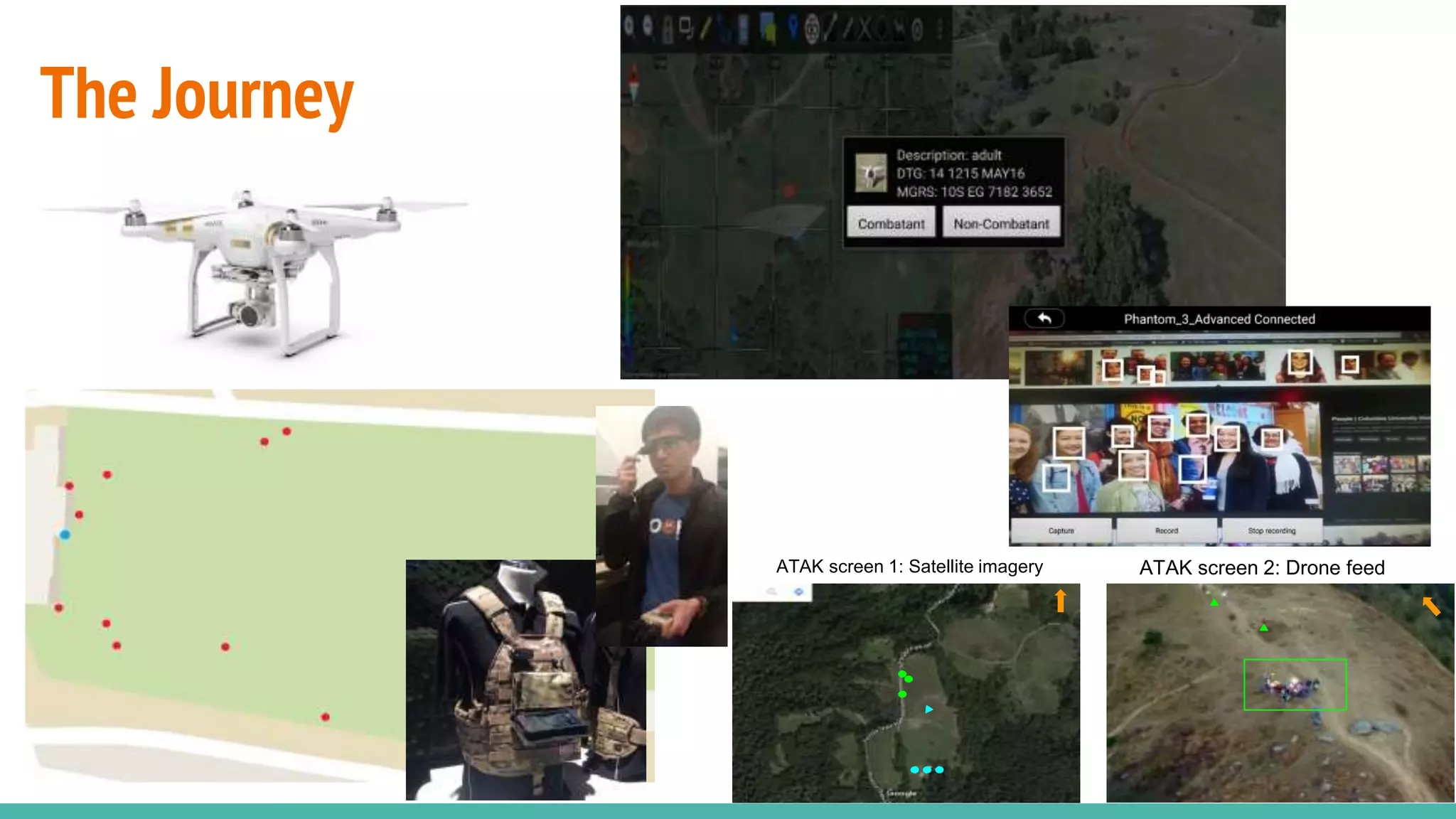
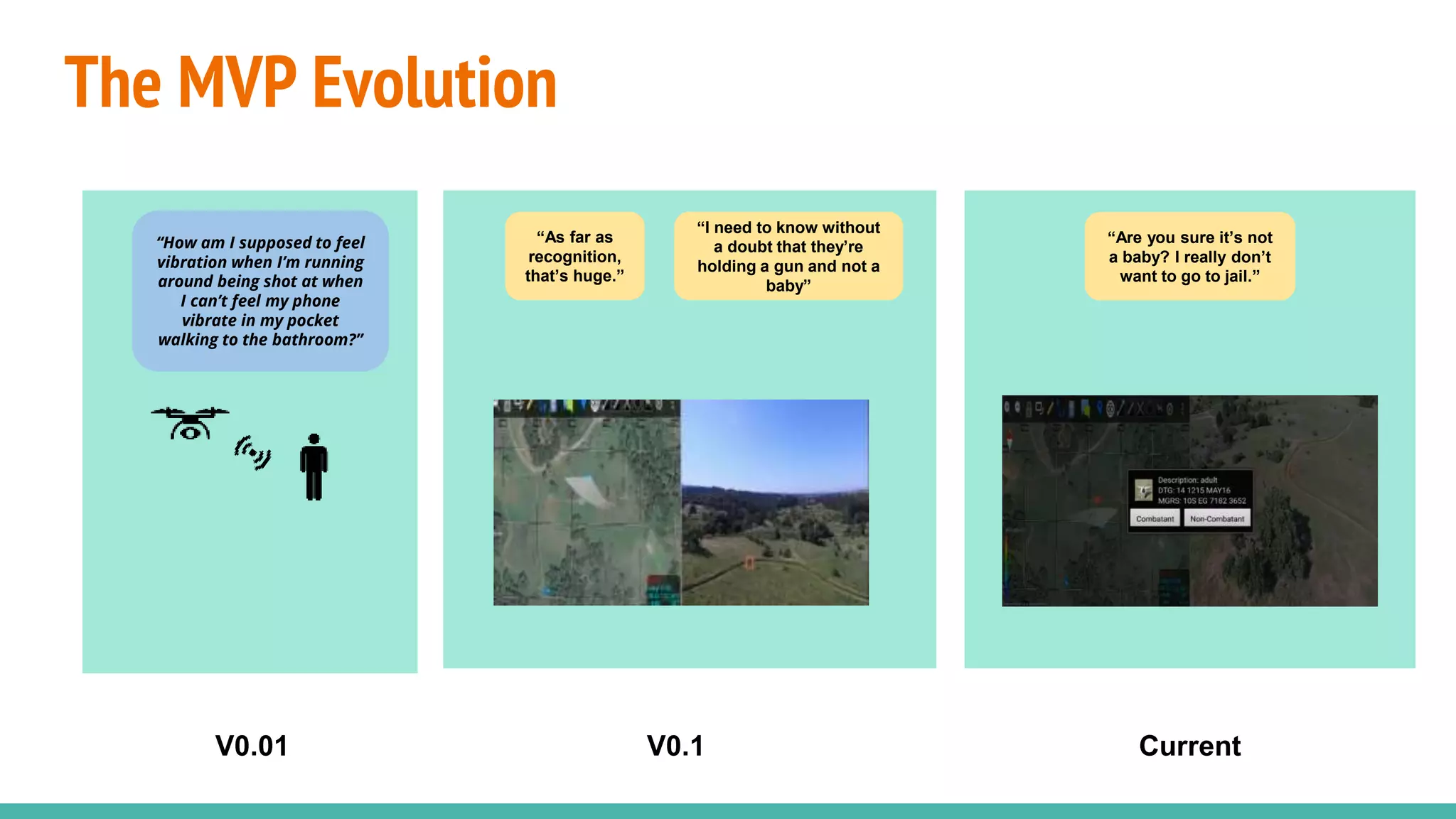
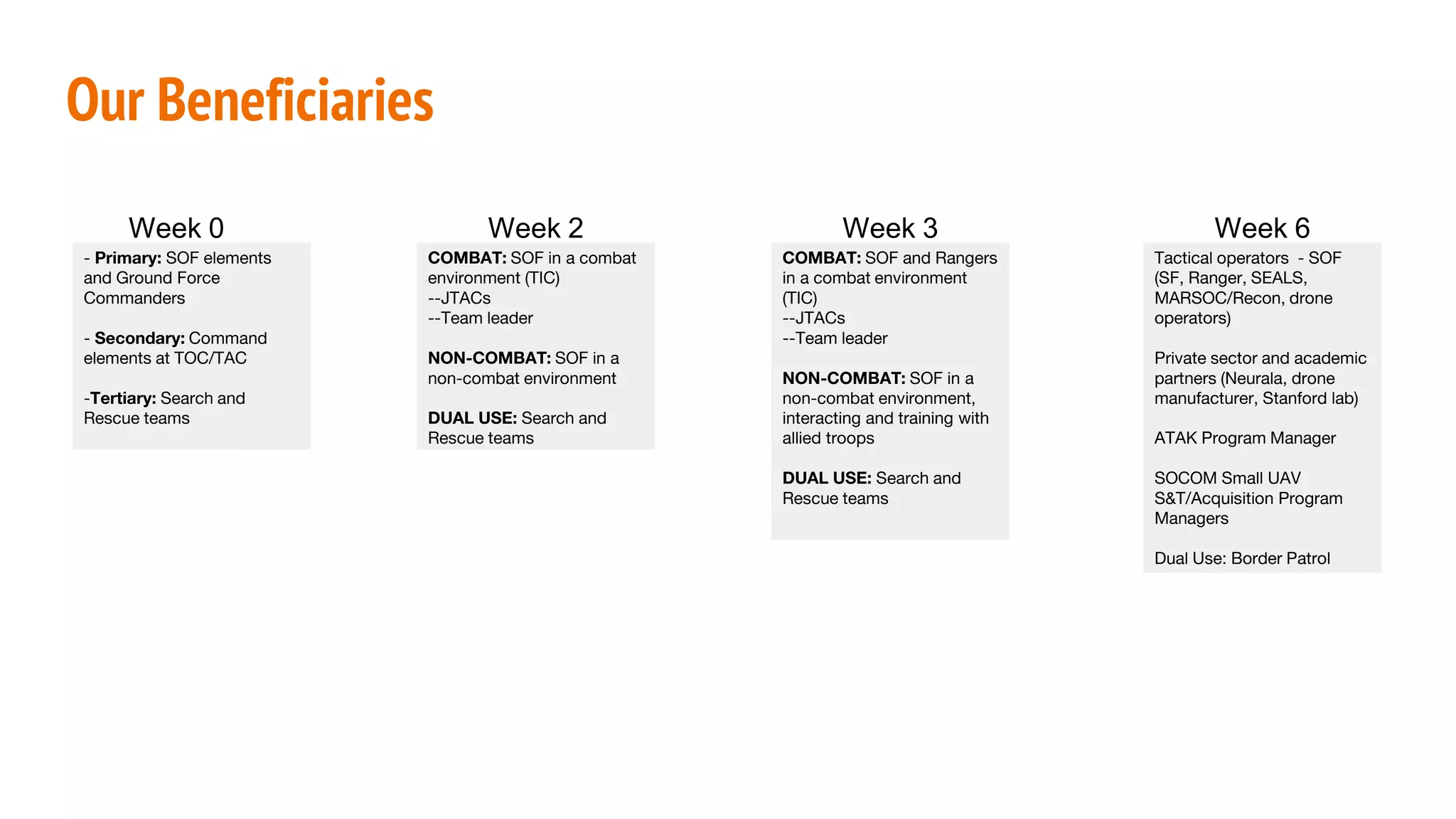
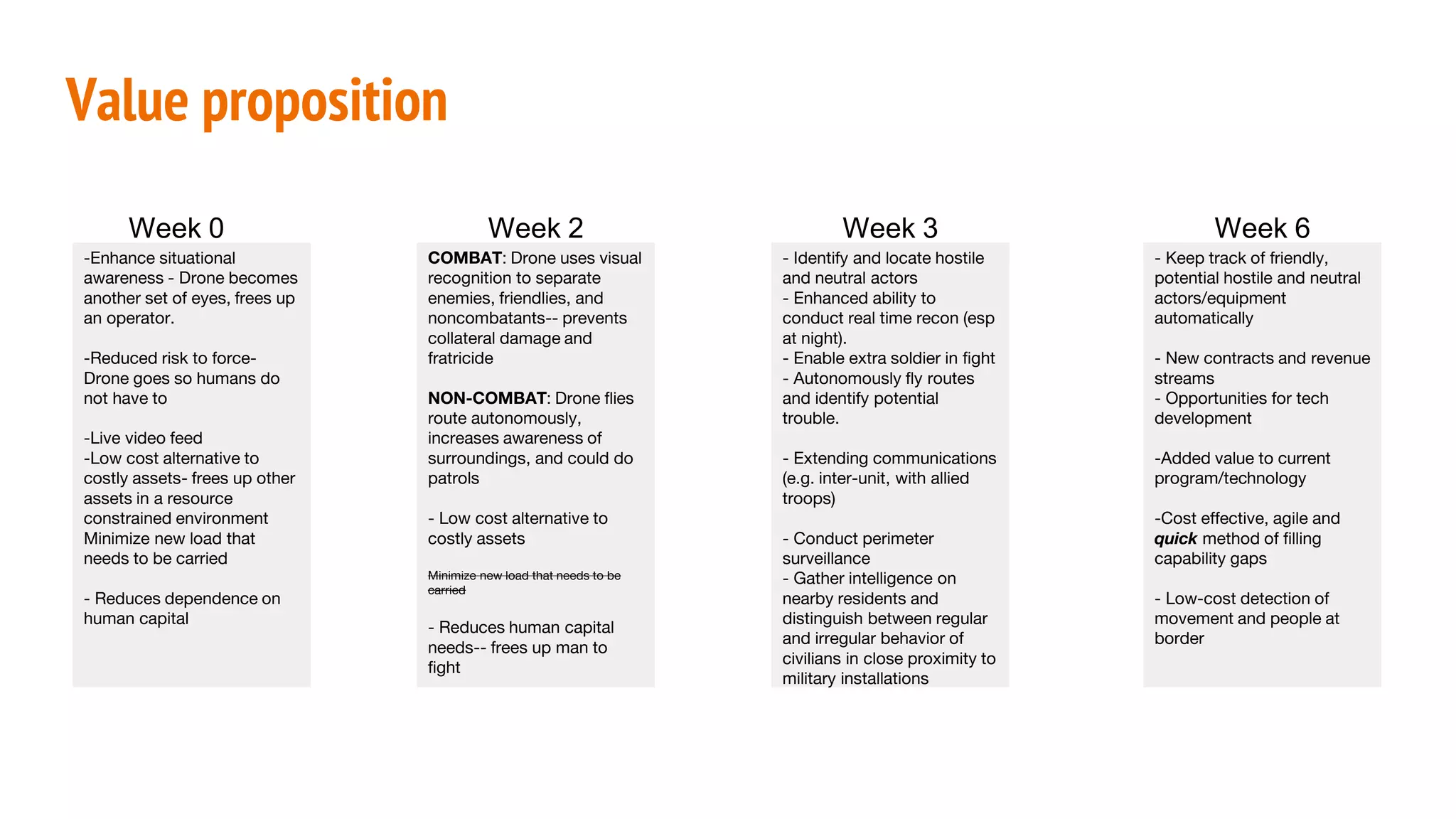
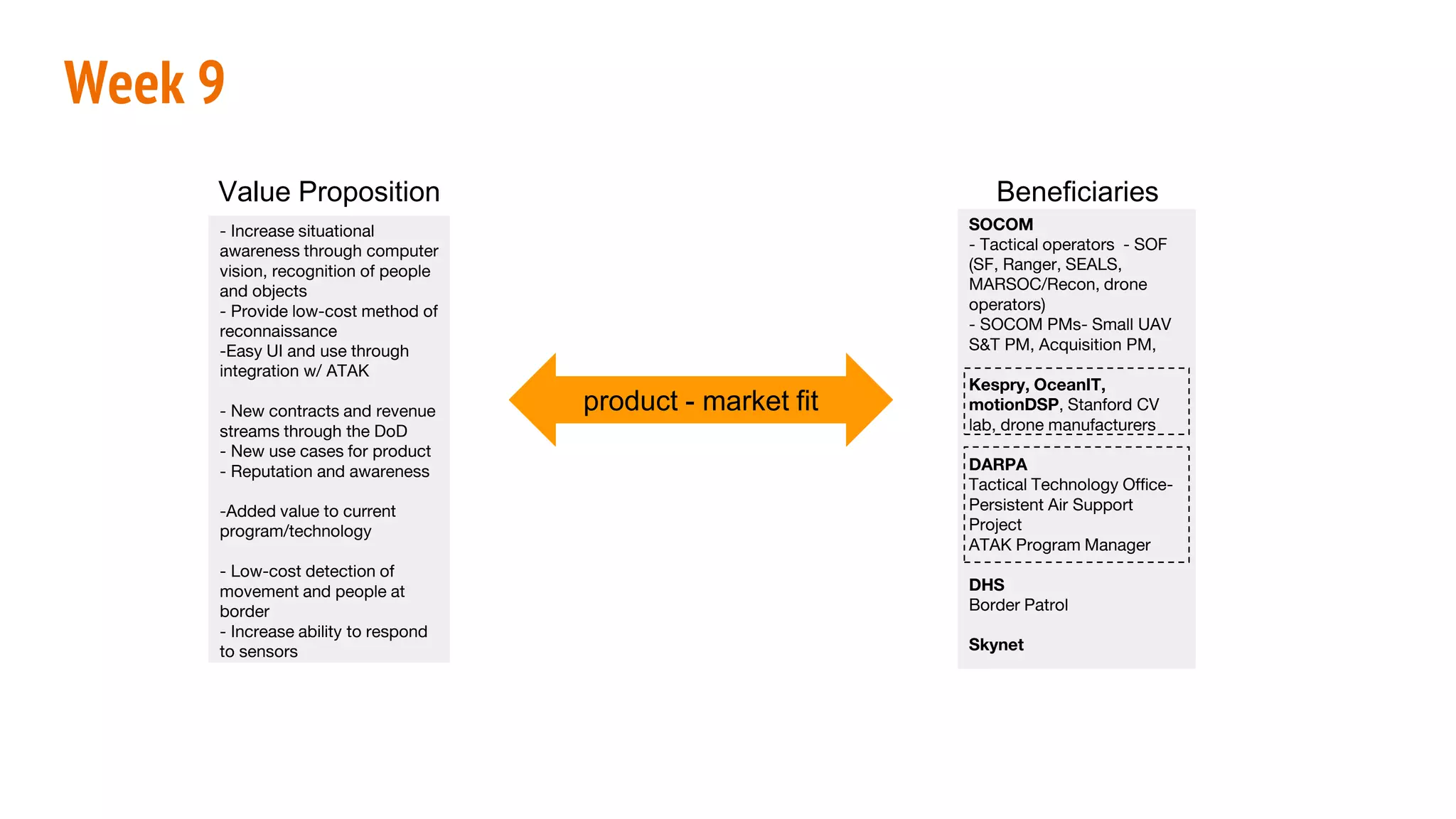
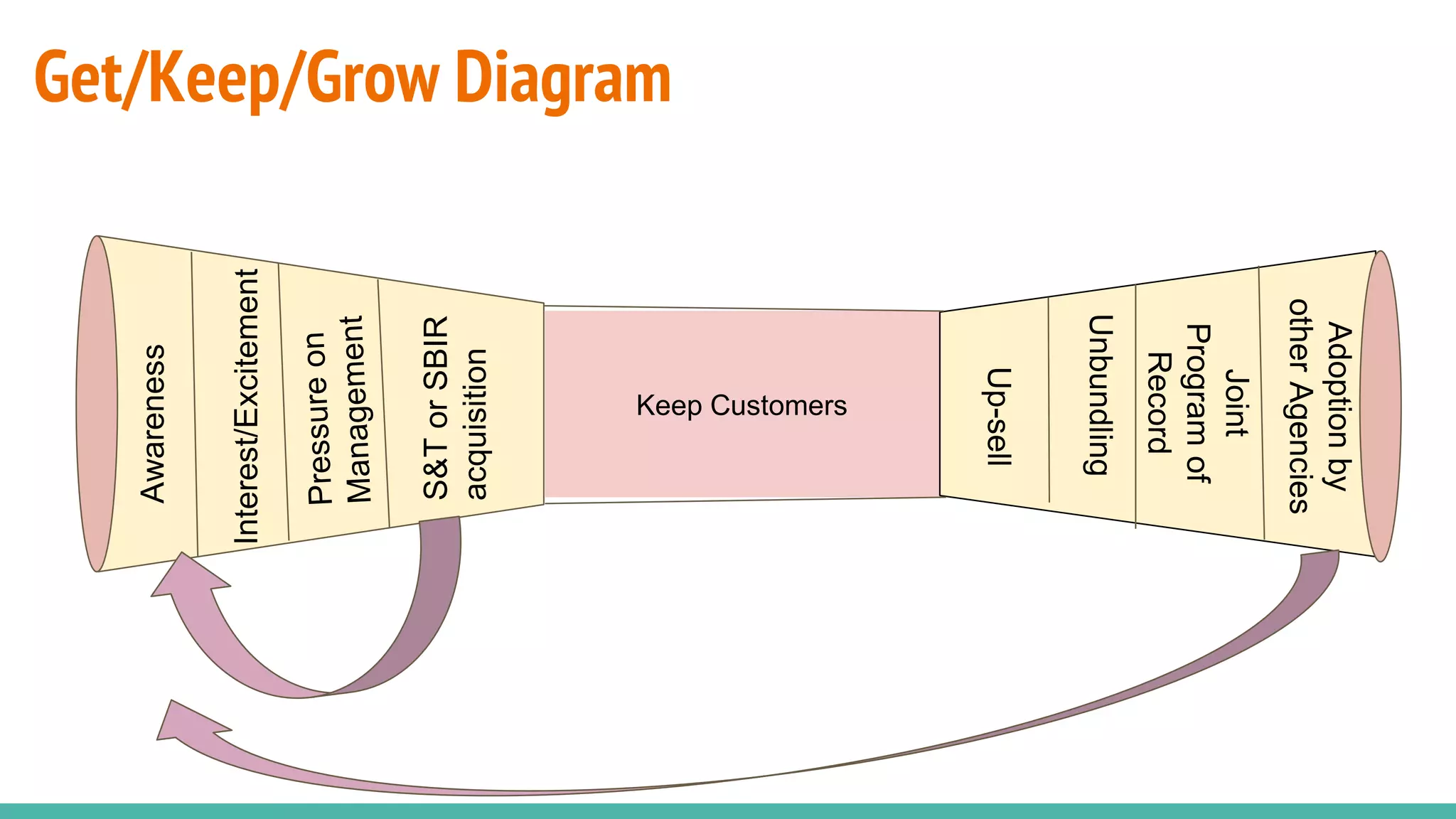
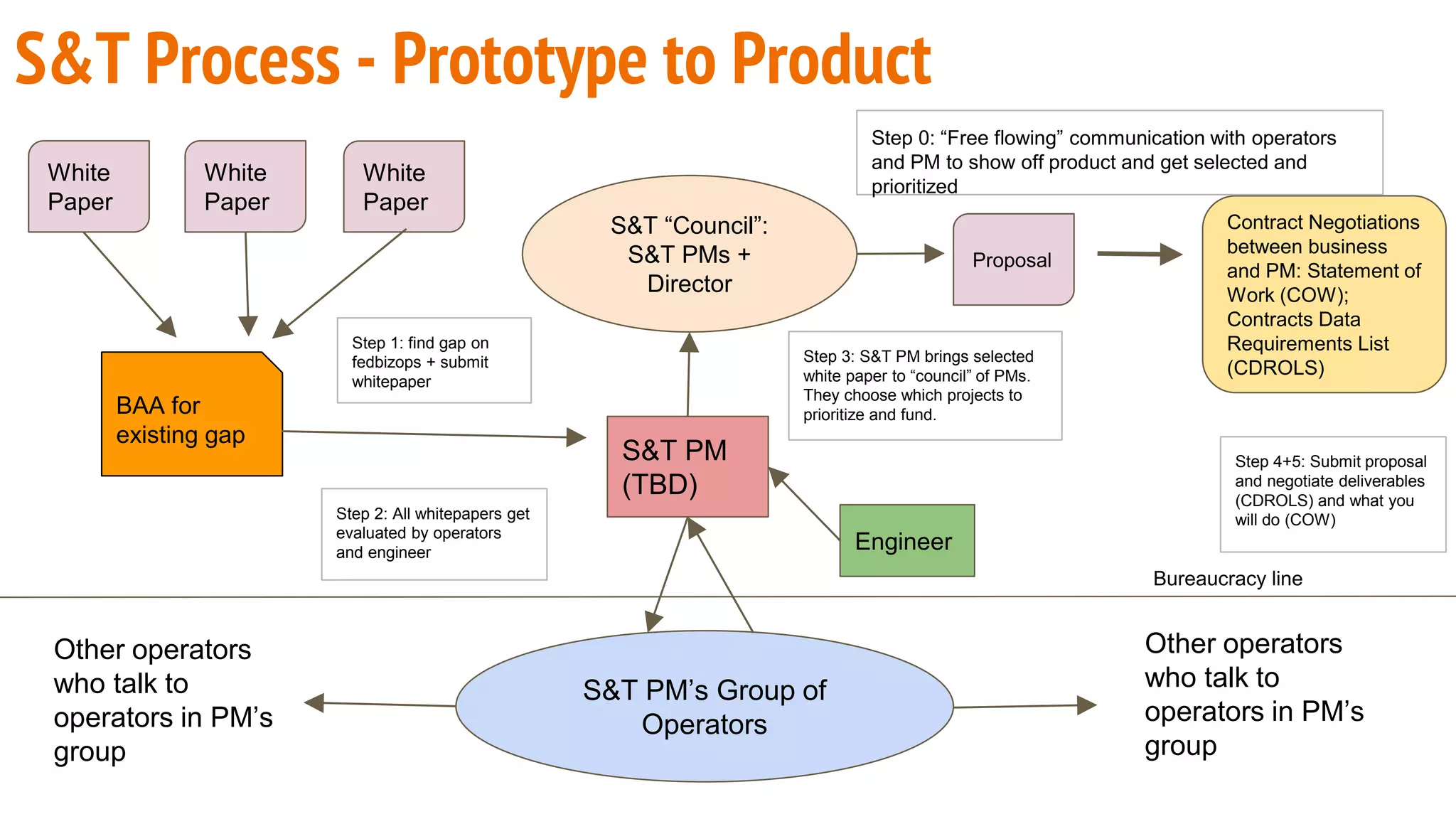
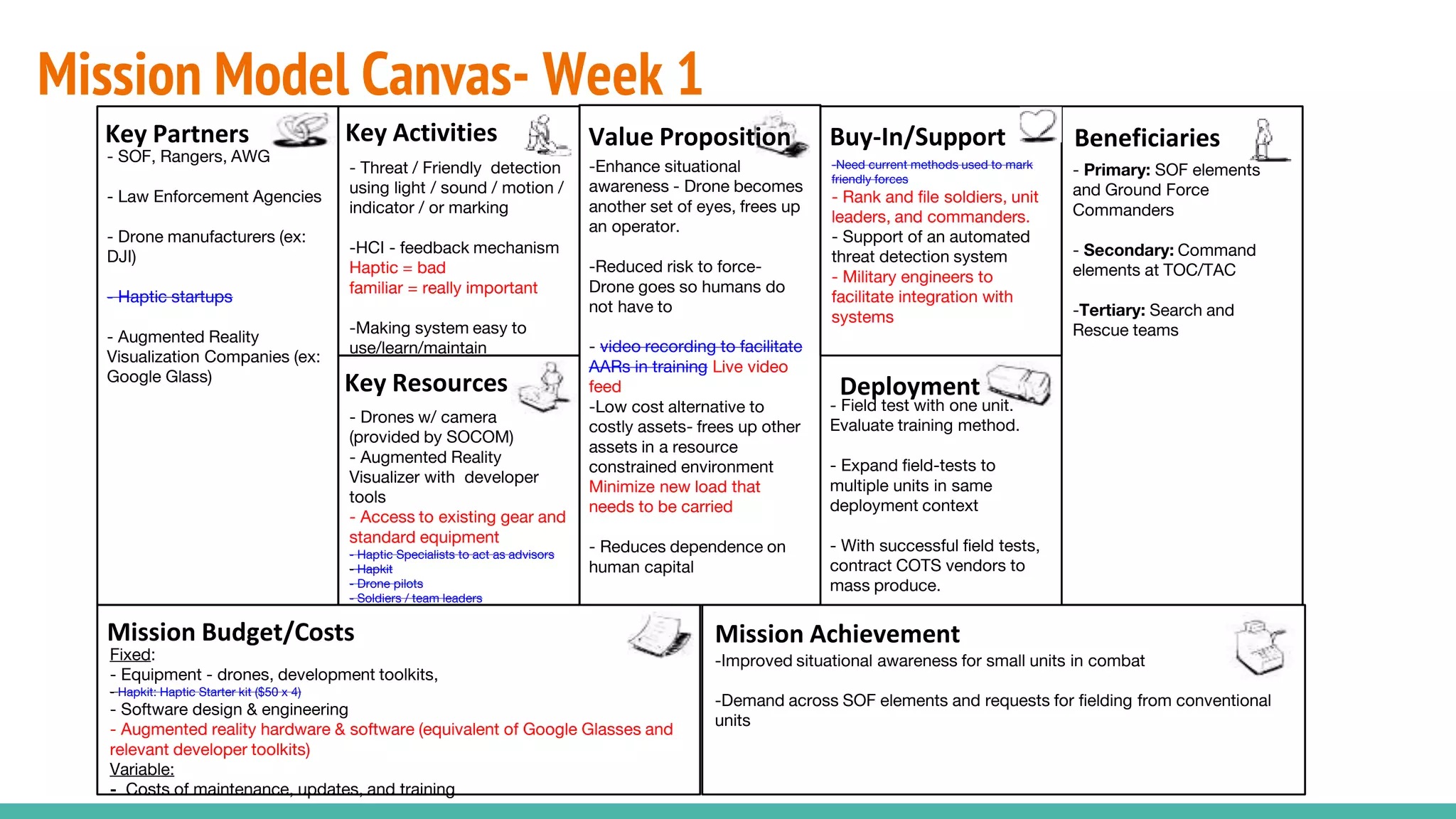
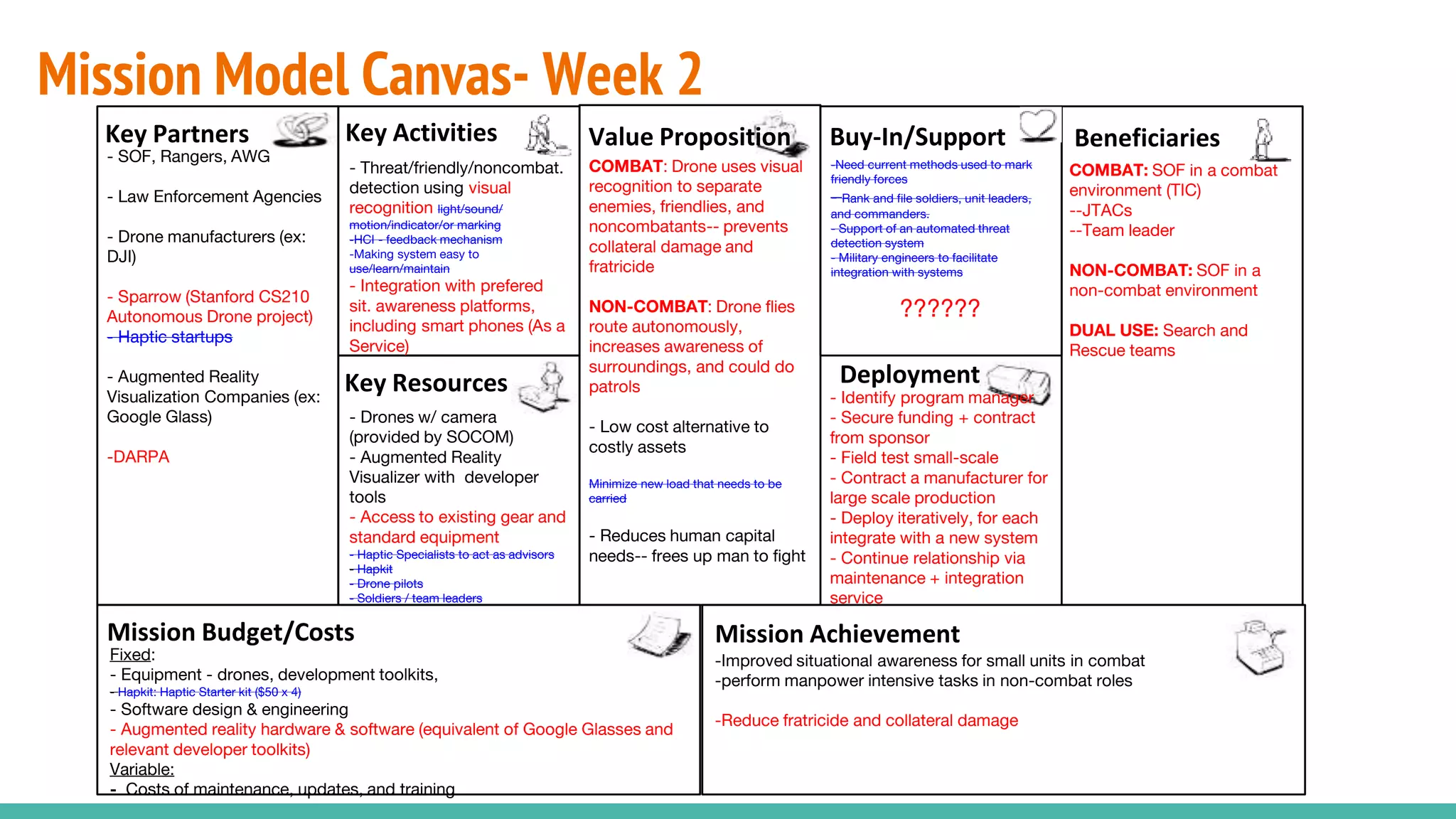
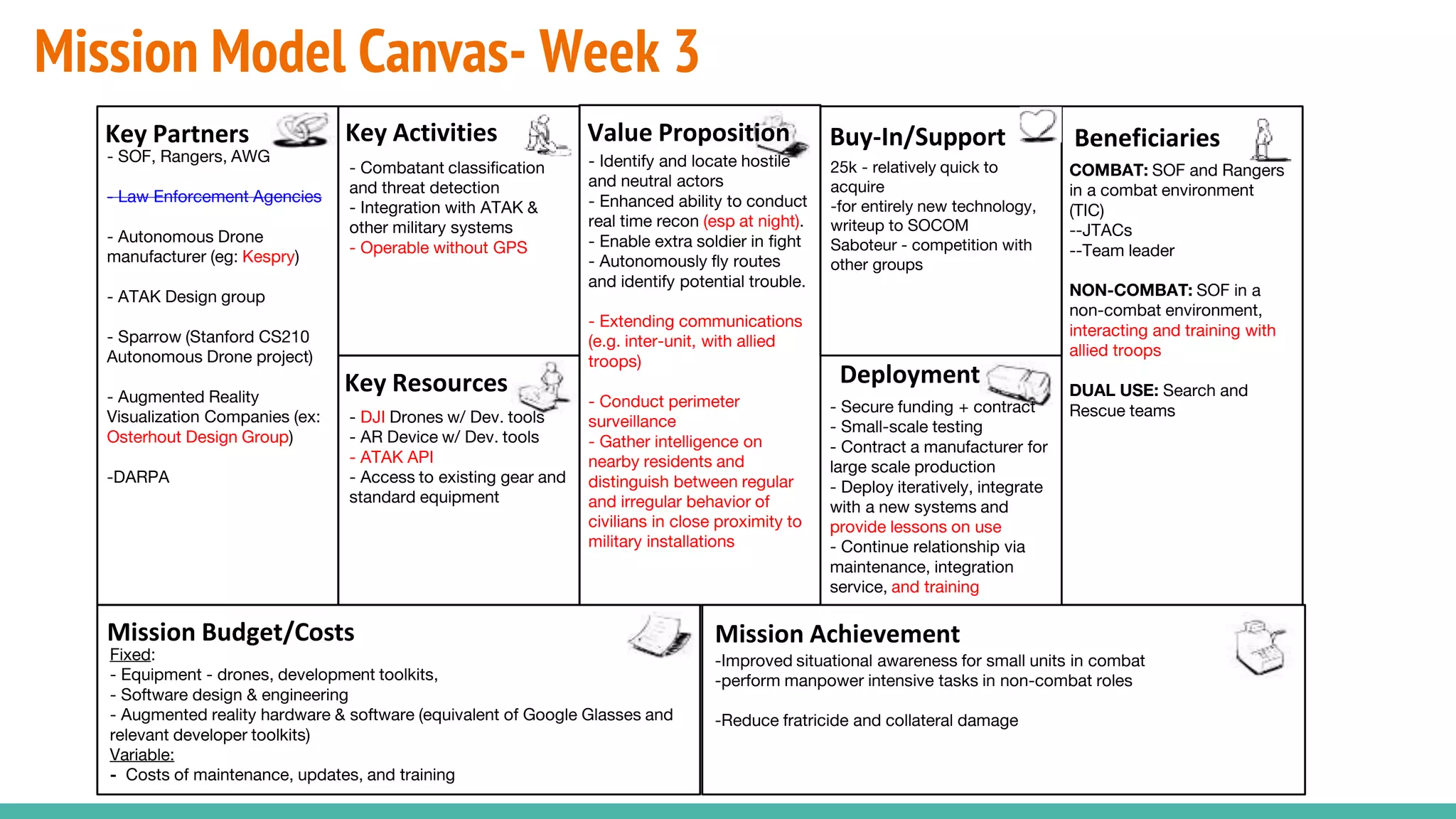
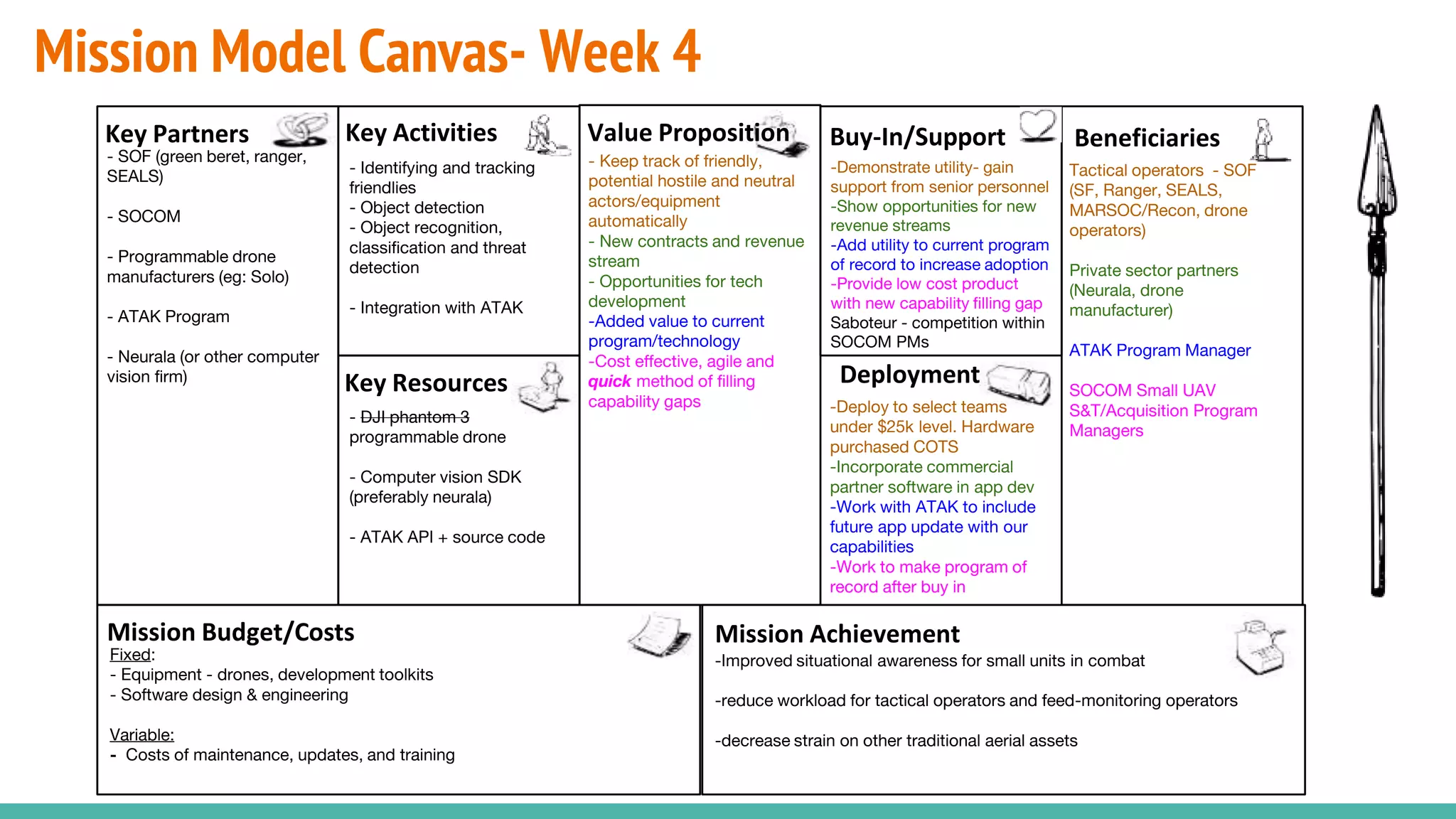
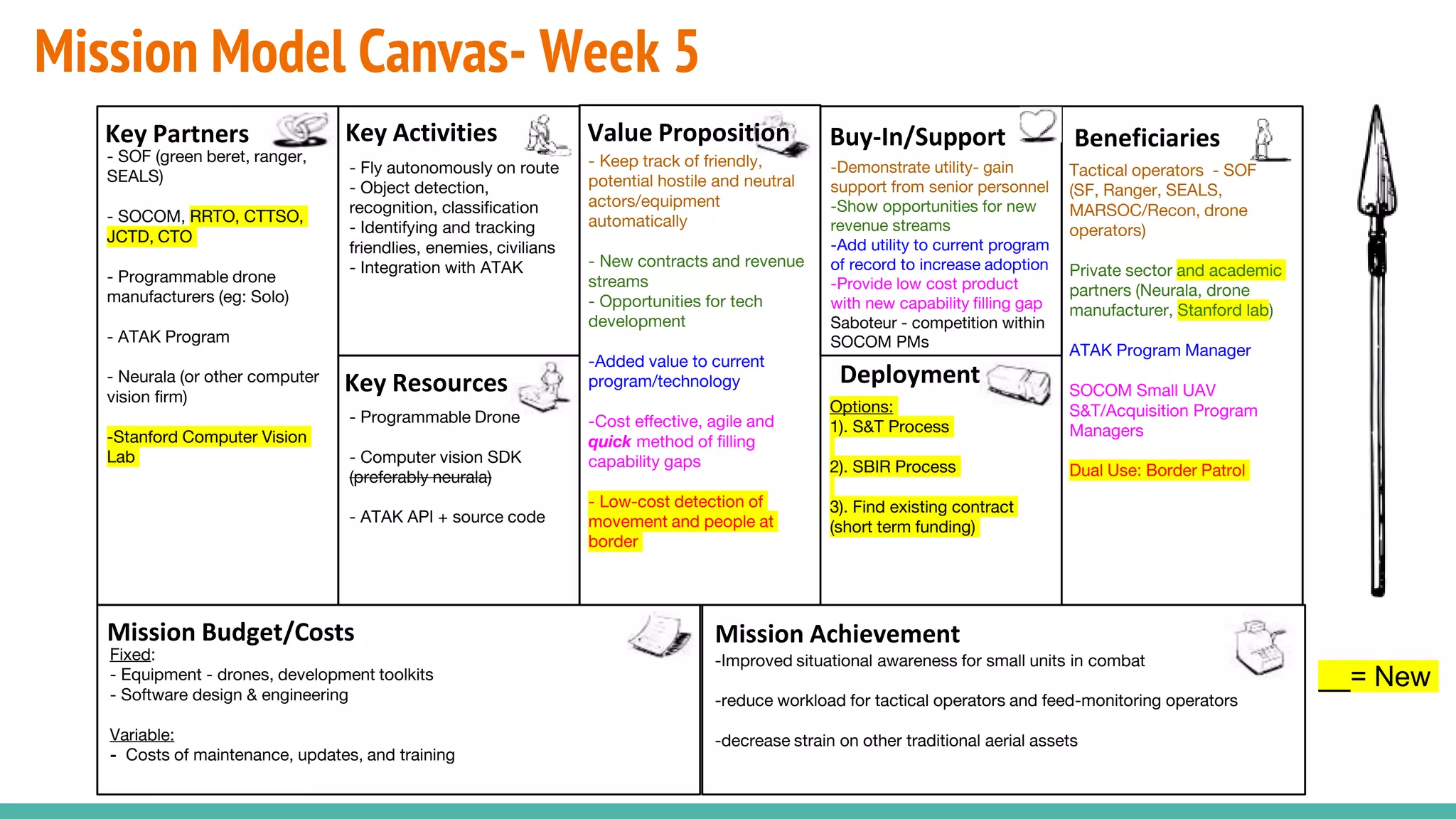
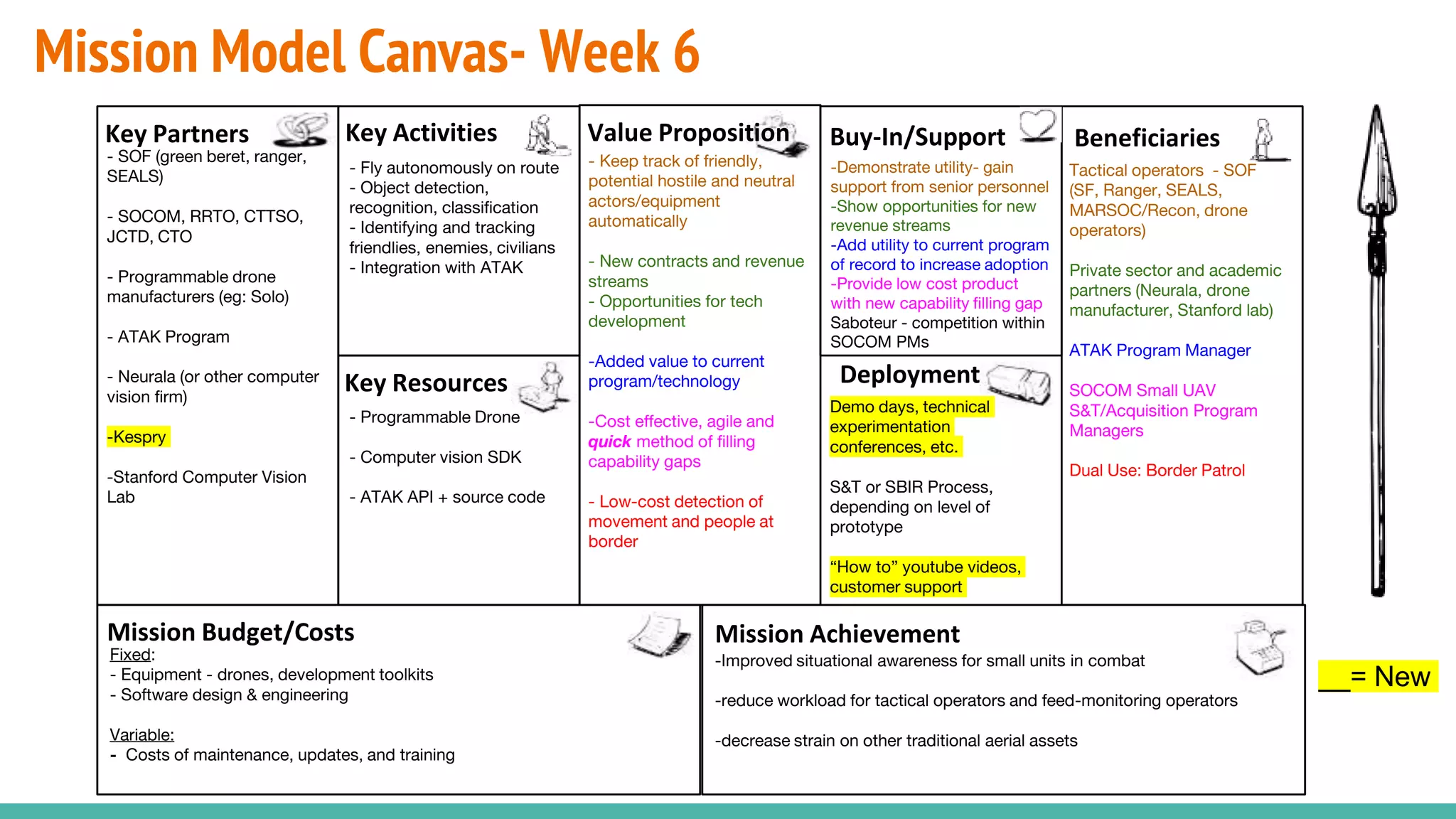
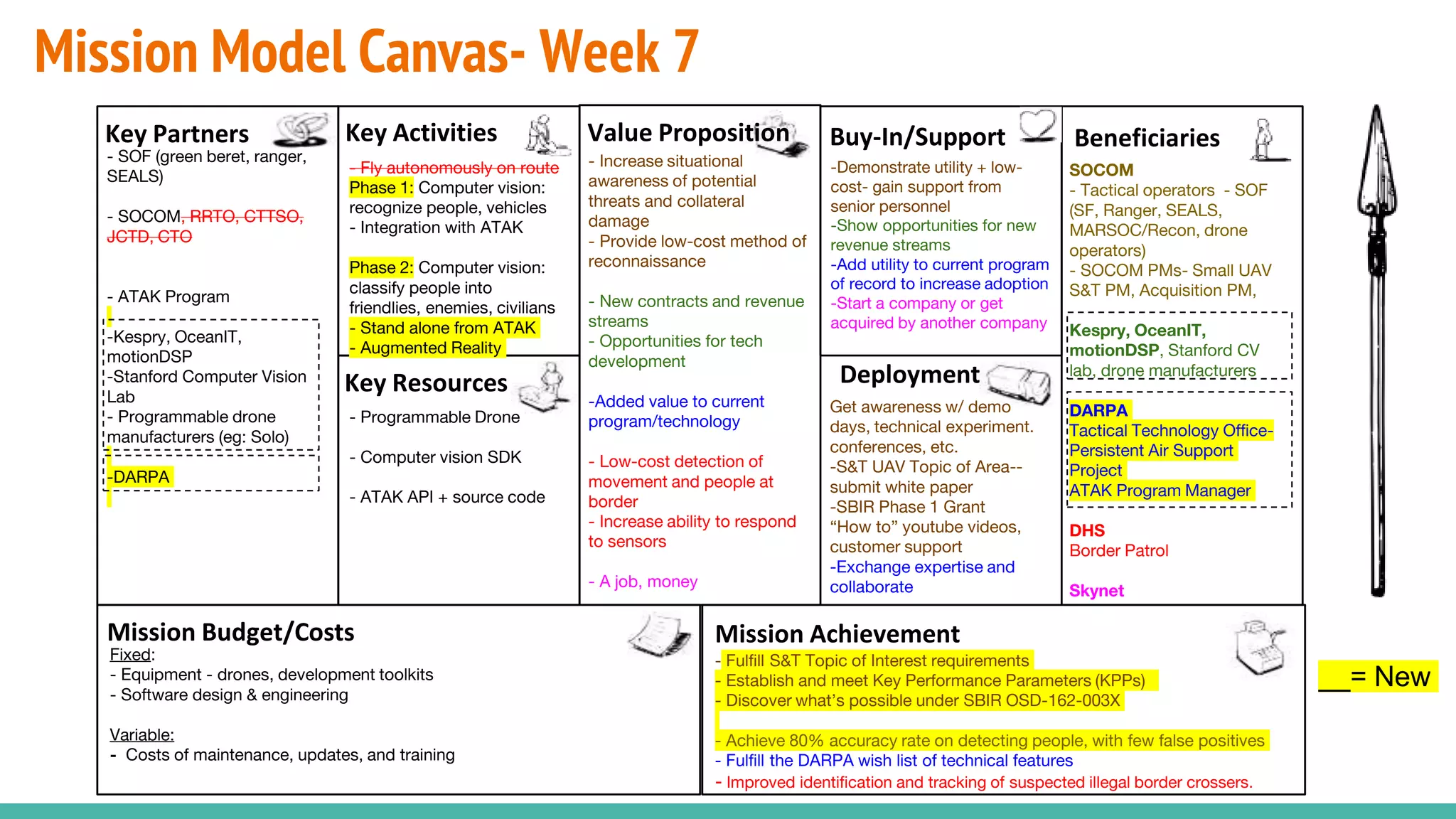
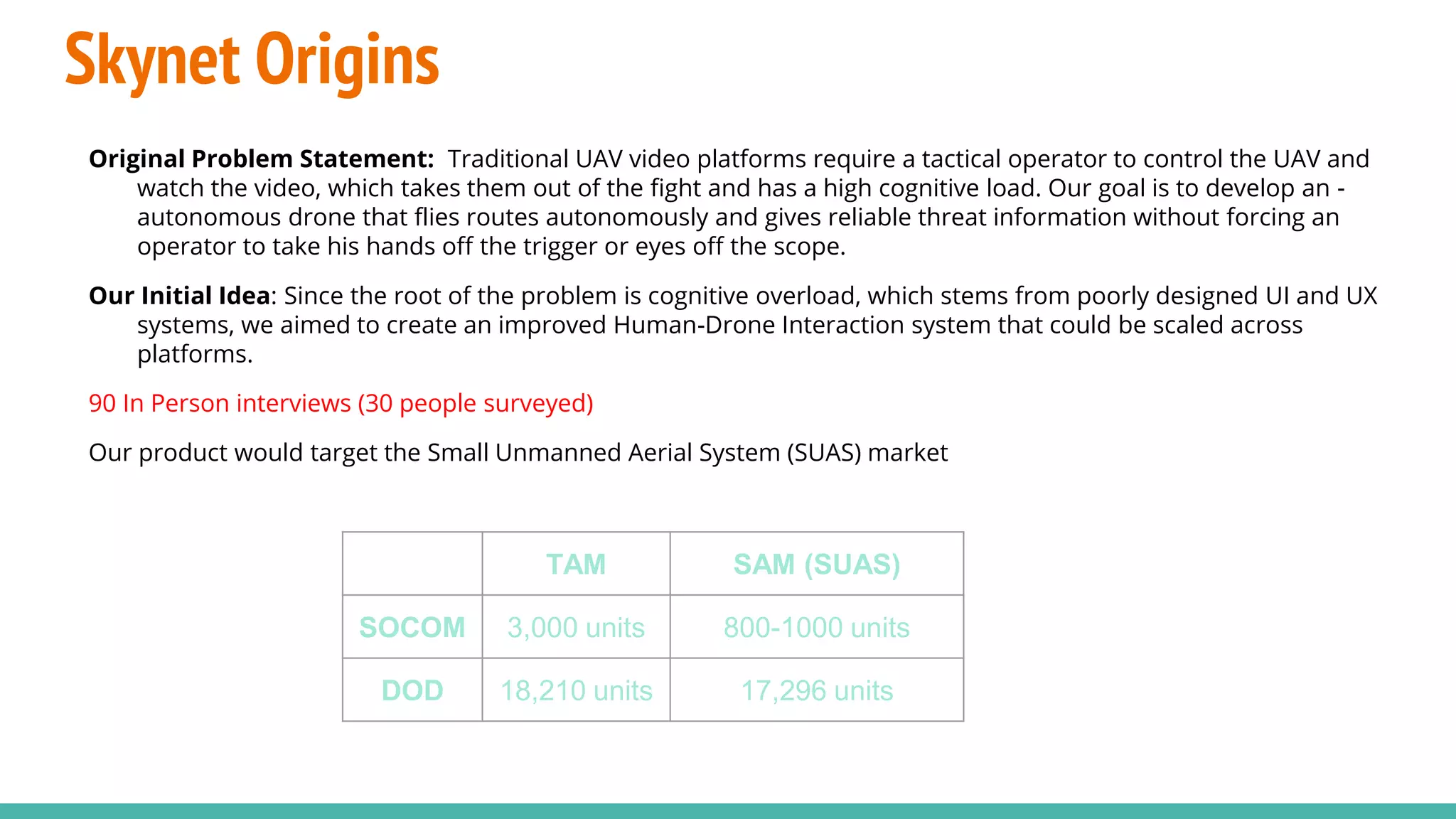
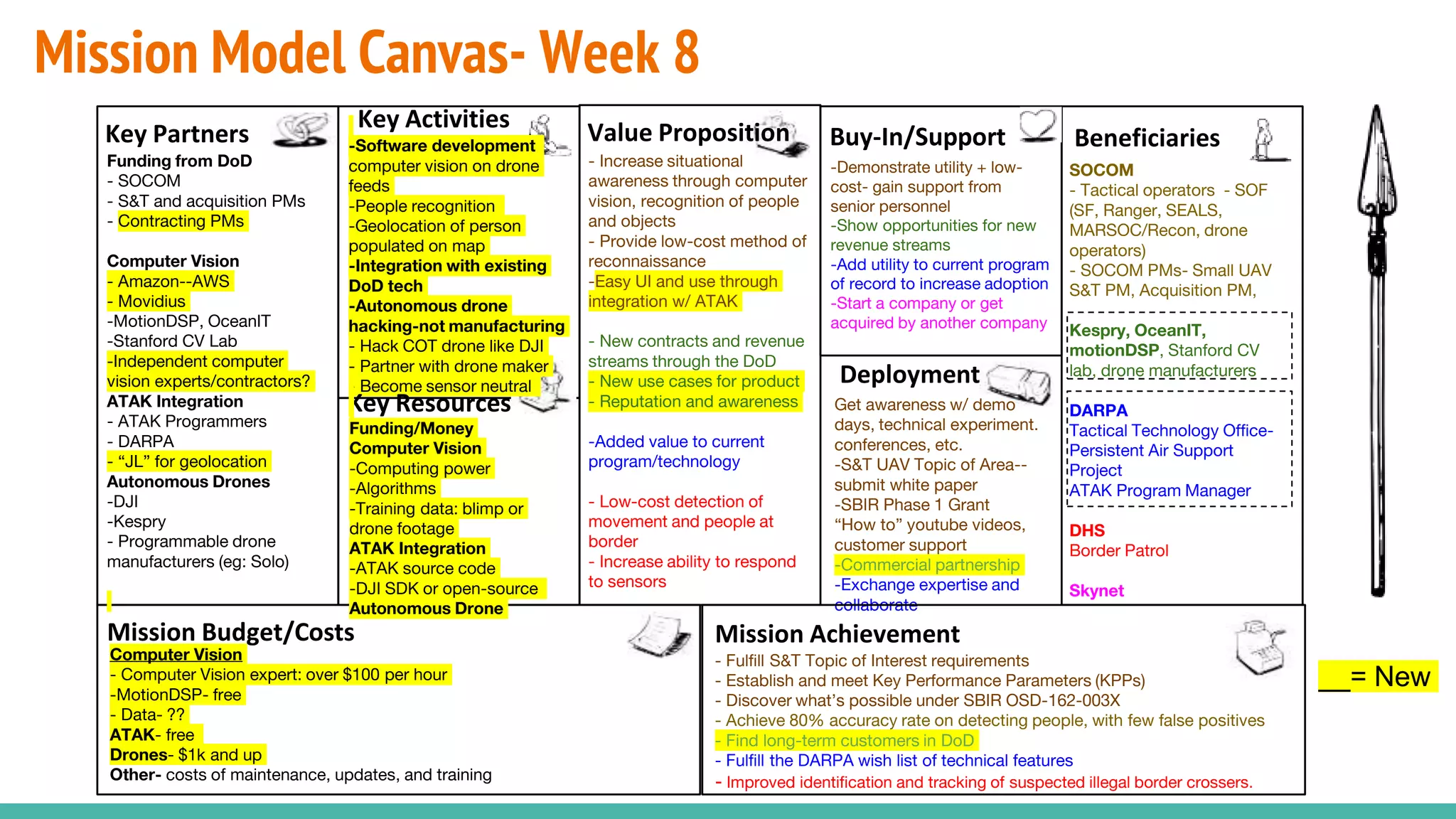
The document discusses the development of a drone system aimed at enhancing situational awareness for military operations by integrating human detection and automated responses via computer vision technology. It details the project's journey, including user interviews, technology exploration, and the establishment of a mission model canvas outlining participants, beneficiaries, and key partners. The project aims to create a user-friendly interface that frees up human operators while improving reconnaissance capabilities and operational efficiency in combat scenarios.